On the Eve of the Post-Quantum Era: How Will Bitcoin Build Its Next-Generation Security Defense?
TechFlow Selected TechFlow Selected

On the Eve of the Post-Quantum Era: How Will Bitcoin Build Its Next-Generation Security Defense?
The Bitcoin community needs to urgently research post-quantum cryptography and reach consensus to address the "quantum reckoning" crisis, which could lead to a collapse of trust and market turmoil.
By Luke, Mars Finance
As night fell over Las Vegas, a rare sense of gravity hung in the air during a private lunch at the Bitcoin 2025 conference. The atmosphere was far from the city’s usual hedonistic clamor—instead, seasoned experts in cryptocurrency voiced a deeper concern: quantum computing, once seen as a distant and abstract threat, is advancing at an alarming pace, its cold light now falling upon Bitcoin's seemingly impregnable cryptographic defenses. Warnings suggest that powerful quantum computers could crack Bitcoin’s private keys within years, putting approximately $42 billion worth of Bitcoin at risk—and potentially triggering a market-wide "cleansing event."
This is no exaggeration. Recent research from Google's Quantum AI team has poured fuel on the fire, showing that the quantum resources needed to break the widely used RSA encryption algorithm have dropped by a factor of 20 compared to earlier estimates. Although Bitcoin uses the Elliptic Curve Digital Signature Algorithm (ECDSA) rather than RSA, both rely on mathematical problems vulnerable to quantum algorithms. As Jameson Lopp, co-founder of Casa, urgently warned: "The Bitcoin community must reach consensus and find mitigation strategies before the quantum threat becomes an existential crisis."
How close are we to this future—one where quantum computing could dismantle Bitcoin’s security? This is not merely a technical question; it strikes at the heart of trust, wealth, and the fate of an entire emerging industry.
How Does the Quantum Ghost Knock on Bitcoin’s Cryptographic Door?
To understand the quantum threat to Bitcoin, one must first examine the bedrock of its security: ECDSA. In simple terms, when you create a Bitcoin wallet, a key pair is generated—a private key (which you must keep absolutely secret) and a public key (which can be shared publicly). The public key undergoes hashing to produce a Bitcoin address. When making a transaction, you use your private key to digitally sign it, allowing others on the network to verify that the signature came from you and that the transaction hasn’t been altered. For classical computers, deriving the private key from the public key is mathematically infeasible—this is the foundation of Bitcoin’s security.
However, the emergence of quantum computers, particularly Peter Shor’s 1994 breakthrough known as Shor’s algorithm, changes everything. Shor’s algorithm efficiently solves large integer factorization and discrete logarithm problems—the very mathematical foundations underpinning the security of public-key cryptosystems like RSA and ECDSA. Once sufficiently powerful and stable quantum computers are built, they could theoretically use Shor’s algorithm to compute private keys from known public keys in a matter of moments.
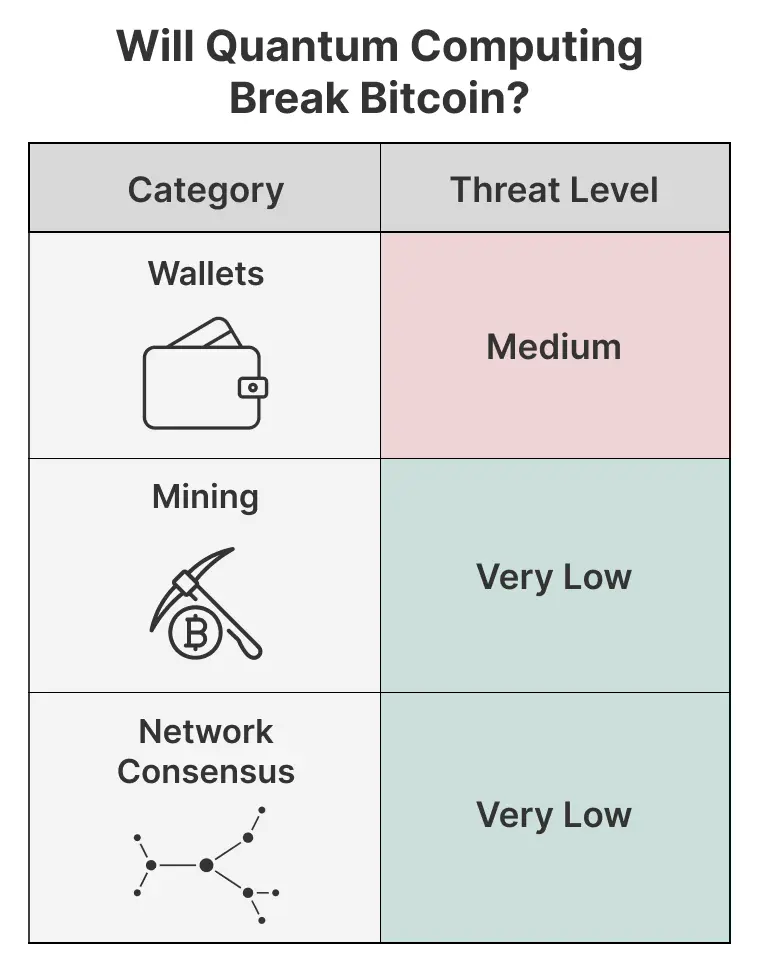
Which Bitcoins are most exposed to quantum attacks? First in line are addresses that directly expose their public keys. The most notable example is Bitcoin’s early P2PK (Pay-to-Public-Key) addresses, which either embed or reveal the public key in transactions. It's estimated that millions of Bitcoins (some say around 1.9 to 2 million) still lie dormant in such addresses—including legendary early “genesis” coins believed to belong to Satoshi Nakamoto. Even more common P2PKH (Pay-to-Public-Key-Hash) addresses, while safer because they store only the hash of the public key, become vulnerable once funds are spent from them: the public key is then revealed in the transaction data. If these addresses are reused (i.e., multiple outgoing transactions), the public key remains exposed, creating ongoing risk. According to earlier analyses by firms like Deloitte, millions of Bitcoins may already be at risk due to address reuse and similar practices. Even newer Taproot (P2TR) addresses, despite improvements like Schnorr signatures, can in certain cases allow inference of the public key or variants thereof, leaving them not fully immune to quantum threats.
In total, the amount of Bitcoin stored in vulnerable addresses could represent a significant portion of the total supply. Earlier estimates (e.g., from 2022) suggested 4 to 6 million BTC might be highly exposed. At current prices (say, $70,000 per BTC), this represents a staggering $280–420 billion in value. This likely explains the origin of the "$42 billion" figure—it’s less a precise number than a symbolic warning about vast wealth sitting atop fragile cryptographic foundations.
Even more troubling is the so-called “short-range attack.” When you initiate a Bitcoin transaction, your public key is broadcast across the network along with the transaction, waiting for miners to confirm it—a process that typically takes 10 to 60 minutes. If a quantum computer can extract the private key from the public key during this brief window, it can forge a new transaction with a higher fee, stealing your Bitcoin before your original transaction confirms. Should such attacks become feasible, virtually all Bitcoin transactions would face immediate danger.
The Quantum Hardware Race: From Theory to Reality at Speed
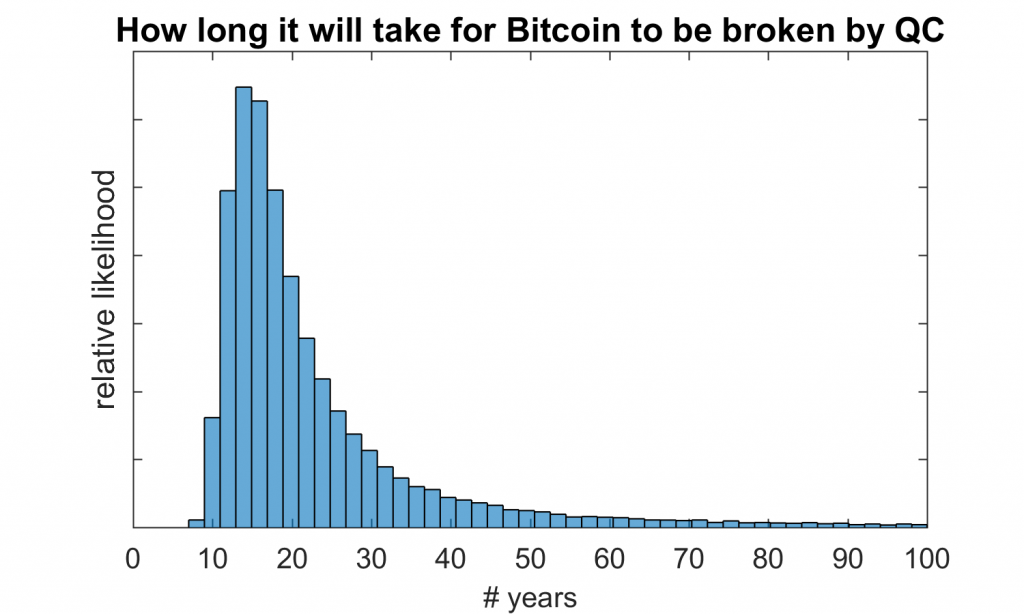
For years, building a quantum computer capable of running Shor’s algorithm against real-world cryptography seemed impossibly distant. Yet recent progress—especially in improving qubit quality, quantity, and error correction—has been remarkable. The true measure of a quantum computer’s cryptographic capability lies not just in raw physical qubits, but in the number and stability of “logical qubits” capable of executing complex algorithms reliably.
In early 2025, Craig Gidney of Google’s Quantum AI team published updated findings suggesting that breaking 2048-bit RSA encryption—widely used in traditional cybersecurity—might require fewer than a million noisy physical qubits and less than a week of runtime. This dramatic reduction stems from algorithmic optimizations and advances in error correction techniques, such as approximate residue arithmetic, more efficient logical qubit storage, and magic state distillation. While Gidney stresses that such a machine would need to operate continuously for five days with extremely low gate error rates—far beyond today’s capabilities—it undeniably shortens our perceived “quantum safety horizon.” As for Bitcoin’s ECDSA (secp256k1 curve), there is no equally precise public estimate yet comparable to the RSA-2048 analysis, but the cryptographic consensus holds that ECDSA may actually be easier to break than RSA due to its underlying mathematical structure.
On the hardware front, major players are racing ahead. IBM’s quantum roadmap is ambitious: its “Osprey” processor reached 433 physical qubits, and “Condor” achieved an experimental 1,121. More importantly, IBM focuses on improving qubit fidelity and error correction. Its “Heron” processor (133 qubits), with lower error rates, is now central to development, with plans to launch the 1,386-qubit “Kookaburra” system in 2025 via multi-chip integration. By 2029, IBM aims to deliver the “Starling” system, featuring 200 high-quality logical qubits capable of performing up to 100 million quantum gate operations.
Google continues pushing forward too. Its “Willow” chip, reportedly with 105 physical qubits, debuted in early 2025 and was described by the team as a “compelling prototype for scalable logical qubits,” achieving error rates below threshold in quantum error correction—a critical milestone toward fault-tolerant quantum computing.
In 2025, Quantinuum dropped a bombshell, announcing its “Helios” quantum system would become commercially available later that year, supporting “at least 50 high-fidelity logical qubits.” If fully realized, this would mark a pivotal leap from experimental research to practical computational power in specific domains. In May 2025, the company also demonstrated record-breaking fidelity in logical qubit teleportation, reinforcing its leadership in building high-quality logical qubits.
Nonetheless, expert predictions on when fault-tolerant quantum computers capable of threatening Bitcoin will arrive remain divided. Some optimistic (or pessimistic) forecasts suggest 3 to 5 years; others believe it will take at least a decade or more. Crucially, the quantum threat isn't a binary on/off switch—it's a gradually increasing probability. Every hardware advance, every algorithmic optimization, quietly moves the countdown closer.
Bitcoin’s Quantum Counteroffensive: Preparing in Advance or Playing Catch-Up?
Faced with this growing threat, the Bitcoin community is not helpless. The cryptographic world has long studied “post-quantum cryptography” (PQC)—new cryptographic algorithms believed resistant to known quantum attacks. After years of evaluation, the U.S. National Institute of Standards and Technology (NIST) has standardized several PQC algorithms, including CRYSTALS-Kyber for key encapsulation, and CRYSTALS-Dilithium, FALCON, and SPHINCS+ for digital signatures.
For Bitcoin, hash-based signature schemes (HBS) like SPHINCS+ are strong contenders. Their security doesn’t rely on unproven mathematical assumptions (like lattice-based cryptography), but on the well-studied collision resistance of hash functions. SPHINCS+ is also stateless—unlike predecessors like XMSS—which is crucial for blockchain’s distributed nature. However, hash-based signatures often suffer from larger signature sizes and slower key generation and verification times, posing challenges for Bitcoin’s transaction efficiency and blockchain storage. Integrating PQC without compromising Bitcoin’s core properties remains a formidable technical hurdle.
An even greater challenge lies in migrating Bitcoin from ECDSA to a new PQC standard. This goes beyond code changes—it requires fundamental protocol upgrades and the smooth transition of millions of users and trillions of dollars in assets.
First, there's the choice of upgrade mechanism: soft fork or hard fork? Soft forks maintain backward compatibility and are generally seen as lower-risk, but may lack the flexibility needed for complex PQC implementations. Hard forks abandon old rules entirely; all participants must upgrade, or risk chain splits—a historically contentious path in Bitcoin that carries high risks of community fragmentation.
Second, there’s the migration mechanism itself. How do users securely move Bitcoin from old (ECDSA) addresses to new quantum-resistant (QR) addresses? This process must be secure, user-friendly, and resistant to new attack vectors during the transition window.
Bitcoin thought leader Jameson Lopp offered profound insights in his widely discussed essay, “Against Allowing Quantum Computers to Recover Bitcoin.” He argues that allowing quantum-equipped actors to “recover” (i.e., steal) Bitcoin not protected by PQC would amount to a massive wealth redistribution favoring a small tech elite—an outcome that would severely undermine Bitcoin’s fairness and credibility. He even proposed a controversial idea: setting a “drop-dead date” after which un-migrated Bitcoin would be considered “destroyed” or permanently unspendable. Lopp acknowledges this is a painful trade-off—potentially causing asset loss for long-dormant or lost-key wallets, and possibly triggering a hard fork—but views it as a necessary “bitter medicine” to preserve Bitcoin’s long-term integrity and core values.
Another developer, Agustin Cruz, introduced a concrete hard fork proposal called QRAMP (Quantum Resistant Address Migration Protocol). It advocates a mandatory migration period, after which unmigrated Bitcoin would be “burned”—a radical push to force the ecosystem into quantum-safe status. Such aggressive proposals highlight potential divisions within the community and the immense difficulty of achieving consensus under decentralized governance.
Beyond upgrading to PQC addresses, promoting best practices like “never reusing addresses” can reduce risk, but this is only a stopgap measure—it cannot eliminate the fundamental vulnerability of ECDSA to quantum algorithms.
Ecosystem Hesitation: Caught Between Inertia and Change
Given such a systemic risk, how prepared is the Bitcoin ecosystem? Newer blockchains like Quantum Resistant Ledger (QRL) were designed from the start with PQC features, while projects like Algorand are actively exploring PQC integration. These are like nimble boats, attempting to sail ahead in the post-quantum wave.
But Bitcoin, a “ten-thousand-ton ship,” faces immense inertia due to its massive market cap, vast user base, and deeply held principles of decentralization and censorship resistance. Any core protocol change is extraordinarily difficult and slow. Awareness of the quantum threat among developers is growing, and discussions—such as Lopp’s essay, QRAMP, and scattered threads on the bitcoin-dev mailing list—are underway. Yet, a clear, widely accepted upgrade roadmap remains elusive. There is currently little public information from major Bitcoin exchanges, wallet providers, or large mining pools about their PQC transition plans—suggesting that Bitcoin’s PQC transformation remains largely in the theoretical and early discussion phase, not yet urgent engineering.
This state places Bitcoin in a paradox: “too big to fail, yet too slow to evolve.” Its powerful network effects and brand recognition are moats—but in the face of rapid technological change, that same stability can become inertia.
“Quantum Cleansing”: Far More Than Just Losing Keys
What happens if Bitcoin fails to transition to PQC before quantum computers gain practical attack capability? It would be far worse than some users losing coins.
A large-scale quantum attack could trigger a market “cleansing event.” Once confidence erodes, panic selling could send Bitcoin’s price into catastrophic freefall. The ripple effects would extend beyond Bitcoin, likely engulfing the entire cryptocurrency market and impacting traditional financial institutions with significant crypto exposure.
More profoundly, it would shatter trust. Bitcoin’s reputation as “digital gold” rests heavily on its supposedly “unbreakable” cryptography. If that foundation is easily shattered by quantum computing, every narrative of value and use case built upon it would collapse. Public trust in digital assets could plummet to historic lows.
Compared to other known risks—like 51% attacks, critical software bugs, or tightening global regulation—the quantum threat is uniquely disruptive. A 51% attack might enable double-spending or censorship, but cannot directly steal private keys. Software flaws can be patched. Regulatory pressure affects compliance and application scope. But a successful quantum attack is a “dimensional strike” against the very concept of cryptographic ownership—striking at the finality of asset control itself.
Looking back at cryptographic history—from DES to AES, from SHA-1 to its deprecation—every major cryptographic transition took place under centralized authority (governments, standards bodies) and spanned years or even decades. Bitcoin’s decentralized governance, while granting resilience and anti-censorship strength, may prove too sluggish when rapid, unified action is required to meet a global technological shift.
Conclusion: Navigating Through the Quantum Fog
The sword of Damocles—quantum computing—hangs over Bitcoin. Its fall may not be imminent, but its chilling presence is increasingly palpable. It represents the most profound long-term challenge yet to the world of cryptography, especially to Bitcoin and the broader cryptocurrency space.
The Bitcoin community now faces an unprecedented test: how to uphold its core tenets of decentralization, censorship resistance, and “code is law,” while executing a survival-critical upgrade of its foundational cryptographic layer. This is not just a race against quantum advancement, but a complex systems engineering challenge involving PQC research, standardization, protocol innovation, community consensus, and coordinated global ecosystem migration.
The path forward is uncertain. Will Bitcoin successfully evolve, turning quantum threat into a catalyst for innovation and entering a more secure post-quantum era? Or will it falter under the weight of consensus challenges and migration complexity, fading into obscurity at dawn of the quantum age? History marches on. The answer may lie in the coming years—in every decision made by the Bitcoin community, every line of code committed, and every heated debate held. This is destined to be an unfinished story of innovation, risk, and resilience—and each of us, whether participant or observer, stands at the threshold of this transformative moment.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News