Exposing a New Scam: Stealing Assets by Maliciously Modifying RPC Node URLs
TechFlow Selected TechFlow Selected
Exposing a New Scam: Stealing Assets by Maliciously Modifying RPC Node URLs
A new type of cryptocurrency scam has recently emerged, primarily targeting offline physical transactions. This scam uses USDT as the payment method and carries out fraudulent activities by modifying the Remote Procedure Call (RPC) of Ethereum nodes.
Author: Lisa
Background
According to feedback from partner imToken, a new type of cryptocurrency scam has recently emerged. This scam typically occurs in offline physical transactions, using USDT as the payment method and exploiting modified Ethereum node Remote Procedure Call (RPC) settings to carry out fraudulent activities.
Attack Process
The SlowMist security team has analyzed this type of scam. The attacker's specific process is as follows:
First, the scammer诱导s the victim to download the legitimate imToken wallet, offering 1 USDT and a small amount of ETH as bait to gain trust. Then, the scammer guides the user to redirect their ETH RPC URL to the scammer’s own node (https://rpc.tenderly.co/fork/34ce4192-e929-4e48-a02b-d96180f9f748).
This node has actually been manipulated by the scammer using Tenderly’s Fork feature, falsifying the user’s USDT balance to make it appear as if funds have been deposited into their wallet. As a result, users see what appears to be a successful transaction and believe the funds have arrived. However, when they attempt to pay gas fees to transfer or cash out the USDT, they realize they’ve been scammed—by which time the scammer has already disappeared.

In fact, beyond just faking balances, Tenderly’s Fork function can also alter contract information, posing an even greater threat to users.
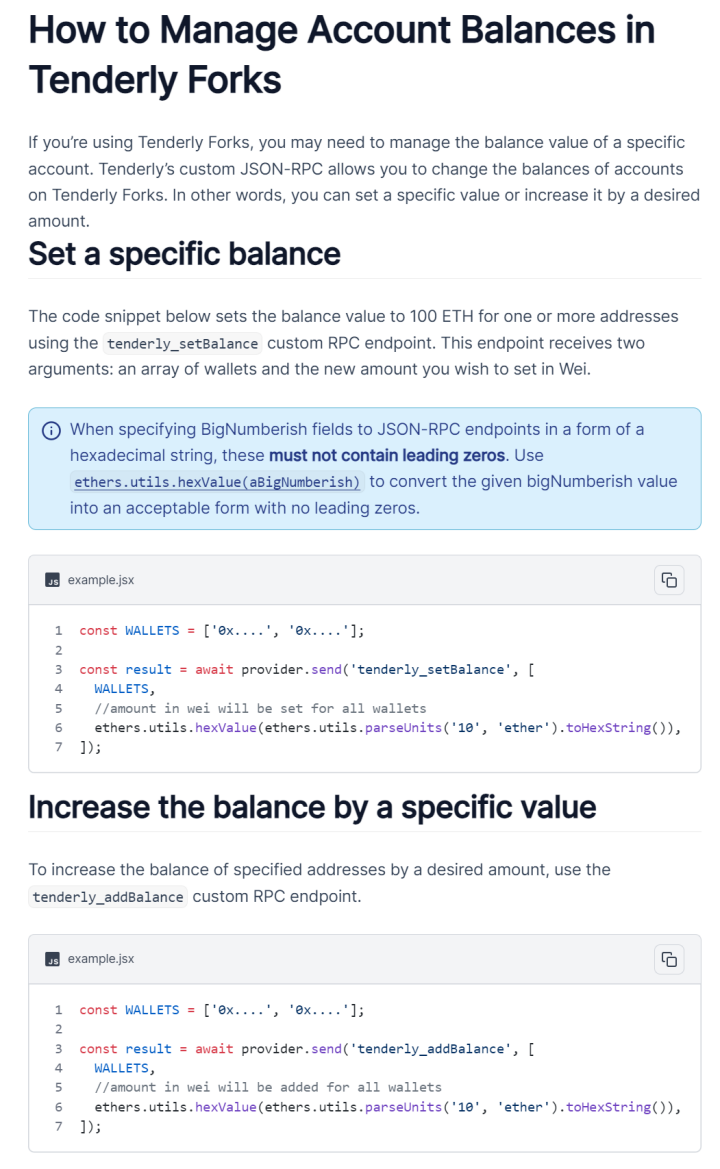
(https://docs.tenderly.co/forks)
This raises an important question—what exactly is an RPC? To interact with a blockchain, we need a standardized way to access network servers, and RPC serves as that communication method, enabling us to query balances, create transactions, or interact with smart contracts. By embedding RPC functionality, wallets allow users to send requests and communicate with the blockchain. For example, when a user connects a wallet like imToken to a decentralized exchange, they are essentially communicating with blockchain servers via RPC. Normally, all types of wallets are set by default to connect to secure nodes, requiring no manual adjustments. However, if users blindly trust others and link their wallets to untrusted nodes, the displayed balance and transaction data may be maliciously altered, potentially leading to financial loss.
MistTrack Analysis
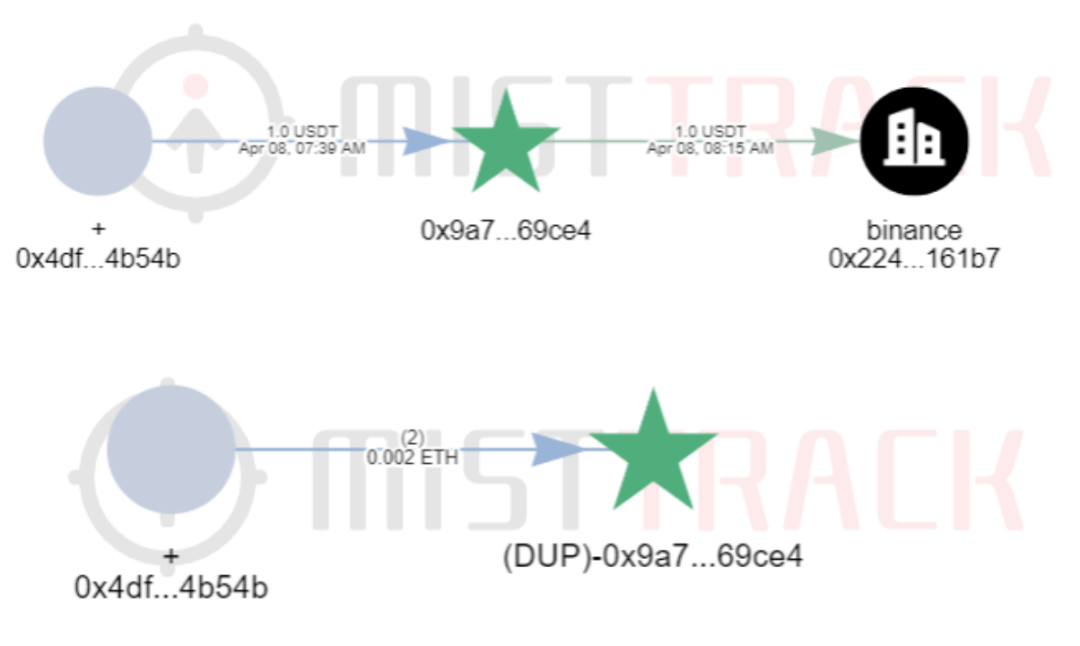
Using the on-chain tracking tool MistTrack, we analyzed one known victim wallet address (0x9a7…Ce4). It shows that the victim received a small amount of 1 USDT and 0.002 ETH from address (0x4df…54b).
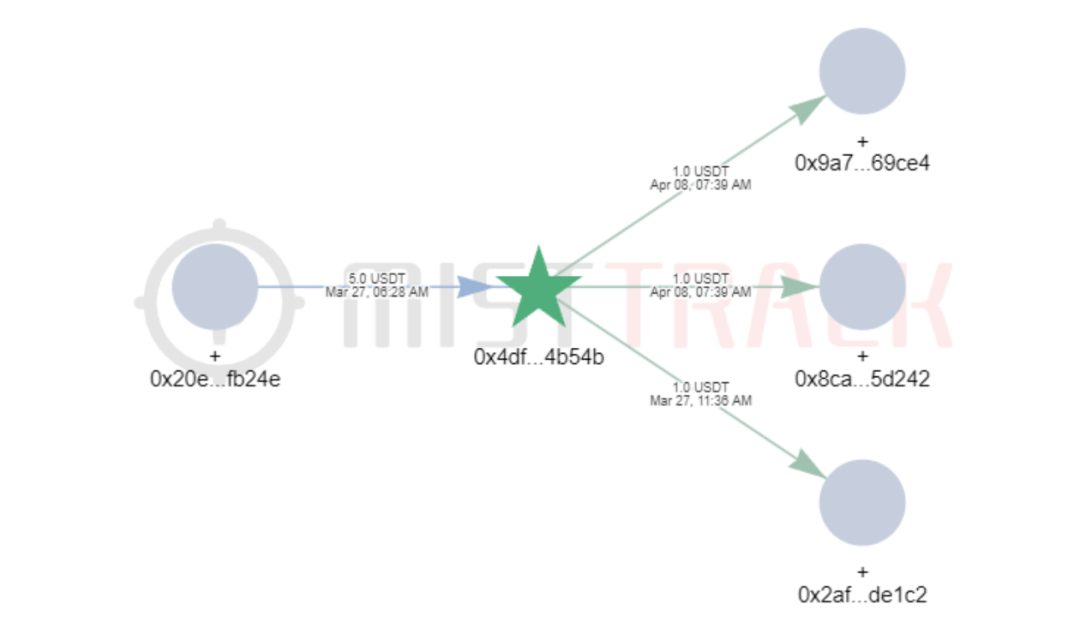
Examining the funding flow of address (0x4df…54b), we found it transferred 1 USDT to three different addresses—indicating this address has carried out such scams at least three times.
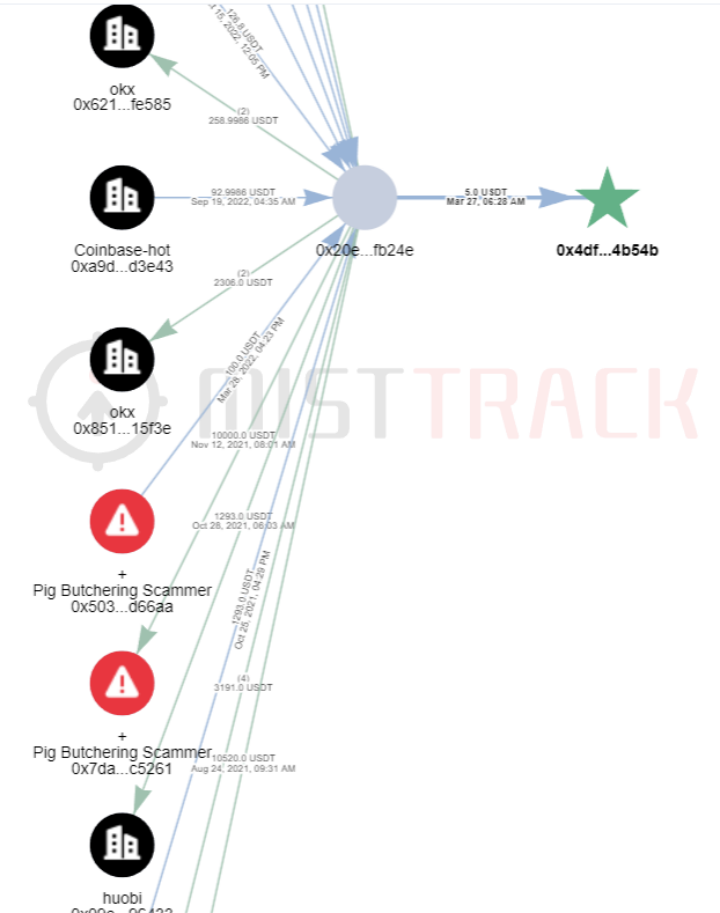
Tracing further upstream, the address is linked to multiple exchanges and has interacted with addresses flagged by MistTrack as "Pig Butchering Scammer".
Summary
The cunning nature of this scam lies in exploiting psychological vulnerabilities. Users often focus solely on whether funds appear in their wallet, overlooking potential risks behind the scenes. Scammers take advantage of this trust and negligence, using seemingly legitimate actions—such as sending small amounts of funds—to deceive victims. Therefore, the SlowMist security team advises all users to remain vigilant during transactions, enhance self-protection awareness, avoid blindly trusting others, and prevent financial losses.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News