Lost $300 million in a year: Coinbase users frequently targeted by precise scams—was there an insider leaking information?
TechFlow Selected TechFlow Selected

Lost $300 million in a year: Coinbase users frequently targeted by precise scams—was there an insider leaking information?
This security crisis may be more serious than imagined.
By Fairy, ChainCatcher
"Hello, this is the Coinbase Security Team. We've detected suspicious login activity on your account..."
The voice on the other end sounds professional and urgent—so convincing that it can accurately recite your name, registered email, and even recent transaction history. Would you hang up immediately, or follow the "customer service" agent’s instructions to transfer your funds into a so-called “secure wallet”?
Recently, multiple Coinbase users have fallen victim to such scams, suffering staggering losses. In March alone, over $46 million was stolen. Annually, social engineering attacks cost Coinbase users an estimated $300 million.
But how are these hackers identifying their targets with such precision? How do they obtain personal user data? This security crisis may be far more severe than previously imagined.
Scams Surge as Phishing Attacks Become Industrialized
On March 28, on-chain investigator ZachXBT revealed that in just the past two weeks, numerous suspected fraud cases targeting Coinbase users had pushed the total amount stolen in March beyond $46 million.
In fact, signs of these scams emerged earlier. As early as early February, ZachXBT exposed that between December 2024 and January 2025, Coinbase users lost as much as $65 million using similar tactics—pointing to an annual $300 million crisis caused by social engineering fraud at Coinbase.
According to ZachXBT's analysis, the scam operations have evolved into a mature industrial chain:
Impersonating Coinbase Official Staff
Scammers use spoofed phone numbers to call victims, leveraging personal information to gain trust. They claim unauthorized login attempts have been detected on the user's account and urge cooperation with a "security verification" process.
Sending Phishing Emails
Scammers send forged emails appearing to come from Coinbase, often including fake case IDs (Case ID).
Directing Users to Transfer Funds
Victims are instructed to transfer funds into a Coinbase Wallet and add the scammer’s address to their whitelist, under the false pretense that this is part of a security validation procedure.
Cloning the Coinbase Website
Scammers create near-identical replicas of the official Coinbase website. These phishing sites deliver tailored prompts via forged emails and Telegram-based scam dashboards.
Beyond this, Cointelegraph recently reported that multiple crypto users received phishing emails impersonating both Coinbase and Gemini. These messages falsely claimed that due to regulatory requirements, users must migrate to self-custody wallets by April 1—a fabricated deadline designed to create urgency.
The emails include links to download Coinbase Wallet or Gemini Wallet apps, along with pre-generated recovery phrases. Once users create new wallets using these phrases and transfer assets, their funds are instantly drained by the attackers.
Internal Data Access Issues Come to Light
The core of social engineering fraud lies in precise information gathering. In the case of Coinbase users being targeted, attackers appear to possess detailed personal data—including phone numbers, email addresses, and transaction records. This raises a critical question: how did this data fall into the hands of scammers?
Yesterday, Mike Dudas, co-founder of The Block, posted on X that he had received an alarming email from Coinbase. The message directly pointed to internal data access violations:
"We are writing to inform you that we identified indications that a Coinbase employee may have accessed limited customer account records in a manner inconsistent with our internal policies, including your account."
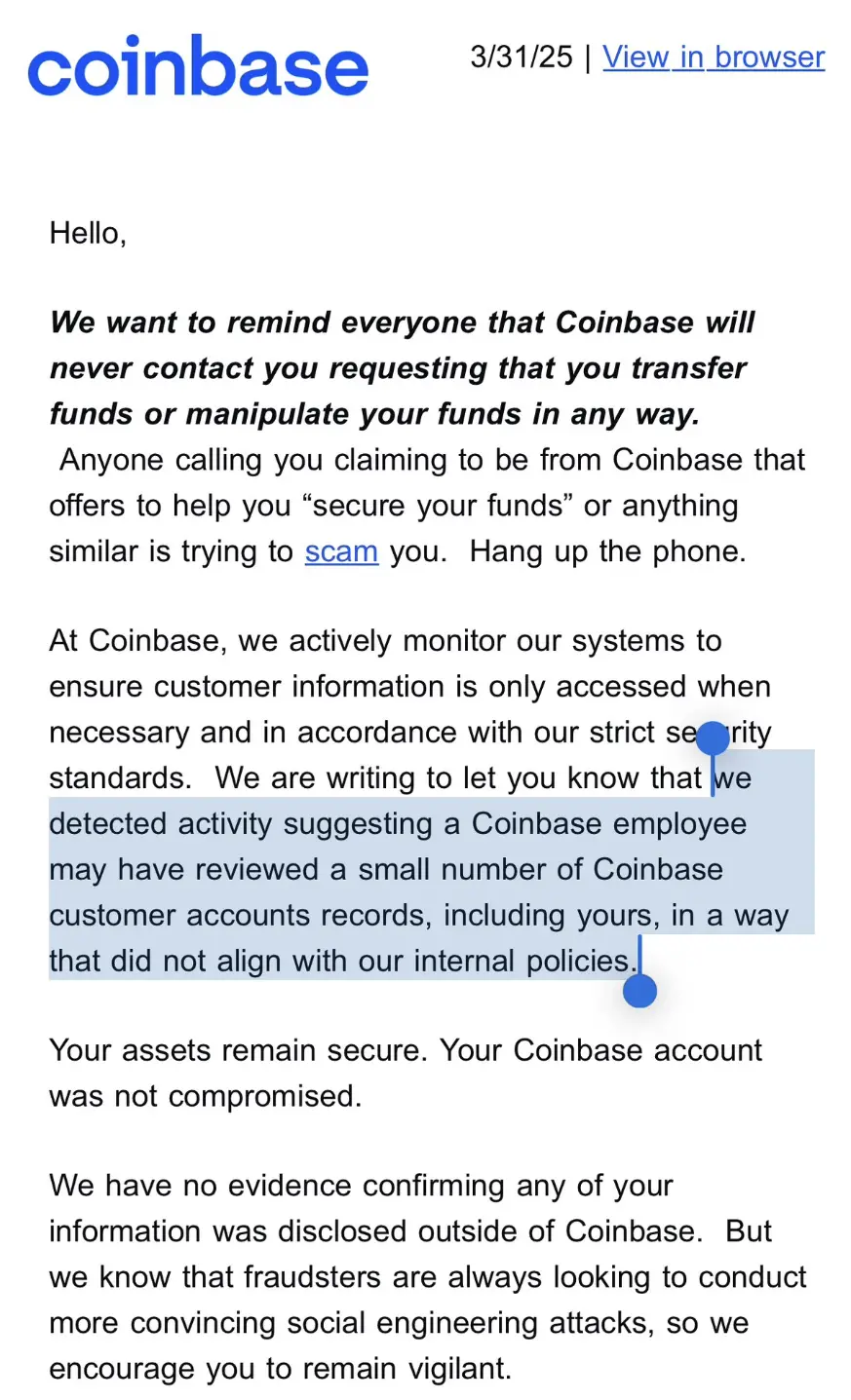
While the email reassured recipients that “your assets remain secure” and there was no evidence of external data leakage, it still delivered a clear warning: internal data access breaches have been confirmed—and they are not isolated incidents.
Dudas stated this explains the surge in phishing calls and emails impersonating Coinbase.
However, the scope of the potential data exposure remains questionable and could involve a broader user base. Community member @ghaiankur commented: "I don’t have any funds on Coinbase, nor have I ever used it. Yet I still received one of these notifications. This might not be about a few targeted accounts—it could involve the entire database."
Data Breaches Emerge as an Industry-Wide Risk
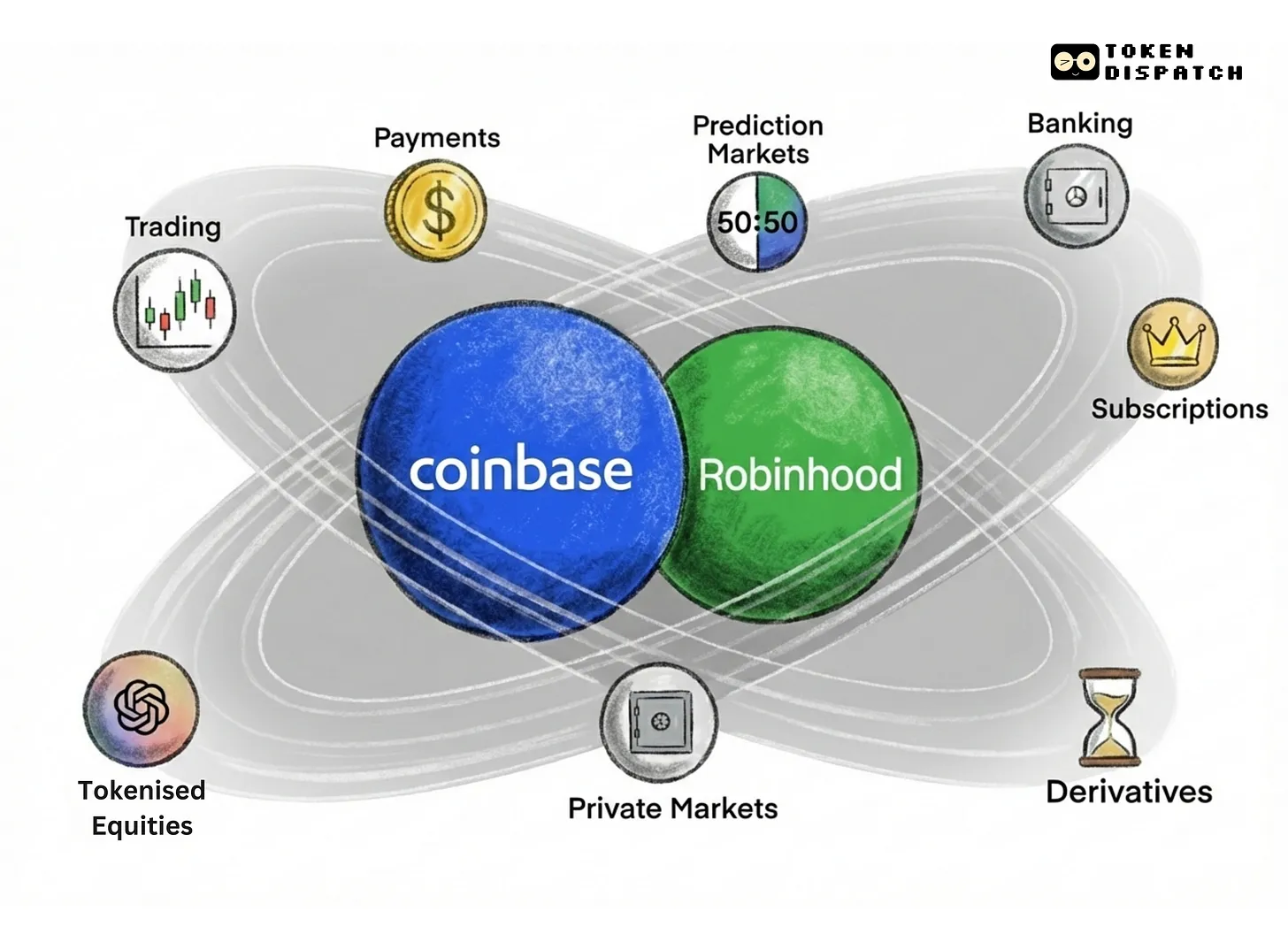
It’s not just Coinbase. Other exchanges appear to face similar internal security vulnerabilities.
After Dudas shared his email, crypto trader Jordan Fish (@Cobie) revealed that exchange Kraken had also recently suffered a comparable incident. He speculated: "This might be part of the attackers’ strategy—penetrating customer support teams to steal user data from within."
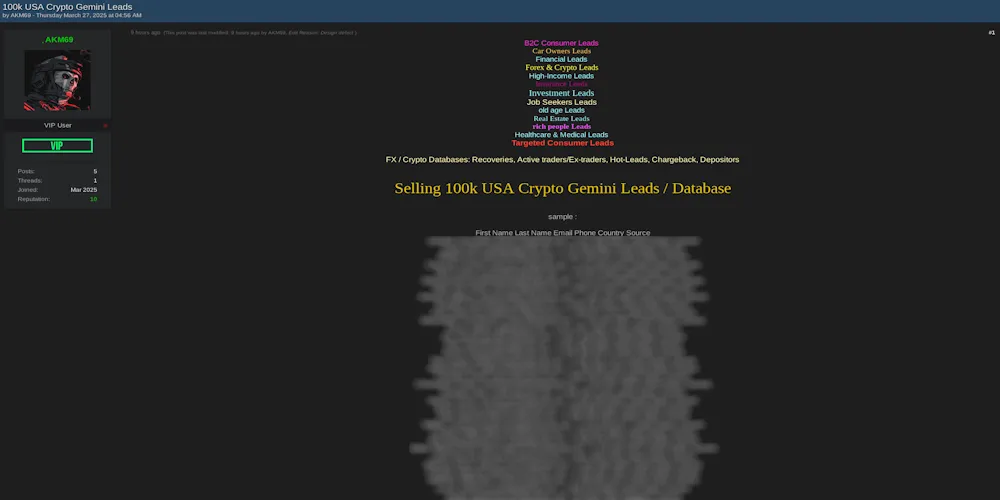
Meanwhile, on March 27, dark web news site Dark Web Informer reported that a hacker using the alias AKM69 claimed to possess private information from a large number of Gemini users. The database reportedly contains 100,000 records, including full names, emails, phone numbers, and location details of U.S. users, as well as some data from Singaporean and UK users.
Exchanges must either learn to protect their users—or be abandoned by them.
Toly, co-founder of Solana, commented on the incident, suggesting exchanges should implement user-controlled transfer time locks to reduce the risk of rapid asset theft. However, the root issue goes deeper: it exposes failures in internal risk controls and the highly industrialized nature of modern fraud operations.
Exchange security is no longer just a matter of technical defense—it’s a matter of management integrity and user trust. In the face of increasingly sophisticated attack methods, building more robust risk control systems will define the future security baseline for the entire industry.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News