Transformer Paper Authors Rebuild Lobster, Saying Goodbye to OpenClaw’s Exposed Vulnerabilities
TechFlow Selected TechFlow Selected
Transformer Paper Authors Rebuild Lobster, Saying Goodbye to OpenClaw’s Exposed Vulnerabilities
Illia Polosukhin, co-creator of the Transformer architecture, has rewritten OpenClaw in Rust and launched IronClaw—a secure AI agent framework that addresses credential leakage vulnerabilities at the architectural level.
Source | QbitAI
How many lobsters are running naked on the internet?
AI agents are exposing your passwords and API keys to the entire web.
Illia Polosukhin, co-author of the Transformer architecture, could no longer stand it—and rebuilt a secure version of Lobster from scratch: IronClaw.

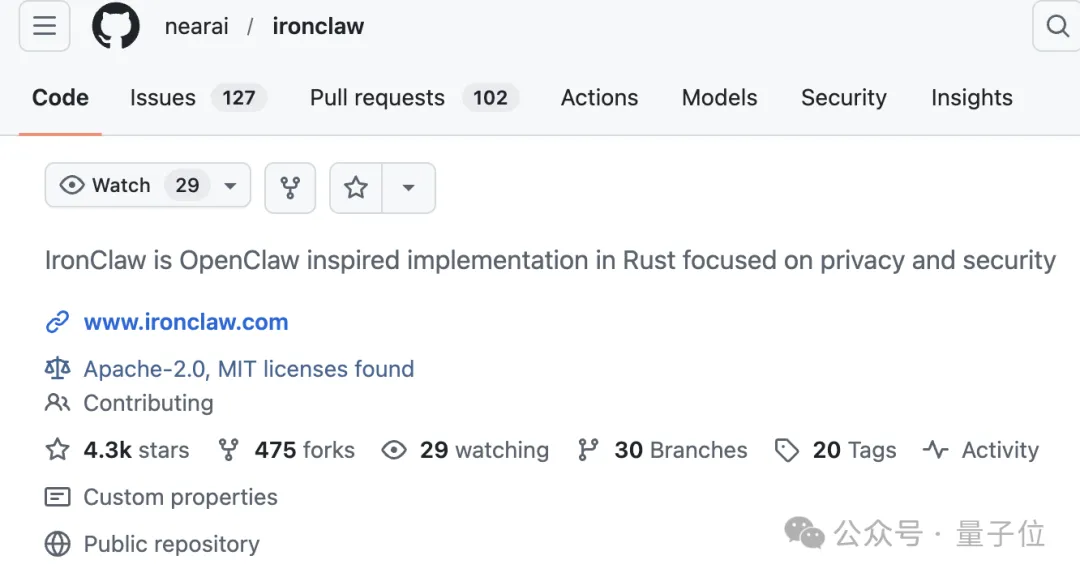
IronClaw is now open-sourced on GitHub, offering installers for macOS, Linux, and Windows. It supports both local deployment and cloud-hosted deployment. The project remains in rapid iteration; binary files for v0.15.0 are already available for download.
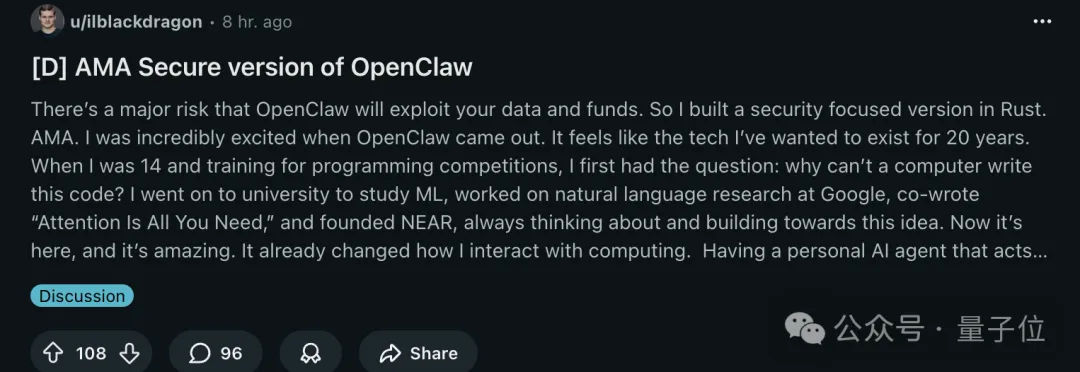
Polosukhin (affectionately nicknamed “Pineapple Brother” hereafter) also launched a dedicated thread on Reddit to address all questions—drawing significant attention.
01 OpenClaw Went Viral—But Also Caught Fire
Pineapple Brother himself was an early user of OpenClaw and called it “the technology I’ve waited 20 years for.”
It has already changed how I interact with computing.
Yet OpenClaw’s security posture is nothing short of catastrophic: one-click remote code execution, prompt injection attacks, malicious skills stealing passwords—the ecosystem has exposed them all, one by one.
More than 25,000 publicly accessible instances were exposed on the internet without adequate security controls, prompting security experts to dub it a “security dumpster fire.”

The root cause lies in the architecture itself.
When users hand their email Bearer Token to OpenClaw, it gets sent directly to the LLM provider’s servers.
On Reddit, Pineapple Brother explained what that implies:
All your information—even data you haven’t explicitly authorized—could be accessed by any employee at that company. The same applies to your employer’s data. This isn’t about malice on the part of those companies; it’s simply the reality that users have no real privacy.
He emphasized that no amount of convenience justifies risking the safety and privacy of yourself and your family.
02 Rebuilding Everything From Scratch—in Rust
IronClaw is a complete rewrite of OpenClaw in Rust.
Rust’s memory-safety guarantees fundamentally eliminate traditional vulnerabilities like buffer overflows—critical for systems handling private keys and user credentials.
In terms of security architecture, IronClaw implements a four-layer defense-in-depth model.
The first layer is Rust’s built-in memory safety.
The second layer is WASM sandboxing: all third-party tools and AI-generated code run inside isolated WebAssembly containers. Even if a tool is malicious, its damage is strictly confined within the sandbox.
The third layer is an encrypted credential vault: all API keys and passwords are stored encrypted using AES-256-GCM, and each credential is bound to policy rules specifying exactly which domains it may access.
The fourth layer is a Trusted Execution Environment (TEE), leveraging hardware-level isolation to protect data—even cloud service providers cannot access users’ sensitive information.
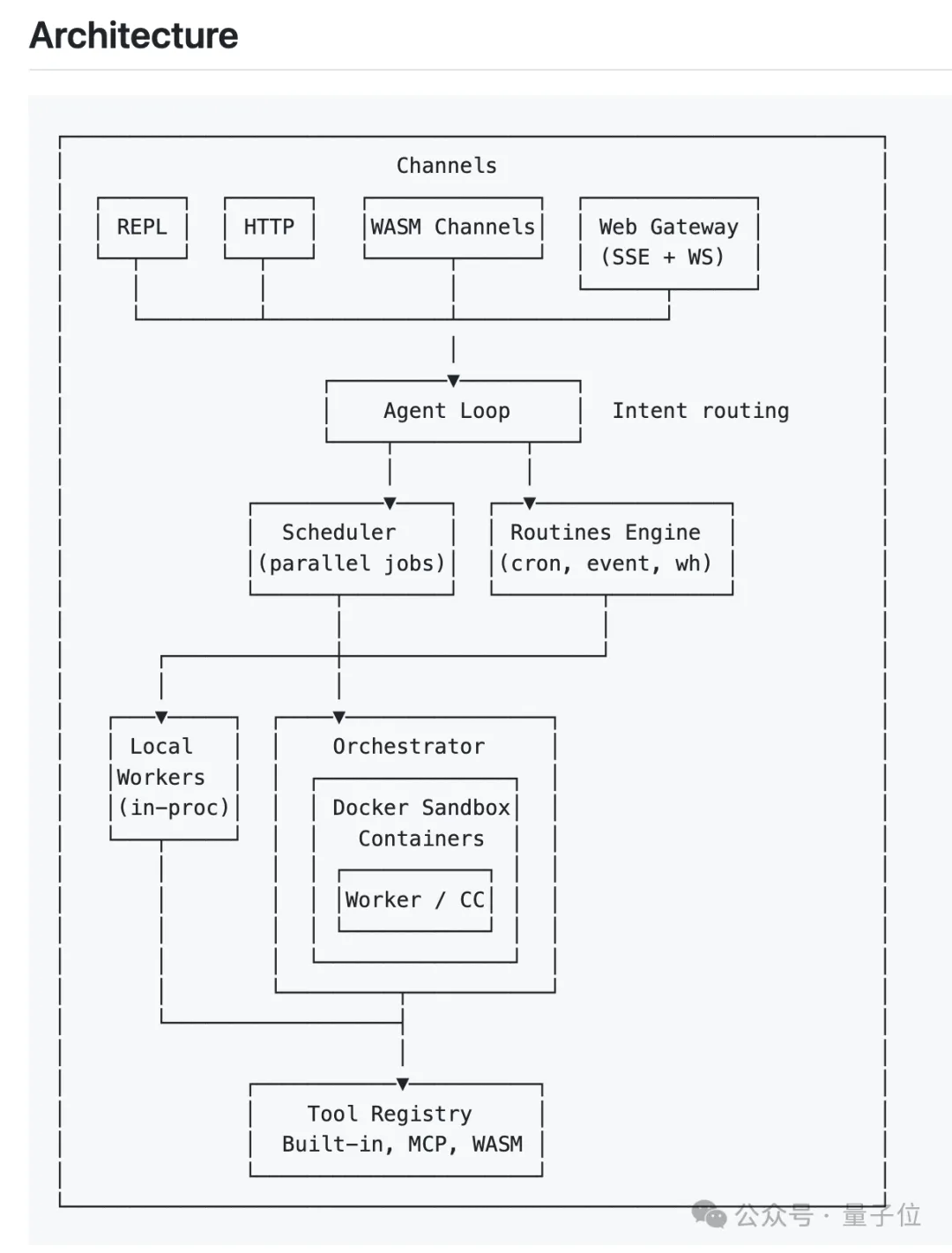
The most critical design principle in this system is: Large language models never touch raw credentials.
Credentials are injected only at the network boundary—precisely when an agent needs to communicate with an external service.
Pineapple Brother gave an example: even if a large model falls victim to a prompt injection attack attempting to exfiltrate a user’s Google OAuth token to an attacker, the credential store will outright reject the request, log the incident, and alert the user.
Still, the developer community remains wary. After all, over 2,000 public OpenClaw instances have been compromised, and numerous malicious skills exist. If IronClaw gains popularity, could it suffer the same fate?
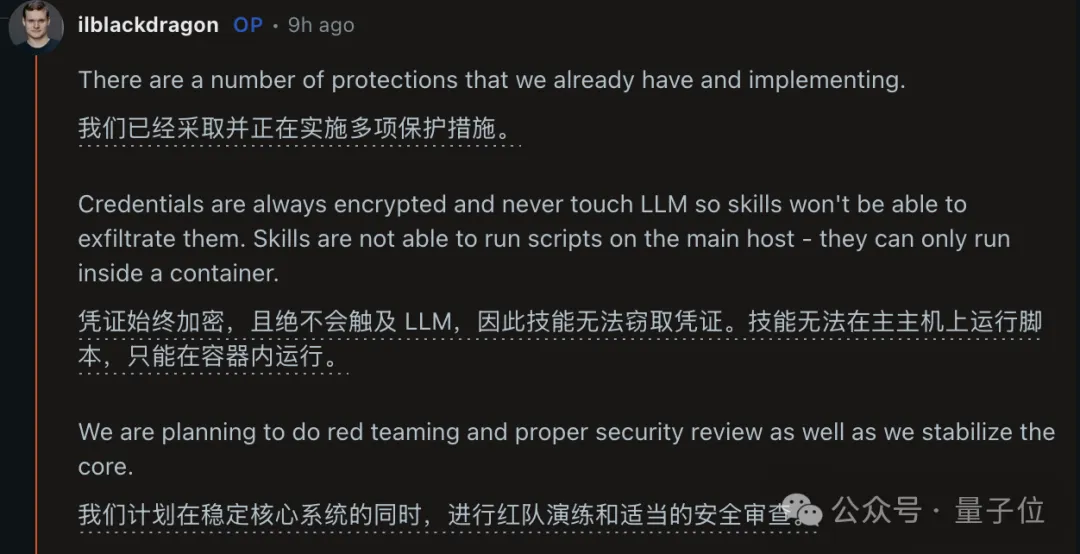
Pineapple Brother responded that IronClaw’s architecture has already eliminated OpenClaw’s core vulnerabilities at their root: credentials remain encrypted at rest and never reach the LLM; third-party skills cannot execute scripts on the host—they run exclusively inside containers.
Even CLI access requires decryption via the user’s system keychain; the encrypted key itself is meaningless without it.
He added that as the core version stabilizes, the team plans formal red-team exercises and professional security audits.
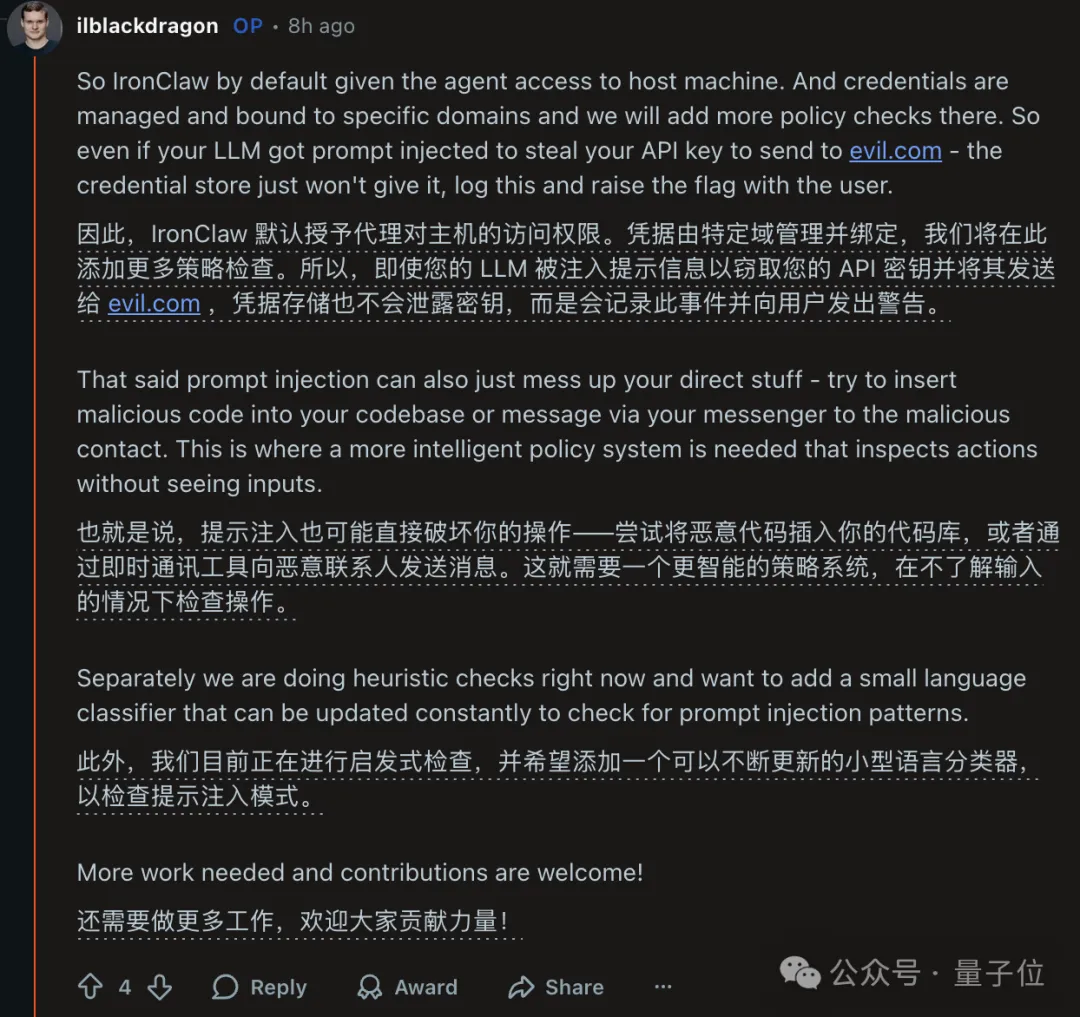
Regarding prompt injection—a widely acknowledged industry challenge—Pineapple Brother offered more detailed insights.
Currently, IronClaw employs heuristic pattern-matching rules. Its long-term goal is to deploy a lightweight, continuously updated language classifier trained specifically to detect injection patterns.
Yet he also acknowledged that prompt injection can do more than steal credentials—it can directly tamper with users’ code repositories or send malicious messages via communication tools.
Defending against such attacks demands a smarter policy engine capable of auditing an agent’s behavioral intent *without* inspecting its input content. “There’s still more work to do—community contributions are welcome.”
One user asked about trade-offs between local and cloud deployment.
Pineapple Brother noted that pure local deployment has clear limitations: agents stop working when devices power off; mobile energy consumption becomes prohibitive; and complex, long-running tasks are infeasible.
He believes confidential cloud is currently the optimal compromise—delivering privacy guarantees approaching those of local devices while solving the “always-on” requirement.
He also highlighted a subtle detail: users can define policies—for instance, automatically enabling additional security barriers during international travel to prevent unauthorized access.
03 A Much Bigger Ambition
Pineapple Brother is no ordinary open-source developer.
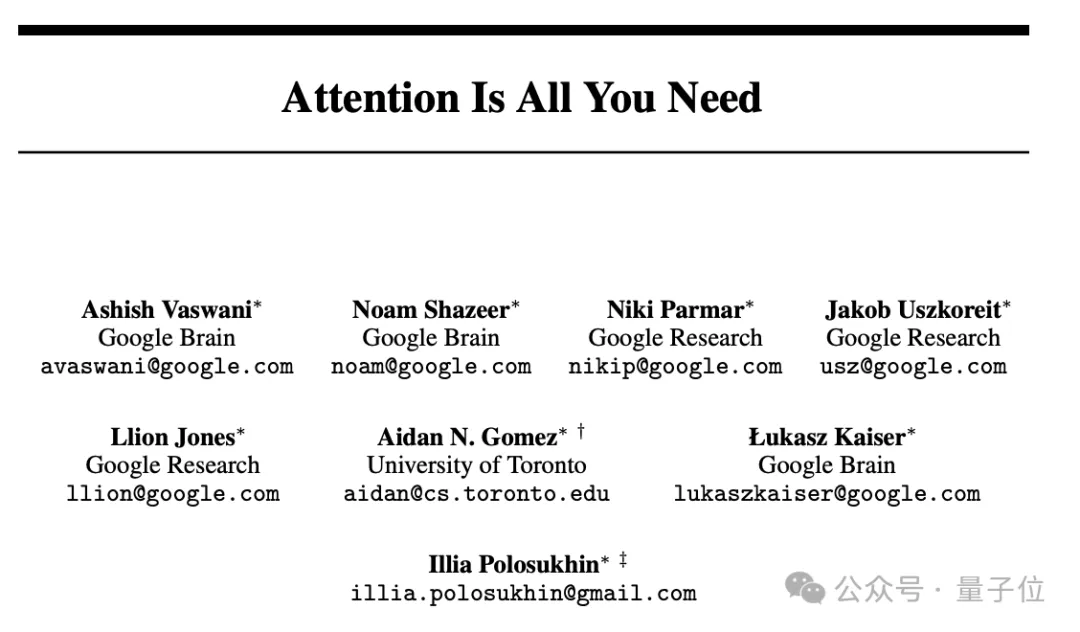
In 2017, he was one of eight co-authors of “Attention Is All You Need,” whose proposed Transformer architecture underpins all modern large language models.
Though listed last among the authors, a footnote clarifies: “Equal contribution. Listing order is random.” Author order was purely arbitrary.
That same year, he left Google to found NEAR Protocol—an initiative aiming to fuse AI and blockchain technologies.
IronClaw embodies a broader strategic vision from NEAR: User-Owned AI.
In this vision, users retain full control over their data and assets, and AI agents perform tasks on their behalf within trusted environments.
NEAR has already built foundational infrastructure—including an AI cloud platform and a decentralized GPU marketplace—while IronClaw serves as the runtime layer of this ecosystem.
Pineapple Brother has even developed a marketplace where agents hire one another.
On NEAR’s market.near.ai, users can register specialized agents. As these agents accumulate reputation, they qualify for higher-value tasks.
When asked how ordinary people should adapt to the AI era over the next five years, Pineapple Brother advised adopting AI-agent workflows as soon as possible—and learning to delegate entire work processes for full automation.
This perspective didn’t emerge overnight.
Back in 2017, when founding NEAR AI, Pineapple Brother told everyone, “In the future, you’ll only need to talk to computers—you won’t need to write code.”
At the time, people thought they were crazy—talking nonsense.
Nine years later, it’s becoming reality.
“AI agents are the ultimate interface between humans and everything online,” Polosukhin wrote. “But let’s make them safe.”
---
GitHub Repository:
https://github.com/nearai/ironclaw
References:
[1] https://www.reddit.com/r/MachineLearning/comments/1rlnwsk/d_ama_secure_version_of_openclaw/
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News