Airdrop Beginner's Guide to Avoiding Scams: Learn How to Identify and Avoid Common Pitfalls to Protect Your Crypto Assets
TechFlow Selected TechFlow Selected
Airdrop Beginner's Guide to Avoiding Scams: Learn How to Identify and Avoid Common Pitfalls to Protect Your Crypto Assets
This guide will analyze common airdrop scams to help you avoid pitfalls.
Author: SlowMist
Translation: TechFlow
Background
In our previous guide on Web3 security, we discussed the topic of multi-signature phishing, explaining how multi-signature wallets work, how attackers exploit them, and how to protect your wallet from malicious signatures. In this edition, we will dive into a marketing strategy widely used in both traditional and crypto industries—airdrops.
Airdrops can rapidly propel a project from obscurity into the spotlight, helping it quickly build a user base and boost market visibility. Typically, users participate in Web3 projects by clicking links and interacting with platforms to claim airdropped tokens. However, hackers set traps throughout the entire airdrop process—from fake websites to backdoored tools. This guide will analyze common airdrop scams to help you avoid these pitfalls.
What Are Airdrops?
An airdrop refers to a Web3 project distributing free tokens to specific wallet addresses to increase visibility and attract early users. It is one of the most direct methods for a project to acquire a user base. Depending on how they are claimed, airdrops generally fall into the following categories:
-
Task-based: Completing tasks specified by the project, such as sharing content or liking posts.
-
Interaction-based: Performing actions like token swaps, sending/receiving tokens, or cross-chain operations.
-
Holding-based: Holding certain designated tokens to qualify for the airdrop.
-
Staking-based: Earning airdrop tokens through single-asset or dual-asset staking, providing liquidity, or long-term locking.
Risks of Claiming Airdrops
Fake Airdrop Scams
These scams can be categorized into several types:
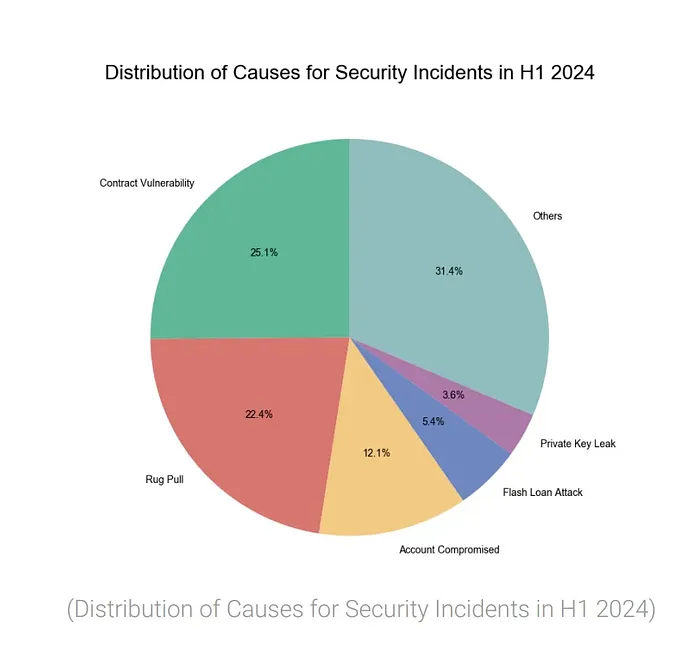
1. Hijacked Official Accounts: Hackers may take control of a project’s official account and post fake airdrop announcements. For example, alerts commonly seen on news platforms state: “Project Y’s X or Discord account has been hacked; do not click on phishing links shared by the hacker.” According to our 2024 mid-year blockchain security and anti-money laundering report, there were only 27 such incidents in the first half of 2024. Users trust official accounts and may click on these links, only to be redirected to phishing sites disguised as legitimate airdrop pages. If they enter their private keys, seed phrases, or grant permissions, hackers can steal their assets.
2. Impersonation in Comments: Hackers often create fake project accounts and post messages in the comment sections of real projects’ social media, claiming to offer airdrops. Unsuspecting users may follow these links and land on phishing websites. For instance, the SlowMist security team has previously analyzed these tactics and provided recommendations in an article titled “Beware of Comment Section Impersonation.” Additionally, right after a legitimate airdrop is announced, hackers quickly post phishing links via fake accounts mimicking official ones. Many users have thus been deceived into installing malicious apps or signing transactions on phishing sites.

3. Social Engineering Attacks: In some cases, scammers infiltrate Web3 project groups and target specific users using social engineering techniques. They may pose as support staff or helpful community members, offering guidance on how to claim airdrops—only to ultimately steal users’ assets. Users should remain vigilant and never trust unsolicited assistance from individuals claiming to be official representatives.
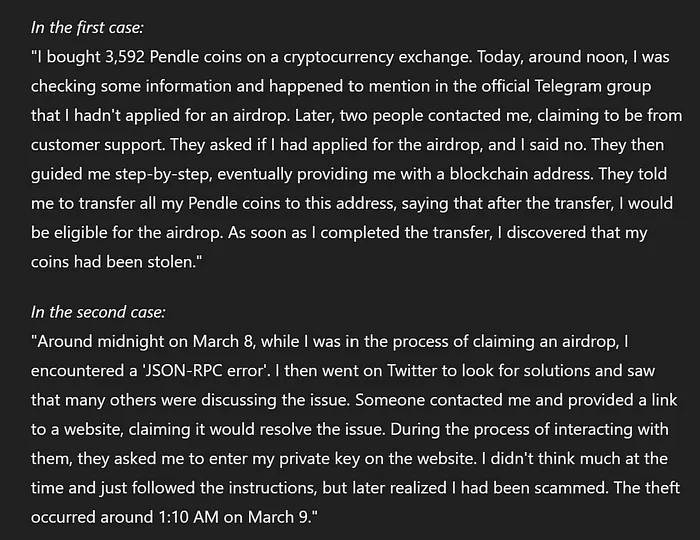
First Case:
-
The user purchased 3,592 Pendle tokens on a cryptocurrency exchange.
-
The user mentioned in the official Telegram group that they hadn’t applied for the airdrop.
-
Two individuals claiming to be customer support contacted the user.
-
They instructed the user to transfer all their Pendle tokens to a specific blockchain address, stating it was required to qualify for the airdrop.
-
After completing the transfer, the user discovered their tokens had been stolen.
Second Case:
-
Around midnight on March 8, the user encountered a "JSON-RPC error" while attempting to claim an airdrop.
-
The user sought solutions on Twitter.
-
Someone reached out and provided a website link, claiming it would resolve the issue.
-
The website requested the user's private key.
-
The user followed the instructions and later realized they had been scammed.
-
The theft occurred around 1:10 a.m. on March 9.
"Free" Airdropped Tokens
While most airdrops require users to complete tasks, sometimes tokens appear in your wallet without any action on your part. Hackers often airdrop worthless tokens into your wallet, hoping you’ll interact with them by transferring, viewing, or attempting to trade them on decentralized exchanges. However, when you try to interact with these scam NFTs, you might encounter an error message prompting you to visit a website to “unlock your items.” This is actually a trap designed to redirect you to a phishing site.

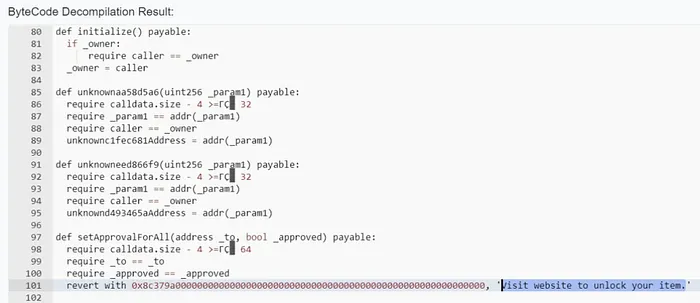
If users access the phishing website linked by the scam NFT, hackers may perform the following actions:
-
Execute "zero-cost purchases" of valuable NFTs (see analysis of "zero-cost purchase" NFT phishing).
-
Steal high-value tokens via approval or permit signatures.
-
Drain native assets.
Next, let’s examine how hackers use carefully crafted malicious contracts to steal users' gas fees.
First, hackers created a malicious contract named GPT on Binance Smart Chain (BSC) (0x513C285CD76884acC377a63DC63A4e83D7D21fb5), then lured users into interacting with it by airdropping tokens.
When users interact with this malicious contract, they are prompted to approve the contract’s access to tokens in their wallet. If the user approves, the malicious contract automatically increases the gas limit based on the user’s wallet balance, resulting in higher gas consumption in subsequent transactions.
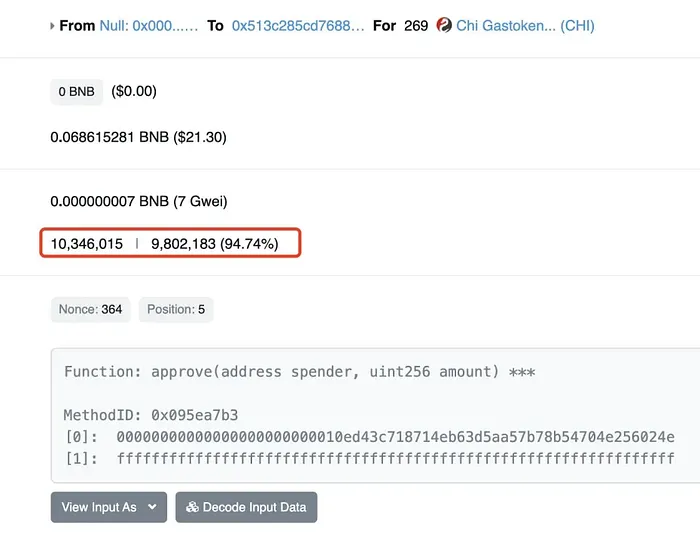
By exploiting the elevated gas limit provided by users, the malicious contract uses excess gas to mint CHI tokens (which can be used for gas compensation). After accumulating a large number of CHI tokens, hackers can burn them during contract destruction to receive gas refunds.
In this way, hackers profit cleverly from users’ gas fees, while users may remain unaware they’ve paid extra. Users who expected to profit from selling airdropped tokens instead lose their native assets.
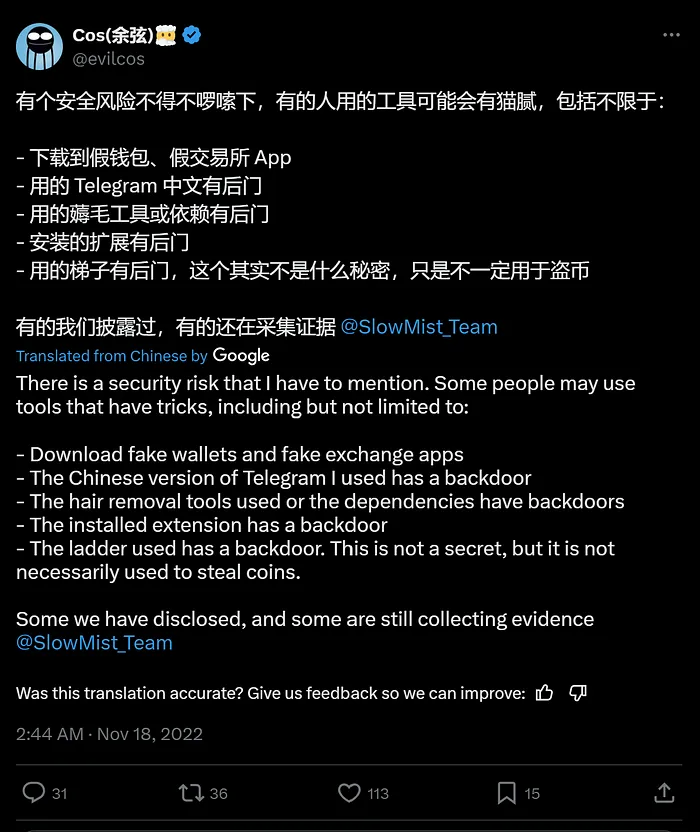
During the airdrop claiming process, some users need to download plugins to complete tasks such as translation or checking token rarity. However, the security of these plugins is questionable. Many users fail to download them from official sources, significantly increasing the risk of downloading backdoored software.
Additionally, we’ve observed online services selling scripts for claiming airdrops, claiming they enable efficient automation of bulk interactions. Be aware that downloading and running unverified scripts is extremely dangerous, as you cannot verify their origin or actual functionality. These scripts may contain malicious code posing potential threats, such as stealing private keys or seed phrases, or performing unauthorized operations like asset transfers. Moreover, some users engaging in these high-risk activities may not have antivirus software installed—or may have disabled it—making it impossible to detect if their device has been compromised by malware, leading to even greater losses.

The victim in the image used a Zengo wallet with 50 individual accounts and 50 native accounts. After 10:22 p.m. on May 9, the victim found their original ETH (Ethereum) missing. Upon confirming the account had been hacked, all funds across every account had already been drained.
The likely cause was the unknowing download of a trojan program. The victim had disabled antivirus software and firewall due to compatibility issues. A later antivirus scan revealed 21 trojans installed on the computer.
Conclusion
In this guide, we’ve highlighted various risks associated with claiming airdrops by analyzing common scam tactics. While airdrops are a popular marketing strategy, users can reduce the risk of asset loss during this process by taking the following precautions.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News