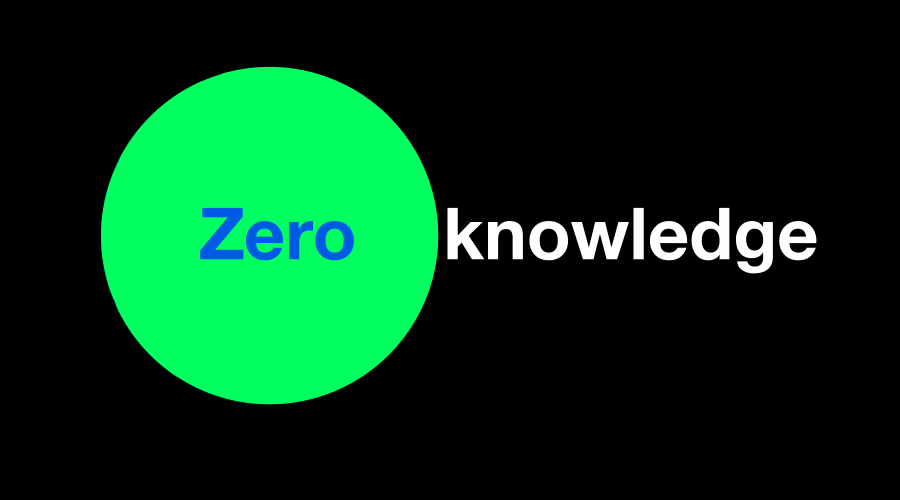
The third major technological innovation in the history of blockchain development: zero-knowledge proof technology applications
TechFlow Selected TechFlow Selected
The third major technological innovation in the history of blockchain development: zero-knowledge proof technology applications
This article mainly introduces the extensive applications, technical approaches, development trends, and challenges of zero-knowledge proofs in the blockchain field.
Author:
Researcher at SUSS NiFT, Singapore University of Social Sciences @Jesse_meta
Researcher at Beosin @EatonAshton2
Security Researcher at Least Authority @kaplannie
Whether data is stored online or in physical archives, information leaks—whether intentional or accidental—are now commonplace. As long as information is stored centrally, it remains vulnerable to single-point attacks. Whenever verification relies on a trusted third party, moral hazard and inefficiency arise. Solving information security issues is critical and urgent. Zero-knowledge proof (ZKP) technology enables users to verify information more efficiently and securely while preserving privacy. If Bitcoin was blockchain’s first major innovation—offering a new form of value storage—and Ethereum’s smart contracts were the second milestone, unlocking vast potential for innovation, then zero-knowledge proofs represent the third major technological breakthrough in blockchain history, delivering both privacy and scalability. This advancement is not only a key component of the Web3 ecosystem but also a foundational technology with transformative societal potential.
This article introduces zero-knowledge proofs from a non-technical perspective, covering their use cases, working principles, current state, and future trends, aiming to help readers without technical backgrounds understand the significant changes ZKPs are poised to bring.
1. What Is Zero-Knowledge Proof?
Zero-knowledge proof (ZKP) is a cryptographic protocol first proposed in 1985 by Shafi Goldwasser, Silvio Micali, and Charles Rackoff in their paper “The Knowledge Complexity of Interactive Proof Systems.” It allows one party to prove to another that a statement is true without revealing any information beyond the truth of that statement. The verifier learns nothing about the secret used to generate the proof. To illustrate: suppose I want to prove I know someone’s phone number. I can do so by successfully dialing their number in front of others—proving I possess the number without revealing it. Zero-knowledge proofs offer an efficient, nearly risk-free method of data sharing. By leveraging ZKPs, we can retain ownership of our data, significantly enhance privacy protection, and potentially render data breaches obsolete.
Zero-knowledge proofs have three core properties:
Completeness
If a statement is true, an honest verifier will be convinced by an honest prover. In other words, truth prevails.
Soundness
If a statement is false, no dishonest prover can convince an honest verifier otherwise—except with negligible probability. That is, falsehoods cannot be accepted as true.
Zero-Knowledge
If a statement is true, the verifier learns only that fact—and nothing else.
There exists a negligible probability of soundness error—meaning a cheating prover might trick the verifier into accepting a false claim. Thus, ZKPs are probabilistic rather than deterministic proofs. However, through advanced techniques, this error rate can be reduced to practically imperceptible levels.
2. Applications of Zero-Knowledge Proofs
The two most important applications of zero-knowledge proofs are privacy and scalability.
2.1 Privacy
Zero-knowledge proofs allow users to securely share necessary information without disclosing personal details—protecting them from hackers and identity theft. As digital and physical worlds increasingly converge, ZKP-based privacy protection becomes crucial not only for Web3 but for broader information security. Without ZKPs, user data often resides in centralized databases controlled by trusted third parties, which remain vulnerable to cyberattacks. The first blockchain application of ZKPs was Zcash, a privacy-focused cryptocurrency that hides transaction details.
2.1.1 Identity Protection and Verification
Online, we frequently provide sensitive personal information—names, birth dates, emails, complex passwords—to prove we are legitimate users, leaving behind traces of private data. Today, receiving scam calls that address us by name has become routine, highlighting the severity of personal data leakage.
Blockchain can assign each person a unique encrypted digital identifier containing personal data. This identifier forms a decentralized identity (DID), resistant to forgery or alteration without the owner’s knowledge. Users control access to their identity, enabling them to prove citizenship without revealing passport details—streamlining authentication and reducing incidents where users lose access due to forgotten passwords. Zero-knowledge proofs, generated from public data and private user information, can authenticate users when accessing services. This reduces cumbersome verification steps, improves user experience, and avoids centralized data storage.
Additionally, ZKPs can build private reputation systems, allowing institutions to verify whether users meet certain credibility standards—without exposing their identities. For example, users could anonymously export reputation from platforms like Facebook, Twitter, or GitHub without revealing specific account sources.
2.1.2 Anonymous Payments
Bank card transactions are typically visible to multiple parties—including payment providers, banks, and governments—potentially compromising user privacy. Users must trust these entities not to abuse their power.
Cryptocurrencies enable peer-to-peer payments without intermediaries. However, on most public blockchains, transactions are publicly visible. While wallet addresses are pseudonymous, chain analysis combined with off-chain data (e.g., exchange KYC records or social media profiles) can link addresses to real-world identities. Knowing someone’s wallet address is akin to having continuous access to their bank balance—posing risks to their identity and assets.
Zero-knowledge proofs offer anonymity at three layers: privacy coins, privacy apps, and privacy-focused blockchains. Zcash, a privacy coin, conceals transaction details such as sender, receiver, asset type, amount, and timestamp. Tornado Cash is a decentralized application on Ethereum that uses ZKPs to obscure transaction trails for private transfers (though often misused for money laundering). Aleo is a Layer 1 blockchain designed to provide native privacy features at the protocol level.
2.1.3 Encouraging Honest Behavior
Zero-knowledge proofs can promote honesty while preserving privacy. Protocols can require users to submit ZKPs proving they’ve followed rules. Due to soundness (“false claims won’t pass”), users must behave honestly to generate valid proofs.
MACI (Minimal Anti-Collusion Infrastructure) is an example that prevents collusion during on-chain voting or decision-making. It uses key pairs and ZKP technology. In MACI, users register their public keys with a smart contract and send encrypted votes. Its anti-collusion design allows voters to change keys, preventing others from linking votes to identities. At the end of the voting period, a coordinator submits a ZKP confirming all messages were processed correctly and the final tally reflects all valid votes. This ensures integrity and fairness.
2.1.4 Personal Information Verification
When applying for a loan, you might obtain a digital income certificate from your employer. The authenticity of this document can be cryptographically verified. Banks can use ZKPs to confirm your income meets minimum thresholds—without seeing sensitive details.
2.1.5 Combining Machine Learning with Private Data
Training machine learning models requires vast datasets. With ZKPs, data owners can prove their data satisfies training requirements—without revealing the actual data. This unlocks the value of private data and enables monetization.
Moreover, model creators can use ZKPs to prove their models meet performance benchmarks—without disclosing proprietary model architecture, protecting against copying or tampering.
2.2 Scalability
As blockchain networks grow, computational demands increase, causing congestion. Some chains pursue sharding, but this requires complex modifications to the base layer—potentially compromising security. A more viable alternative is ZK-Rollups, using verifiable computation to outsource execution to a separate chain. These rollups submit ZKPs along with results to the main chain for validation. The ZKP guarantees correctness; the main chain only updates state, without storing full transaction data or replaying computations. There's no need to wait for dispute resolution—greatly improving efficiency and scalability. Developers can build lightweight dApps running on everyday hardware like smartphones, accelerating Web3 adoption.
ZK-based scaling can be applied at Layer 1 (e.g., Mina Protocol) or Layer 2 (e.g., ZK-Rollups).
3. How Do Zero-Knowledge Proofs Work?
Dmitry Laverenov (2019) categorizes ZKP systems into interactive and non-interactive types.
3.1 Interactive Zero-Knowledge Proofs
Interactive ZKPs involve three steps: witness, challenge, and response.
Witness: The hidden secret serves as evidence. This evidence creates a set of questions only someone possessing the secret can answer correctly. The prover randomly selects a question, computes the answer, and sends it to the verifier.
Challenge: The verifier randomly selects another question from the set and asks the prover to answer.
Response: The prover computes the answer and returns it. The verifier checks whether the response aligns with expected behavior—confirming knowledge of the secret.
This process repeats until the probability of guessing correctly without knowing the secret becomes negligible. For example, if the chance of guessing right is 1/2, after 10 rounds the odds drop to ~0.001—making fraud virtually impossible.
3.2 Non-Interactive Zero-Knowledge Proofs
Interactive ZKPs have limitations: they require both parties to be present and repeated interactions. Each new proof requires fresh communication, and proofs aren’t reusable across different verifications.
To overcome this, Manuel Blum, Paul Feldman, and Silvio Micali introduced non-interactive ZKPs. Here, prover and verifier share a common reference string, enabling a single-round proof. The prover uses a special algorithm to generate a ZKP from the secret and sends it. The verifier uses another algorithm to check its validity. Once created, anyone with the shared parameters and verification algorithm can validate the proof independently.
Non-interactive ZKPs were a major breakthrough, enabling modern ZKP systems. Key implementations include ZK-SNARKs and ZK-STARKs.
4. Major Technical Approaches to Zero-Knowledge Proofs
Alchemy (2022) classifies ZKP approaches into ZK-SNARKs, ZK-STARKs, and recursive ZK-SNARKs.
4.1 ZK-SNARKs
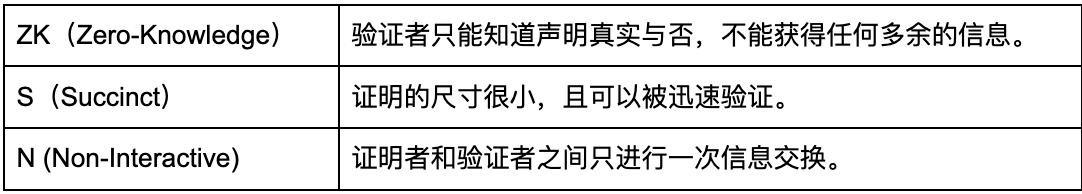
ZK-SNARKs are zero-knowledge succinct non-interactive arguments of knowledge.
Public blockchains ensure transaction correctness by requiring nodes to re-execute every transaction—a process that slows the network and limits scalability. Nodes must also store transaction data, leading to exponential blockchain growth.
ZK-SNARKs solve this by proving the correctness of off-chain computations without requiring nodes to replay each step. This eliminates the need to store redundant data, boosting throughput.
SNARKs encode computations into mathematical expressions to generate validity proofs. Verifiers check these compact proofs. If passed, the underlying computation is deemed valid. The proof size is much smaller than the computation itself—hence “succinct.”
Most ZK-SNARK-based ZK-Rollups follow these steps:
1. Users on L2 sign transactions and submit them to a sequencer.
2. The sequencer compresses multiple transactions using cryptography and generates a SNARK validity proof.
3. An L1 smart contract verifies the proof and decides whether to finalize the batch on-chain.
Notably, ZK-SNARKs require a trusted setup. During this phase, a key generator uses a program and secret parameter to produce two public keys—one for generating proofs, one for verifying them. These keys are generated once via a trusted ceremony and reused by all participants. Users must trust that ceremony participants acted honestly—an assumption difficult to verify. Knowledge of the secret parameter allows fake proofs to be forged, posing a security risk. Researchers are actively exploring trustless alternatives.
Advantages
1. Security
ZK-Rollups are considered more secure than Optimistic Rollups because ZK-SNARKs employ advanced cryptographic safeguards, making fraud extremely difficult.
2. High Throughput
ZK-SNARKs reduce Ethereum’s computational load, alleviating congestion. Off-chain computation lowers fees and accelerates transaction processing.
3. Small Proof Size
The compact size of SNARK proofs makes them easy to verify on-chain, resulting in low gas costs and reduced user expenses.
Limits
1. Relative Centralization
Most ZK-SNARKs rely on a trusted setup—contradicting blockchain’s trustless ethos.
Generating SNARK proofs is computationally intensive, requiring specialized hardware. These expensive machines are accessible to few, making the proving process highly centralized.
2. ZK-SNARKs use elliptic curve cryptography (ECC), currently secure but potentially vulnerable to advances in quantum computing.
Projects Using ZK-SNARKs
Polygon Hermez
In 2021, Polygon acquired Hermez for $250 million—the first full merger between two blockchain networks. Hermez brought ZK technology and tools to Polygon’s rapidly growing user base, supporting the development of zkEVM. Hermez 1.0 was a payment platform that executed batches of transactions off-chain, enabling fast ERC-20 transfers between accounts—at up to 2,000 TPS. Hermez 2.0 evolved into a zero-knowledge zkEVM that executes Ethereum transactions transparently, including smart contracts with ZK verification. Fully EVM-compatible, it requires minimal code changes, easing deployment for developers. Hermez 1.0 used SNARK-proofs; version 2.0 uses both SNARK and STARK proofs. STARK-proofs verify off-chain transactions, but their high on-chain verification cost led to using SNARK-proofs to verify STARK-proofs.
zkSync
Launched in 2020 by Matter Labs, zkSync 1.0 supported only payments and transfers. zkSync 2.0, supporting smart contracts, went live on mainnet in March 2023.
zkSync compiles Solidity smart contract code into Yul—an intermediate language that targets various EVM bytecodes. Using the LLVM compiler framework, Yul is recompiled into custom, circuit-friendly bytecode optimized for zkSync’s zkEVM. This approach avoids generating ZK proofs for every high-level execution step, simplifying decentralization while maintaining performance. Future enhancements may add support for Rust, JavaScript, or other languages—increasing flexibility and attracting more developers.
Aztec
Aztec is the first hybrid zkRollup, enabling both public and private smart contract execution in one environment. It provides a zero-knowledge execution layer—not a zkEVM. By combining public and private execution in a single rollup, it enables confidential operations within public contexts—for example, private trades in public AMMs, secret chat in open games, or anonymous voting in public DAOs.
4.2 ZK-STARKs
ZK-STARKs eliminate the need for trusted setup. ZK-STARK stands for Zero-Knowledge Scalable Transparent Argument of Knowledge. Compared to ZK-SNARKs, they offer better scalability and transparency.
Advantages
1. Trustlessness
ZK-STARKs replace trusted setup with publicly verifiable randomness, reducing reliance on participants and enhancing protocol security.
2. Greater Scalability
Even as underlying computation grows exponentially, ZK-STARKs maintain low proof and verification times—unlike ZK-SNARKs, whose time scales linearly.
3. Stronger Security Guarantees
ZK-STARKs use collision-resistant hash functions instead of elliptic curves, making them resistant to quantum computing attacks.
Limits
1. Larger Proof Size
ZK-STARK proofs are larger, increasing on-chain verification costs.
2. Lower Adoption
ZK-SNARKs were the first practical ZKP implementation in blockchain, so most ZK-Rollups use them, benefiting from mature developer tools and ecosystems. Despite support from the Ethereum Foundation, ZK-STARKs lag in adoption, with less developed infrastructure.
Which Projects Use ZK-STARKs?
Polygon Miden
Polygon Miden is an Ethereum Layer 2 scaling solution that uses zk-STARKs to bundle numerous L2 transactions into a single Ethereum transaction—boosting throughput and lowering costs. Without sharding, Miden produces a block every 5 seconds with TPS exceeding 1,000. With sharding, TPS can reach 10,000. Users can withdraw funds from Miden to Ethereum in just 15 minutes. At its core is Miden VM—a STARK-based Turing-complete virtual machine that simplifies formal verification of smart contracts.
StarkEx and StarkNet
StarkEx is a permissioned framework for building custom, application-specific scaling solutions. Projects use StarkEx for low-cost off-chain computation, generating STARK proofs of correct execution. Each proof covers 12,000–500,000 transactions. These proofs are sent to an on-chain STARK verifier, which confirms correctness before accepting state updates. Applications built on StarkEx include perpetuals DEX dYdX, NFT L2 Immutable, Sorare (digital sports cards), and cross-chain DeFi aggregator rhino.fi.
StarkNet is a permissionless L2 where anyone can deploy smart contracts written in Cairo. Contracts on StarkNet can interact to create composable protocols. Unlike StarkEx, where apps submit transactions, StarkNet’s sequencer batches and processes them. StarkNet suits protocols needing interoperability or functionality beyond StarkEx’s scope. As StarkNet matures, StarkEx-based apps can migrate to enjoy composability.
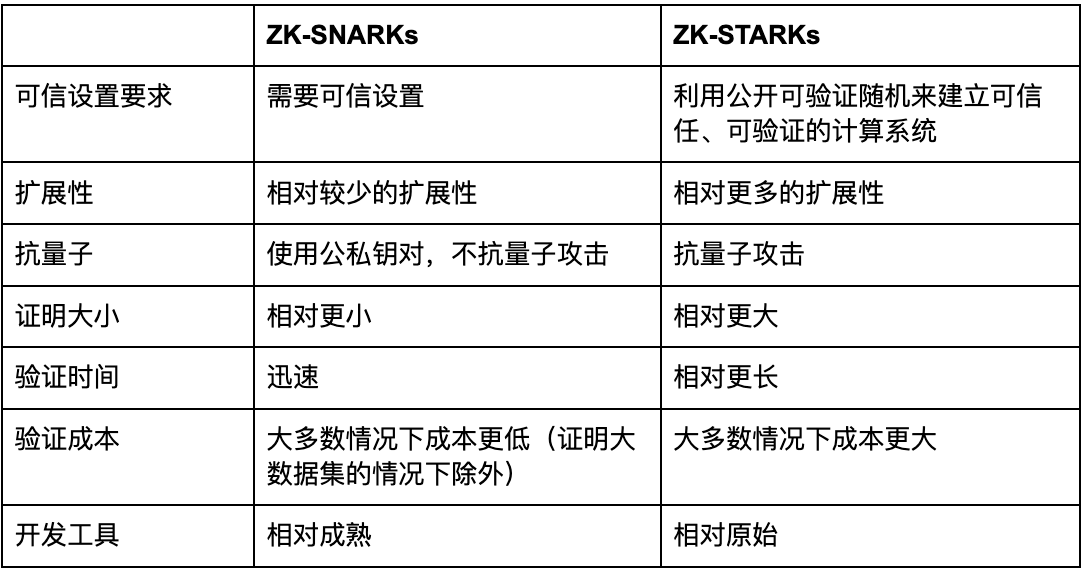
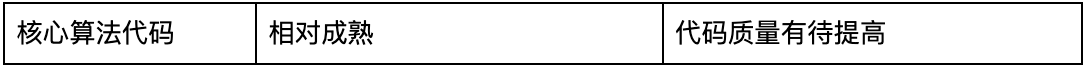
ZK-SNARKs vs. ZK-STARKs Comparison
4.3 Recursive ZK-SNARKs
Standard ZK-Rollups handle only one block at a time, limiting transaction volume. Recursive ZK-SNARKs can verify multiple blocks by merging SNARKs from different L2 blocks into a single validity proof submitted to L1. Once accepted by the L1 contract, all included transactions are finalized—dramatically increasing the number of provable transactions.
Plonky2, developed by Polygon Zero, is a new recursive ZK-SNARK mechanism that accelerates transaction processing. Recursive SNARKs aggregate multiple proofs into one, speeding up generation. Plonky2 uses parallelization to generate proofs for thousands of transactions simultaneously, then recursively combines them into a single block proof—making it faster than traditional methods that attempt to generate one large proof at once. Moreover, Plonky2 can generate proofs on consumer-grade devices, addressing the hardware centralization issue common in SNARK systems.
5. Zero-Knowledge Rollup vs. Optimistic Rollup
ZK-SNARKs and ZK-STARKs have become core infrastructures for blockchain scaling projects—especially Zero-Knowledge Rollups. A Zero-Knowledge Rollup is a Layer 2 Ethereum scaling solution that moves computation off-chain using ZKP technology to alleviate network congestion. Its main advantages include significantly higher transaction throughput, lower fees, and immediate finality—once a transaction is included in a rollup, it’s confirmed.
Besides ZK-Rollups, Ethereum’s other major L2 approach is Optimistic Rollup. Transactions in Optimistic Rollups are assumed valid and executed immediately. Only if fraud is detected (via a fraud proof) is a transaction reverted. Thus, security is weaker than ZK-Rollups. To prevent fraud, Optimistic Rollups impose a challenge period—transactions aren’t finalized until it ends. This delays withdrawals and fund recovery.
The original EVM wasn’t designed with ZKPs in mind. Ethereum co-founder Vitalik Buterin believes ZK-Rollups face short-term technical complexity but will ultimately win the scalability race. Below is a comparison:
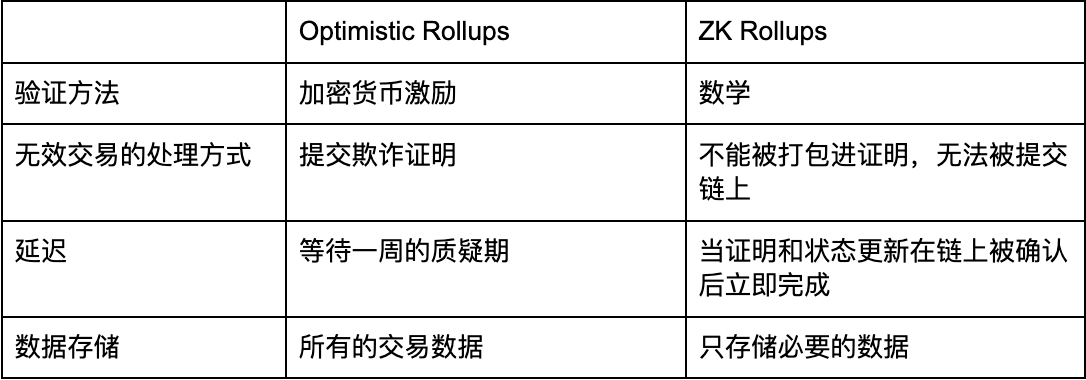
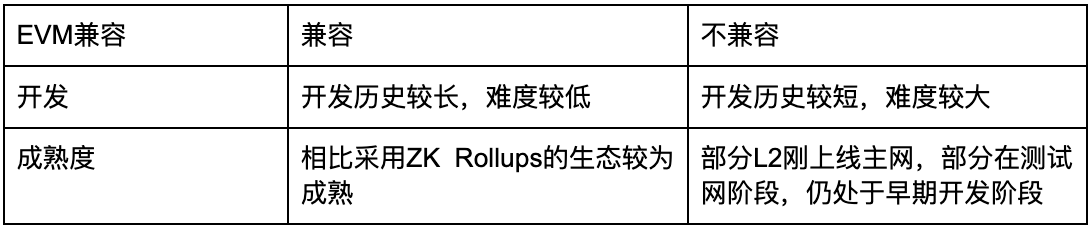
Source: SUSS NiFT, ChatGPT
6. What Is the Future of Zero-Knowledge Proof Technology?
Zero-knowledge proof technology occupies a unique position: years of intense research have yielded cutting-edge results in cryptography and secure communications—many of which are still relatively new. Numerous intriguing questions remain unanswered by academia and the developer community. Meanwhile, real-world applications continue to test and expand the boundaries of ZKP capabilities.
One area of growing interest is post-quantum security of ZKPs. Publicly verifiable SNARKs (Succinct Non-Interactive Arguments of Knowledge) are central to ZK technology—but most widely used schemes (e.g., Groth16, Sonic, Marlin, SuperSonic, Spartan) are not considered quantum-safe. The mathematical problems they rely on can be solved efficiently by quantum computers, undermining their long-term viability.
Academic efforts are underway to develop quantum-safe ZKPs applicable to general statements without preprocessing. Leading examples include Ligero, Aurora, Fractal, Lattice Bulletproofs, and LPK22. Ligero, Aurora, and Fractal are based on hash functions; Lattice Bulletproofs and LPK22 use lattice-based cryptography—both believed to be quantum-resistant. Improving the efficiency and adoption of these schemes is becoming a trend.
Another expectation is improved resilience against attacks and greater maturity in implementation code. As codebases grow, we’ll see more secure, audited libraries and best practices emerge. Of course, new vulnerabilities will be discovered over time. We anticipate the field maturing toward widespread adoption, with standardized protocols and interoperability between implementations. Initiatives like ZKProof are already driving this effort.
An ongoing trend is increased work on efficient algorithms and specialized hardware. Recent years have seen reductions in proof size and improvements in prover and verifier efficiency. Advances in algorithms, dedicated hardware, and computation optimization may yield even faster, more scalable systems.
While improved efficiency benefits users, we also expect the functional scope of ZKPs to expand. Previously limited to preprocessed zk-SNARKs, we now see growing use of upgradable variants. Additionally, some applications leverage ZKPs primarily for their succinctness—even when full zero-knowledge isn't required.
Finally, another emerging trend is the intersection of machine learning and zero-knowledge proofs (ZKML). This involves training large language models in multi-party settings and using ZK tech to verify computations—highly relevant to today’s AI landscape. This area holds strong potential for new projects.
Conclusion
Through this article, we’ve explored the broad applications, technical pathways, development trends, and challenges of zero-knowledge proofs in blockchain. With continued advancements in hardware and cryptography, we believe ZKPs will achieve further breakthroughs—delivering faster, safer applications for the digital world.
About the SUSS NiFT Blockchain Ecosystem Security Alliance
The SUSS NiFT Blockchain Ecosystem Security Alliance, jointly initiated by international-leading blockchain security firm Beosin and SUSS NiFT, brings together diverse organizations—including universities, blockchain security firms, industry associations, and fintech service providers. Founding council members include Beosin, SUSS NiFT, NUS AIDF, BAS, FOMO Pay, Onchain Custodian, Semisand, Coinhako, ParityBit, and Huawei Cloud. Moving forward, alliance members will collaborate closely, leveraging ecosystem partnerships to deliver cutting-edge security solutions for the global blockchain industry. The council welcomes more visionaries from the blockchain space to join forces in safeguarding the ecosystem.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News