CertiK and Kraken Clash: Can White Hats Turn Black?
TechFlow Selected TechFlow Selected

CertiK and Kraken Clash: Can White Hats Turn Black?
Is the behavior of white-hat hackers legal?
Author: Jin Jianzhi, Senior Lawyer at Shanghai Manqin Law Firm
The drama in the crypto industry is truly fascinating. Take, for instance, the recent clash between crypto security unicorn CertiK and U.S. super exchange Kraken—this one turned me into a watermelon field’s raccoon.
Here's how it unfolded: During its security testing, CertiK claimed to have discovered a critical vulnerability on Kraken’s platform that could allow malicious actors to artificially inflate cryptocurrency account balances. According to CertiK, their test aimed to trigger Kraken’s alert threshold system. However, Kraken responded by asserting that CertiK went far beyond legitimate security research and engaged in behavior resembling extortion—allegedly exploiting the flaw for personal gain.
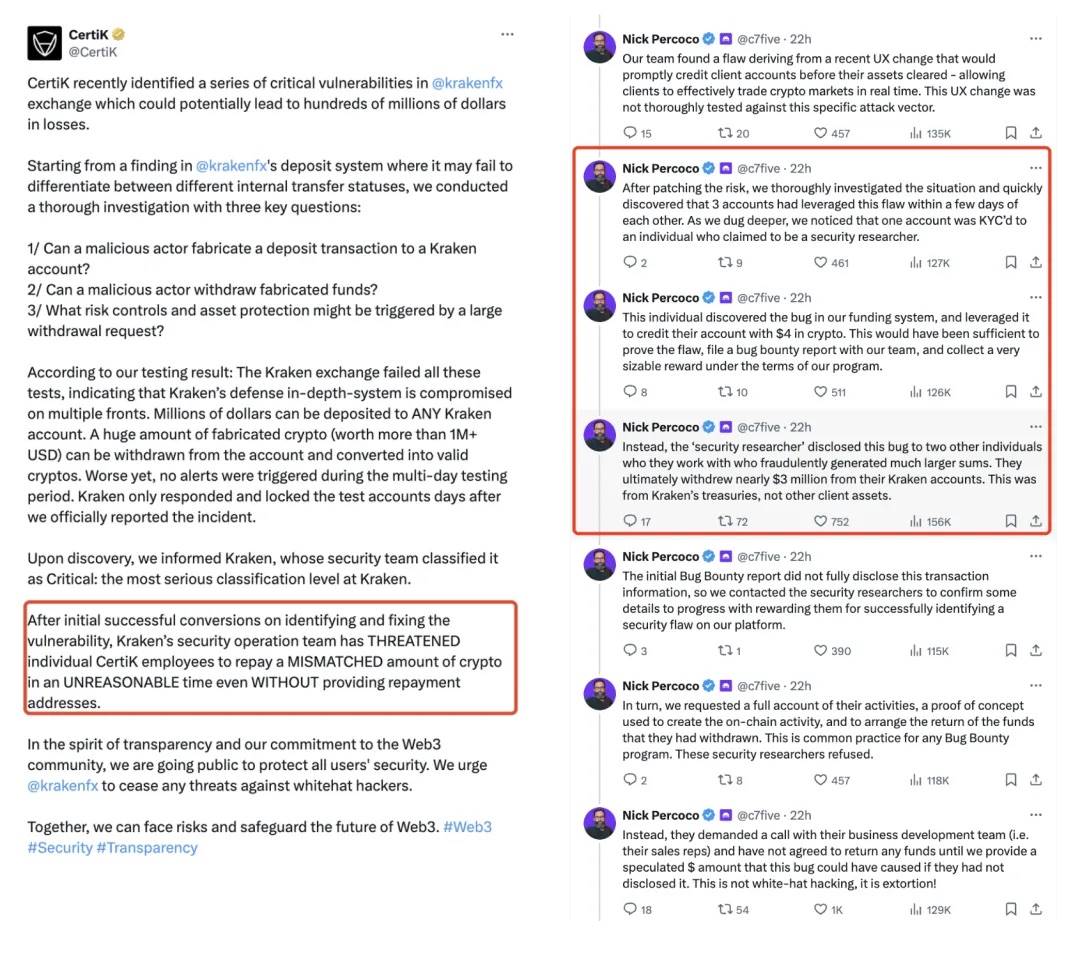
According to CertiK, their testing revealed multiple serious vulnerabilities within Kraken’s systems—flaws that, if left unpatched, could result in losses of hundreds of millions of dollars. CertiK emphasized that their actions were intended to enhance cybersecurity and protect user interests. They released a full timeline of events along with deposit addresses involved, claiming transparency and good faith.
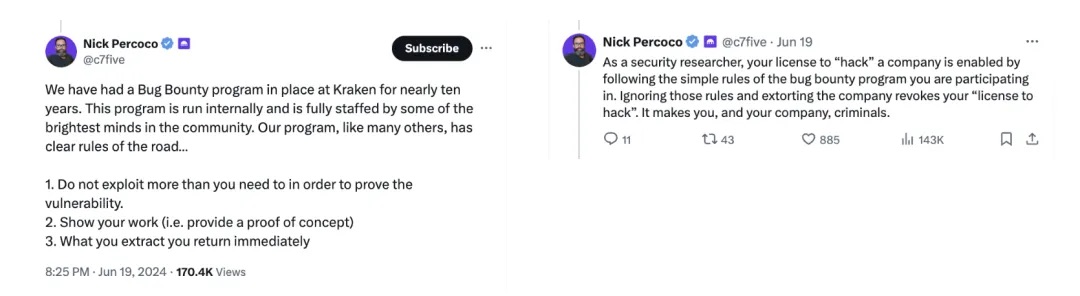
Kraken and its CSO Nick Percoco countered via social media and public statements, stressing that their bug bounty program has clear rules requiring all researchers to operate within defined boundaries. Kraken asserted that CertiK’s actions posed a direct threat to platform security and confirmed they had reported the incident to law enforcement authorities.
This standoff isn't just about technology and security—it touches on legal and ethical boundaries, particularly concerning the limits and responsibilities of white-hat hacking. This case offers rich context for Manqin lawyers to explore the legal parameters governing white-hat activities.
01 Are White-Hat Hackers Legally Protected?
Strictly speaking, the actions of white-hat hackers closely resemble illegal intrusion into computer systems. Yet, in most cases, such conduct is not legally treated as criminal activity. The intent and methodology behind white-hat operations fundamentally distinguish them from malicious cyberattacks.
On-chain white-hat hackers contribute positively by identifying and patching vulnerabilities, helping organizations build more secure environments, thereby enhancing overall network reliability and trustworthiness.
Does receiving compensation affect this assessment? Bounties serve as an effective incentive mechanism, attracting skilled individuals to focus on cybersecurity. For companies, paying bounties is often a cost-effective way to fix flaws while demonstrating commitment to security. Therefore, accepting reasonable rewards is generally accepted as standard industry practice.
02 In This Case, Was CertiK Acting as a White-Hat Hacker?
At the heart of the dispute between CertiK and Kraken lies the question of behavioral boundaries. Specifically, CertiK’s motives and legality regarding the transfer of $3 million to an external wallet have become central points of contention.
Lack of Transparency
CertiK is a known security partner of Kraken and was fully aware that Kraken operates a formal bug bounty program. It could—and should—have obtained explicit authorization before initiating any tests. Moreover, according to community disclosures and Kraken, when reporting the vulnerability, CertiK did not initially disclose the exact amount transferred. Only after Kraken demanded the return of "$3M" did CertiK reveal its “full list of test addresses,” attempting to prove it hadn’t moved the disputed sum.
Funds Were Moved—That’s a Fact
According to Kraken and blockchain investigator @0xBoboShanti, CertiK researchers began probing and testing as early as May 27—contradicting CertiK’s own timeline. More importantly, although CertiK claims these operations were meant only to test whether Kraken’s alert systems would trigger promptly, the reality goes beyond mere detection: funds were actually transferred to independent wallet addresses. Such action clearly exceeds acceptable bounds of standard security testing. Reports indicate CertiK has conducted similar transfers at several other exchanges, even using Tornado Cash for fund obfuscation and ChangeNOW for asset liquidation.
These two factors strongly suggest CertiK likely crossed the line of white-hat conduct.
03 Legal Framework Is Key
From a legal perspective, white-hat hacking is typically considered lawful—but only under specific conditions and proper authorization.
In the United States, the primary law governing such activities is the Computer Fraud and Abuse Act (CFAA). Under CFAA, accessing a protected computer without authorization—or exceeding authorized access—can constitute a criminal offense. Even if motivated by security concerns, white-hat hackers risk prosecution unless operating strictly within granted permissions. As technology evolves, some jurisdictions are developing more nuanced regulations to better define and protect responsible disclosure practices.
In China, the Cybersecurity Law sets broad requirements for strengthening cyber defenses and managing cyberspace. Unauthorized intrusions—even those conducted for security testing—are generally viewed as illegal. Additionally, the law emphasizes protection of personal data and privacy. Any handling of user data during testing must ensure confidentiality and integrity. Upon discovering a vulnerability, there is a legal obligation to promptly report it to both regulatory bodies and affected operators. This reporting framework aims to enable timely remediation and prevent exploitation.
In the Web3 space, certain white-hat activities involving fund movement are sometimes tolerated—especially when done under implicit or explicit project approval (e.g., through grants), or when funds are simply moved to isolated wallets without further use. Such practices are informally accepted within the industry.
However, in CertiK’s case, the actual movement of funds—and subsequent actions—raises complex legal questions. First, whether the fund transfer stemmed from private gain rather than pure testing intent. Second, whether CertiK disregarded Kraken’s clearly stated rules for ethical hackers by re-testing the same vulnerability through unauthorized fund movement. Third, whether post-transfer activities (like laundering or selling) amount to unlawful profit-taking. Furthermore, CertiK’s communication (or lack thereof) with Kraken following the incident also impacts the legal evaluation of its conduct.
04 Conclusion and Reflection
Although the Kraken-CertiK dispute is governed by U.S. law—and thus outside the scope of authoritative commentary by Chinese legal professionals—if this incident occurred under Chinese jurisdiction, CertiK’s actions would likely face charges of blackmail and illegal intrusion into computer information systems.
Indeed, white-hat hackers can sometimes “go black.” Even with noble initial intentions, conducting tests without proper authorization or leveraging discovered vulnerabilities for personal benefit crosses both legal and ethical lines. As demonstrated by the CertiK-Kraken saga, unauthorized fund transfers—especially involving large sums—can transform what might seem like a security exercise into behavior indistinguishable from black-hat attacks.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News