Fully Homomorphic Encryption Research: Computing Without Decryption—What Changes Will It Bring to Web3?
TechFlow Selected TechFlow Selected

Fully Homomorphic Encryption Research: Computing Without Decryption—What Changes Will It Bring to Web3?
FHE is the holy grail of computing; value and computation are transitioning toward open, permissionless networks, and FHE will underpin most of the required infrastructure and applications.
As the market falls silent during a bear cycle, investors and project teams inevitably begin searching for new growth opportunities.
In the absence of sustained hot topics, this quiet period presents an ideal chance to explore and deeply understand emerging technologies—technologies that may become the core of the next market narrative.
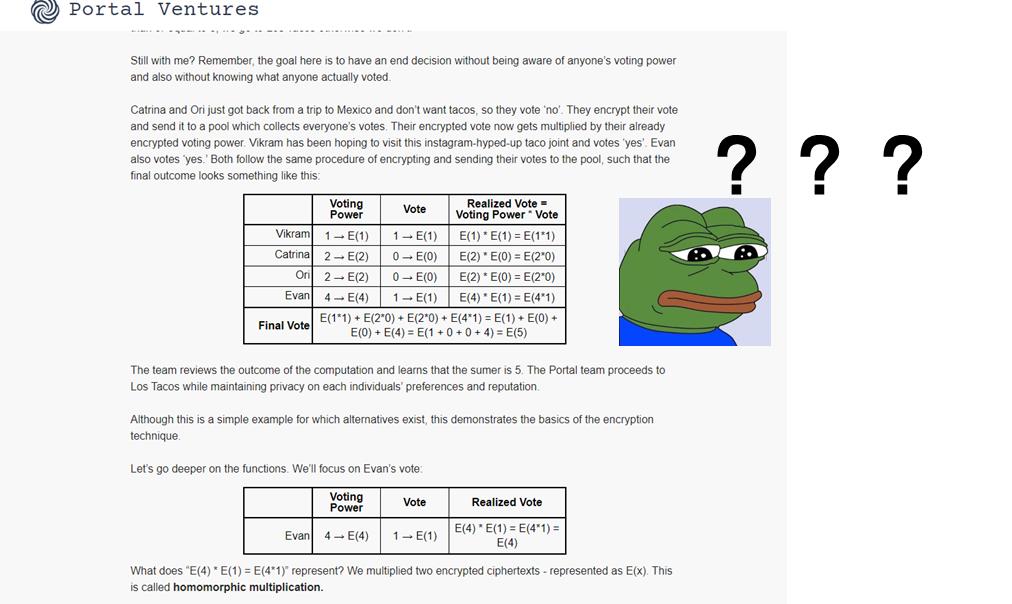
Last month, prominent crypto venture firm Portal Ventures published a detailed article on fully homomorphic encryption (FHE) on its official blog. However, this in-depth technical piece seems to have attracted little mainstream attention.
The authors at Portal Ventures stated: "Fully homomorphic encryption is the holy grail of cryptographic schemes."
Understanding the technologies that VCs are focusing on is crucial for investors, as it helps us anticipate and interpret potential trends in the next market cycle. Indeed, technologies such as homomorphic encryption, zero-knowledge proofs, and secure multi-party computation all have profound implications in cryptography, with FHE in particular holding immense application potential in cryptocurrency and Web3.
Yet the problem remains: most people know very little about what FHE truly means, how it works, or how it differs from other technologies. During periods of market downturn and low investment sentiment, stepping back from the noise of hype to deeply study these cutting-edge technologies is undoubtedly a wise move.
Coincidentally, I once had the opportunity years ago to work with technical solutions related to FHE. Therefore, I’ve decided to provide a deep dive into Portal Ventures’ article, hoping to offer readers some fresh perspectives and insights.
What Exactly Are Homomorphic and Fully Homomorphic Encryption?
If you read Portal Ventures' original text directly, you might feel overwhelmed by the complex mathematical descriptions of fully homomorphic encryption (FHE).
Indeed, the world of cryptography is full of complexity and technical depth, but we can absolutely explain these concepts in simple, accessible terms. In this section, I aim to provide more intuitive and easy-to-understand examples to help you grasp the essence of fully homomorphic encryption.
First, imagine a "magic box." You can place any item inside and lock it. Once locked, you cannot see or touch the contents. But astonishingly, this magic box allows you to change the color or shape of the item inside—without opening it.
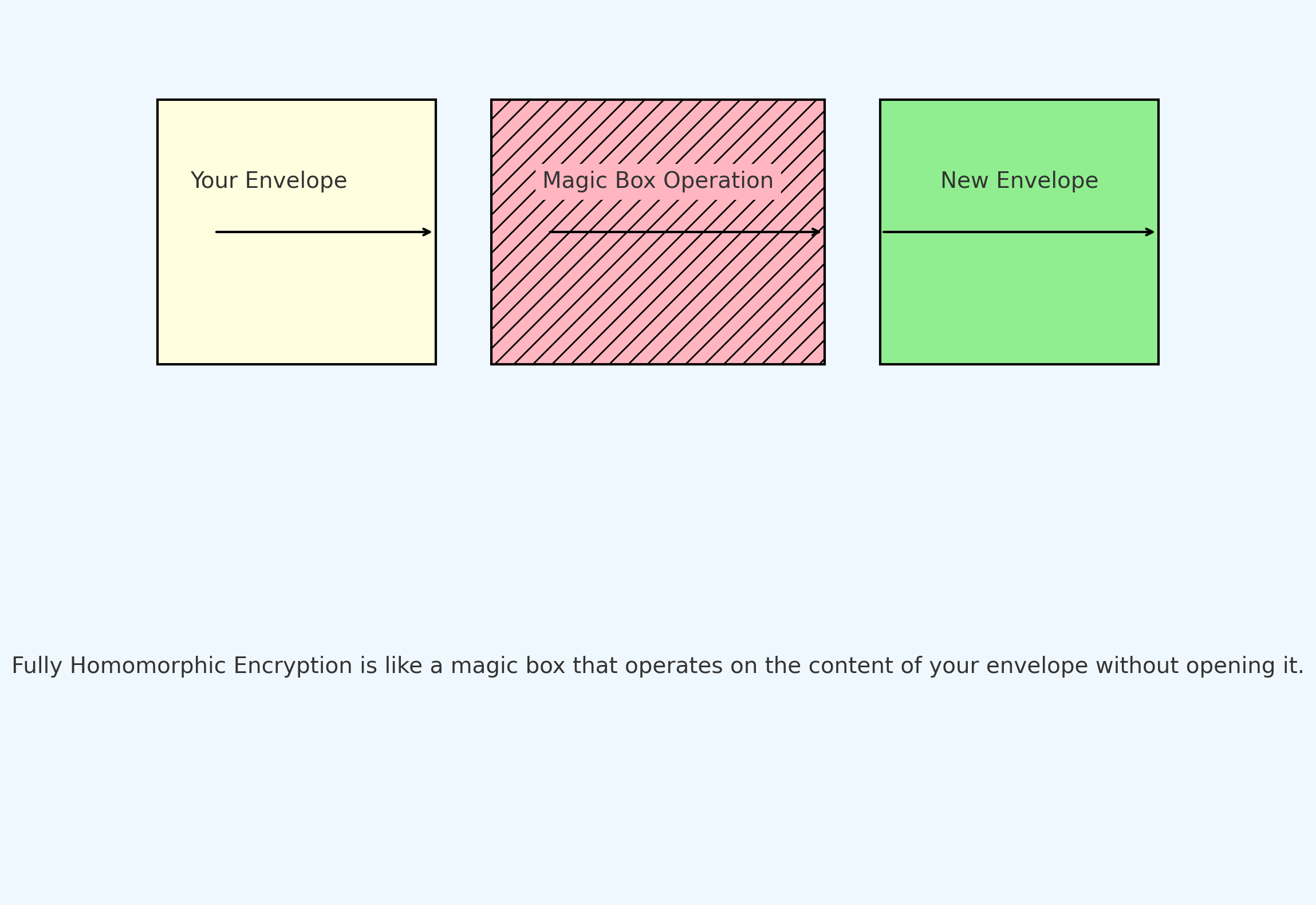
As shown above, fully homomorphic encryption (FHE) can be thought of as a magical box:
-
Your Envelope: This represents the original data you want to encrypt.
-
Magic Box Operation: Even without decrypting or opening the envelope, you can perform operations (like addition or subtraction) on the data inside.
-
New Envelope: After the magic box operation, you get a new encrypted result.
This is the fundamental idea behind homomorphic encryption: performing operations on encrypted data without knowing the data itself.
This analogy helps clarify what "fully homomorphic encryption" does. But in reality, the concept still feels somewhat abstract. So, what exactly do "fully" and "homomorphic" mean?
-
What Does “Fully” Mean?
-
In cryptography, encryption schemes can support various operations such as addition and multiplication. When we say an encryption scheme is "fully homomorphic," we mean it supports an unlimited number of basic operations (e.g., addition and multiplication) on encrypted data without requiring decryption. This contrasts with partially homomorphic schemes, which only support one type of operation (e.g., only addition or only multiplication).
-
What Does “Homomorphic” Mean?
-
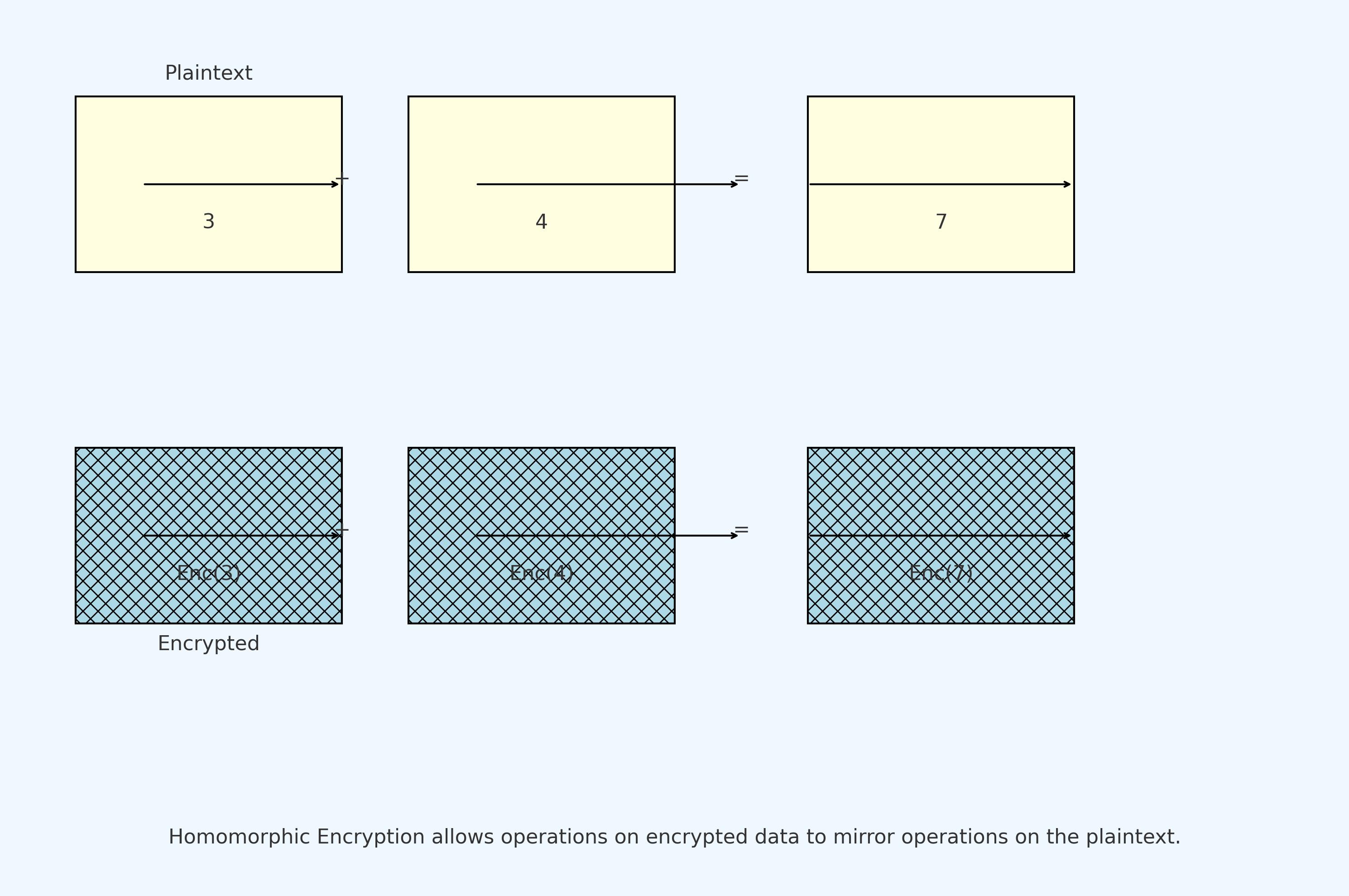
"Homomorphic" comes from Greek, meaning "same shape or structure." In cryptography, when we say an encryption scheme is homomorphic, it means certain operations performed on ciphertexts produce results equivalent to performing those same operations on plaintexts. In other words, if you perform an operation on encrypted data and then decrypt the result, it’s the same as first decrypting the data and then performing the operation on the plaintext.
-
For example, consider an encryption scheme supporting homomorphic addition. Suppose you have two numbers: 3 and 4. You can encrypt both numbers first, then use this homomorphic scheme to add the two encrypted values. Finally, decrypt the result. The decrypted output will be 7—the same as adding 3 and 4 directly in plaintext.
But you might ask: how can we perform arithmetic like addition and multiplication on non-numeric data? In practice, we can use specific encoding methods to convert non-numeric data into numeric forms, enabling operations like addition and multiplication. This means FHE's applications extend far beyond pure math, reaching diverse domains.
To make this more intuitive, let’s consider a medical data example.
-
Suppose a hospital has patient data such as age and blood glucose levels, but due to privacy concerns, it doesn't want to send raw data to a cloud provider for analysis.
-
Using FHE, the hospital can first encrypt this data.
-
Imagine the cloud provider needs to compute the average patient age (requiring addition and division) and the product of total glucose sum and patient count (involving addition and multiplication).
-
All these computations can be done directly on encrypted data, without decryption. The cloud provider performs calculations without ever seeing the raw data, then returns the encrypted result to the hospital. This ensures data privacy while fulfilling processing needs.
This is the magic of fully homomorphic encryption: it offers a secure yet flexible approach to data processing.
Why Is FHE Important?
Currently, existing methods for computing on encrypted data are far from ideal—they are relatively resource-intensive and time-consuming.
Therefore, the industry standard involves third parties (i.e., companies) decrypting data before performing computations.
Take a concrete example: imagine you have a file containing financial information about high-profile individuals.
-
Let’s call this file "M." You need a company to analyze this data.
-
How does the current process work? First, I encrypt M using an encryption function like RSA or AES. Now M becomes E(M), where E is the encryption function.
-
Next, I send E(M) to the company’s server. The company uses the corresponding decryption function D to decrypt E(M) back into plaintext, i.e., D(E(M)) = M.
-
The company then performs analysis directly on the plaintext file M.
-
After completing the analysis, the company re-encrypts the result to generate E(M').
-
The company sends the encrypted M' back to me, and I decrypt it again.
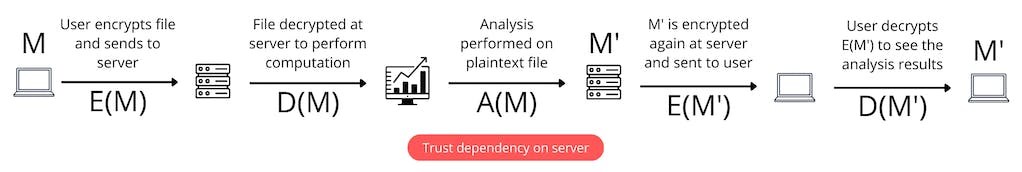
Notice the key issue here: when the company decrypts M and stores it on their servers for computation, a third party gains access to sensitive data that should remain protected. If the system is hacked or someone acts maliciously, serious problems arise.
Fully homomorphic encryption (FHE) solves this by allowing computation directly on encrypted data. The company no longer needs to decrypt E(M); they perform analysis directly on the ciphertext. No decryption is required, and no trust assumptions are needed.
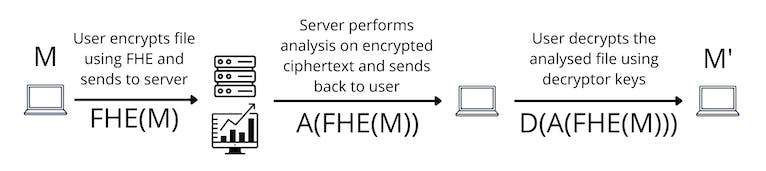
In summary, FHE addresses a critical flaw in current data processing workflows—the risk of exposing private data when processed by third parties. FHE provides a method to effectively process encrypted data while ensuring data privacy.
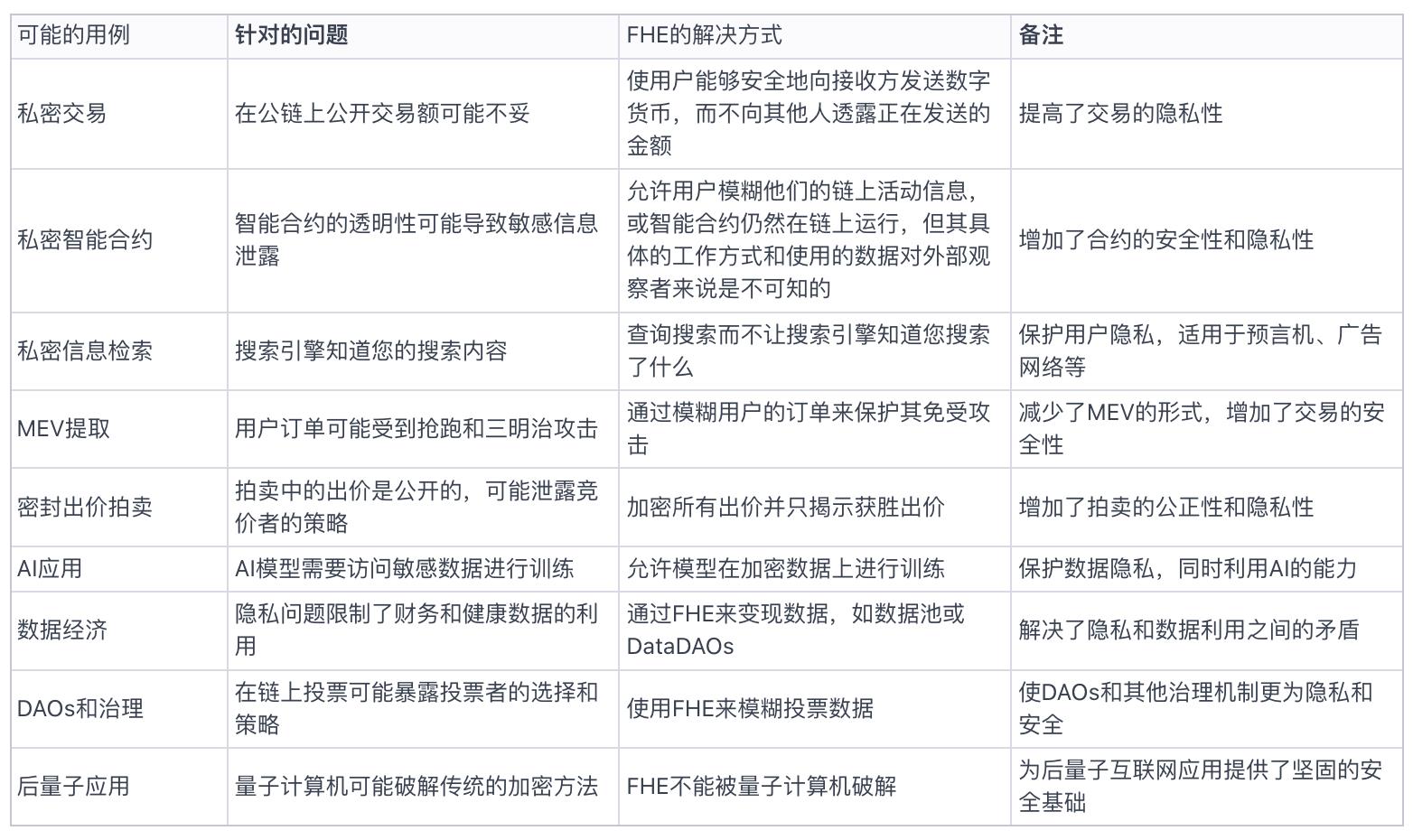
How Can FHE Be Applied in Crypto?
Fully homomorphic encryption (FHE) opens a new door for the crypto world, enabling many previously unimaginable use cases. Poly Venture’s original description of these scenarios is brief, so we’ve organized a more structured interpretation in the table below.
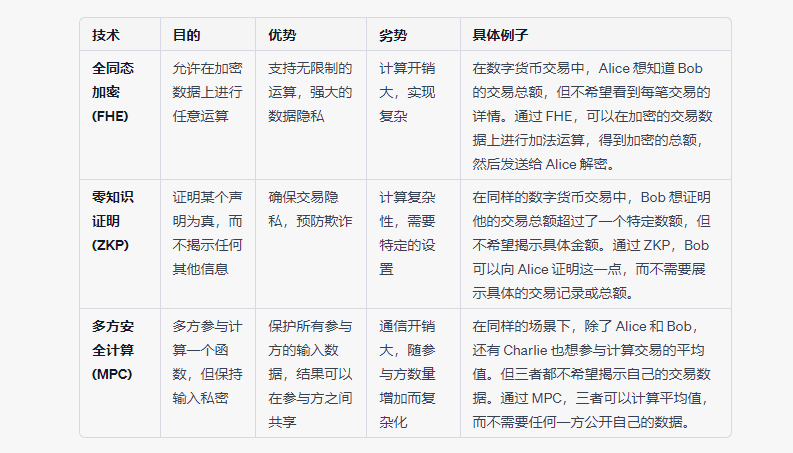
FHE vs ZK vs MPC: What’s the Difference?
After learning about fully homomorphic encryption (FHE), it’s natural to compare it with familiar technologies like zero-knowledge proofs (ZK) and multi-party computation (MPC). At first glance, they seem to address similar privacy and computation challenges. But what are the actual relationships and differences among them?
First, let’s review the basic definitions of these three technologies:
-
FHE: Enables computation on encrypted data without decryption.
-
ZK: Allows one party to prove the truth of a statement to another without revealing any additional information about it.
-
MPC: Enables multiple parties to jointly compute over their private inputs without revealing those inputs to each other.
Now, let’s examine their similarities, differences, and intersections across several dimensions:
-
Purpose:
-
FHE primarily aims to enable computation without decryption.
-
ZK focuses on proving the correctness of a fact without revealing details about it.
-
MPC enables secure joint computation among multiple parties without exposing individual inputs.
-
Privacy vs Computation:
-
In ZK, computation isn’t necessarily private. For instance, you can use ZK to verify that a bank balance exceeds $100,000, but the verification process itself may not be private.
-
In contrast, FHE ensures computational privacy because all operations occur on encrypted data.
-
Limits & Challenges:
-
MPC requires at least one honest participant and can be vulnerable to DDoS attacks, collusion, and high communication overhead.
-
ZK is mainly used for proving correctness, not as a privacy-preserving computation tool.
-
FHE offers strong privacy guarantees but suffers from low computational efficiency and high resource demands.
-
Applications in Crypto:
-
FHE can be used to build more privacy-preserving smart contracts and blockchain applications.
-
ZK powers scalable blockchain solutions like zk-rollups.
-
MPC is primarily used for private key management and custody.
-
Cross-Use Cases:
-
MPC can be combined with FHE to create threshold FHE, enhancing security by splitting an FHE key among multiple participants.
-
zkFHE—combining zero-knowledge proofs with FHE—is being researched to enable zk-rollups on FHE-based smart contracts.
Overall, while FHE, ZK, and MPC overlap in some areas, each has unique strengths and distinct application scenarios. In the crypto space, all three technologies hold great promise for enhancing privacy and security, and their integration and further research remain active frontiers within the cryptographic community.
Finally, we provide a simplified comparison table summarizing the above technologies for clearer understanding.
Future Outlook for FHE
From the discussion above, it’s clear that fully homomorphic encryption (FHE) is a powerful technology.
But why hasn’t it been widely adopted—or even frequently mentioned in crypto circles? Partly due to the technical barrier to understanding, but also because FHE still faces significant challenges that prevent it from easily entering commercial and mainstream use.
Key challenges include:
-
Computationally Intensive: As ciphertexts interact, noise accumulates to maintain security. FHE schemes use "bootstrapping" to reduce noise, but this process is extremely computationally intensive and resource-heavy.
-
Limited Functionality: FHE computations are restricted to addition, multiplication, and their combinations. For example, conditional statements (like if-statements) cannot be used because the content is encrypted. Building complex operations like comparisons or division requires careful design of basic logic, leading to more complicated programming and lower efficiency.
-
Compatibility / Composability Issues: Existing applications and service providers weren’t built to compute on encrypted data. This limits FHE integration with current systems and increases development inertia for FHE-compatible apps.
Potential solutions include:
-
Hardware Accelerators: Some FHE schemes, like nuFHE and cuFHE, can leverage GPU acceleration. However, major breakthroughs will come from faster FPGAs and ASICs. Other technologies, such as photonic computing, are also being explored to accelerate FHE hardware implementations.
-
New Programming Paradigms: Just as Python has libraries like pandas and numpy for complex math, FHE-specific libraries and SDKs are being developed. Projects like Zama and Sunscreen are already building such tools. Additionally, specialized compilers will be needed to unify FHE with ZKP and MPC development.
-
Integration with Existing Solutions: Middleware layers will emerge to bridge existing tools with FHE, enabling compatibility between conventional software and encrypted data processing.
Finally, Portal Ventures concludes its original article by emphasizing:
“FHE is the holy grail of computing, and we’re approaching its commercialization. Value and computation are transitioning toward open, permissionless networks, and we believe FHE will underpin much of the necessary infrastructure and applications.”
Moreover, they express interest in projects currently researching FHE. This shows that VCs are paying attention to FHE—or more broadly, that VCs tend to lead the charge in exploring advanced, under-the-radar technologies.
History shows that crypto projects based on new technologies often shine brightly, command high valuations, and attract significant capital.
Before the next feast begins, we should take time to study the identities of the invited guests—so we’re ready when the banquet starts.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News