Lazarus Targets macOS: A Fake Zoom Link Attempts to Drain Crypto Executives’ Funds
TechFlow Selected TechFlow Selected

Lazarus Targets macOS: A Fake Zoom Link Attempts to Drain Crypto Executives’ Funds
Lazarus was the mastermind behind the $1.4 billion Bybit hack in 2025.
Author: Zoltan Vardai
Compiled by: TechFlow
TechFlow Intro: Security researchers have discovered that the North Korean hacker group Lazarus is deploying a new macOS malware toolkit dubbed “Mach-O Man” to target executives at cryptocurrency firms and traditional financial institutions. The attackers lure victims via fake Zoom and Google Meet meeting links. Once victims execute the provided command, the malware silently runs in the background to steal sensitive data—including browser credentials and Keychain passwords—and exfiltrates it via Telegram. Lazarus was also behind the $1.4 billion Bybit heist in 2025.
Security researchers have linked a newly identified macOS malware campaign to the Lazarus Group—a North Korea–affiliated hacking organization responsible for several of the largest cryptocurrency thefts on record.
Mauro Eldritch, founder of threat intelligence firm BCA Ltd. and an offensive security expert, disclosed this new malware toolkit—named “Mach-O Man”—on Tuesday. It spreads via ClickFix social engineering, targeting both traditional enterprises and cryptocurrency companies.
Attack Flow: Fake Zoom Meeting → Background Malware Installation
The attack works as follows: Victims are lured into joining a spoofed Zoom or Google Meet video call. A webpage then prompts them to execute a command. Once executed, the malware downloads and installs silently in the background—bypassing conventional security controls and triggering no alerts—ultimately granting attackers access to user credentials and corporate system privileges.
In his report published Tuesday (link), Eldritch warned that this campaign could lead to account takeovers, unauthorized infrastructure access, financial losses, and critical data breaches. Lazarus’s targeting scope has now expanded beyond crypto-native companies.
The Lazarus Group is the prime suspect behind multiple historic cryptocurrency heists—including the $1.4 billion breach of the Bybit exchange in 2025, which remains the largest single theft in industry history.
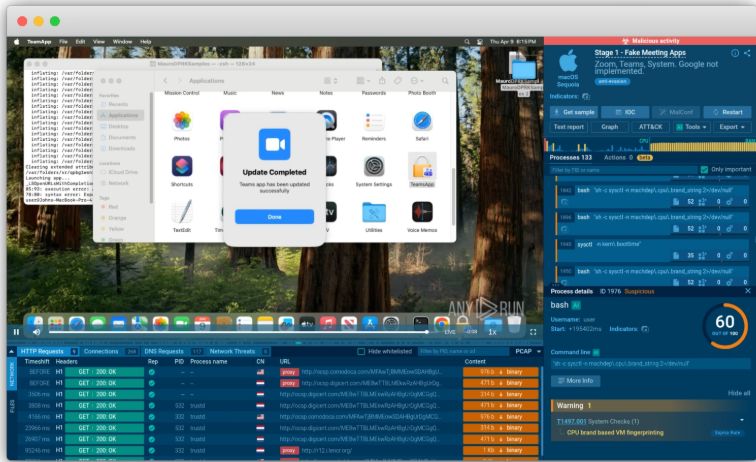
Caption: Spoofed Mach-O Man toolkit application interface
Source: ANY.RUN
End Goal: Stealing Everything from Browsers and Keychain
The final stage of the attack chain is a credential stealer designed specifically to extract browser extension data, saved browser credentials, cookies, macOS Keychain entries, and other sensitive information.
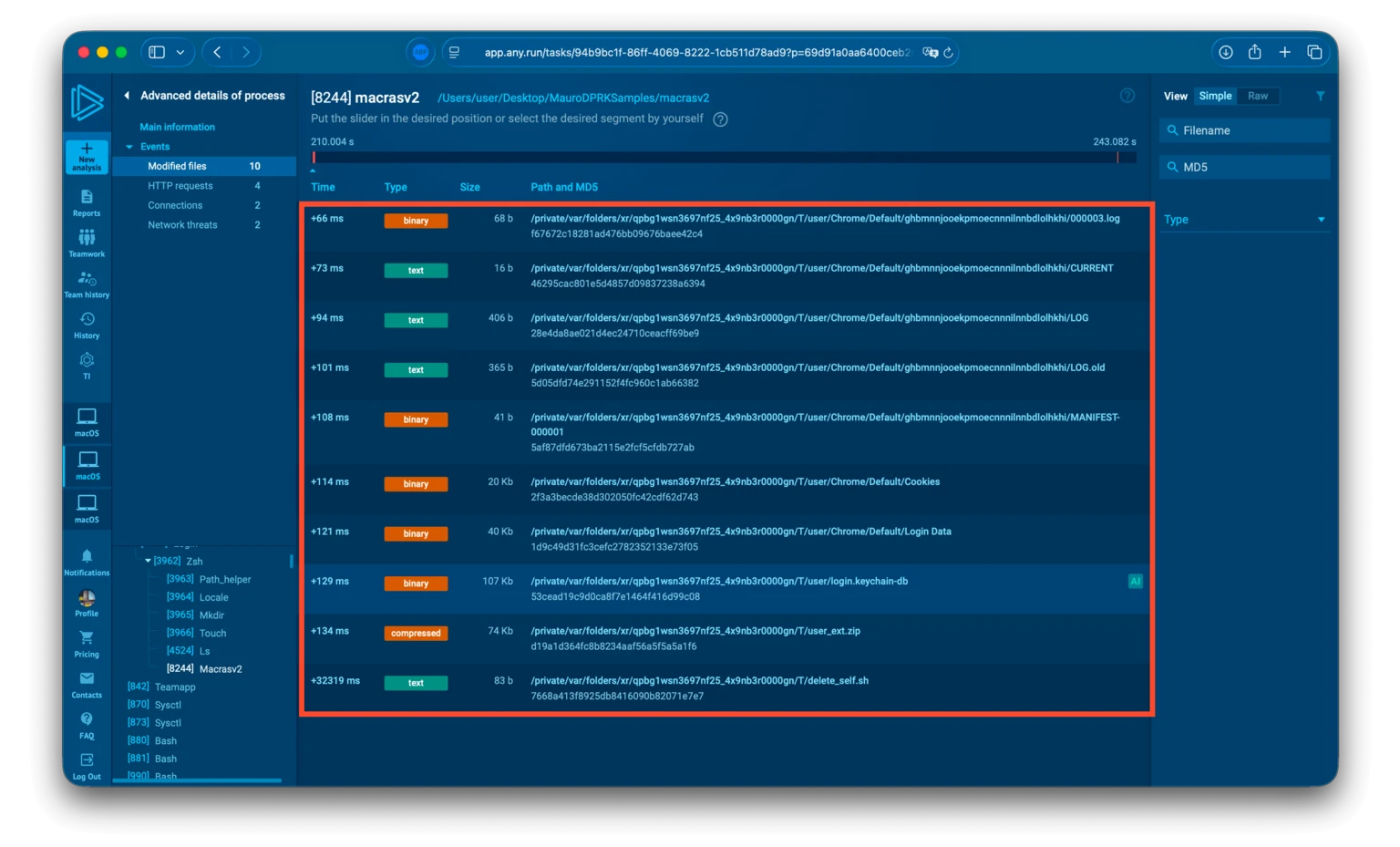
Caption: Final deployed directory structure of the stealer
Source: ANY.RUN
After collecting the data, the malware packages everything into a ZIP archive and sends it to the attackers via Telegram. Finally, a self-destruct script deletes the entire toolkit using the system’s rm command—bypassing user confirmation and permission checks to force-delete files without leaving traces.
This novel malware toolkit was reconstructed and analyzed by security experts using ANY.RUN’s cloud-based macOS malware sandbox capabilities.
North Korean Hackers’ Attack Surface Continues to Expand
Earlier this April, North Korean hackers used AI-powered social engineering to steal approximately $100,000 from the crypto wallet Zerion, gaining access to logged-in sessions, credentials, and corporate private keys belonging to some team members.
Additionally, CZ recently issued a warning after his security team “SEAL” identified 60 North Korea–linked individuals posing as IT professionals who had infiltrated cryptocurrency firms.
North Korea’s infiltration of the cryptocurrency industry extends far beyond simple “hacking.” From impersonating employees to AI-driven social engineering and custom-built malware, the attack surface continues to widen. macOS users have long been considered relatively secure—but clearly, Lazarus disagrees.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News