Cambridge Study: Undersea Cable Cuts Have No Impact on Bitcoin; Centralization of Cloud Services Is the Real Risk
TechFlow Selected TechFlow Selected

Cambridge Study: Undersea Cable Cuts Have No Impact on Bitcoin; Centralization of Cloud Services Is the Real Risk
Seven submarine cables were cut simultaneously—Bitcoin barely flinched, but research uncovered its true vulnerability.
Author: CryptoSlate
Translated by TechFlow
TechFlow Intro: A Cambridge University research team analyzed 11 years of data and 68 verified submarine cable failures—and found that cutting undersea cables has virtually no impact on the Bitcoin network. Yet they uncovered a real vulnerability—not underwater, but among cloud providers such as Hetzner, AWS, and Google Cloud. This study’s conclusions powerfully refute the “Bitcoin fragility” narrative while offering a quantitative framework for assessing genuine infrastructure risks.
Full Text Below:
In March 2024, seabed disturbances near Côte d’Ivoire severed seven submarine cables, triggering severe regional internet disruption (measured by IODA score >11,000).
For Bitcoin, however, the global impact was negligible. Only about five nodes were affected in the impacted region—just 0.03% of the global network—with a node loss magnitude of -2.5%, well within normal fluctuation ranges.
No price volatility. No consensus interruption.
A new Cambridge study covering 11 years of Bitcoin network data and 68 verified submarine cable failure events concludes that such failures have historically caused extremely limited disruption to the Bitcoin network.
In contrast, coordinated attacks targeting just a few hosting providers are up to an order of magnitude more effective at disrupting observable nodes than random infrastructure failures.
Notably, China’s mining crackdown and the broader adoption of censorship-resistant infrastructure may have unintentionally steered Bitcoin toward a more robust network topology.
Tor—long viewed as a privacy tool—is now functioning as a structural resilience layer. Most Bitcoin nodes operate over Tor.
Empirical Data Contradicts Concerns
Cambridge researchers Wenbin Wu and Alexander Neumueller built a dataset spanning 2014–2025: 8 million Bitcoin node observations, 658 submarine cables, and 385 cable failure reports—cross-referenced with outage characteristics.
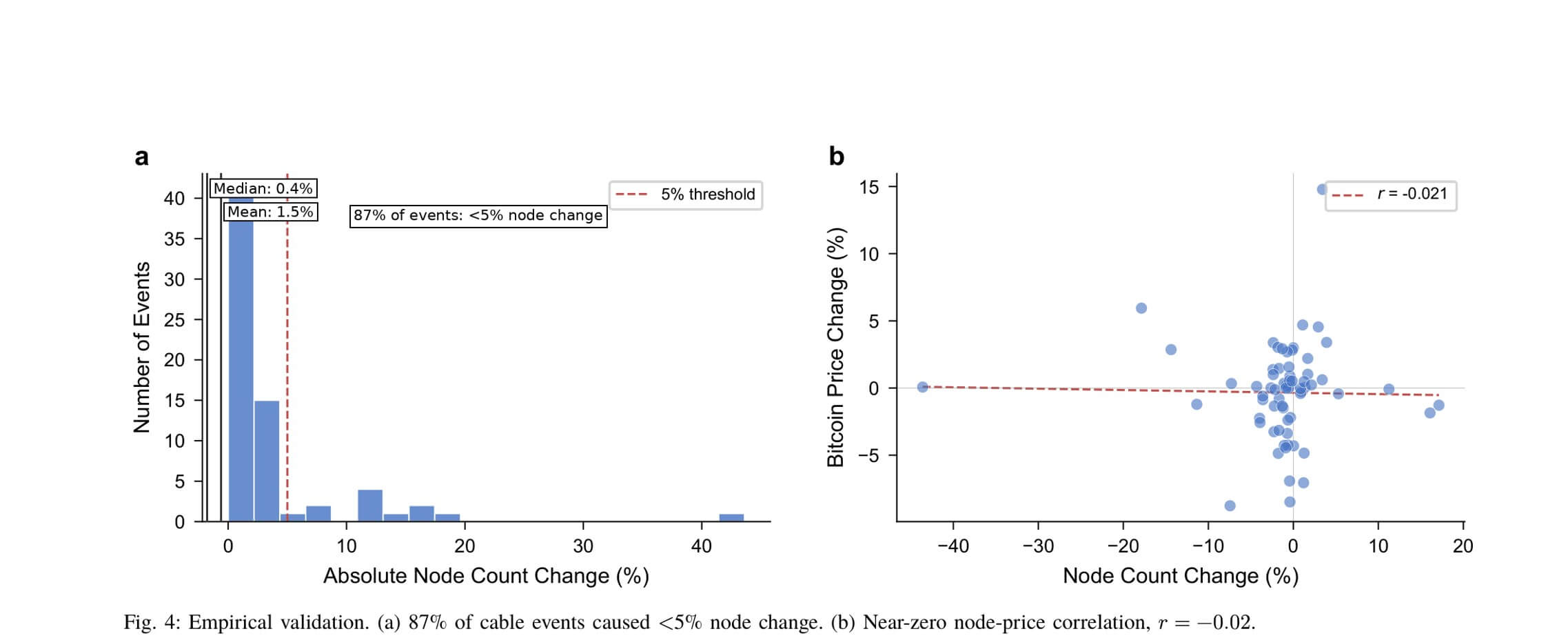
Of the 385 reports, 68 matched verifiable outages. In 87% of these validated cable events, node changes remained below 5%. The average impact was -1.5%; the median, -0.4%.
Node disruptions showed near-zero correlation with Bitcoin price (r = -0.02). Cable failures dominating regional headlines typically left no trace across Bitcoin’s distributed network.
The study models Bitcoin as a multilayer network: a physical connectivity layer linking 225 countries via 354 submarine cable edges; a routing infrastructure layer (autonomous systems); and the Bitcoin peer-to-peer overlay layer.
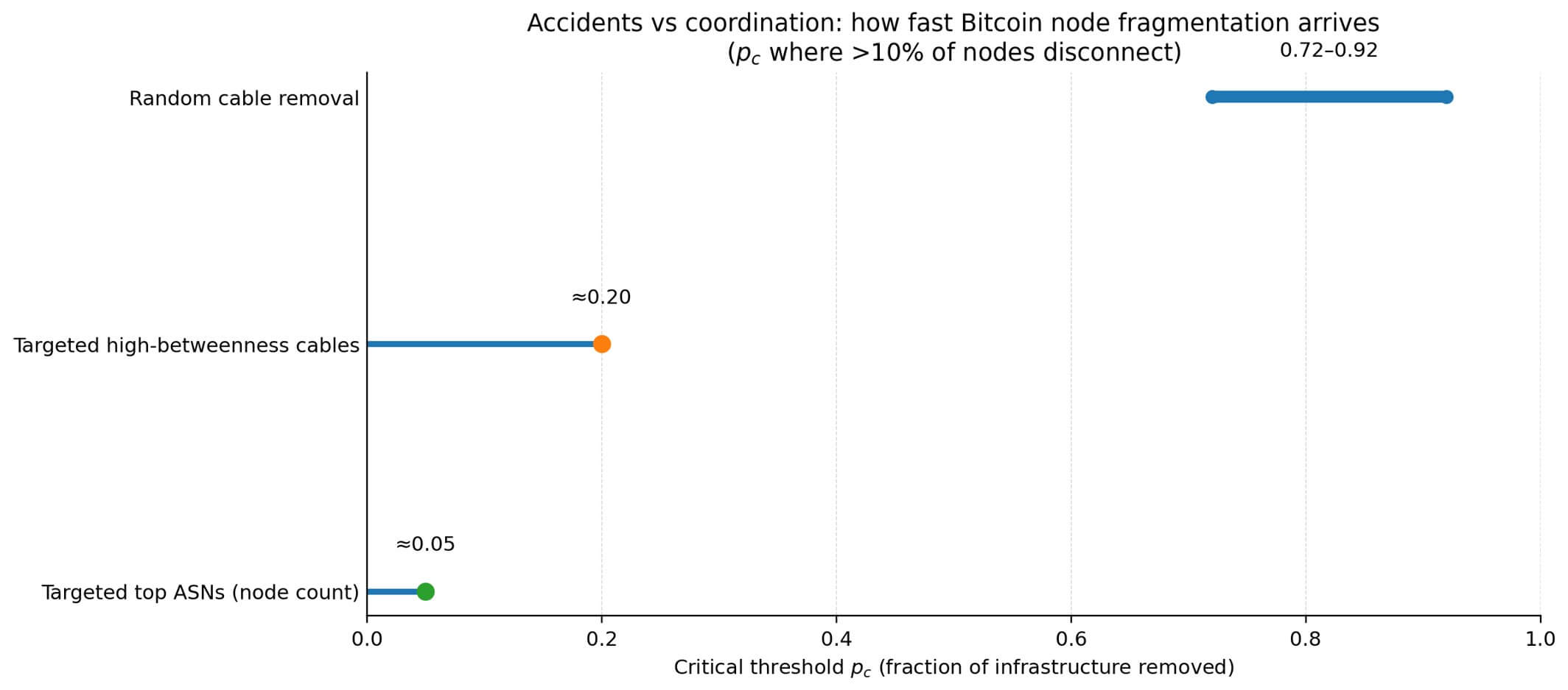
Under random cable removal, the critical threshold for >10% node disconnection falls between 0.72 and 0.92. Meaningful fragmentation of Bitcoin would require near-total failure of inter-country cables.
Where the Real Vulnerability Lies
Targeted attacks operate very differently. Random cable removal requires disabling 72%–92% of cables to reach the 10% node-disconnection threshold; targeted attacks against high-betweenness centrality cables reduce that figure to just 20%.
The most effective strategy targets top autonomous systems (ASNs) by node count—removing only 5% of routing capacity suffices to hit the threshold.
The authors characterize this ASN-targeted scenario as “hosting provider shutdowns or coordinated regulatory action—not actual physical cable cuts.” The model identifies top networks including Hetzner, OVHcloud, Comcast, Amazon Web Services (AWS), and Google Cloud.
A Bitnodes snapshot from March 2026 confirms this pattern: Among 23,150 accessible nodes, Hetzner hosts 869, Comcast and OVH each host 348, AWS hosts 336, and Google Cloud hosts 313.
This is not a claim that “five providers could destroy Bitcoin.”
Even if the entire public network were removed, most nodes would remain operational—because Tor carries the bulk of the network. Yet this finding reveals where coordinated actions could generate connection shocks and propagation disruptions absent from random cable failures.
Recent cloud service outages illustrate this risk category. Amazon attributed a March 2026 outage to a failed software deployment; other reports described AWS Middle East outages following a data center attack.
These incidents had no meaningful impact on Bitcoin—but they confirm that hosting-provider–correlated failures are real, not theoretical.
Tor as a Structural Resilience Layer
The composition of the Bitcoin network has shifted significantly.
Tor adoption rose from near zero in 2014 to 2,478 nodes (23%) in 2021, then to 7,617 nodes (52%) in 2022. By March 2026, 14,602 of the 23,150 accessible nodes ran over Tor—63% of the total. This growth coincided with multiple censorship events: Iran’s internet blackout in 2019, Myanmar’s 2021 coup, and China’s 2021 mining ban.
Node operators independently migrated to censorship-resistant infrastructure—demonstrating the network’s adaptive, self-organizing capacity.
Tor introduces a challenge: Most Bitcoin nodes are now unobservable in terms of location.
To address this, the authors construct a four-layer model treating Tor relays as a distinct network layer. Tor relays are physical servers whose locations are known.
Using consensus weight data from 9,793 relays, the authors model how cable failures severing national connections simultaneously take relays offline.
The findings were unexpected. The four-layer model consistently yields higher critical failure thresholds than models considering only the public network—by 0.02 to 0.10.
Most Tor relay consensus weight is concentrated in Germany, France, and the Netherlands—countries with extensive cable connectivity. Cable failures severing peripheral nations’ connections do not diminish relay capacity in these well-connected countries.
An attacker must disable more infrastructure to simultaneously disrupt both public-network routing and Tor circuits.
The China Factor
Bitcoin’s resilience hit its lowest point—0.72—in 2021, coinciding with peak hash rate concentration.
Cambridge data shows that in 2019, 74% of hash rate was located in East Asia. Geographic concentration of nodes reduced public-network resilience by 22% between 2018 and 2021.
The rebound in 2022 was strong: Following China’s mining ban, infrastructure decentralization lifted the threshold to 0.88, while Tor adoption accelerated in parallel.
Though the authors avoid asserting singular causality, regulatory pressure clearly drove geographic redistribution—and spurred adoption of censorship-resistant infrastructure—both enhancing network robustness.
Apparent centralization partly stems from measurement error. As Tor adoption rose, the public-network sample became concentrated in fewer locations: the Herfindahl-Hirschman Index jumped from 166 to 4,163, yet Hetzner’s actual share fell from 10% to 3.6%. This concentration reflects sampling bias—not true centralization.
Cloud Providers Are the Real Risk
Concerns over submarine cable security will continue rising. Investigations in the Baltic Sea, the European Commission’s Security Toolbox, and reporting on Russian infrastructure all point to persistent geopolitical anxiety.
For Bitcoin, historical data shows most cable events are mere noise.
The infrastructure issue truly worth watching is whether policy coordination, cloud service outages, or hosting restrictions can generate connection shocks at the autonomous system level.
The ASN-targeted scenario’s operational threshold is 5% of routing capacity—the tipping point for noticeable disruption among accessible public-network nodes, not consensus failure.
Tor’s majority share provides a floor under extreme scenarios. Protocol-layer mechanisms not included in the study—such as block relay networks, compact block relay, and Blockstream Satellite—add further resilience layers, making the estimates conservative.
Bitcoin is not as fragile as critics imagine—but neither is it fully decoupled from infrastructure.
The network exhibits graceful degradation—not catastrophic collapse—under stress. Censorship pressure drives infrastructure adoption, which in turn strengthens resistance to coordinated risks.
Threat models starring submarines cutting undersea cables overlook closer chokepoints: a handful of networks where coordinated action—without dramatic underwater operations or acts of war—can cause temporary disruption.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News