Using the Bucket Theory to Break Down Bitcoin and Ethereum Layer2 Security Models and Risk Indicators
TechFlow Selected TechFlow Selected

Using the Bucket Theory to Break Down Bitcoin and Ethereum Layer2 Security Models and Risk Indicators
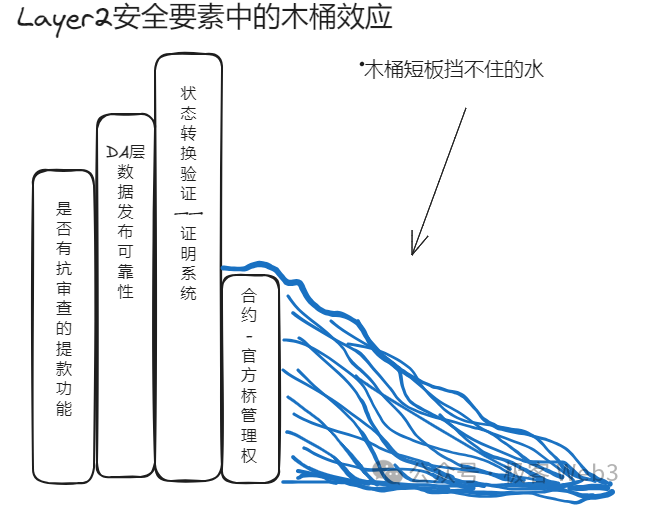
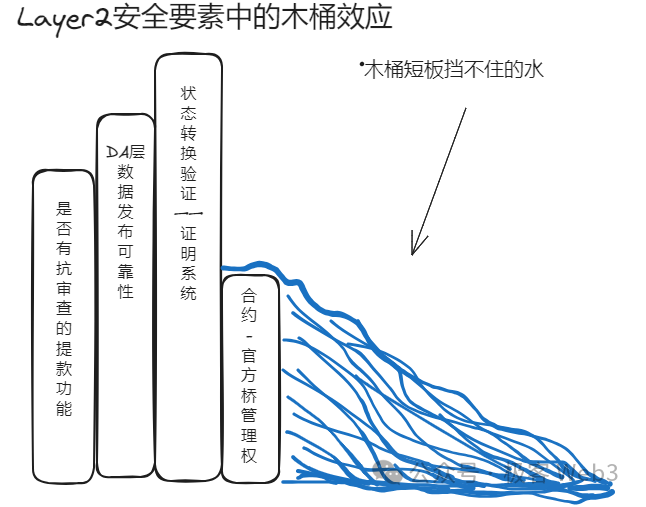
When discussing a complex system with multiple modules, we must first identify which part is the "shortest plank."
Authors: Faust & Wuyue, Geek Web3
Advisor: Kevin He (@0xKevinHe), VP of Technology at Xinhuo Tech
Introduction: American management scholar Laurence J. Peter once proposed the "Bucket Theory," which states that a system's overall performance is limited by its weakest component. In other words, how much water a bucket can hold is determined by its shortest stave. This principle may be simple, but it is often overlooked. Previous debates about Layer2 security have largely ignored the varying priorities and significance among different components, focusing almost exclusively on state transition reliability and data availability (DA), while neglecting deeper, more fundamental factors—undermining the very foundation of such theories. Therefore, when analyzing complex multi-module systems, we must first identify the “shortest stave.”
Inspired by the Bucket Theory, our systematic analysis reveals clear dependency relationships among components in Bitcoin/Ethereum Layer2 security models—some being more foundational and critical than others, i.e., the “shorter” ones.
Based on this, we propose an initial prioritization of the importance/foundational nature of various components within mainstream Layer2 security models:
-
Whether control rights over contracts/official bridges are properly decentralized (how centralized is multisig control)
-
Whether there is censorship-resistant withdrawal functionality (forced withdrawals, escape hatches)
-
Whether the DA layer/data publication method is reliable (whether DA data is published on Bitcoin or Ethereum)
-
Whether a reliable fraud proof or validity proof system is deployed on Layer1 (Bitcoin L2s require BitVM)
We should moderately absorb Ethereum community research on Layer2 and avoid Lysenkoism
Compared to the highly structured Ethereum Layer2 ecosystem, Bitcoin Layer2 feels like uncharted territory—a concept gaining increasing importance after the Ordinals boom. While showing signs of growth, its ecosystem has become increasingly chaotic, with Layer2 projects sprouting up like mushrooms after rain. While bringing hope to Bitcoin’s ecosystem, many deliberately conceal their security risks, with some even claiming “reject Ethereum Layer2, take a unique path for Bitcoin,” trending toward extremism.
Given functional differences between Bitcoin and Ethereum, Bitcoin Layer2s are inevitably unable to align perfectly with Ethereum Layer2s in early stages—but this does not justify outright rejection of widely accepted industry standards established by Ethereum and modular blockchain communities (analogous to the “Lysenko affair” in the former Soviet Union, where biologist Trofim Lysenko used ideology to suppress Western genetics).
On the contrary, these evaluation criteria, painstakingly developed by predecessors and widely recognized, have demonstrated strong credibility. Deliberately dismissing them is simply irrational.
While building Bitcoin Layer2, we must fully recognize the value of “learning from the West for Eastern use,” thoughtfully absorbing and optimizing conclusions from the Ethereum community. However, when borrowing ideas beyond Bitcoin’s native ecosystem, we must acknowledge differing starting points and ultimately seek common ground while respecting differences.
This is akin to discussing similarities and differences between “Westerners” and “Easterners.” Regardless of origin, the suffix “person” implies many shared traits; only the prefixes “Western” or “Eastern” lead to variations in specific characteristics.
Ultimately, overlaps between “Westerners” and “Easterners” mean many things applicable to one also apply to the other—similarly, many principles valid for “Ethereum Layer2” also apply to “Bitcoin Layer2.” Before distinguishing their differences, clarifying shared fundamentals may be far more meaningful.
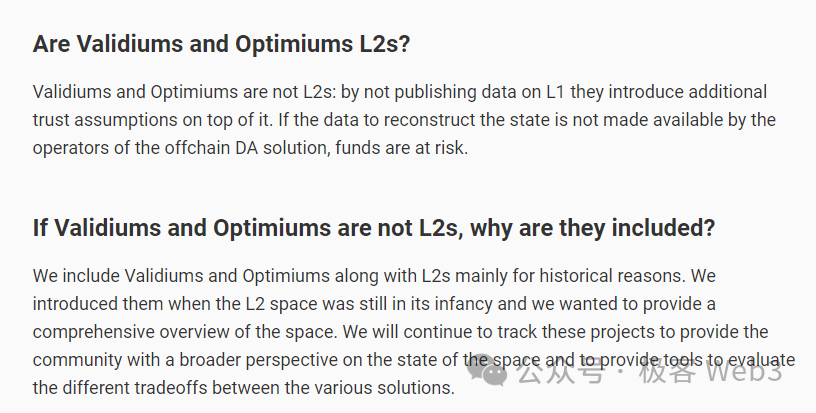
Guided by the principle of seeking common ground while preserving differences, this article does not attempt to define what qualifies as a Bitcoin Layer2 versus what does not, as this topic remains highly contentious—even within the Ethereum community, no objective consensus exists on which solutions qualify as true Layer2s.
What is certain is that while various technical approaches offer scalability benefits to Bitcoin, they carry distinct security risks. The trust assumptions embedded in their security models will be our primary focus here.
Understanding Layer2 Security and Evaluation Criteria
Layer2 security is not a new topic, nor is the term “security” itself—it encompasses multiple sub-attributes.
Previously, the founder of EigenLayer simplified “security” into four elements: transaction irreversibility (anti-rollbacks), censorship resistance, data availability (DA)/data publication reliability, and state transition validity.

(The founder of EigenLayer shared views on how client-side verification/sovereign rollup schemes inherit Bitcoin mainnet security)
L2BEAT and veteran Ethereum community members have proposed relatively systematic Layer2 risk assessment frameworks—though primarily designed for smart contract-based Layer2s, not sovereign rollups or client-verified non-smart-contract models.
While not 100% applicable to Bitcoin L2s, these frameworks contain valuable insights broadly accepted in Western communities, providing useful benchmarks for objectively evaluating risks across different Bitcoin L2s.
(Vitalik noted that because Rollup solutions cannot achieve theoretical perfection during early deployment, auxiliary mechanisms—called “training wheels”—are required, introducing trust assumptions. These trust assumptions represent risks)
Where do these security risks originate? Currently, both Ethereum and Bitcoin Layer2s often rely on centralized sequencers or small committees operating sidechain-style nodes. If unchecked, these increasingly centralized sequencers/committees could steal user assets and run away at any time, reject transactions, freeze funds, etc. This relates directly to the state transition validity and censorship resistance highlighted earlier by EigenLayer’s founder.
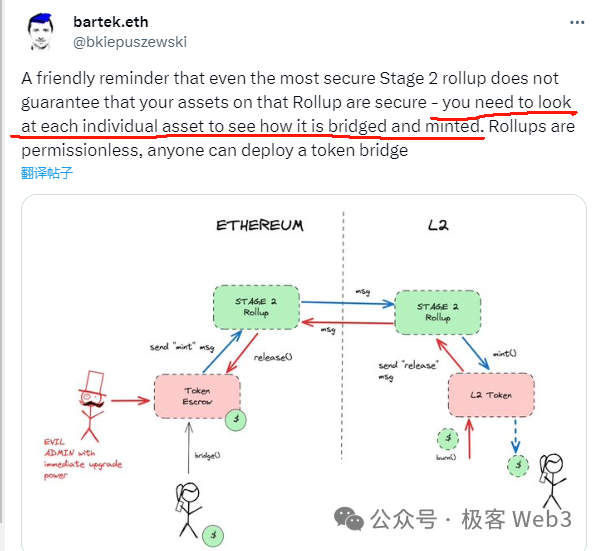
Additionally, since Ethereum Layer2s depend on ETH-chain contracts for state validation and deposit/withdrawal verification, if contract controllers (i.e., Layer2 teams) can rapidly upgrade logic and inject malicious code (e.g., allowing a designated address to drain all tokens locked in the L1-L2 bridge contract), they can directly steal custodied assets.
This falls under the “multisig distribution issue,” which equally applies to Bitcoin Layer2s, as Bitcoin L2s typically rely on “custodian bridges” requiring multiple nodes to approve cross-chain requests via multisig. Thus, Bitcoin L2s face similar questions about fair multisig allocation—we might even view this as the most fundamental “training wheel” in Bitcoin Layer2 architecture.
Moreover, DA issues are extremely important. If a Layer2 fails to publish data on Layer1 and instead uses unreliable off-chain DA layers, collusion within such DACs (Data Availability Committees) could withhold latest transaction data, leading to data withholding attacks that render networks unusable and potentially prevent withdrawals.
L2BEAT summarized these concerns, identifying several core elements in Layer2 security models:
-
Reliability of state validation/proof systems (State Validation)
-
Reliability of DA data publication methods (Data Availability)
-
If the Layer2 network deliberately rejects your transactions or goes offline, can you forcibly withdraw assets from Layer2? (Sequencer Failure, Proposer Failure)
-
Is control over Layer2-related contracts—the official cross-chain bridge—sufficiently decentralized? If concentrated, do users have enough time to react in case of insider theft? (Exit Window)
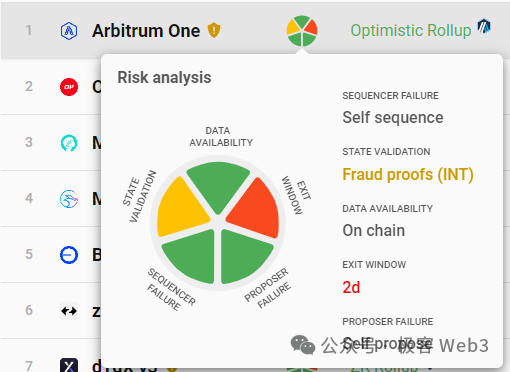
(Risk factor visualization for various Layer2 projects on L2BEAT)
Anyway, analyzing Layer2 security essentially means examining how many scenarios exist where user assets could be compromised, and whether the system’s design effectively constrains such threats. When malicious behaviors cannot be entirely prevented, we must assess how much “trust” is required—how many individuals in a group we must trust, and how many “training wheels” we depend on.
Below, we analyze risk factors present in general Ethereum/Bitcoin Layer2 models (excluding “state channels” or “payment channels,” as well as inscription indexing protocols due to their special nature). We’ll also explore which factors are more foundational, lower-level, and thus represent greater trust risks than others.
The Bucket Effect in Layer2—What Are the Shortcomings?
The Shortest Stave—Contract / Official Bridge Control Rights
Applying the Bucket Theory to Layer2 security, it becomes evident that the shortest stave is the previously mentioned “contract upgradability” (mainly concerning Ethereum Layer2), or more broadly, “control over official cross-chain bridges” (applicable to both Bitcoin and Ethereum Layer2s).
For Ethereum Layer2s, if the team can quickly upgrade contracts on Layer1, they could theoretically steal tokens locked in the L2 bridge address regardless of how robust the DA layer or proof system is.
Bridge contract control rights determine the entire system’s safety—they are the most fundamental and critical part of any Layer2 or modular blockchain stack. If bridge components/contracts can be updated under multisig control, we must introduce a trust assumption: assuming the Layer2 contract/bridge operators won’t act maliciously.
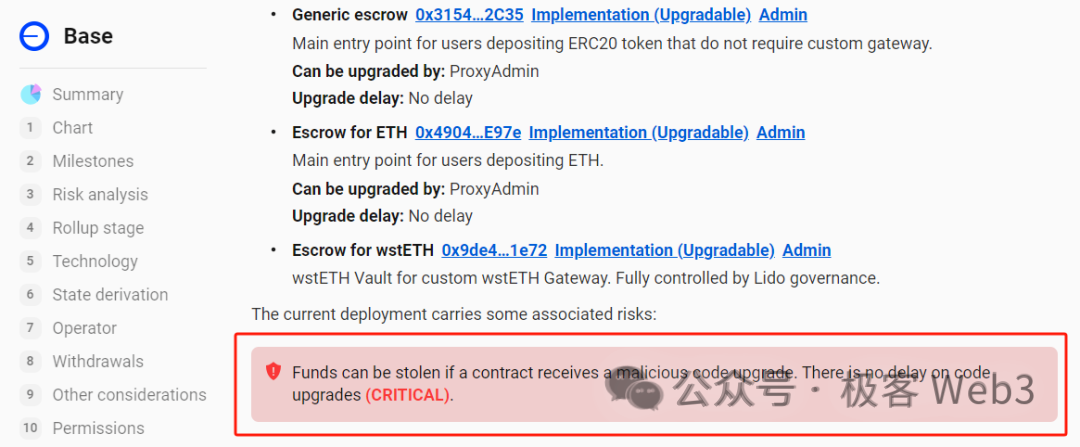
(L2BEAT notes upgrade delays for various Layer2 project contracts; most can be upgraded immediately by controllers—if they attempt theft or lose keys to hackers, user assets are doomed)
Unlike Ethereum Layer2s, Bitcoin Layer2 bridges aren't controlled by Layer1 smart contracts, since Bitcoin doesn’t support them natively. Ethereum Layer2 workflows heavily rely on Layer1 contracts, whereas Bitcoin Layer2s cannot.
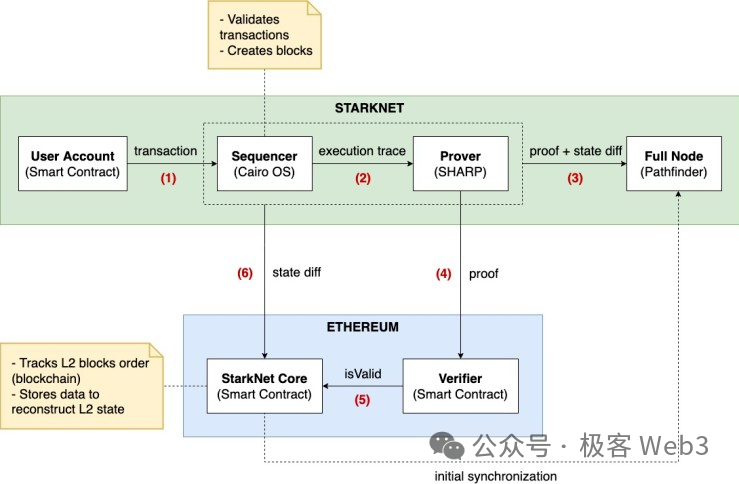
(Starknet schematic)
For Bitcoin Layer2s, this presents unavoidable trade-offs—both advantages and disadvantages. Currently, the “trustless bridges” enabled via Ethereum Layer1 contracts cannot be replicated on Bitcoin L2s. Such “Trustless Bridges” require dedicated Layer1 contracts plus coordination with DA and fraud/ZK proof systems, essentially functioning like Orbiter’s “optimistic bridge” or Polyhedra’s ZK bridge.
The current industry consensus is that, ignoring potential bugs, optimistic and ZK bridges offer top-tier security—effectively trustless provided code contains no vulnerabilities and cannot be maliciously upgraded.
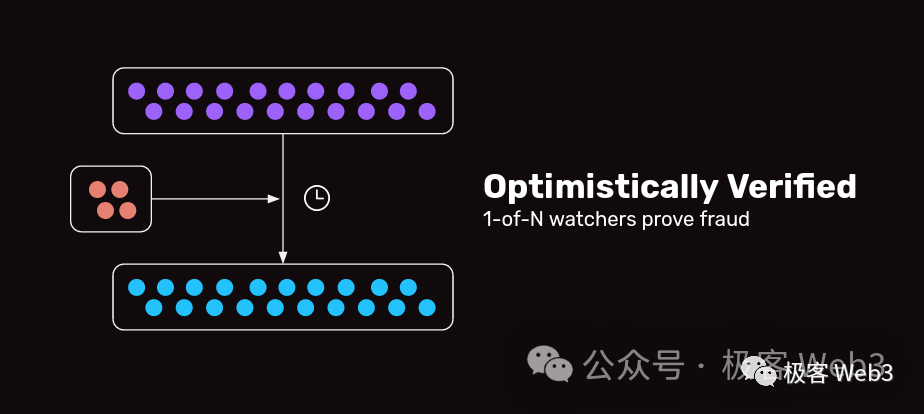
(Optimistic bridges only need one honest watcher among N to ensure security—trust model is 1/N)
Since Bitcoin Layer2s cannot deploy contract components on Layer1 (excluding Lightning Network), their official bridges are mostly “custodian bridges” or “multisig bridges” formed by a few nodes. Their security depends on multisig/threshold signature configurations, requiring strong trust assumptions: assuming custodians won’t collude or have their private keys stolen.
Currently, most custodian/threshold-signature bridges cannot match the security level of Ethereum Layer2 “trustless bridges” (assuming Ethereum Layer2 contracts aren’t maliciously upgraded). Clearly, the security of assets held in Bitcoin Layer2 networks hinges on the security of their official bridges—or the decentralization of multisig bridge authority—this constitutes their first “training wheel.”
Since upgrade privileges for Ethereum Layer2 bridge contracts often reside with a small set of multisig holders, if those signers collude, even Ethereum Layer2 bridges can fail—unless contracts are immutable or subject to long delay periods (currently only Degate and Fuel V1 meet this standard).
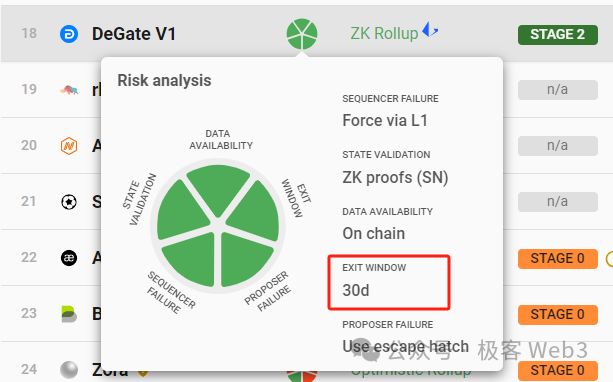
(Degate provides users a 30-day safe exit window for each contract upgrade—during which users detecting malicious logic can safely escape via forced withdrawals/escape hatch)
Regarding “official bridges,” Ethereum and Bitcoin Layer2s share similar trust models: trusting multisig controllers won’t collude maliciously. This group controls the L2 bridge, either altering its logic or approving invalid withdrawals—either way risking user asset loss.
The only difference is that Ethereum Layer2 bridges become trustless if contracts aren’t maliciously upgraded or have sufficiently long upgrade windows, whereas Bitcoin Layer2s cannot achieve this under any circumstances.
The Second-Shortest Stave—Censorship-Resistant Forced Withdrawals
Assuming the previously discussed multisig/bridge control issues are resolved—that layer poses no threat—then the next most critical aspect becomes censorship resistance in withdrawals.
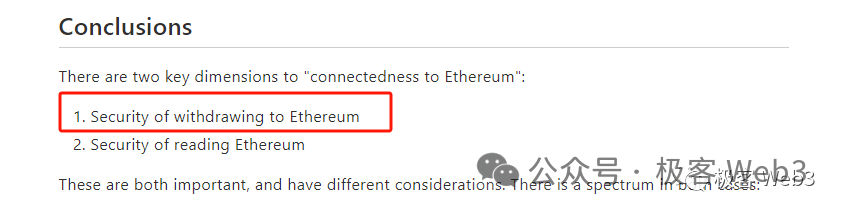
As Vitalik emphasized months ago in his article “Different types of layer 2s,” whether users can successfully withdraw assets from Layer2 back to Layer1 is a crucial security metric.
If a Layer2 sequencer continuously rejects your transaction requests or suffers prolonged downtime, your assets become “frozen” and unusable. Even with functional DA and fraud/ZK proof systems, lacking censorship resistance makes the Layer2 fundamentally insecure—your assets can still be held hostage.
Furthermore, Plasma, once popular in the Ethereum ecosystem, allows anyone to securely withdraw assets to Layer1 when DA or fraud proofs fail. At that point, the entire Layer2 network is effectively dead, yet users can still retrieve their funds. Clearly, censorship-resistant withdrawal functionality is more foundational and lower-level than DA or proof systems.
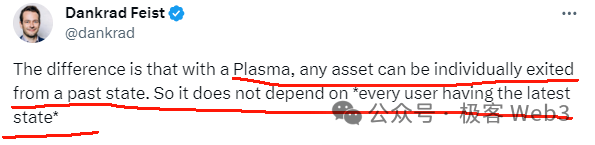
(Dankrad from Ethereum Foundation stated Plasma allows users to safely evacuate assets even if DA fails or users cannot sync latest data)
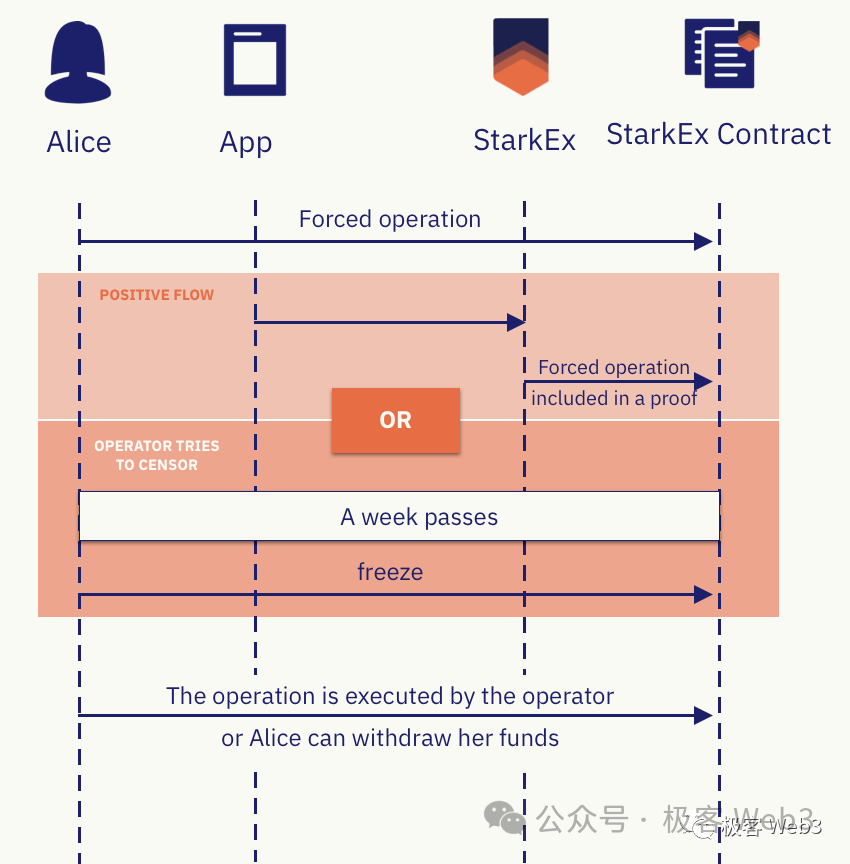
Some Ethereum Layer2s, including Loopring, StarkEx, dYdX, and Degate, implement anti-censorship forced withdrawal/escape hatch activation functions on Layer1. For example, in Starknet, if a user submits a Forced Withdrawal request on Layer1 and receives no response from the Layer2 sequencer within a 7-day window, they can manually invoke the freezeRequest function to freeze the L2 and activate escape mode.
At this point, the sequencer cannot submit data to the Rollup contract on L1, freezing the entire Layer2 for one year. Then, users can submit Merkle proofs demonstrating their Layer2 asset state and directly withdraw equivalent funds from Layer1 (essentially retrieving their share from the official bridge deposit address).
Clearly, escape hatch mechanisms can only be implemented on chains supporting smart contracts like Ethereum; Bitcoin cannot execute such complex logic. In other words, escape hatches are essentially an Ethereum Layer2 exclusive feature. Bitcoin Layer2s must resort to additional auxiliary measures to imitate this functionality—constituting the second “training wheel.”
However, merely declaring a “forced withdrawal request” is significantly simpler than activating a full escape hatch. The former only requires users to send a transaction to a designated address on Layer1, embedding within the calldata the data intended for all Layer2 nodes (bypassing the sequencer to communicate requests directly to other Layer2 nodes). If “forced withdrawals” go unanswered for too long, users can then trigger escape mode—an arguably more rational design.
(Reference: How Important Are Forced Withdrawals and Escape Hatches for Layer2?)
Currently, some Bitcoin Layer2 teams plan to mimic Arbitrum’s forced transaction mechanism, allowing users to publish forced transaction envelopes on the Bitcoin chain. With this approach, users can bypass the sequencer and directly “voice” their demands to other Layer2 nodes. If the sequencer continues rejecting requests despite seeing the envelope, other nodes will detect this and may impose penalties.
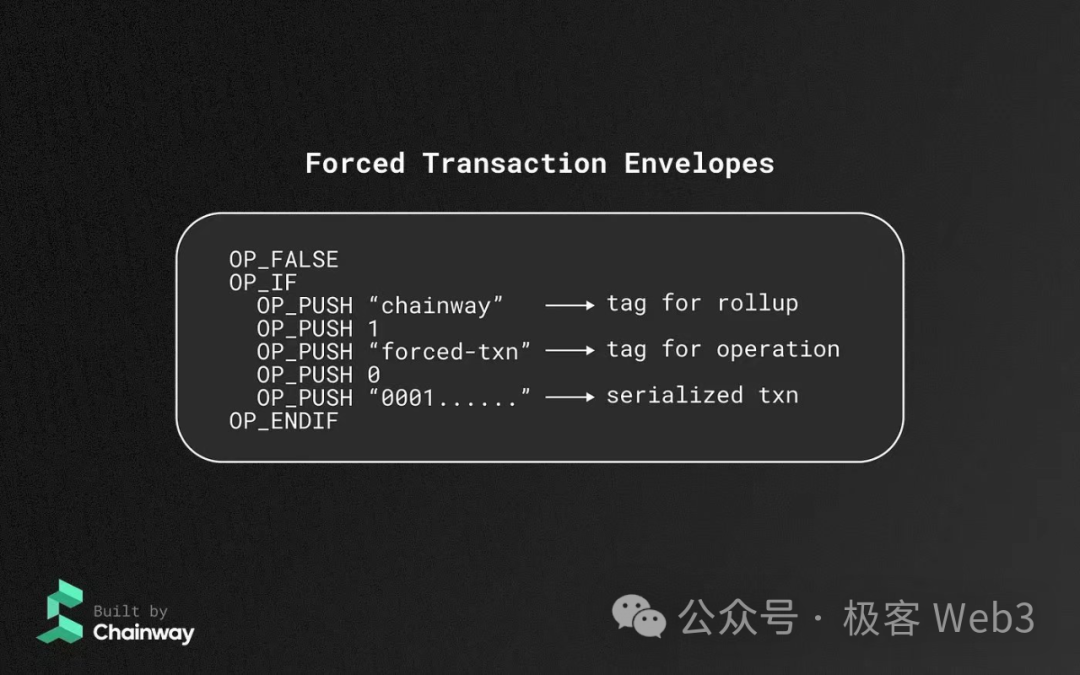
The challenge lies in the fact that Arbitrum’s forced transaction capability relies on its fraud proof system to penalize proposers who ignore user transactions. For Bitcoin Layer2s, where fraud proofs are difficult to verify on Layer1, implementing similar enforcement poses significant challenges. (Setting aside BitVM for now) For sovereign rollups whose security resembles client-side verification, reliability assessments remain difficult without examining implementation details per project.
Of course, given that many current Bitcoin Layer2s operate similarly to sidechains—achieving decentralized sequencing—they partially mitigate censorship issues. But this is only a supplementary measure, certainly not a final solution.
PS: Some current Layer2 designs, such as Validium, lack robust escape hatch mechanisms—when data withholding attacks occur or DA becomes unavailable, users may be unable to withdraw. This stems from inadequate escape hatch design. Theoretically, optimal escape withdrawals should depend solely on historical data, independent of DA/new data availability.)
The Third-Shortest Stave: Reliability of DA Layer Data Publication
Although called Data Availability (DA), the term actually refers to data publication. It was poorly named initially by Vitalik and Mustafa without careful consideration, resulting in the misnomer “DA” or “data availability.”
Data publication, by definition, refers to whether the latest block/transaction data/state transition parameters can be reliably received by interested parties. Publishing data on different chains varies in reliability.
(Reference: Misconceptions About Data Availability: DA = Data Publication ≠ Historical Data Retrieval)
The Western community generally agrees that legacy public chains like Bitcoin and Ethereum are the most trust-minimized DA layers. If a Layer2 sequencer publishes new data on Ethereum, anyone running an Ethereum geth client can download and sync that data with virtually no obstruction, thanks to Ethereum’s massive network scale and abundant public data sources.
Notably, Ethereum Rollups mandate that sequencers publish transaction data/state transition parameters on Layer1—enforced through validity or fraud proof systems.
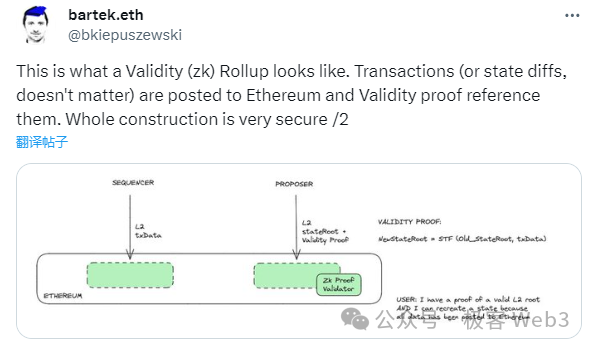
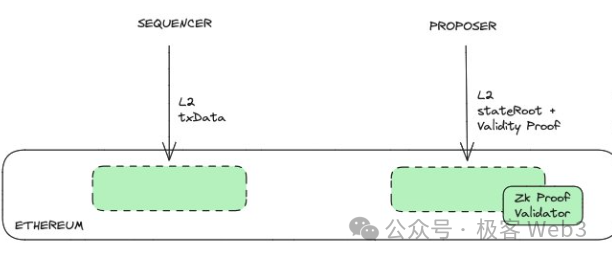
For instance, after a ZK Rollup sequencer publishes transaction data on Layer1, a dataHash is generated in the contract logic. The verifier contract checks that the proposer-submitted validity proof corresponds to this dataHash.
This ensures that the state transition data/DA is forcibly published on-chain. Submitting only stateroot and validity proof would fail verification.
This guarantees tight coupling between state transition data/DA and proof verification—if only stateroot and validity proof were submitted, verification would fail.
The Ethereum/Celestia communities have thoroughly debated whether DA data publication or proof verification is more fundamental. The prevailing conclusion is: the reliability of the DA layer is more important than the completeness of fraud/validity proof systems. For example, Plasma, Validium, Optimium—where DA resides off-Ethereum while settlement occurs on Ethereum—are vulnerable to “data withholding attacks,” meaning:
Sequencers/Proposers can collude with off-chain DA nodes to update stateroot on Layer1 while withholding input parameters needed to validate that stateroot, leaving outsiders blind to its correctness.
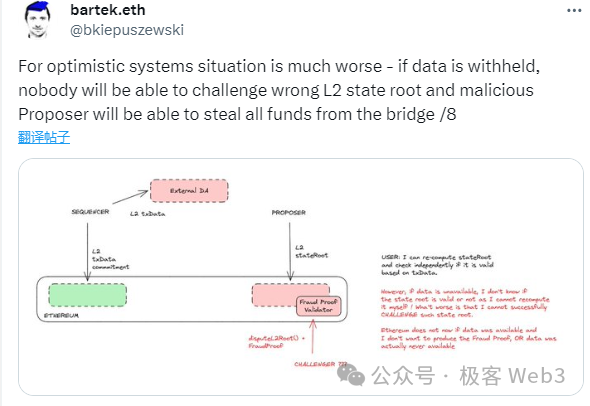
When this happens, the entire Layer2 network becomes unusable, as no one knows what the ledger truly looks like. On fraud-proof-based Layer2s (Plasma, Optimium), the sequencer can arbitrarily alter account balances; on validity-proof-based Layer2s (Validium), though accounts can’t be freely rewritten, the network becomes a black box—indistinguishable from failure. Hence, canonical Ethereum Layer2s are mostly Rollups, while Validium and Optimium are generally not endorsed by the Ethereum Foundation.
(Reference: Data Withholding and Fraud Proofs: Why Plasma Doesn’t Support Smart Contracts)
Therefore, the reliability of the DA layer—the accessibility of state transition parameters—is more important and foundational than the completeness of fraud/validity proof systems. For Bitcoin Layer2s, especially those based on client-side verification, even without a Layer1 fraud/validity proof verification system, as long as the DA layer functions normally, participants can still detect erroneous state transitions.
Currently, Bitcoin mainnet struggles to verify fraud/validity proofs (again excluding BitVM), so assume Bitcoin L2s lack proof verification systems. Under ideal conditions, if an L2 sequencer acts maliciously and publishes a stateroot on the settlement layer/BTC unrelated to DA data, it still cannot truly steal user assets—because its unilaterally submitted stateroot/state transition result won’t be accepted by honest nodes, rendering it ineffective.
(As long as exchange and bridge operators running nodes don’t collude with the sequencer, the latter cannot quickly monetize stolen assets through falsified data. Eventually, if just one honest node detects anomalies and raises an alarm, social consensus can correct errors—but social consensus is costly and not instantly effective.)
In sidechain-like models, if most nodes collude to execute malicious state changes, problems can be spotted quickly. As long as third-party infrastructure like bridges and exchanges refuse to accept false data, malicious Layer2/sidechain controllers cannot cash out, unless they convince others to engage in direct OTC trades on-chain.

(Vitalik once wrote that client-side verification is the true foundation of blockchain security—Verify by yourself)
An interesting point: both Ethereum and Bitcoin Layer2s can implement “client-side verification.” But Ethereum Layer2s build upon this with Layer1 and proof systems to guarantee state transition validity, minimizing reliance on social consensus (provided mature fraud/validity proof systems exist).
Bitcoin Layer2 “client-side verification” schemes, however, heavily rely on social consensus, introducing corresponding risks (for Bitcoin L2s, such risks are generally manageable but could still cause individual losses; for Ethereum L2s, since official bridges require proof system coordination, incomplete proof systems allow sequencers to steal assets and withdraw to L1. Specific outcomes depend on bridge design).
Thus, a Layer2 capable of verifying fraud/validity proofs on Layer1 is inherently superior to pure “client-side verification” models.
PS: Most Bitcoin Layer2s using fraud/validity proof systems cannot involve Layer1 directly in verification—making them functionally equivalent to “client-side verification” models, using Bitcoin merely as a DA layer.
Theoretically, BitVM could enable fraud proof verification on Bitcoin, but engineering challenges are immense. Given extensive prior discussion in the Ethereum community about Layer1-based proof verification—now widely known—this article won’t elaborate further on such systems.
Conclusion
Through a simple bucket model analysis, we reach a preliminary conclusion: in mainstream Layer2 security models, components can be ranked by importance/foundational nature as follows:
-
Whether contract / official bridge control rights are reasonably decentralized
-
Whether censorship-resistant withdrawal functionality exists
-
Whether the DA layer / data publication method is reliable
-
Whether a reliable fraud proof / validity proof system is deployed on Layer1
Of course, we did not analyze Lightning Network/state channels, ckBTC in ICP ecosystems, or inscription indexing protocols, as they differ significantly from typical Rollup, Plasma, Validium, or client-verified models. Due to time constraints, a thorough assessment of their security and risk factors remains pending—yet given their significance, future evaluations are inevitable.
Meanwhile, debate persists among project teams regarding whether inscription indexing protocols qualify as Layer2s. Regardless of definitional disputes, such innovations bring substantial technological advancement to the Bitcoin ecosystem and will ultimately unleash tremendous vitality.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News