After the Ethereum merge, DVT (Distributed Validator Technology) is crucial
TechFlow Selected TechFlow Selected
After the Ethereum merge, DVT (Distributed Validator Technology) is crucial
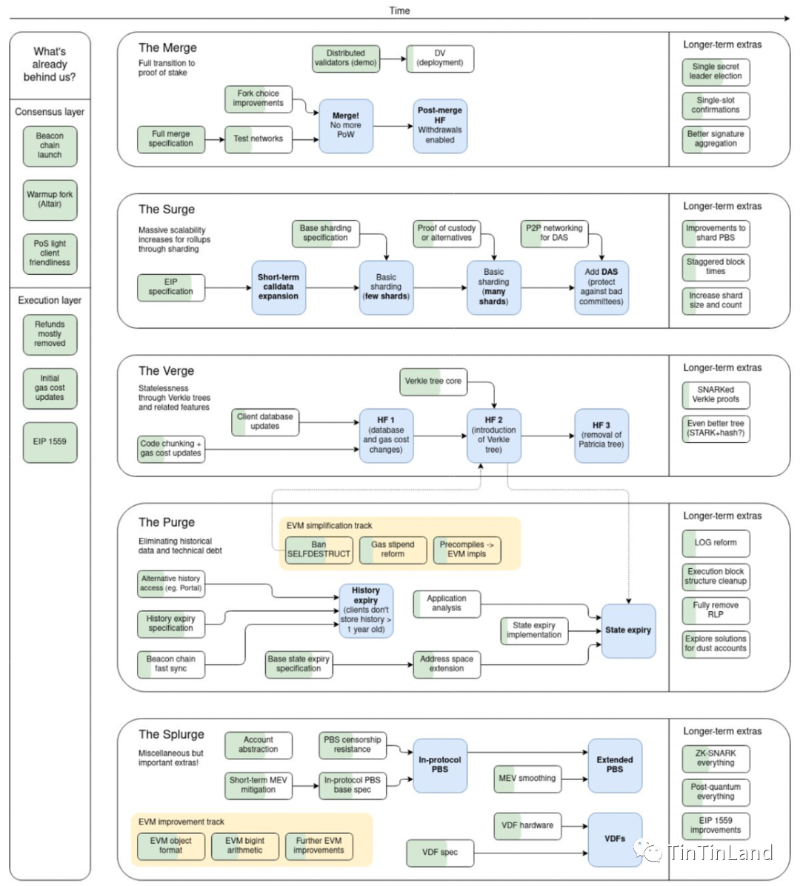
The Ethereum roadmap indicates that Distributed Validator Technology (DVT) will be the next key step after the Merge. According to Messari's latest report, DVT can enhance validator security and may become one of the major developments for the Ethereum network.
On September 15, 2022, the Ethereum blockchain completed its most significant upgrade in seven years—The Merge, transitioning from Proof-of-Work (PoW) to Proof-of-Stake (PoS) consensus. While this shift reduces energy consumption and lowers entry barriers, concerns remain about increased network centralization under PoS, as larger stakeholders gain disproportionately greater voting power. Therefore, after The Merge, developers must participate in development and testing to minimize potential network failures, enhance decentralization, and expand the network.
Ethereum's roadmap indicates that Distributed Validator Technology (DVT) will be the next critical step following The Merge. According to a recent report by Messari, DVT can improve validator security and may become one of the major developments for the Ethereum network.
What is DVT?
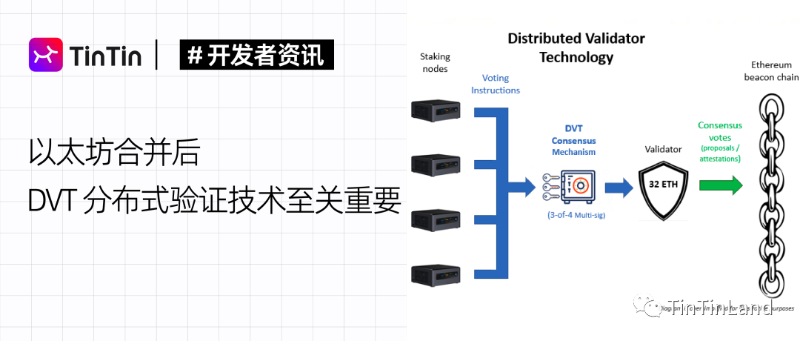
Distributed Validator Technology (DVT) functions similarly to multi-signature consensus voting, enabling Ethereum PoS validators to operate across multiple nodes or machines. This allows validators to cast votes from distributed locations—the core purpose being to support Ethereum’s decentralized validation operations. First introduced in research papers by members of the Ethereum Foundation, DVT was originally referred to as SSV. Using a 3-out-of-4 setup (explained below), DVT enables individuals, groups, or communities to jointly form a single validator. By adding a fault-tolerant layer for validators, DVT improves resilience—ensuring that even if one node fails, the validator continues operating, thereby eliminating single points of failure, slashing penalties for double-signing, and fork-related penalties.
Related Concepts
Consensus: A single validator’s responsibilities are distributed among multiple co-validators; message signing requires agreement among them.
M-of-N Threshold Signatures: A validator’s private key is split into N shares, with each participant holding 1/N. Signing is completed when M participants agree and sign.
How It Works
DVT consists of four key components: Distributed Key Generation (DKG), Shamir's Secret Sharing for BLS signatures, Secure Multi-Party Computation (MPC), and the DVT Byzantine Fault Tolerance (BFT) consensus layer.
Distributed Key Generation (DKG): Encrypts and distributes the private key among all participants, preventing any single party from fully controlling it.
Shamir's Secret Sharing: The private key is divided and distributed among participants. To reconstruct the key, a predefined threshold of shares (e.g., 3 out of 4) must be combined.
Multi-Party Computation (MPC): MPC is the most crucial component in DVT. Through scalable computation, operators use their key shares to sign messages and perform operations without ever reconstructing the full private key on a single device. MPC enables secure coordination of key generation and reconstruction across distributed machines.
Consensus: Fault tolerance is achieved via a threshold signature scheme and consensus algorithms between Beacon nodes. Once an ETH validator connects to the Beacon node, consensus is established.
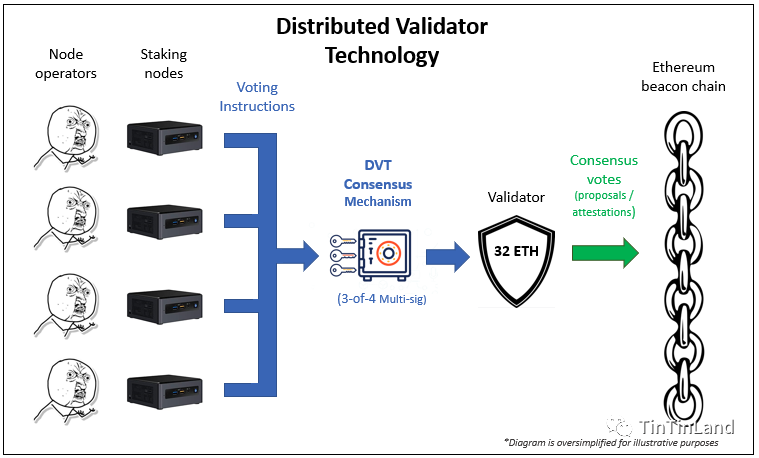
As shown in the figure above, DVT operators first compute the process of generating shared public and private encryption keys. Then, the split private key is shared among different participants, while key fragments are distributed to operators. Next, operators use multi-party computation to randomly select validation nodes (which share information with other nodes). Participating validators reach consensus once they pass the predefined threshold authentication.
Why Do We Need DVT?
DVT addresses many challenges emerging post-Merge, with centralization being the primary threat. Additionally, protocol rules leading to validator asset loss and reduced stability of the Ethereum ecosystem are urgent issues requiring resolution.
Centralization Risks
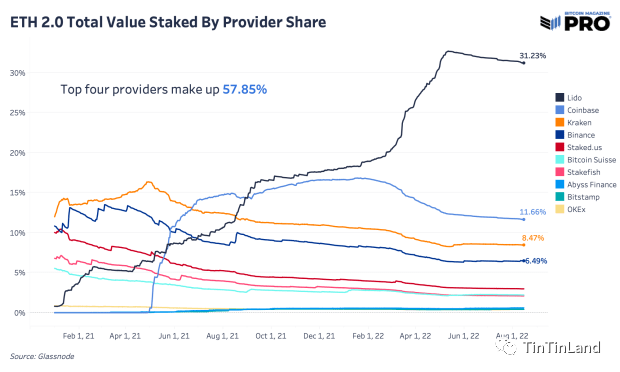
Ethereum rules restrict users holding less than 32 ETH from running validators. For these users, staking services are the only option, leading to large amounts of crypto assets being held in centralized exchanges. Lido Finance, Ethereum’s largest staking provider, holds over 4 million ETH—accounting for 32% of total staked assets. When vast quantities of assets are concentrated in exchanges, risks such as hacking, unreasonable censorship, and technical errors threaten Ethereum’s ecosystem, increasing centralization risk.
 Image
Image
Single Point of Failure
Private keys are critical for independent validators—losing or forgetting them means losing access to assets. Post-Merge, PoS protocol rules prohibit redundancy, allowing each validator to sign through only one machine. This means that if a node goes down or suffers a cyberattack, a single-node validator without failover protection risks direct asset loss and negatively impacts overall Ethereum stability.
Double-Signing Penalties
If a validator signs multiple times using the same key due to network or cloud outages, users may lose part of their staked funds.
Fork Penalties
Under PoS, if a validator’s connected Beacon node fails and creates a fork, the validator may be deemed offline and still face penalties despite the external issue.
Centralization contradicts the fundamental principles of blockchain, while security threats and financial penalties create negative consequences. To address these challenges, Distributed Validator Technology has emerged.
What Is the Potential of DVT?
With the potential to enhance Ethereum’s decentralization, security, and operational efficiency, DVT is highly anticipated by industry experts.
Advantages
DVT-run validators operate as resilient node clusters, reducing risk and improving staking stability.
For large validators, DVT ensures high availability and reduces infrastructure costs: Improved redundancy and lower slashing risks allow fewer validators to manage more nodes, lowering hardware expenses. By enabling clients and addresses to run across multiple nodes, DVT reduces the risk of failure at any single address or client.
For small validators, DVT offers protection levels comparable to larger validators: Small validators achieve efficiency on par with larger ones. By reducing the ETH requirement for running nodes, DVT enables users to validate via community staking pools or home-based setups.
For liquid staking protocols, DVT increases efficiency, reduces risk, and enables operator participation: By providing redundancy across the network, DVT eliminates reliance on any single operator that could cause downtime. Operators can organize into different clusters, enhancing the performance of staking protocols.
Use Cases
In Decentralized Staking Pools: With DVT, staking pools can transition to decentralized models, reducing penalties and slashing by minimizing downtime.
Staking Infrastructure Providers: DVT enables infrastructure providers to implement active-active cluster redundancy, achieving dynamic deployment and configuration. Previously, providers needed redundant solutions for active-passive institutional setups. Now, active-active redundancy ensures continuous operation by distributing validators across multiple machines to build fault tolerance.
Setting Up Independent Validators: With DVT, validators can distribute signing rights across multiple nodes in an active-active redundant setup, minimizing risks of signature failure and penalties due to downtime or double-signing.
Related Projects
Since the introduction of DVT, both Obol Network and SSV Network have developed projects based on this technology.
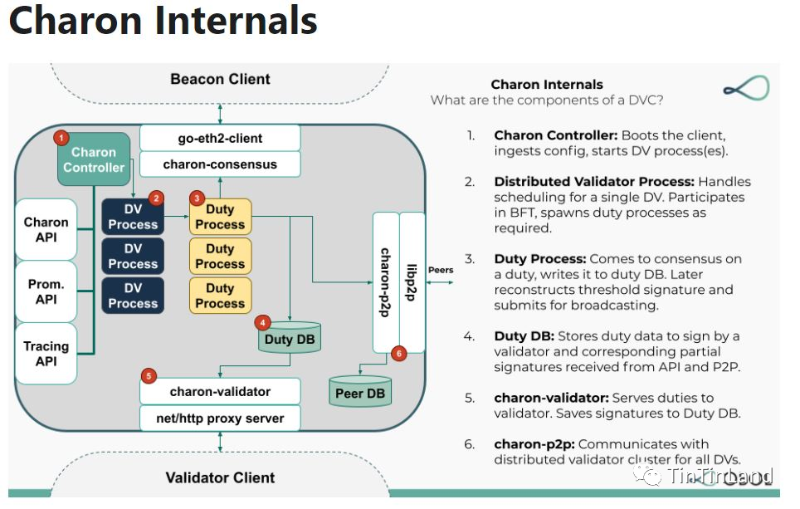
1. Obol Network
Obol Network launched Charon, a plugin client that enables DVT, allowing validators to operate in a fault-tolerant, distributed manner. By refining DVT, Obol introduces active-active redundancy to overcome limitations of traditional active-passive systems. Instead of running on a single machine, validators operate across multiple machines to achieve fault tolerance and withstand partial node failures. Multiple Charon clients communicate and reach consensus, acting together as a unified validator. During this process, Charon supports any client with HTTP API compatible with the beacon chain standard and maintains existing remote signing infrastructure, offering validators an easier adoption path.
Looking ahead, Obol Labs will continue focusing on DVT, advancing its applications in applied cryptography and cryptoeconomics.
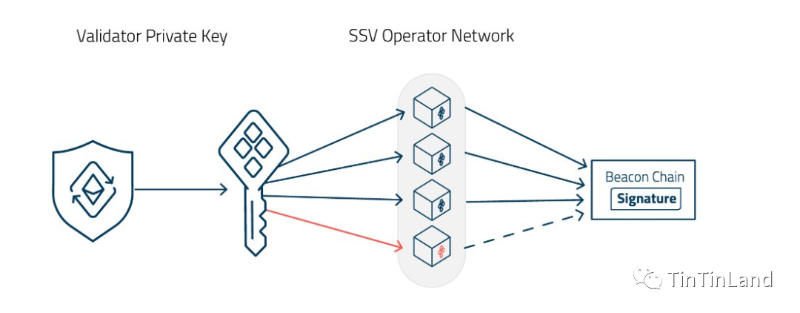
2. SSV Network
SSV Network has released a decentralized staking infrastructure layer. In its model, each validator selects four nodes from the operator network to perform multi-signature voting. SSV Network comprises two layers: the SSV peer-to-peer (P2P) network layer and the Ethereum smart contract layer for governance. The former reads operator lists and validator stake allocations from smart contracts to manage validators; the latter adds operators, assigns assets, and evaluates them based on DVT operator rankings.
Currently, SSV Network has funded multiple projects applying DVT and will continue building foundational blocks for applications using decentralized Ethereum staking infrastructure.
Conclusion
For users, DVT resolves many staking challenges and lowers entry barriers. For developers, DVT also offers substantial benefits. With DVT, institutions or individual validators enjoy enhanced protocol security and flexibility, benefiting from active-active redundant configurations and diversified operations. In the near future, DVT is expected to empower staking, enabling complementary validator node setups and collaborative operations—paving the way toward a truly decentralized Ethereum.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News