After EIP-3074, can malicious signatures lead to Ethereum account funds being depleted?
TechFlow Selected TechFlow Selected
After EIP-3074, can malicious signatures lead to Ethereum account funds being depleted?
The caller field in EIP-3074 signatures is crucial; a malicious caller could steal your funds.
Author: lightclients
Translation: MetaCat

After EIP-3074, a single mistaken signature could drain the balance of your Ethereum account.
Yes, this is real.
Co-author of EIP-3074 here! Let me temporarily calm down this concern before things get more out of hand.
First: I’m not aware of any wallet currently supporting signing unprefixed data. This means no wallet currently supports EIP-3074. No matter how many dashboards you browse or how many advanced features you open. You cannot sign EIP-3074 messages right now.
The messages you sign to “log in” to dapps use a standard based on EIP-191, completely different from EIP-3074. This prepends the following data to your signed message:
0x19 <0x45 (E)> <thereum Signed Message:\n" + len(message)> <data to sign
This is why it’s impossible to trick someone logging into a dapp into actually signing a valid Ethereum transaction.
Transactions are prefixed with a single-byte value:
0x01 - 2930 tx
0x02 - 1559 tx
0x03 - 4844 tx
More info at: https://github.com/ethereum/execution-specs/tree/master/lists/signature-types
EIP-3074 plans to use prefix 0x04. This eliminates ambiguity with all other types of signable data in Ethereum. Wallets must actively choose to allow users to sign these messages.
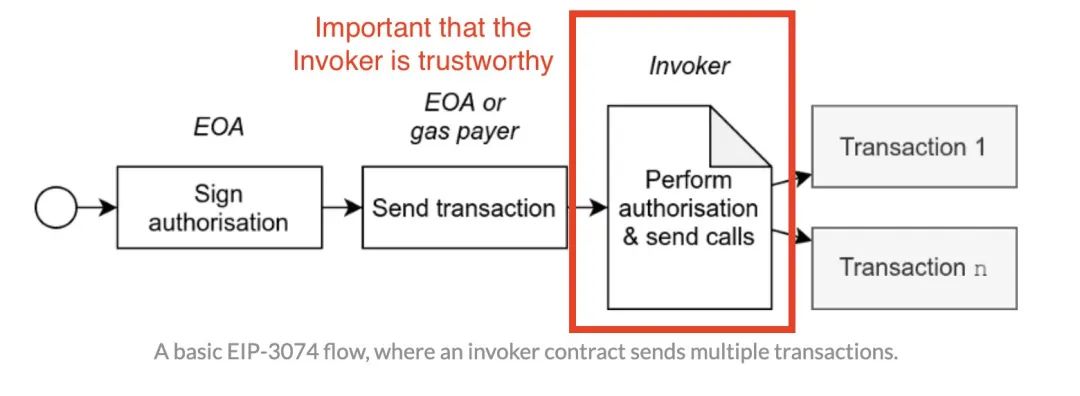
Depending on how exactly wallets integrate EIP-3074, it may create situations where users are more easily exploited. To understand this, we need to make sure we understand how EIP-3074 signatures work.
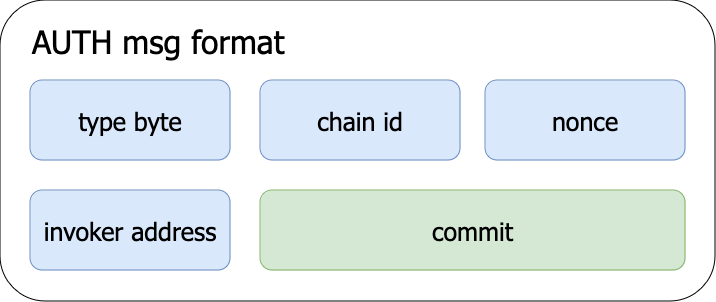
The authentication message used to construct the signature has the following fields. Importantly, it includes a caller address—the only address AUTH considers valid for the signature.
For an account to be drained, both of the following must be true:
1) The wallet needs to allow users to sign to any invoker address,
2) The user must fail to verify whether the invoker is trustworthy.
This means either one alone won’t cause problems.
We expect wallet software to understand that: An EIP-3074 invoker is more like an extension of wallet software code than a regular contract. Wallets don't allow users to freely run arbitrary code and access their private keys; likewise, they shouldn’t allow users to arbitrarily delegate their Ethereum accounts.
Therefore, if wallet software integrates EIP-3074 insecurely and users fail to verify the invoker they're interacting with, delegation to a malicious invoker might occur. However, this can still be undone by sending a single transaction from an EOA, which revokes all ongoing AUTH signatures.
At minimum, wallet software should make signing EIP-3074 messages a big deal—on par with exporting your private key.
Even assuming wallets integrate 3074 securely, accounts could still be stolen. This is a fundamental property of batch transactions. It allows you to easily send multiple operations, just as it enables attackers to trick you into sending a batch of assets to an address they control.
Wallet software must clearly display every operation you are signing. This way, it's easy to notice: "I only intended to make one transaction, but this signature request also makes me execute a dozen others." If blind signing is used for batching, this cannot be detected.
Yes, EIP-3074 places strong trust in wallets. But we already trust them with our private keys—that’s the highest level of trust!
EIP-3074 can be safely integrated and used. If any wallet has questions about how to do this properly, please feel free to reach out. As authors of EIP-3074, we’re currently thinking about how best to support the next phase of this standard’s development.
Over the past few years, we’ve spent significant time developing hypothetical scenarios around how it could be used—and abused. We’re excited these ideas are moving toward production. But we also recognize this is the most challenging part.
In summary, concerns that a single mistaken signature after EIP-3074 could drain your Ethereum account balance:
-
Currently, wallets do not support EIP-3074-style signatures, which follow a new format.
-
The invoker field in EIP-3074 signatures is critical. A malicious invoker could steal your funds.
-
Wallets must ensure the invoker address is trustworthy. This is similar to how wallets currently prevent execution of arbitrary code.
-
Batching in EIP-3074 opens up possibilities where bad actors can trick you into signing asset transfers. Wallets must clearly show what happens when signing an EIP-3074 message.
-
Yes, we place high trust in wallets, but users already entrust them with their private keys—the highest level of trust.
EIP-3074 vs EIP-4337
EIP-3074 is excellent news for account abstraction providers because it greatly benefits our users.
-
ERC-4337 is the best way to onboard new users into crypto.
-
EIP-3074 is the best way to onboard existing users into smart accounts.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News