The “God’s Key” of DeFi: Examining DeFi’s Greatest Vulnerability Through the $285 Million Drift Hack
TechFlow Selected TechFlow Selected

The “God’s Key” of DeFi: Examining DeFi’s Greatest Vulnerability Through the $285 Million Drift Hack
Drift’s move has cut right into the industry’s most unwilling-to-face wound.
Author: TechFlow
April 1 — April Fools’ Day.
Drift Protocol, Solana’s largest perpetuals exchange, is being drained—and the community’s first reaction is: “Nice April Fools’ prank.”
This is not a prank. Around 1:30 p.m., on-chain monitoring accounts Lookonchain and PeckShield simultaneously sounded the alarm: an unfamiliar wallet beginning with “HkGz4K” was rapidly siphoning assets from Drift’s treasury. The first withdrawal: 41 million JLP tokens, worth $155 million. Then came $51.6 million in USDC, 125,000 WSOL, 164,000 cbBTC… Dozens of assets gushed out like water from a bathtub after the plug is pulled.
In one hour, treasury assets plummeted from $309 million to $41 million—over half the TVL, evaporated.
The Drift team posted a rare, urgent tweet on X: “Drift Protocol is under active attack. Deposits and withdrawals are suspended. We are coordinating with multiple security firms, cross-chain bridges, and exchanges to contain the situation.”
Then came the line destined for the annals of crypto history: “This is not an April Fools joke.”One Key, All Doors Opened
Estimates of Drift’s losses vary across sources. PeckShield pegs the figure at ~$285 million; Arkham reports over $250 million; CertiK’s preliminary assessment sits around $136 million. Regardless of the exact number, this is the largest DeFi security incident so far in 2026.
More noteworthy than the dollar figure is the attack vector.
PeckShield founder Jiang Xuxian told Decrypt plainly: the admin key behind Drift was “clearly leaked or compromised.” On-chain researchers pieced together a picture showing that the attacker gained privileged access to the Drift protocol—and thereby controlled the flow of funds from the treasury.
In other words, no sophisticated smart contract vulnerability exploitation, no flash loan attack, no oracle manipulation. Just the most basic, oldest security failure: someone lost their private key.
An even more unsettling detail: the attacker did not act impulsively. On-chain data shows this wallet received its initial funding via Near Intents eight days before the attack—and then lay dormant. One week before the breach, it even received a tiny $2.52 transfer from Drift’s treasury. A probe. A knock on the door.
A week later, the door was kicked open.The Fall of Crypto’s Robinhood
For Drift co-founder Cindy Leow, April 1’s nightmare carries an especially cruel undertone.
The story of this Malaysian-Chinese entrepreneur was once among Solana DeFi’s most inspiring narratives. Starting with Bitcoin arbitrage between China and South Korea in 2016, she ran a proprietary trading fund, contributed derivative projects on Ethereum, and co-founded Drift with David Lu in 2021—betting on Solana’s speed advantage to build on-chain perpetuals.
Chronologically, Drift rode nearly every wave. In 2024, it secured two funding rounds led by Polychain and Multicoin, totaling $52.5 million. It launched prediction markets to rival Polymarket, introduced 50x leverage, pushed TVL past $550 million, and surpassed $50 billion in cumulative trading volume. In a Fortune interview, Leow boldly positioned Drift as “Robinhood for crypto.”
That analogy now reads with bitter irony. Robinhood’s core promise is giving ordinary people access to Wall Street’s financial tools. Drift’s core promise was enabling users to trade on-chain in a “non-custodial” environment—where your money never passes through anyone’s hands, interacting only with code.
But behind that code lies an admin key. And the security of that key ultimately depends not on cryptography—but on humans.
There’s another jarring historical coincidence: in 2022, during Drift v1, the treasury was drained in a prior incident. The team published an exceptionally detailed technical report—even releasing proof-of-concept code demonstrating how an attacker could empty the entire treasury in a single transaction. That incident cost $14.5 million; the team covered all user losses out of pocket.
Four years later, the same nightmare replayed—on a scale 20 times larger.Decentralized Faith, Centralized Weakness
Zooming out from Drift reveals an uncomfortable pattern taking shape.
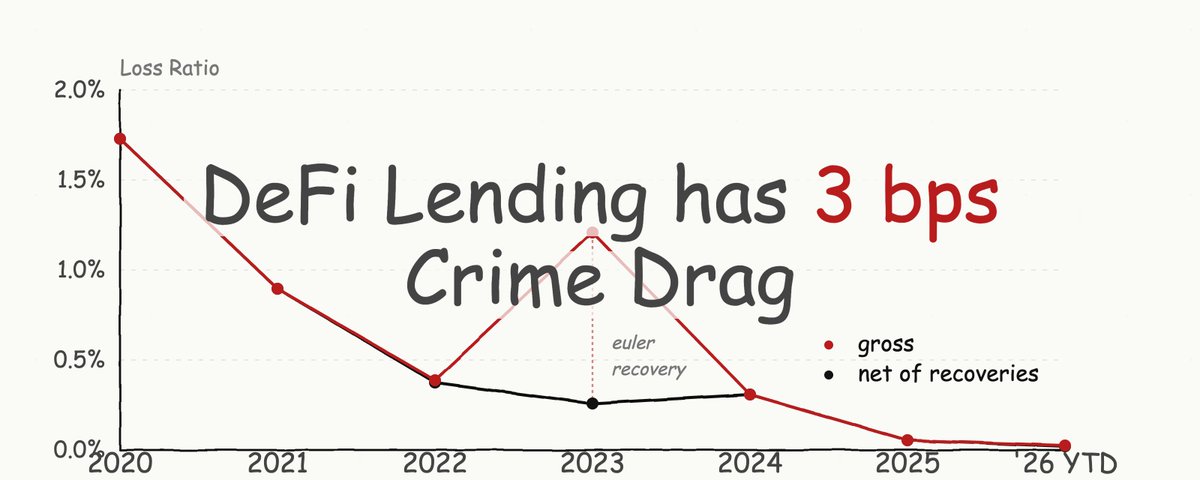
In early 2025, Resolv Labs’ AWS Key Management Service was breached; attackers used privileged keys to authorize massive minting of the USR stablecoin, triggering cross-platform cascading losses. Later that year, total crypto theft hit a record $3.4 billion, according to Chainalysis—which highlighted a pivotal shift in its report: the most destructive incidents now occur at the infrastructure layer. Compromised developer machines, single minting keys stored in the cloud, social-engineering–phished signing processes—these are the real black holes swallowing funds.
Now add Drift to that list.
Lay these cases side-by-side, and one conclusion becomes nearly inescapable: private key security has supplanted smart contract vulnerabilities as DeFi’s greatest systemic risk.
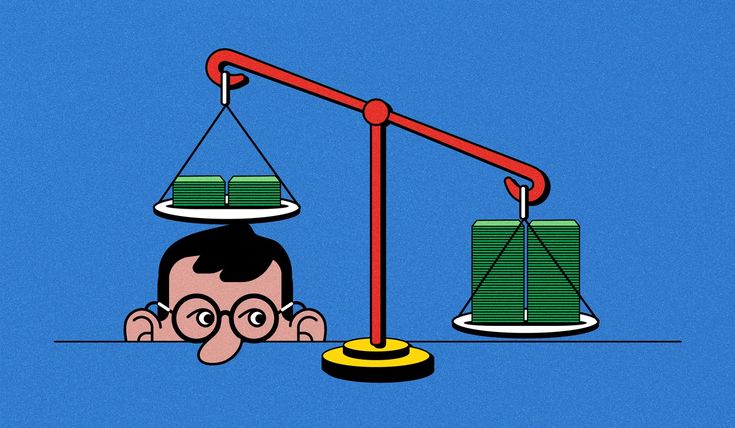
There’s a cognitive gap here—one wide enough to swallow billions of dollars.
DeFi protocols tell a story of “decentralization,” “non-custodianship,” and “trustlessness.” Your assets are held by code; no intermediary can touch your money. Users internalize this narrative, depositing funds into these protocols with the quiet confidence that they’re “dealing with math.”
Reality is different. Nearly every live DeFi protocol holds one or more “God keys”—admin keys, upgrade permissions, treasury control rights, emergency pause switches. These keys exist sometimes for safety (to apply emergency brakes), sometimes for flexibility (to upgrade logic)—but their essence is identical: a centralized point of trust, wrapped in decentralized storytelling.
Users think they’re interacting with code. In truth, they’re trusting one person—or a small group—not to err, not to get phished, not to be coerced, not to leave their laptop unattended in a café.
This isn’t Drift’s unique problem—it’s DeFi’s structural contradiction.Where Did the $285 Million Go?
The attacker’s on-chain moves were clean, precise—and chillingly professional.
After draining assets from Drift’s treasury, the attacker swiftly swapped most tokens for stablecoins, then routed the funds to Ethereum via the Wormhole bridge. On Ethereum, part of the stablecoins were used to purchase ~19,913 ETH (worth ~$42.6 million); the rest was dispersed across multiple wallet addresses.
One absurd detail: the attacker’s wallet still holds large amounts of Fartcoin—roughly 2.5% of its total supply. A hacker who just pulled off the year’s largest DeFi heist, clutching meme coins named after flatulence.
As of publication, deposits and withdrawals remain suspended on Drift. The DRIFT token has fallen from ~$0.072 pre-attack to ~$0.05—a drop of over 28%. From its all-time high of $2.60, its cumulative decline exceeds 98%. Phantom Wallet now displays a warning to users attempting to access Drift.
The Drift team says it’s coordinating with security firms, cross-chain bridge operators, and centralized exchanges to freeze and trace stolen funds. But if history offers any guidance, recovering funds transferred across bridges and scattered across multiple wallets remains highly unlikely.A Question the Industry Must Face Honestly
Drift’s breach cuts deep into the industry’s most avoided wound.
In its end-of-2025 report, Chainalysis optimistically declared that DeFi security had made “substantial progress”: even as TVL doubled back to $119 billion, DeFi-related losses declined. Venus Protocol was cited as a success story—the security monitoring system detected anomalies 18 hours before the attack, the protocol paused operations promptly, governance froze the attacker’s funds, and the attacker even lost money.
Drift punctures that “progress narrative.” You can conduct exhaustive smart contract audits; you can deploy state-of-the-art on-chain monitoring—but if an admin key falls to social engineering, phishing, or brute force, all your security infrastructure collapses like a fortress built on sand.
The DeFi industry must pause—and answer one question honestly: When you tell users “non-custodial,” what exactly do you mean?
If a protocol’s admin key can instantly move all assets in the treasury, what’s the real difference between that and depositing your money into a bank account held by someone you’ve never met? At least banks offer insurance, regulation, and legal recourse.
The answer may not be eliminating admin privileges—they’re often necessary. But at minimum, the industry must stop pretending they don’t exist. Multi-signature governance, timelocks, hardware security modules, key rotation—these solutions have existed for years. Yet too many protocols still tether hundreds of millions of dollars in security to the vigilance of one or two human operators.
The dream of a “Robinhood for crypto” is compelling. But before realizing it, perhaps we should first answer a more fundamental question: Who holds the key?
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News