Lightning Network Outlook for 2025: New Horizons for Enhanced Privacy and Usability
TechFlow Selected TechFlow Selected

Lightning Network Outlook for 2025: New Horizons for Enhanced Privacy and Usability
This article will explore what the user experience of the Lightning Network might be like, based on solutions currently being developed by many brilliant minds.
Translated by: BTCStudy
Since its inception, the Lightning Network has come a long way. Numerous optimizations have made Lightning payments smooth and seamless—though not yet perfect. Today’s user experience may be close to our ideal, but as developers, we must confront this challenge head-on: what do we need to do to improve it?
In this article, we’ll explore what the Lightning Network user experience might look like, based on solutions currently being developed by some of the brightest minds in the space.
We’ll start by outlining today’s user experience and its pain points. Then, I’ll illustrate a possible future for the Lightning Network with the help of technologies that are already being implemented or actively developed.
What challenges does the Lightning Network face in 2023?
Let’s address the elephant in the room: today, a large portion of Lightning transactions happen through custodial wallets. Using Lightning transactions on the Nostr protocol as a rough proxy for custodial users across the entire network, nearly 90% of transactions are conducted via applications where users must trust a third party to hold their private keys.
Why do most current users opt for custodial services? Because of convenience, simple UX, and the usability challenges associated with non-custodial Lightning wallets. We can break down these current challenges into three broad categories:
Manual Effort
If users are forced to take more steps than traditional payment methods to achieve the same goal, most will lose interest. For example:
-
Users must stay online to send and receive payments. One major cause of Lightning payment failures today is an offline recipient, occurring in roughly 0.5–1% of all Lightning payments.
-
Users must share invoices outside the protocol—via text, email, instant messaging apps, etc.—to initiate or request payments, which is a cumbersome process.
-
Users running their own Lightning nodes must actively manage Bitcoin distribution across channels. Opening a channel to an unresponsive peer could leave funds idle and underutilized.
-
This represents the opportunity cost of capital on the Lightning Network: if your funds are allocated to an unresponsive peer, they cannot be used to route payments (and earn fees).
-
Technical Knowledge
These issues require users to have deep knowledge of the Lightning Network and/or unrelated protocols—something most average users are unlikely to pursue.
-
Setting up a Lightning node requires technical proficiency. A Lightning node must remain constantly online to maintain connectivity with the rest of the network.
-
If a user's node goes offline, the Bitcoin in their channels could potentially be lost or stolen.
-
-
A node operator must continuously rebalance liquidity across their channels; if there's no outbound balance on your side, you can't send payments; conversely, if all funds are on your side, you can't receive payments.
-
When a payment fails or gets stuck, node operators must be proficient at using command-line interfaces to troubleshoot.
-
Backing up a node is complex—node operators need to securely store both their seed phrase and channel state, otherwise existing channels may be force-closed if connectivity is lost.
Technical Limitations
The Lightning Network's technology is not yet fully deployed. Several technical issues still need resolution.
-
We lack a standardized, user-friendly method to send payments directly to anyone without relying on centralized servers.
-
Examples include unified QR codes or experiences like paynym.
-
LNURL and Lightning Address are options, but they have drawbacks—they still depend on someone running a server somewhere.
-
-
Because a Lightning node must stay online, signing keys must also remain online, creating broad security risks.
-
Opening and closing channels incurs costs tied to on-chain transaction fees; during periods of high demand, fees spike rapidly, making channel operations expensive.
-
To avoid this, users must open channels before fee spikes—but predicting optimal timing isn’t easy.
-
-
Privacy on the Lightning Network remains insufficient.
-
When requesting a payment on Lightning, you must expose certain information, such as your node’s IP address.
-
While senders generally enjoy better privacy than receivers, they still leak some data during transactions.
-
Due to how Lightning nodes communicate, third parties can easily identify the on-chain UTXOs associated with channel funding transactions. If performed at scale, this surveillance could lead to network-wide de-anonymization.
-
(Editor’s note: The problems described here are real, but most are irrelevant to the average Lightning Network user.
To use (trust-minimized) Lightning payments, your node doesn’t need to be online 24/7—your self-custodial Lightning wallet (which is effectively a node) only needs to be online when sending or receiving payments.
Additionally, you should regularly open the app to ensure your counterparty hasn’t cheated you. The biggest pain points for regular users are those mentioned above:
(1) Needing to stay online when receiving/sending payments;
(2) Lack of reusable payment requests (invoices are one-time-use);
(3) Inbound/outbound liquidity issues—if your peer has no balance in the channel, you can’t receive payments.
Currently, custodial wallets supporting LNURL eliminate these issues for users—but at the cost of requiring trust. Wallets with LSP support mainly solve the third issue and significantly enhance UX (users don’t need to manage channels themselves), but resolving the first two still depends on technological progress—spoiler alert: they’re solvable.
That said, broader adoption of the Lightning Network and improved user experience also depend on node operators overcoming these pain points, because the Lightning Network is a network.)
What would the Lightning Network look like if most (if not all) of these issues were resolved?
The Lightning Network User Experience in 2025
Here, we focus on the potential of the Lightning Network’s user experience. This isn’t a concrete roadmap, just a projection of what UX could be like once certain upgrades are deployed.
Channel Splicing: Making Channels Invisible to Users
We expect “splicing” to become widely available across Lightning wallets in the coming years—but what does this mean for network participants?
First, node operators will be able to add or remove funds from channels without incurring excessive on-chain fees, and without needing to close and reopen channels (Editor’s note: meaning capacity can be adjusted while keeping the channel active). As resizing channels becomes cheaper, node operators—or automated software—can better manage their channels, leading to higher payment success rates.
Lightning Service Providers (LSPs) can also benefit from reduced (channel resizing) costs and deliver stronger user privacy. Privacy-focused LSPs can pool user funds together, batching splicing transactions to obscure fund origins.
Once splicing becomes widespread, moving funds between the Lightning Network and Bitcoin blockchain will be cheap and seamless, wallets will display a unified balance—because users no longer need to distinguish between on-chain and off-chain funds.
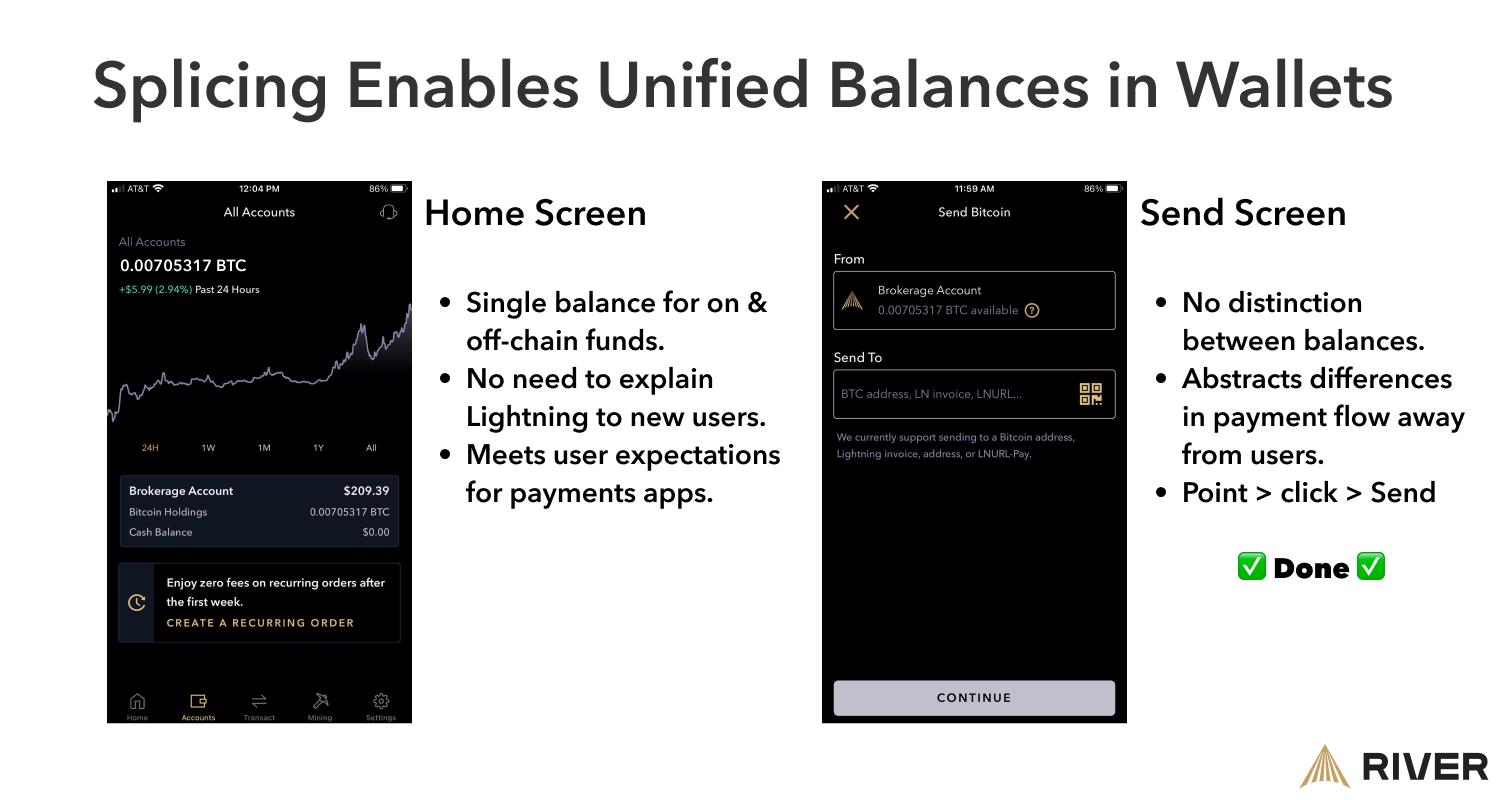
During periods of high on-chain fees, LSPs can cheaply manage user channels by combining splicing with atomic rebalancing on sidechains (such as Liquid).
(Editor’s note: Phoenix mobile wallet already supports channel splicing; their developers have detailed the resulting user experience improvements.)
Lightning Service Providers Lowering the Barrier to Entry
In the near future, LSPs may become a key part of the user experience, as they can hide complexity and reduce the capital required to run a node, acting as gateways into the network.
The magic of the Lightning Network lies in its instant settlement, but failed payments and other pain points degrade the user experience. With infrastructure provided by LSPs—whether services or the nodes themselves—users can interact with the Lightning Network more directly. LSPs can eliminate the need for user interaction with infrastructure entirely by offering a “cloud node” model, where users retain control over their funds without interacting with the node. LSPs could also offer lighter versions consuming less phone battery, or combine both models.
As more capital moves onto the Lightning Network, users must be able to restore their Lightning node (or wallet) just like an on-chain wallet—for example, by entering a sequence of 12 or 24 words in the app. Service providers can let users store encrypted backups of their Lightning wallets in the cloud. If a device is damaged or compromised, the encrypted backup can be easily restored on a new device.
Eliminating Manual Steps
If people must take extra steps to benefit from Bitcoin (or any magical tech), many will drop off along the way.
Current solutions exist for this problem: LSPs can receive payments on behalf of offline users, eliminating the need to “stay online”, making the experience closer to existing payment systems.
As Bitcoin developers gain more funding, more solutions will emerge enabling independent payment reception without third-party reliance.
Payment IDs like Lightning Address are usable today but almost always supported by custodians. Users need to receive payments using reusable QR codes without depending on third parties. Reusability is crucial: copying, pasting, and sending invoices to payers involves too many steps. A simple solution would benefit all Lightning users.
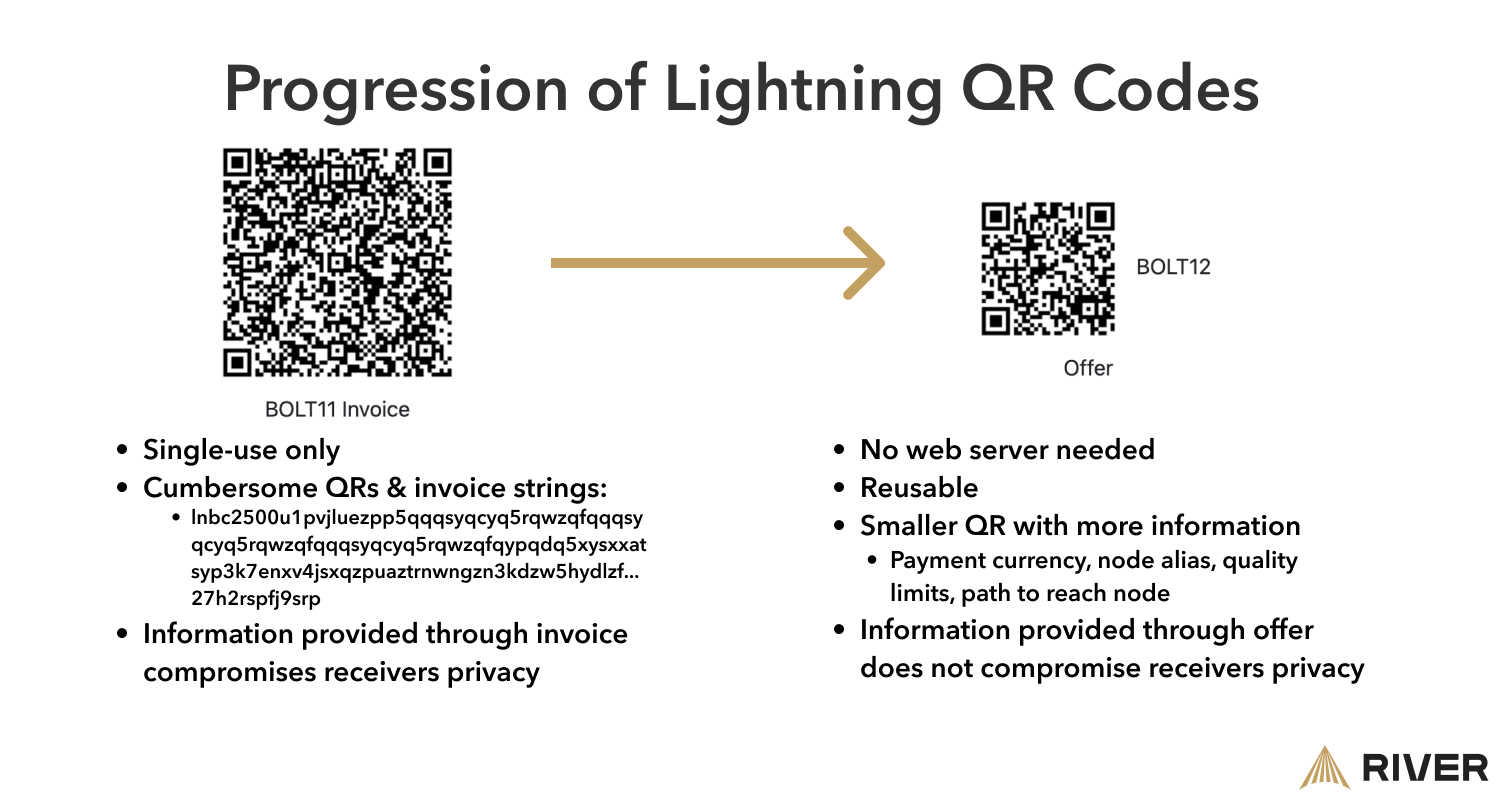
In the image above, smaller, simpler QR codes called “offers” allow wallets to handle invoice requests automatically, without user intervention. Another benefit of offers is that they can carry metadata such as currency, vendor name, quantity limits, and routing paths to the recipient’s wallet.
Many users prefer simple onboarding, meaning they may favor setups involving trusted service providers. One example is the Fedimint protocol: a group manages an “e-cash mint.” This model provides better privacy and enables additional products and services such as inheritance management, private mining pools, decentralized dispute resolution, synthetic USD positions, and more. Since Lightning is embedded within these communities, users can seamlessly join or leave different federations based on personal judgment, with low migration costs.
Privacy by Default on the Lightning Network
For privacy to become standard on the Lightning Network, privacy-enhancing technologies must operate invisibly—meaning users benefit without taking any action. App developers and service providers must work behind the scenes, for instance, isolating on-chain transactions from Lightning activity.
Thwarting Surveillance on the Lightning Network
It will become extremely difficult to determine whether an on-chain transaction opens or closes a Lightning channel, as new technologies make them indistinguishable from regular Bitcoin transactions. With wider adoption of Taproot features like signature aggregation, details about payment channels—including the number of participants—can be hidden. (Editor’s note: this relates to Schnorr signatures introduced in the Taproot upgrade, which under certain conditions can aggregate both parties’ signatures into one, making cooperative channel closures indistinguishable from ordinary wallet transactions.)
With widespread Taproot adoption in wallets, users can gain better privacy when paying peers beyond their direct counterparties. Currently, multi-hop payments carry a payment ID (the hash of the payment) visible to every intermediate node along the path. Certain Taproot-based signature schemes can create “puzzle” payment IDs, preventing forwarding nodes from seeing the full picture—only sender and receiver have complete visibility. (Editor’s note: this also relates to Schnorr signatures and the related “PTLCs” technique, where each hop receives unique information.)
Lightning users may no longer need to worry—or even know—the specific path their payment takes, whereas today every node along the route can see where the payment originated. (Editor’s note: this appears to be a misunderstanding—the intermediate nodes do not know the origin of the payment.) During the “Canada Freedom Convoy” event, we saw how governments can and will seize funds, freeze fiat bank accounts, and censor dissenters.
LSPs can anonymize the origin of a Lightning transaction by acting as blinded intermediaries in routing. In this setup, the LSP knows only part of the payment path, while the sender knows the rest; intermediate nodes and the destination remain “blinded.” This model provides stronger security with zero user involvement.
(Editor’s note: the technology referenced here is “path probing.” Currently, Lightning recipients must reveal their network location so payers can find a route. “Path blinding” allows recipients to provide an entry point to their route, hiding their true position. Payers only need to find a path to this entry node. Contrary to the author’s implication, path blinding primarily protects recipient privacy. How much the LSP learns depends on its position between the entry node and the recipient.)
Using the Lightning Network as a Virtual Private Network
Wallets can creatively offer privacy-enhancing features. For example, wallets and LSPs can act as “invoice proxies” for users: a wallet creates an invoice and forwards it to an LSP, which then completes the payment. To the recipient, it appears the LSP paid them—thus enhancing sender privacy without changing familiar payment flows. Tony Giorgio, co-founder of Mutiny Wallet, notes this approach lets wallet users blend into the crowd of all LSP users.
A minority of Lightning users may desire stronger privacy. Transaction obfuscation techniques are proven ways to enhance privacy, but they require manual effort and often incur high on-chain fees. Since LSPs already operate servers, they are well-positioned to coordinate collaborative transaction services for users. Service providers can create privacy checkpoints: when users open or close channels, adjust channel capacity (as discussed in the “channel splicing” section), or pay for goods or services.
Enhancing E-commerce with the Lightning Network
Merchants can use Lightning payments to offer customers a return period. Customers can pay a special invoice at checkout, retaining the ability to “retract” the transaction until goods or services are delivered. This was previously impossible.
Security Is Key to Institutional Adoption
To bring more institutions onto the Lightning Network, it must be effortless to move funds from offline cold wallets into Lightning channels without sacrificing security. Taproot channels enable this use case securely.
Moreover, this allows institutions to safely hold large amounts of capital on the Lightning Network. They can use custom hardware to protect against risks associated with online wallets.
Conclusion
The Lightning Network has proven its utility for instant settlement payments—but we must acknowledge it’s not flawless. Still, network participants can remain optimistic about solving UX barriers; some of the smartest developers are tirelessly improving the user experience.
As more technical solutions emerge and more capital flows into Lightning, LSPs may play an increasingly vital role in shielding end users from complexity. Technological advances will also benefit self-custody users, bringing the entire network closer to a “just works” experience.
There’s much to be excited about on the Lightning Network; all the future projections in this article are grounded in solutions currently under development. The more developers and businesses focus on optimizing UX, the greater the network participation and capital inflow—and the better the experience for everyone.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News