Crypto's Killer Use Case: Building Permissionless Identity
TechFlow Selected TechFlow Selected

Crypto's Killer Use Case: Building Permissionless Identity
The primary use case for encryption has arrived: applications based on permissionless identity.
Author: KERMAN KOHLI
Translation: TechFlow
We are currently in a downturn in the cryptocurrency market—arguably hit hard by a bear market. Everyone is asking: where are the real-world use cases and value for these tech products we're building? Many have offered seemingly compelling arguments, but none provide clear reasoning as to why these products should be superior to ordinary Web2 applications. I've been thinking about this for a while, and based on personal experience and judgment, I'm cautiously optimistic about certain perspectives. This article isn't about ideology; it's focused on practical issues of technology and standards. Before we dive in, let’s first examine how the current internet works.
Web2, Data Producers, and Identity Verification
When you register for a service online, the provider doesn’t actually know your true identity, because all your information can be forged. Your IP address, browser cookies, device fingerprint—all are merely approximate identifiers that can be faked. Everything can be falsified.
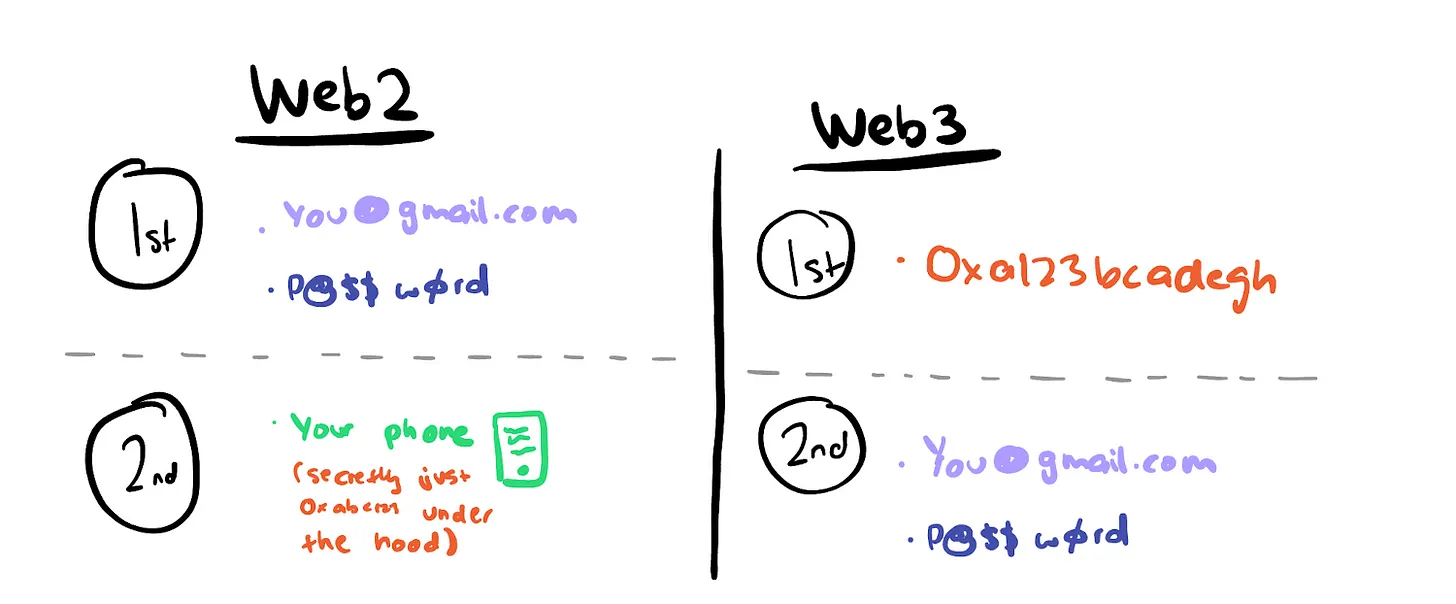
This has led to the emergence of identity verification standards primarily relying on:
-
Email addresses;
-
Passwords;
-
Two-factor authentication (2FA) schemes.
Whenever you use services online, providers need a persistent, secure identity to bind your data to. More importantly, they need a way for “you” to verify “yourself.”
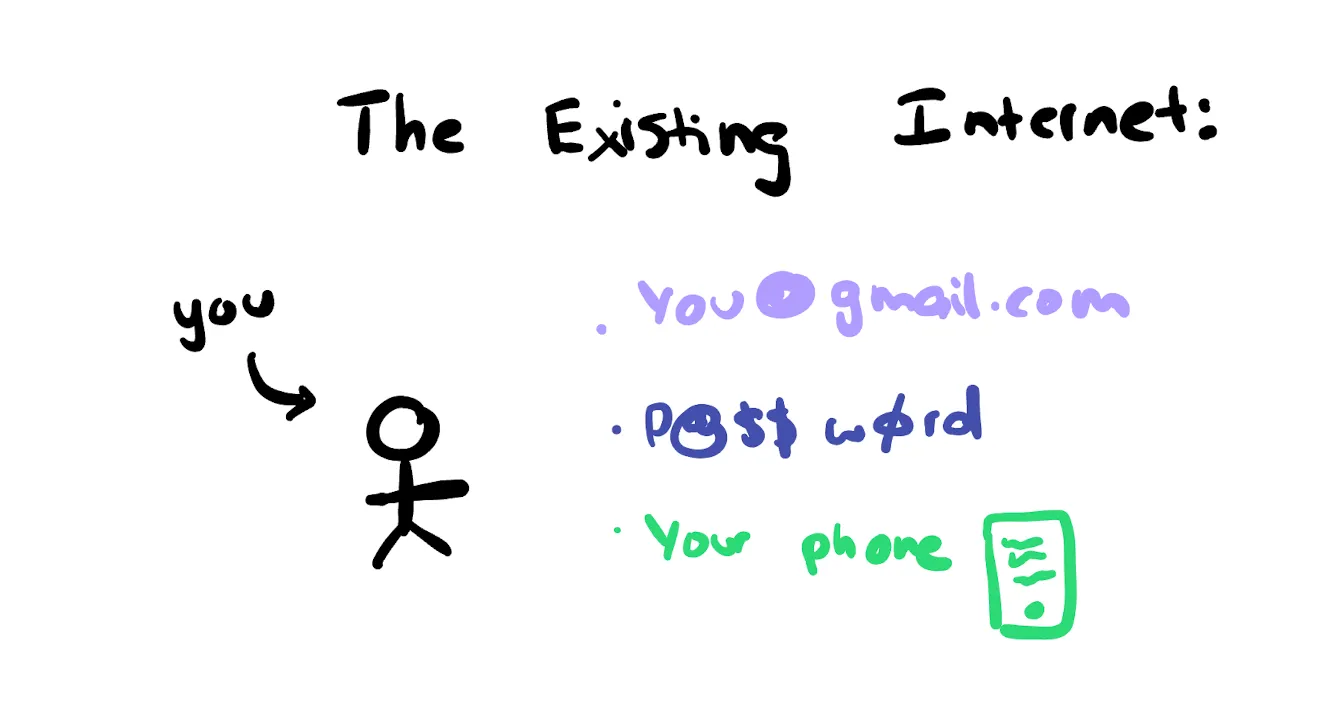
Each database creates a different identifier for you. Facebook, Twitter, Instagram each create unique identifiers for you within their databases.
When you use OAuth to log into other services, they may reference that identifier, but they still create a new entry in their own database to identify you. OAuth providers might share limited data points with external developers, who then bind any generated information to the newly created user ID in their application’s database.
You may have noticed that "you" are redundantly represented across every service you use. This isn't out of malice from Web2—it's simply the only logical approach given current hardware limitations. However, over decades of internet evolution, this has led to bigger problems:
1. All your identity and reputation data are confined within the specific ecosystem where you registered. Your Twitter followers remain Twitter’s data—you can’t export them.
2. Any information created online is tied to an identity within that service. A Google review can only show information Google owns about you.
3. Each new service you sign up for requires rebuilding trust and credibility within that ecosystem, regardless of your past actions elsewhere.
This is our current environment:
-
Your profile is the sole thing identifying you;
-
Yet, your information remains fragmented.
As authenticity and credibility of online information come under increasing scrutiny, we’re beginning to see this as a growing problem. Whenever I read opinionated articles, I typically:
-
Identify who the author is;
-
Trace their Twitter and any other sources I can find;
-
Look for references to the article on other sites;
-
Make an overall assessment of the author’s bias and opposing viewpoints.
However, I know I’m in the minority here. Most people unquestioningly accept provided information without understanding the identity of the data producer (where data is defined as any information presented via articles, tweets, videos, etc.).
The key issue we collectively face is we lack a definitive method to deterministically identify our online identities. Every time you visit a website, receive a message, or get an email, you risk communicating with the wrong person due to reliance on unique usernames. This is already creating serious problems—we can no longer reliably identify ourselves in digital communication.
I could be "XXX.eth" on-chain, "XXX" on Telegram, and "xxx" on another platform. But if someone messages you on Telegram as "xxx," you might assume it's me. Without public key authentication, trust online is a mess.
Over time, the lack of stronger, persistent digital identity recognition has become a shared human challenge.
Cryptography and Crypto Timestamps
Part 1: Cryptography
This might sound strange—bear with me. They are two distinct yet similar-sounding concepts.
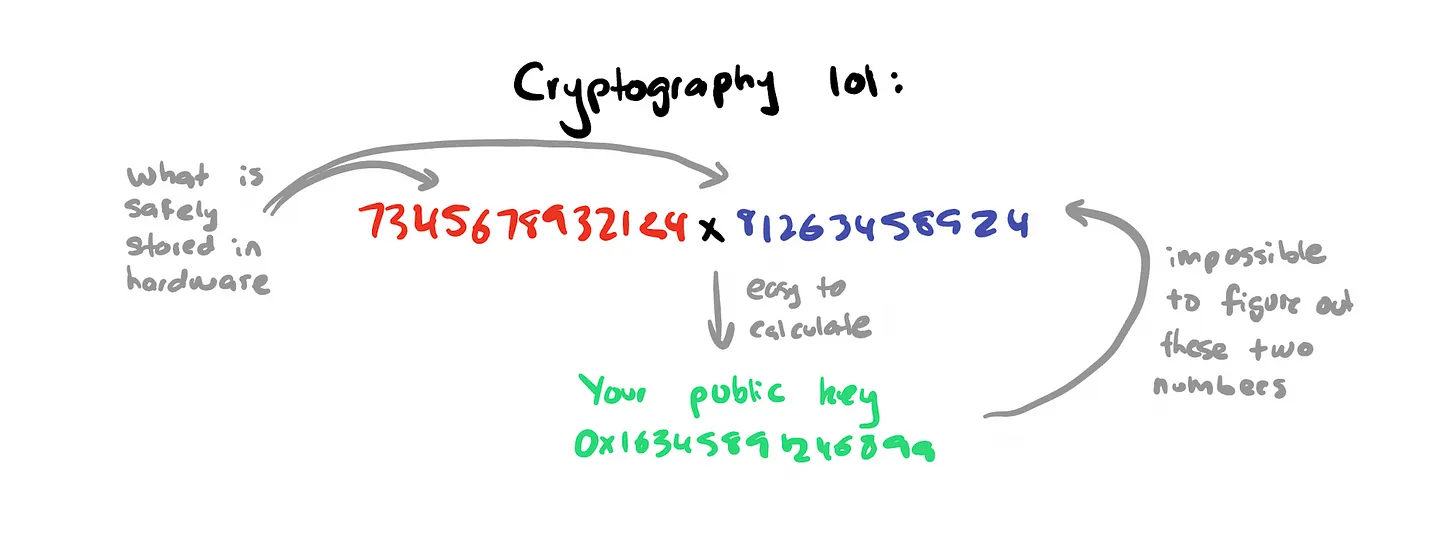
Cryptographic identity fundamentally involves multiplying two large prime numbers to generate a larger number. While this sounds simple, the complexity lies in the fact that guessing those primes is essentially impossible—they are practically unbreakable. When you authenticate using a private key, your hardware uses unique information to establish its identity. This represents a critical shift in identity management: the identity owner knows large numbers that are also universally recognized by standard protocols on the receiving end.
In contrast, traditional web infrastructure forces us to re-establish identity for every new service, resulting in different IDs across databases.
Part 2: Crypto
How do blockchains fit in? The second tricky part of this puzzle is: how do you verify when information was broadcast? If you just sign a message with today’s date, how do you know it’s accurate? Maybe you delegate timing responsibility to a third party—but what if they’re compromised? You end up with recursive logic.
Blockchains are innovatively databases that record timestamped information. They don’t rely on human-dependent notions of time; instead, they use block numbers to determine when something occurred. I don’t think we fully appreciate how groundbreaking this is. You don’t send a transaction with a “timestamp” field. You simply submit the transaction to the network—when miners include it in a block, it gets timestamped.
Think about it: what system exists where you give it information, and it tells you exactly when that information was actually produced? We always expect that when we say something or communicate online, that’s when it “happens.” Not in crypto. When we want to convey information on-chain, we only express what we want to say—the blockchain tells us when it happened.
To recap:
-
Cryptography creates a shared standard for identity verification that everyone can agree on;
-
Crypto, powered by blockchains, creates a shared standard for time that everyone can agree on.
Why Identity Matters?
Amid our collective obsession with wealth, we’ve forgotten that blockchains represent two fundamental innovations. It also means we can start changing the world by introducing one innovation and gradually adding the second when meaningful. You don’t need both simultaneously to make an impact.
By 2023, with the rise of AI, the world needs stronger identity standards. Information is foundational to society, but when trust and verification of information erode, we end up in dangerous territory.
Sending stablecoins and playing casino games are fun, but cryptocurrencies can solve much bigger challenges facing society today. Because crypto is built on the foundation of cryptography, it has a far more robust ecosystem in cryptographic standards than anywhere else. You can already see cryptography becoming the gold standard, as seen with Apple adopting PassKeys and the rise of one-time passwords for 2FA.
-
In Web2, cryptography is a second-class citizen.
-
In Web3, cryptography is a first-class citizen.
Alright, now we’re on the same page—let’s talk about cryptocurrency and identity. I’ve been deeply involved in this issue for years, and I believe I’ve identified some previously overlooked key insights. The biggest use case for crypto isn’t “decentralized identity” or some noble ideal. It’s not about:
-
“Owning your data and monetizing it”;
-
“Uploading your passport to the blockchain for better KYC”;
-
“Linking your Twitter, Facebook, and Ethereum address to create a new identity.”
These ideas are far removed from reality—empty narratives that haven’t created products helping real users. Such narratives mainly serve to raise massive funding from investors, without adding value for end consumers. To clarify these misconceptions, it’s crucial we use better language. I believe statements like “on-chain identity” lead to wrong conclusions, implying you must operate on-chain—which isn’t true either.
The Way Forward
Permissionless Identity: “Portable, Persistent, Cryptographically-Secured Identity”
These are public keys as we know them today. Whether data resides on-chain or off-chain doesn’t matter. The point is you authenticate on digital services via public keys. All information binds to your public key, enabling interoperability.
Here’s why they hold clear advantages over any Web2 system we have today:
-
Built in one environment, usable in another. All your activities and data in one ecosystem can be accessed in a completely unrelated one.
-
Permanence. Once a private key is derived, it doesn’t disappear. You cannot delete a private key or on-chain data.
-
Usable on-chain or off-chain. Your identity is the aggregate of everywhere you authenticate via public key, on or off-chain. The innovation matters—not the blockchain.
-
Ability to create new identities (or fragments) with a click, alongside existing ones. Unlike Web2, where all identities ultimately tie back to your passport (phone number, ISP), permissionless identities require no permission to create or fragment.
-
Accessible to anyone with internet access and proper hardware. No “issuing” authority generates identities. As long as you have the right infrastructure to protect your identity, you can create one. Due to its borderless nature, the possibilities enabled by such an identity are limitless.
Conclusion
Permissionless identity fundamentally enables an entirely new category of applications—ones that are 10x better than anything we see on the current web. A world where one app enhances the experience of all others. You’ll begin to see a flywheel effect develop, which I envision unfolding as follows:
-
As crypto-native consumer apps emerge, they will naturally rely on permissionless identity as a default authentication standard.
-
These apps will begin to sense context from your behavior and actions across past interactions and other applications.
-
The ability to “import” context from the past and elsewhere enables significantly better user experiences.
-
Users demand more apps support public key-based authentication for login and usage.
-
As the number of apps supporting public key authentication grows, users derive greater utility from their permissionless identities.
I’d bet the primary use case for crypto has already arrived: applications built on permissionless identity. The sooner we realize this, the faster we can move forward in creating applications that people actually need.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News