Interpreting Vitalik's Latest Paper: Privacy Pools, Making Compliance Without Sacrificing Privacy and Decentralization
TechFlow Selected TechFlow Selected

Interpreting Vitalik's Latest Paper: Privacy Pools, Making Compliance Without Sacrificing Privacy and Decentralization
We urgently need a way to prove to regulators that my source of funds is clean and legal, without exposing privacy or compromising decentralization.

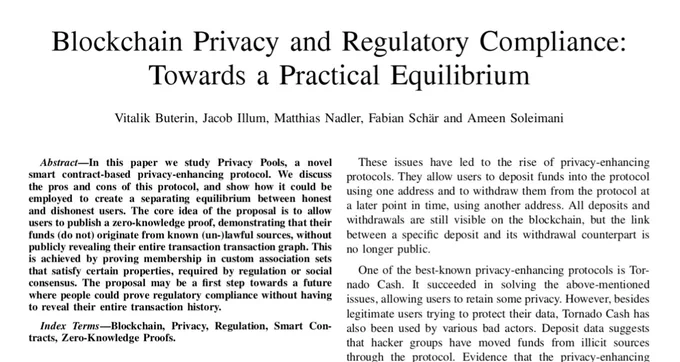
Yesterday, Vitalik co-authored a paper titled "Blockchain Privacy and Regulatory Compliance: Towards a Practical Equilibrium" with researchers from the University of Basel, sparking widespread discussion on Twitter.
Why should we pay attention to such an academic paper during a bear market?
Vitalik’s writings and ideas often shape new narratives and technological directions in the blockchain space. Meanwhile, other prominent experts offer unique insights into blockchain technology and its development trends.
Moreover, the paper addresses the critical issue of balancing privacy and regulatory compliance—key factors that will determine the future trajectory and legitimacy of the crypto industry. Finding equilibrium between user privacy protection and regulatory requirements remains one of the most pressing challenges facing the sector.
After reviewing the paper, we found that its proposed Privacy Pools protocol offers a technically feasible solution for reconciling privacy with compliance. This could prevent tragedies like Tornado Cash’s regulatory shutdown from recurring.
However, the paper is highly technical and academic, making it difficult for average users to grasp its nuances and implications.
Therefore, TechFlow Research has analyzed and distilled the paper, aiming to explain its core concepts in accessible language, helping more people understand this crucial topic—privacy versus compliance—and the potential technical pathways toward resolution.
Who Are the Authors?
First, the paper was led by Vitalik and co-written by academics and industry professionals with relevant expertise.
Vitalik serves as the first author. Given his influence and reputation in the cryptocurrency world, having him at the forefront ensures greater visibility and credibility for the proposed solution.
Other co-authors include: Jacob Illum, a researcher at Chainalysis;
mat nadler, a PhD student at the University of Basel with experience in DeFi and EVM development;
Fabian Schär, a professor at the University of Basel specializing in public blockchains and DeFi protocols;
Ameen Soleimani, founder of several well-known crypto projects with extensive practical experience.
Background: The Conflict Between Privacy and Regulation – The Tragedy of Tornado Cash
-
Public blockchains are designed to be transparent—anyone can verify transactions without relying on centralized intermediaries. However, this transparency creates privacy issues, as every address's transaction history is permanently recorded and subject to tracking and analysis.
-
The Bitcoin whitepaper assumed privacy through public-key anonymity, but this has proven insufficient. Various blockchain analytics tools can now link addresses and transactions. Thus, stronger cryptographic techniques are needed to enhance privacy on public blockchains.
-
Systems using general-purpose zero-knowledge proofs, such as Zcash and Tornado Cash, can expand the anonymity set to include all transactions, significantly improving privacy. However, Tornado Cash was also abused by hackers, leading OFAC to sanction its smart contract addresses.
TechFlow adds some technical context about Tornado Cash for readers unfamiliar with its regulatory issues:
-
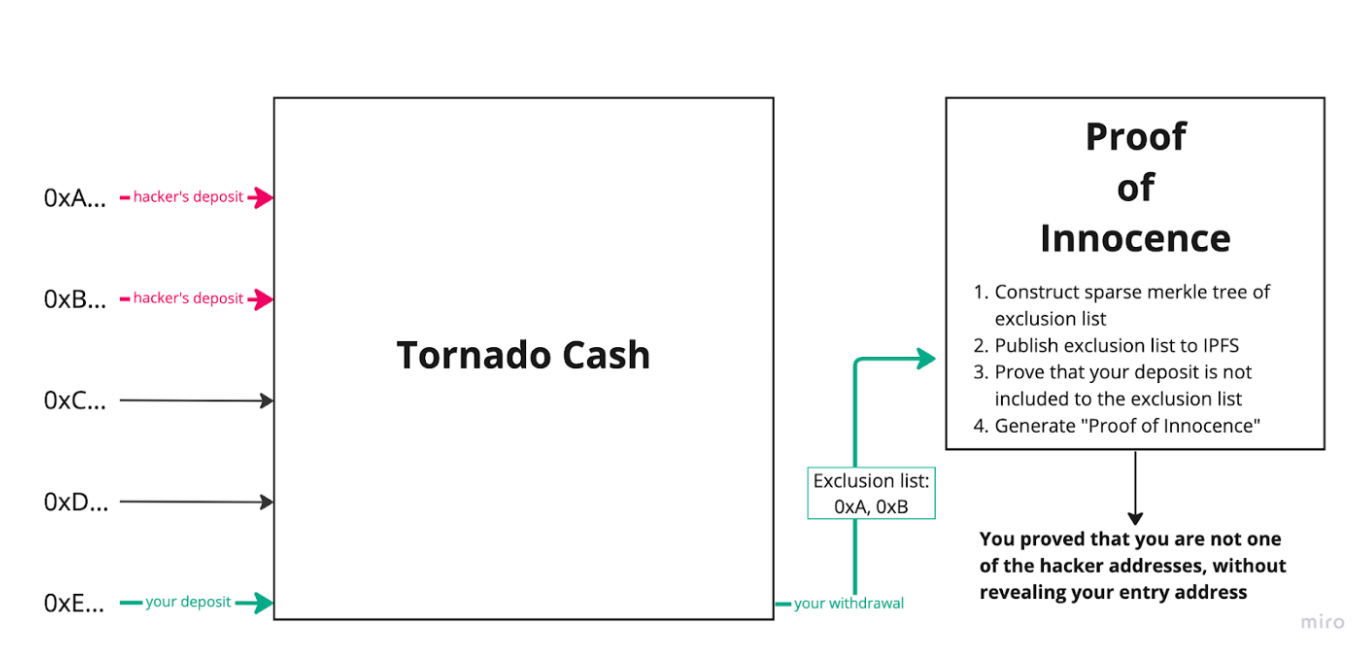
Tornado Cash is a privacy-enhancing protocol based on zero-knowledge proofs that enables anonymous transactions. Users deposit funds and later withdraw them to a different address. On-chain, only deposits and withdrawals are visible—there is no way to link the two. This provides strong anonymity.
-
However, the protocol was exploited by hacking groups for money laundering. Evidence shows North Korean hacker groups used Tornado Cash to launder illicit funds.
-
As a result, the U.S. Treasury’s OFAC added Tornado Cash’s smart contract addresses to its sanctions list. Regulators argue the protocol facilitates money laundering and hinders financial crime investigations.
-
The key problem with Tornado Cash is that legitimate users cannot easily disassociate themselves from criminal activity attracted to the protocol.
-
Additionally, generating withdrawal proofs requires reliance on Tornado Cash’s centralized server. Users must submit withdrawal details to the server, which uses its private database to confirm which deposit corresponds to the withdrawal and then generates the proof.
-
This introduces centralization: only Tornado Cash holds the complete database required to generate valid proofs. Regular users cannot verify the correctness of these proofs—they and regulators must simply trust the system.
We urgently need a method to prove to regulators that our funds are clean and legitimate—without compromising privacy or requiring centralized trust.
Hence, the paper proposes a viable technical solution called the Privacy Pools protocol: it allows users to prove their funds originate from a customizable association set—protecting privacy while enabling verification of whether funds came from sanctioned sources.
This could be the first step toward coexistence between privacy and regulation.
zk + Association Sets: The Key to the Solution
From the background above, we understand the core challenge: proving funds are “clean” while preserving both privacy and decentralization.
To preserve privacy, zero-knowledge proofs (zk) come naturally to mind. Indeed, Vitalik’s latest paper affirms the value of zk, especially zk-SNARKs, in addressing privacy concerns:
-
Zero-knowledge: Proves a statement is true without revealing any private data.
-
Succinctness: Proofs are short and fast to verify, even for complex computations.
However, zk-SNARKs alone solve only part of the problem: they can prove a transaction occurred while hiding its details—but not necessarily prove the source of the funds is legitimate.
To fully resolve the issue, we need to prove the origin of funds is legitimate—while still hiding transaction details.
Thus, the paper combines zk with another concept: Association Sets.
-
An association set allows a user to prove their funds come from a custom-defined group of transactions—not fully hidden, nor fully revealed. For example, if I transfer 1 BTC, and that BTC was accumulated from multiple prior transactions, those prior transactions form an association set.
-
Association sets can vary in size and composition. Users can choose larger sets for stronger privacy or smaller, curated sets to demonstrate compliance.
With this concept in mind, let’s see how zk + association sets enable both privacy and verifiable fund origins:
-
When depositing, the user generates a secret via zk and computes a public coin ID. (This links the user to the funds.)
-
When withdrawing, the user submits a nullifier to prove they’ve used the secret. (This proves ownership of the funds.)
-
Using zk, the user proves their coin ID exists in both the global set and their declared association set. (This proves the funds are “clean.”)
-
Observers can only see the number of transactions and the associated pool—never the identities or specific transaction paths.
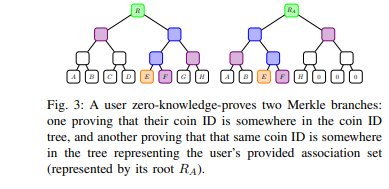
More technically, consider the Merkle tree diagram from the original paper. The Merkle tree stores coin IDs—representing transactions that have been zk-processed so their details remain hidden.
The left tree represents all current transactions, possibly including the user’s funds. To prove the legitimacy of these funds, the user refers to the right tree—a self-defined association set containing their transaction along with others. By justifying the legitimacy of transactions in this right-hand set, the user indirectly proves the legitimacy of their current funds.
Conceptually, this forms a privacy pool. The association set contains the provenance of the user’s funds. Thanks to zero-knowledge proofs, the user can prove this provenance is real—without revealing any sensitive transaction details.
Practical Use Case of Privacy Pools
The paper presents a vivid example illustrating how Privacy Pools work in practice.
-
Scenario Setup:
-
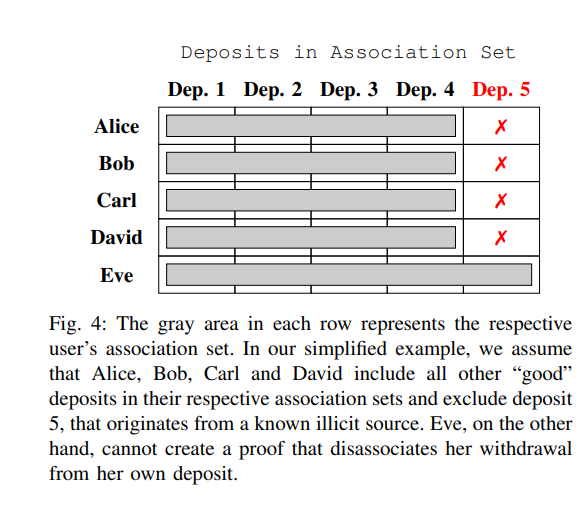
Five users: Alice, Bob, Carl, David, and Eve.
-
The first four are honest users; Eve is a known thief.
-
While Eve’s real identity may be unknown, the public knows that funds received by the “Eve” address are stolen.
-
User Choices During Withdrawal:
-
When each user withdraws, they can choose an association set under the proposed method.
-
The association set must include their own deposit—users cannot exclude their own contributions.
-
Alice, Bob, Carl, and David—being honest—can avoid association with Eve by selecting an association set that excludes her, thereby proving they are not linked to illicit funds.
-
Eve faces a dilemma: she cannot select a set containing only herself—that would immediately expose her as the bad actor.
-
To hide, Eve might include all five users in her association set, hoping to blend in.
-
But since the other four users all chose sets excluding Eve, observers can use elimination to identify Eve as the outlier—the only one who included everyone—and thus conclude she is the bad actor.
-
-
Outcome:
-
Through their choice of association sets, Alice, Bob, Carl, and David successfully prove they are not associated with Eve, the known bad actor.
-
Eve cannot conceal her misconduct because her inclusion of all users reveals her intent to obfuscate.
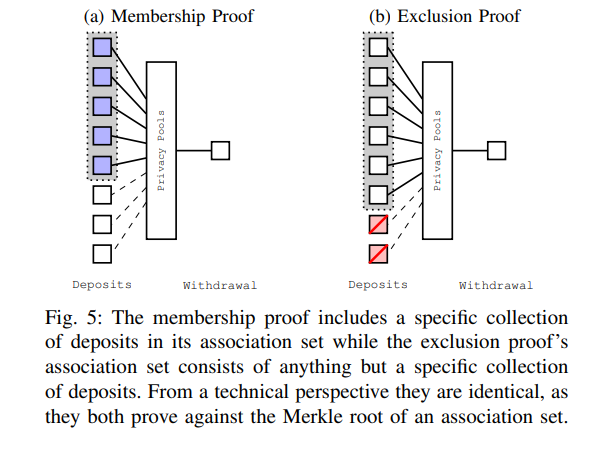
Figure 5 in the paper further illustrates the difference between these two types of proofs: a membership proof includes a specific set of deposits, while an exclusion proof includes all deposits except a specified set.
Future Outlook
Although the proposed protocol combining zkSNARKs and association sets achieves a promising balance between compliance and privacy, several technical and governance challenges remain. The authors suggest future research directions:
-
Further Study of Privacy Properties: The level of privacy provided depends on many factors. The size of association sets, appropriateness of root selection, and user errors could allow sophisticated attackers to link transactions.
-
Research on Separation Dynamics: Further study how good and bad actors behave under certain assumptions, and how public proofs by legitimate users impact the privacy of others.
-
Legal Research: Legal scholars can examine specific disclosure requirements. The paper’s proposal is highly adaptable, and legal experts can help refine the protocol and ecosystem to comply with diverse jurisdictional regulations.
Finally, we believe that at this moment, privacy and compliance are often seen as irreconcilable opposites.
The technology described in this paper finds a middle ground—offering a positive vision for the entire industry. We hope more researchers and developers will be inspired by this approach to contribute to the healthy and sustainable growth of the crypto ecosystem.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News