The Use of Humans: Agentic Wallets and the Next Decade of Wallets
TechFlow Selected TechFlow Selected
The Use of Humans: Agentic Wallets and the Next Decade of Wallets
In 1984, Apple killed the command line with a mouse. In 2026, Agents are killing the mouse.
By Lacie Zhang, Researcher at Bitget Wallet

In 1984, Apple (Macintosh) killed the command line with a mouse. In 2026, Agents are killing the mouse.
This is not a metaphor. Companies like Google, Amazon, NVIDIA, Visa, Microsoft, and Alibaba—each having spent billions refining graphical user interfaces—are now deliberately bypassing GUIs in favor of CLI, API, and Agent-native interfaces. The logic is simple: human-driven growth fuels the 0-to-1 phase, but the next tenfold user base won’t be looking at screens.
Yet everyone avoids confronting one question: when software users shift from humans to Agents, do humans still need to be present?
As early as 1950, Norbert Wiener—the founder of cybernetics—issued a warning: once humans lose the ability to observe and intervene, feedback loops break down and systems spiral out of control. Today’s OpenAI emphasis on “Harness Engineering” is essentially a continuation of this idea.
Over seventy years later, Agentic Wallets confront the crypto version of this problem. Confirmation pop-ups, signature requests, approval workflows, mnemonic backups, multi-factor verification—cryptocurrency wallets spent a decade building security mechanisms to answer one question: “Is this transaction truly authorized by you?” Agents render this human-centric interaction model obsolete: requiring manual confirmation for every action prevents Agents from executing continuously, in real time, and autonomously; granting Agents unrestricted private-key control exposes humans to unacceptable risk.
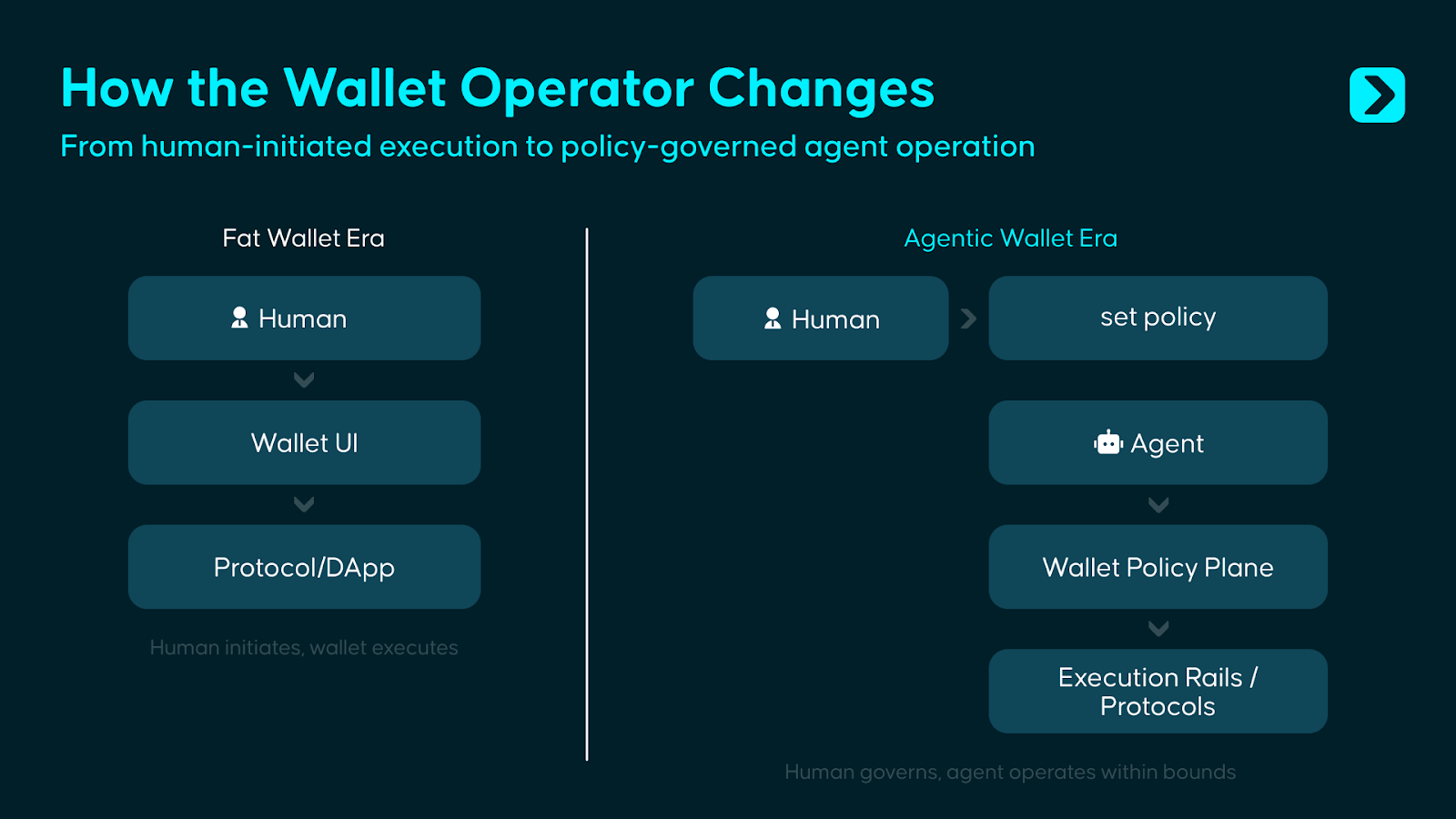
The answer lies neither at one extreme nor the other. Full autonomy is the sexiest narrative of the Agent era—but Wiener’s warning remains valid. We believe an Agentic Wallet must serve two distinct principals simultaneously: first, empowering humans with rule-setting, risk-control, and governance-intervention capabilities; second, granting Agents constrained execution permissions, enabling them to autonomously perform on-chain operations within clearly defined boundaries. In other words, the wallet must evolve from a human-used asset container and signing tool into a permission-and-execution system where humans define boundaries and Agents operate strictly within them.
What should such a system look like? That is precisely what this article aims to answer.
I. Beyond the Fat Wallet: Another Wallet War
In its Fat Wallet Thesis, Delphi Digital made a compelling argument: as protocols and application layers grow increasingly commoditized, value will accrue to the wallet layer—because wallets sit closest to users, control distribution channels and order flow, and benefit from interface familiarity, accumulated assets, and migration friction that lock users into a particular wallet long-term.
But Agents don’t follow this logic. As “dispassionate” machine executors, Agents won’t stay loyal to any single wallet due to interface familiarity, brand preference, or usage habits. Instead, they’ll continuously seek the infrastructure combination offering lowest cost, minimal latency, and highest execution reliability. As standards like ERC-8004 gain adoption, Agent identity and reputation layers may also become portable across systems—meaning wallets’ lock-in effect on Agents is inherently weaker than their lock-in effect on humans.
This doesn’t mean wallet value disappears—it simply shifts location. In simple personal-use scenarios, Agents erode wallets’ existing moats built on UI, habit, and entry-point advantage; yet in more complex organizational deployment scenarios, once enterprises configure policy rules, approval workflows, risk parameters, and audit frameworks across entire “Agent fleets,” migration costs no longer stem from frontend experience—but from rebuilding the entire permissions, governance, and operational configuration stack.
Thus, the Agentic Wallet answers a different proposition beyond the Fat Wallet: While the Fat Wallet competes for user entry points, the Agentic Wallet competes for control over funds the moment software begins directly managing them.
Looking back at wallet evolution reveals that each product-form shift corresponds fundamentally to a change in the object of user trust:
- Mnemonic wallets require users to trust themselves.
- Smart contract wallets require users to trust code.
- Embedded wallets require users to trust service providers.
- And with Agentic Wallets, users must trust a control system composed jointly of permissions, policies, and governance mechanisms.
This system’s goal isn’t to let software take over fund management—but to let software act under limited authorization while preserving ultimate human control. Hence, the core of an Agentic Wallet isn’t merely “enabling Agents to use wallets,” but rather “enabling Agents to manage funds belonging to human users under conditions that are constraining, auditable, and intervenable.”
II. The Wallet’s Boundary Is the Agent’s Starting Line
Existing wallets continue functioning well within their originally designed contexts—but the issue is that an increasing number of Agent-driven use cases are pushing beyond those design boundaries.
Scenario 1: Trading Agents Need Speed—but “Capability to Execute” ≠ “Permission to Execute”
An investment portfolio Agent monitors cross-chain liquidity around the clock. When an opportunity arises, it must execute trades within seconds. Traditional wallet control logic requires users to open the app → review the transaction → tap confirm. By the time this workflow completes, the opportunity window has often already closed.
Technically, Agents already possess the capability to invoke swap functions, generate calldata, and bridge funds. The problem is that capability does not equal permission. An Agent’s ability to initiate a transaction does not imply it should be freely allowed to control funds.
The role of an Agentic Wallet is precisely to separate these two: Agents can act instantly—but only within preconfigured rules, e.g., restricted to approved assets, subject to daily budget caps, bounded by slippage limits, and automatically paused under abnormal market conditions. Skills define *what* an Agent *can do*, whereas the wallet enforces *what* it *is permitted to do*.
Scenario 2: Payment Agents Need to Spend—but Should Not Hold Full Fund Control
A payment Agent automatically settles API bills, SaaS subscriptions, and vendor payments. Within current wallet architectures, it typically faces only two options: wait for manual approval on every payment—or hold a private key with unlimited signing authority. The former doesn’t scale; the latter poses excessive risk.
An Agentic Wallet offers constrained authorization: it can pay only whitelisted merchants, use only designated assets, execute payments only within daily budget limits, and fully log all expenditures.
Scenario 3: Multiple Agents Need Shared Budgets with Mutually Isolated Permissions
A single entity may run multiple Agents simultaneously: one for trading, one for payments, one for auditing. While existing wallets can create multiple sub-accounts, unified permission orchestration across those accounts—including global budget caps, cross-Agent policy constraints, and consolidated audit trails—is not a native capability of today’s wallets.
In contrast, the Agentic Wallet model treats this as a first-class design concern: each Agent receives its own independent, narrowly scoped permissions; meanwhile, a unified policy layer governs overall risk exposure, cross-Agent rate limits, shared budgets, and generates consistent audit records.
These scenarios point to one conclusion: private-key management remains the bedrock of wallet security—and letting Agents directly access private keys is an unacceptable risk source in any scenario. Yet securing private keys alone is no longer sufficient. When the actor shifts from human to Agent, wallets must answer a second question: Who is permitted to act, under what conditions, at what amounts, on which assets, and toward which counterparties? Private-key management is the first line of defense; managing permission boundaries for non-human actors is the new second firewall of the Agent era.
III. Bounded Autonomy: The Design Philosophy of Agentic Wallets
The industry remains in early exploration of Agentic Wallets, with no truly mature solutions yet available. However, as noted earlier, this article defines an Agentic Wallet as a funds-control system bridging human governance and Agent execution: humans set boundaries, Agents act within them, and the wallet ensures this constraint relationship remains enforceable, auditable, and intervenable.
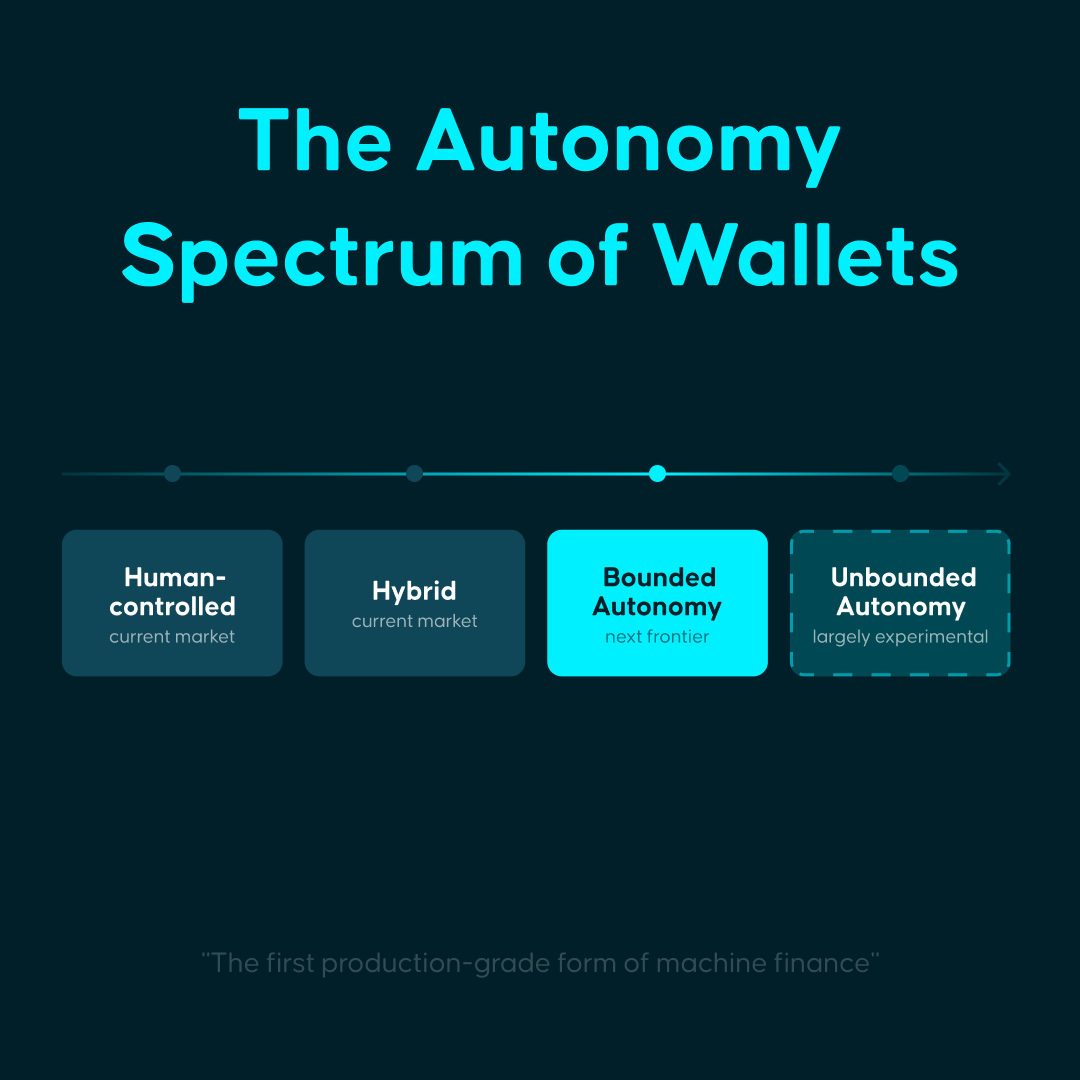
Moreover, depending on the degree of authorization granted to Agents, Agentic Wallets may serve four distinct modes:
- Human-Controlled: Agents provide suggestions and assistance, but each operation still requires human confirmation. This improves interaction efficiency without changing the underlying fund-control logic.
- Hybrid: Agents handle routine tasks—such as data retrieval, quoting, alerts, or low-risk execution—while humans intervene less frequently. However, edge cases—like fund transfers, contract calls, or exception branches—still require human approval.
- Bounded-Autonomy: Agents act autonomously within clearly defined rules, limits, and override pathways. Humans transition from per-transaction approvers to rule-setters. This article focuses primarily on this mode.
- Fully Autonomous: Agents possess near-complete economic sovereignty, independently allocating funds and bearing consequences without predefined boundaries. While theoretically possible, this model remains immature across safety, governance, accountability, and compliance—and currently exists mostly in experimental stages.
For reference, Stripe’s 2025 Annual Letter classifies agentic commerce into five levels: L1 eliminates web forms; L2 enables descriptive search; L3 introduces persistent memory; L4 implements delegation; L5 achieves anticipatory purchasing. It explicitly states the industry as a whole still “hovers at the boundary between L1 and L2.”
From this perspective, current market demand likely centers on Human-Controlled and Hybrid scenarios, while Bounded Autonomy represents the true frontier today—and the first production-grade form in which Agents genuinely begin managing funds.
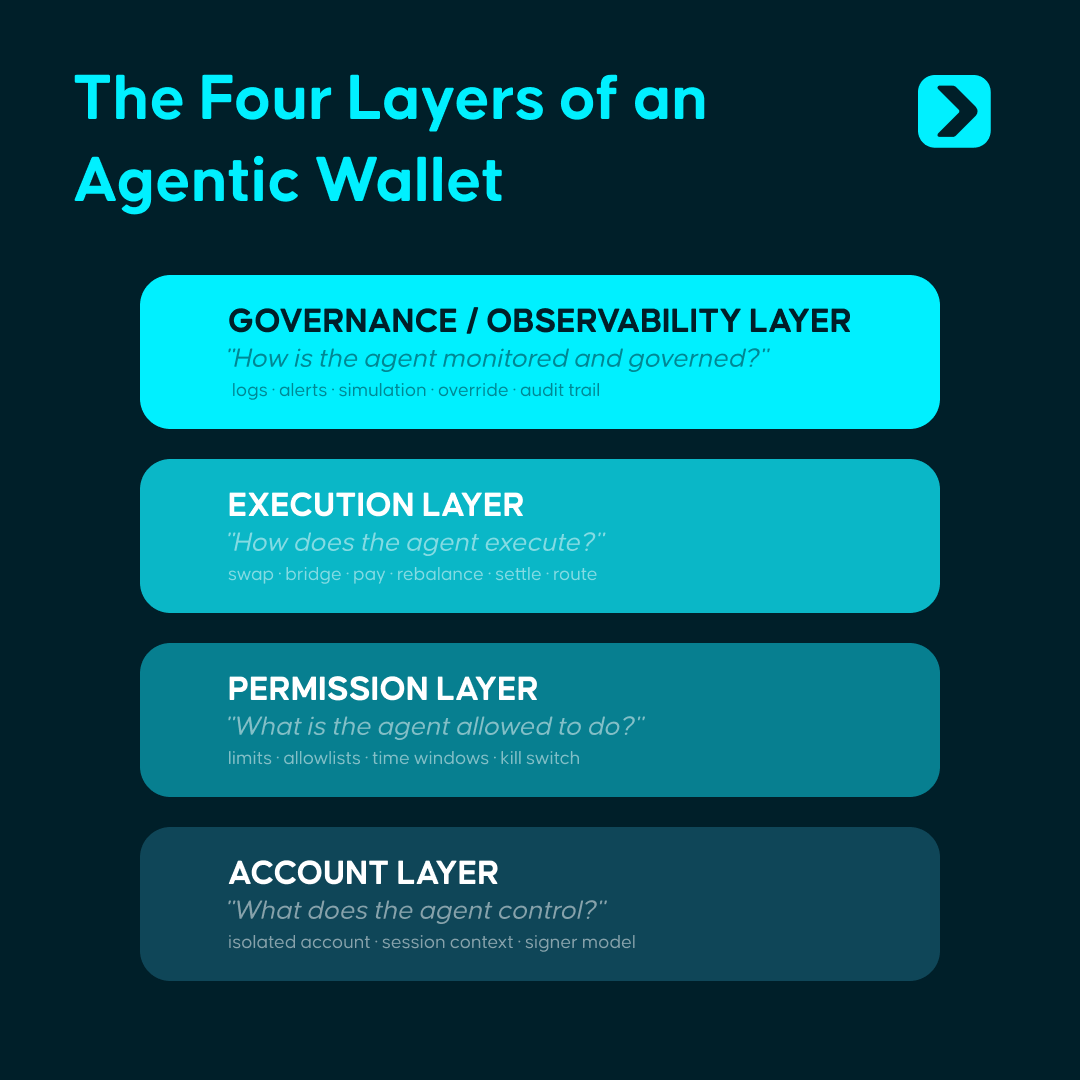
Realizing this vision requires a four-layer architecture:
- Account Layer: Establishes isolated economic containers for each Agent—via EOA, smart contract accounts, server wallets, or TEE environments. The system must apply differentiated rules to different Agents.
- Permissions Layer: Defines behavioral boundaries for Agents—including spendable amounts, operable assets, interactable contracts, executable time windows, and post-boundary-trigger actions. This is the architectural core.
- Execution Layer: Exposes interfaces for Agents—not for human clicks. Sending, paying, swapping, bridging, rebalancing, liquidating, and settling must all be abstracted as primitives directly callable by programs.
- Governance Layer: Must provide logging, simulation, audit trails, alerts, pause switches, human veto rights, and recovery mechanisms. This layer determines whether an Agentic Wallet can truly enter production.
Above this four-layer architecture, four core capabilities are required to sustain system operation:
- Skills: Provide standardized on-chain operation modules. Agents can execute trades, payments, bridges, etc., like function calls—without manually assembling low-level calldata. Skills solve the abstraction problem of “what can be done.”
- Policies + KYA / KYT: The Policies engine validates each operation against human-defined rules, converting boundaries into machine-enforceable constraints; KYA/KYT mechanisms identify an Agent’s origin, identity, risk context, and operational history. The former constrains behavior; the latter identifies the actor—both ensuring all fund movements remain within preset boundaries.
- Session Keys: Offer time-bound, amount-limited, scope-restricted secure delegation. Agents receive temporary, constrained authorization—not full private keys. Authorization expires automatically without manual revocation—“granting Agents execution eligibility without exposing them to complete private keys.”
- Audit & Notification: Deliver fully traceable operation logs and real-time alerting. Every action is reversible; every anomaly triggers alerts; every Agent can be paused instantly.
Today we typically control Agent behavior logic via instructions—but task orchestration does not equate to fund constraints. Agents may still misjudge, deviate, or suffer from attacks and malicious input contamination. The wallet layer’s significance lies precisely in pre-hardcoding system rules for questions like: “Can funds be moved? How much? Which assets? With whom? And how to halt under anomalies?” Even if an Agent strays, actual fund movements remain confined within preset boundaries.
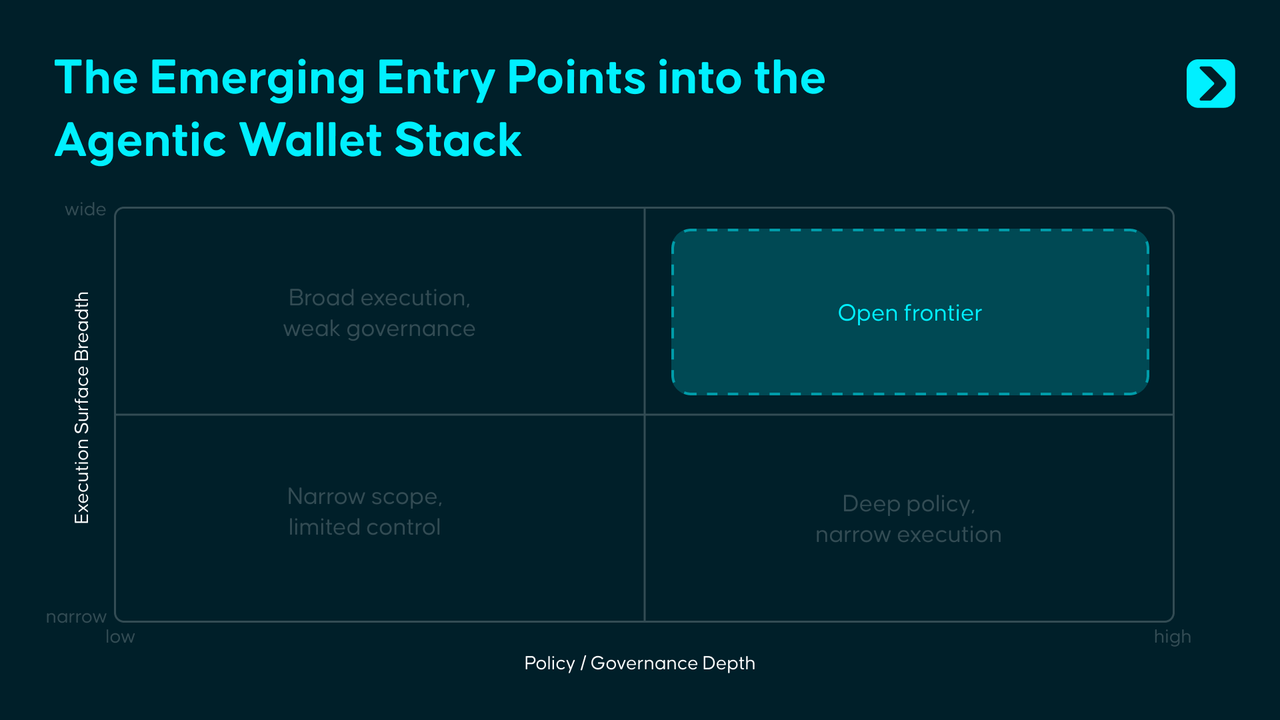
IV. Current State of Agentic Wallets: Four Paths and Four Gaps
Surveying existing Agentic Wallet initiatives, we identified four representative cases—each having largely solved “how to get Agents into the financial system,” yet none having yet addressed “how to let Agents safely use funds across chains and complex real-world environments.”

Coinbase, Safe, Privy, and Polygon have each delivered viable solutions at the infrastructure, governance, permissions, and identity layers—but have not yet integrated these localized capabilities into a unified control framework capable of operating cross-chain, migrating across environments, and remaining robust under complex adversarial conditions. Current bottlenecks common to Agentic Wallets center on four critical gaps:
First, identity and reputation remain non-portable.
On-chain Agent identity and reputation systems can be built—but universal credit frameworks spanning chains, wallets, and runtime environments remain nonexistent. An Agent’s history and reputation accrued in one ecosystem cannot naturally migrate to another.
Second, the policy layer lacks unified standards.
Coinbase uses spending limits; Safe uses on-chain modules; Privy uses a policy engine; Polygon uses session-scoped wallets. The industry broadly recognizes the permissions layer as central—but has yet to establish portable, composable, and cross-product reusable policy standards.
Third, adversarial security remains highly underdeveloped.
Prompt injection, tool poisoning, malicious Skills, and contaminated external inputs won’t be automatically resolved by traditional smart-contract audits. The truly novel challenge introduced by the Agent era is: when a model’s decision process is distorted by malicious inputs, how should the wallet detect, intervene, and block the risk?
Fourth, full-chain coverage remains far from realized.
Most current solutions are tied to a single chain or limited multi-chain scope—but Agent economic activity won’t remain confined to a single ecosystem. A truly mature Agentic Wallet must address multi-chain environments, diverse execution contexts, and cross-domain permission consistency.
V. Beneath the Surface: The Next Decade of Agentic Wallets
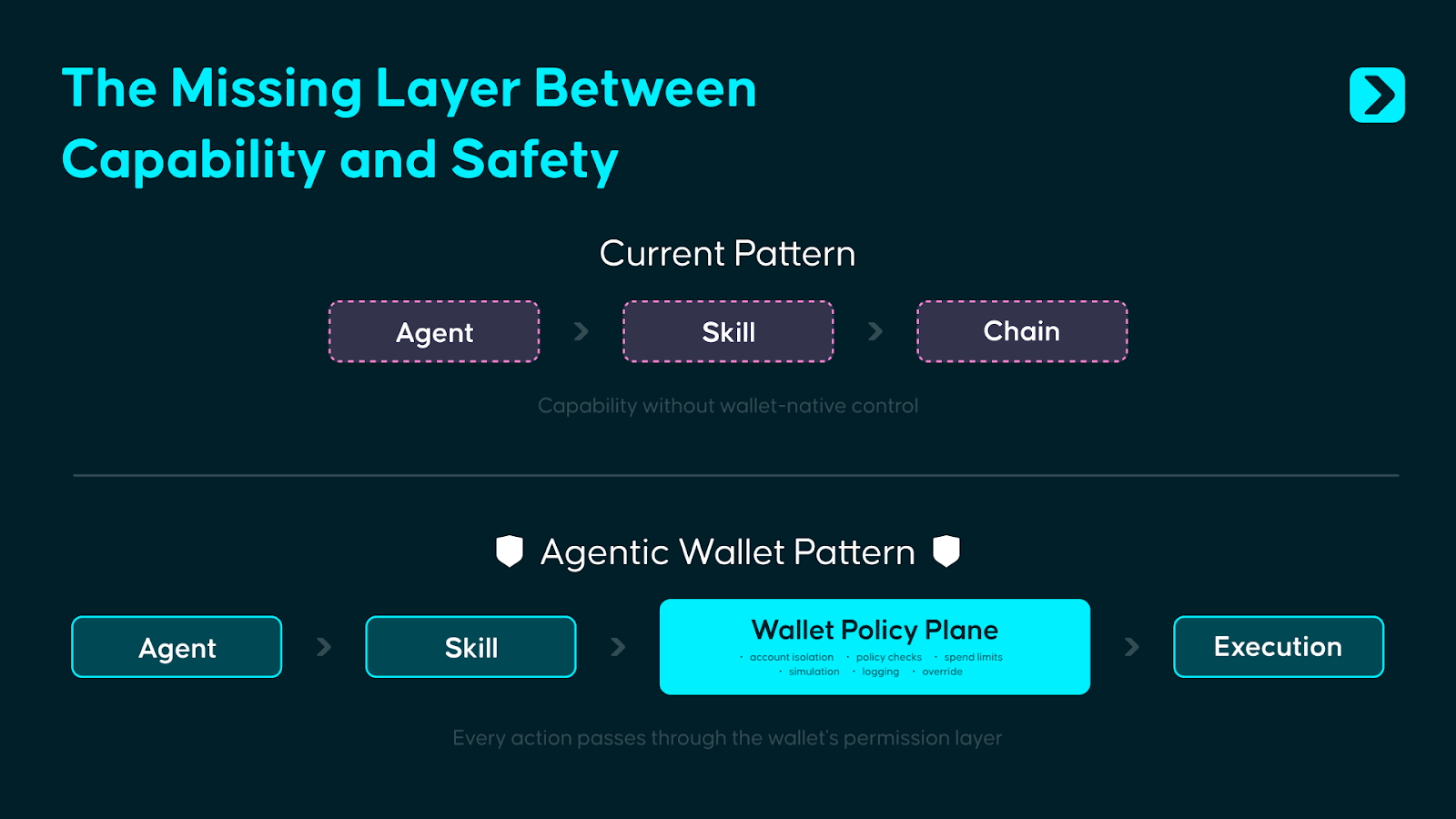
Currently, Agentic Wallet design prioritizes empowering humans to exert fine-grained control over Agents. In most implementations, the wallet plays a passive role—as little more than a signer: the Agent invokes a Skill, the Skill generates a transaction, the wallet signs it in the background, and on-chain execution follows.
But if Agents truly begin managing funds, signing only at the final step is clearly insufficient. A more reasonable approach is to embed permission checks before execution: after an Agent invokes a Skill, the request first enters the wallet’s internal Policy Plane—and execution proceeds only upon successful policy validation.
The Wallet Policy Plane borrows concepts from system architecture’s Control Plane and Data Plane. Positioned between Agent behavior and on-chain execution, it unifies the Policies engine, KYT/KYA verification, Session Key validation, risk scoring, and anomaly handling into a single decision plane.
This concept is familiar: Stripe’s payment architecture follows similar logic—developers call clean APIs, but behind the scenes, Stripe performs risk identification, rule checking, and compliance processing before funds move. The fundamental task of an Agentic Wallet is identical: provide developers with a clean execution interface at the top layer, while using a front-loaded policy engine to adjudicate permissions at the lower layer.
The urgency stems from rapidly expanding attack surfaces—prompt injection, tool poisoning, malicious Skills—while wallet-side security infrastructure lags far behind. A standardized Wallet Policy Plane has yet to emerge as an industry-wide foundational primitive.
That said, the Policy Plane itself won’t be the final state. As Agent identity and reputation systems mature, authorization logic will shift from static rule-based to dynamic trust-based models. Today, we rely on preset boundaries, amount caps, whitelists, and manual override paths; tomorrow, on-chain transaction records, behavioral traces, and cross-ecosystem credit data will gradually form a verifiable Agent credit foundation—making more authorization decisions based on identity, history, and actual performance.
When Agents begin conducting economic interactions with each other at machine speed, control mechanisms must be built in from day one. The wallet’s role will likewise evolve: initially acting as a gatekeeper blocking out-of-bounds behavior; eventually becoming infrastructure—enabling trusted entities to connect accounts, permissions, and settlement systems continuously and with minimal friction.
For the past decade, the wallet battlefield was the screen—the entry point. For the next decade, the battlefield lies beneath the surface—in the invisible layer of control.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News