TechFlow News: On May 5, according to CoinDesk, Ripple announced on Monday that it will share its internal intelligence on North Korean hackers with Crypto ISAC—the cryptocurrency industry’s threat intelligence-sharing organization—to help businesses identify coordinated intrusion campaigns.
This move follows a recent shift in attack patterns targeting the cryptocurrency industry. The April theft of $285 million from the Drift protocol was not a conventional smart-contract vulnerability exploit; rather, North Korean hackers spent months building relationships with Drift contributors and installing malware on their devices before stealing private keys. Ripple stated: “The strongest crypto security posture is a shared one. A threat actor rejected by one company after background screening may submit job applications to three other companies within the same week. Without shared intelligence, every company starts from scratch.”
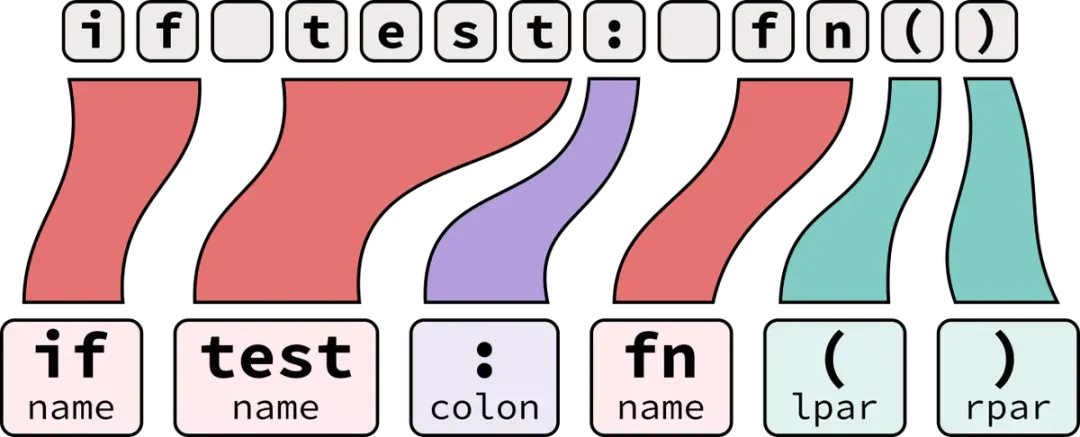
Ripple will provide Crypto ISAC with data including LinkedIn profiles, email addresses, locations, and phone numbers—enabling security teams across companies to recognize repeated attempts by the same actor. Between 2022 and 2024, DeFi attacks primarily targeted code vulnerabilities; however, as technical security has improved, attacker tactics have shifted from exploiting code to human infiltration—hackers now apply for jobs at crypto firms, pass background checks, attend video conferences, and build trust, thereby executing attacks that evade detection by traditional security tools.
The Lazarus Group’s influence is beginning to reshape legal procedures. On Monday, an attorney representing victims of North Korean terrorism served a restraining notice upon the Arbitrum DAO, arguing that the 30,765 ETH frozen due to the April Kelp cross-chain bridge vulnerability should be classified as North Korean assets under U.S. law enforcement statutes. Aave has filed an objection to this filing, stating, “Thieves do not acquire lawful ownership of property through theft.” Combined losses from the Drift and Kelp incidents exceed $500 million, and both have been publicly attributed to the Lazarus Group.