Cobo Security Team Analysis: Critical Security Vulnerability in Stargate Cross-Chain Bridge's Underlying Protocol LayerZero
TechFlow Selected TechFlow Selected

Cobo Security Team Analysis: Critical Security Vulnerability in Stargate Cross-Chain Bridge's Underlying Protocol LayerZero
On March 28, LayerZero updated its cross-chain verification contract without issuing any public announcement. By comparing the original verification contract with the new one, Cobo Security Team discovered that this update was a fix for a previously identified critical security vulnerability.
This article is contributed by the Cobo Blockchain Security Research Team. The team members come from well-known security labs and have years of experience in cybersecurity and vulnerability mining. They have previously assisted Google and Microsoft in handling high-severity vulnerabilities and received acknowledgments from vendors including Google and Microsoft. They also achieved outstanding rankings on Microsoft's MSRC Most Valuable Security Researcher leaderboard. The team currently focuses on smart contract security, DeFi security, and other areas, researching and sharing cutting-edge blockchain security technologies.
We also welcome lifelong learners with a research-oriented mindset and scientific methodology in the field of cryptocurrency to join us and contribute insights and research perspectives to the industry!
Recently, LayerZero, the underlying protocol of the Stargate cross-chain bridge, silently updated its default transaction verification contract. After analysis by the Cobo Blockchain Security Team, this update fixed a critical vulnerability present in earlier versions, which could have affected the assets of all cross-chain projects built on LayerZero.
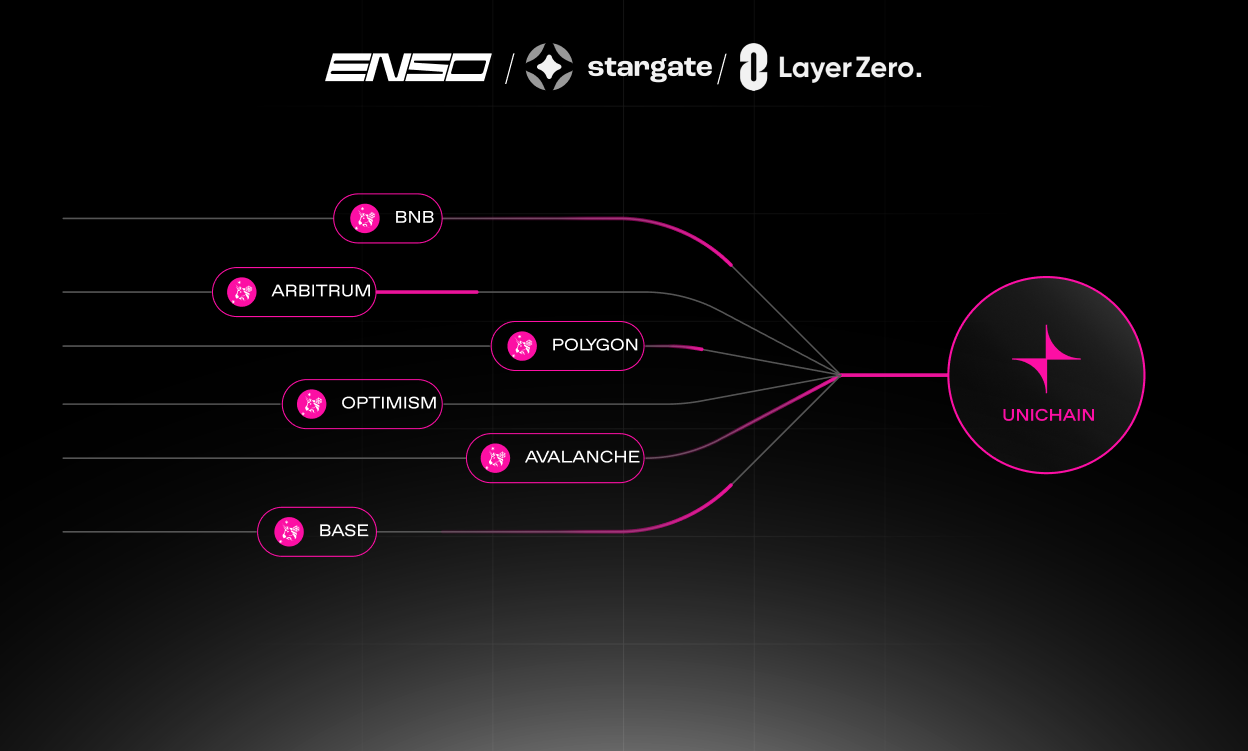
Stargate Finance (https://stargate.finance/) is one of the most prominent cross-chain bridge projects recently, with a TVL exceeding $350 million at the time of writing.
The Stargate cross-chain bridge relies on LayerZero for cross-chain message passing. The basic principle of how LayerZero enables cross-chain message transmission is as follows:
-
The Oracle submits the blockhash and block receiptsRoot from the source chain to the target chain.
-
The Relayer submits the receipt of the cross-chain message transaction from the source chain, along with the Merkle path linking this receipt to the receiptsRoot, to the target chain. The transaction validation contract on the target chain then verifies the consistency between the receipt submitted by the Relayer and the receiptsRoot submitted by the Oracle, based on Ethereum's MPT [1] structure.
-
If the verification passes, the receipt is considered valid and is forwarded to the upper-layer protocol, triggering subsequent cross-chain asset operations.
On March 28, LayerZero quietly updated its verification contract used for cross-chain communication without any public announcement [2]. By comparing the original verification contract (MPTValidator) with the new version (MPTValidatorV2) [3], the Cobo Security Team discovered that this update patched a major security vulnerability.
The core patch code is shown below:

In the original vulnerable code, during MPT verification, the next-level hashRoot was retrieved using an externally provided pointer from the proofBytes. This process used low-level Solidity assembly instructions such as add and mload to extract the hashRoot. However, since there was no bounds check ensuring the pointer stayed within the length of proofBytes, attackers could provide an out-of-bounds pointer, causing the contract to read data outside of proofBytes as the next-level hashRoot. This allowed potential forgery of the hashRoot, enabling forged transaction receipts to pass MPT verification. As a result, even if the Oracle remains fully trustworthy, the Relayer alone could forge receipt data and launch attacks against the cross-chain protocol—breaking LayerZero’s prior security assumptions.
Currently, the Oracle in the LayerZero protocol operates like a multisig contract—data submitted by two out of three admins is considered valid. However, the Relayer is controlled by a single-signature EOA, meaning any individual Relayer can submit malicious data and complete the entire attack flow.
The patched code uses the provided path and the safeGetItemByIndex function to retrieve the next-level hashRoot in the MPT, ensuring that the hashRoot is strictly sourced from within the current proofBytes, thus enabling correct and secure MPT verification.
The vulnerable code exposed in this incident lies at the heart of LayerZero’s MPT transaction verification—the foundational component upon which both LayerZero and its upper-layer protocols (such as Stargate) depend. Although the LayerZero team has now patched the obvious vulnerability, other undiscovered attack vectors may still exist. Furthermore, many of LayerZero’s critical contracts are still controlled by EOAs without implementing multisig or timelock mechanisms. If the private keys of these privileged EOAs are ever compromised, it could jeopardize the assets of all dependent upper-layer protocols.
Therefore, the Cobo Blockchain Security Team urges investors to be mindful of the risks associated with new projects and calls on the LayerZero team to conduct thorough audits of their contract code while promptly transitioning EOA-held privileges to multisig or timelock contracts to minimize exposure to potential attacks.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News