Key Takeaways: How to Secure My Assets When Navigating the Web3 Dark Forest?
TechFlow Selected TechFlow Selected
Key Takeaways: How to Secure My Assets When Navigating the Web3 Dark Forest?
The centralized custody trust crisis triggered by the FTX incident will have what impacts on exchanges, the security industry, and others?
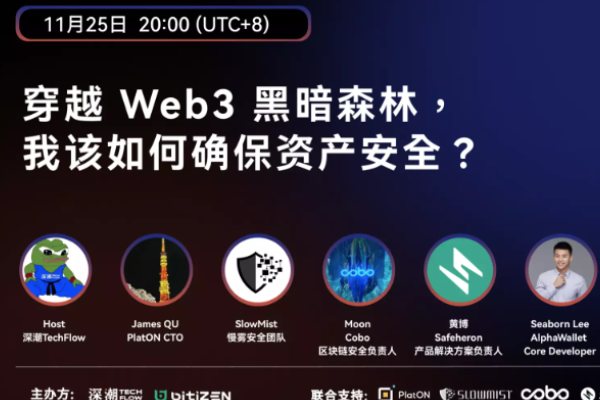
Last Friday, TechFlow co-hosted with Bitizen Wallet on Twitter Space the event titled “Navigating the Web3 Dark Forest: How Can I Secure My Assets?” TechFlow has compiled the key takeaways from this session for your reading.

Event Guests:
- James, CTO of PlatON
- SlowMist, security team
- Moon, Head of Blockchain Security at Cobo
- Huang Bo, Product Solution Lead at Safeheron
- Seaborn, Core Developer at AlphaWallet
- Winson Liu, Founder of Bitizen
Moderator: What impacts will the trust crisis triggered by the FTX incident have on exchanges and the security industry?
PlatON: For PlatON, we focus on two things: building blockchains with advanced consensus algorithms, and creating a privacy-preserving computation network—essentially packaging cryptographic algorithms into usable libraries and open protocols that can integrate privacy computing with blockchain.
Why do this? Because our lives are increasingly data-driven—an irreversible trend. Once digitized, this data becomes wealth, currently monopolized by tech giants whose AI feeds us personalized content. This leads to fragmented realities where individuals receive vastly different information streams, often resulting in conflict. People are being led by centralized AI systems, increasing societal anxiety. That’s why we aim to build a democratized AI—with privacy-preserving algorithms—that ensures data ownership remains with its rightful owner.
Although FTX operated under the banner of crypto, its collapse was fundamentally traditional—misappropriation of funds, lack of oversight, and chaotic spending. At the moment of collapse, hackers also stole money. It fell spectacularly due to poor governance—carrying Wall Street's prestige but lacking proper financial regulations and checks. As a result, many were deceived and suffered heavy losses. This trust crisis gives central authorities an excuse to step in: “We must protect investors.”
Those who truly owned their data and controlled their assets were unaffected; it was the centralized exchanges (CEXs) with flawed internal management that failed. FTX collapsed through conventional means—it had little to do with blockchain or decentralization.
I am more concerned about recent developments, such as Singapore’s Monetary Authority stating that cryptocurrencies are dangerous and should be tightly regulated.
SlowMist: SlowMist is a company dedicated to blockchain ecosystem security. We appreciate the invitation and are honored to join this discussion.
The FTX incident has significantly impacted various sectors, especially the security and exchange industries.
- First, users now face renewed distrust toward centralized exchanges and institutions.
- Second, major CEXs and institutions are adopting Proof of Reserves (PoR), aiming to rebuild user confidence. This transparency benefits both users and the broader crypto ecosystem.
- Third, previously opaque CEXs are gradually becoming partially transparent, voluntarily disclosing information and accepting community scrutiny—a positive evolution.
Post-FTX, users may prioritize exchanges that provide PoR verification, reducing risks associated with depositing funds on unverified or fraudulent platforms.
While PoR is commendable, some implementations rely solely on third-party audits of reserve snapshots at specific points in time. This approach is insufficient. Users ideally want real-time, continuous PoR transparency from CEXs—not just periodic audits by reputable firms.
Cobo: Cobo provides digital asset custody and blockchain technology services. I lead blockchain security on the client side.
The FTX incident has undoubtedly caused a trust crisis among exchanges, triggering bank runs and potentially causing smaller exchanges to fail. Larger exchanges may respond by implementing PoR (Proof of Reserves). In the long term, this increases fund transparency—a positive development. However, overall, the event dealt a significant blow to the blockchain industry.
Recently, industry KOLs have said FTX set the sector back years. This sentiment is reflected in market prices—just when recovery seemed possible, we may now face a prolonged bear market. While the impact on blockchain security isn't direct—since this wasn’t a technical vulnerability but rather human greed or mismanagement—it does highlight systemic flaws.
However, there’s a silver lining: growing distrust in centralized platforms may drive more users toward decentralized wallets. This creates demand for self-custody solutions, prompting teams to innovate in areas like wallet plugins and risk-alert tools aimed at retail users.
Safeheron: I’m Huang Bo, Product Solution Lead at Safeheron. Safeheron is a self-custody platform built on MPC and TEE technologies, primarily serving institutional clients and high-net-worth individuals requiring multi-signature asset management.
Tracing back, the crisis began with Three Arrows Capital, which detonated a chain reaction culminating in FTX’s collapse—triggering a full-blown financial crisis across the industry affecting users, builders, and institutional players alike.
Exchanges were hit hardest. Users and institutions are now extremely cautious—traumatized by Three Arrows and FTX—and are rapidly withdrawing funds into decentralized wallets fearing further black swan events.
This shrinks survival space for mid-tier exchanges, leaving Binance dominant. Market recovery will take time—there are no new narratives or fresh talent entering the space.
Everyone thought this cycle would be driven by institutions—but they’ve already been wiped out. Restoring market confidence requires a powerful new narrative to reignite liquidity. Whether centralized platforms evolve via regulatory integration or trusted third-party custodians remains uncertain.
Today’s guests work on wallets or security—this shift presents opportunities. The entire industry is pushing centralized platforms toward greater transparency in internal controls, risk management, and fund handling to restore trust. This opens doors for security teams to showcase their expertise.
But mass migration to decentralized wallets brings new risks: managing private keys is still a major challenge—for both individuals and institutions. Phishing and social engineering attacks remain rampant—for example, recently the founder of Distributed Global had his funds stolen shortly after withdrawing from FTX.
AlphaWallet: I'm Seaborn, a developer at AlphaWallet. Unlike other experts here, I've only recently joined the team, so my insights may not be as deep.
Our team, Smart Token Labs, aims to help real-world businesses tokenize more easily—similar to how Taobao enabled physical merchants or factories to reach consumers during the internet era.
Our product has two parts:
- TokenScript middleware—backend-focused, dealing with smart contracts, mostly invisible to end-users;
- Super App—my team, AlphaWallet—which functions like Alipay: not just a payment tool, but a super app hosting various services.
My wallet team is one of the beneficiaries mentioned earlier—we offer self-custody: you control your private keys, we never touch them, and you're responsible for backups.
Regarding FTX: it’s bad news for creditors (those who lost funds). But for others (who weren’t directly affected), it could be beneficial.
As previous speakers noted, awareness around security has increased. More users are moving assets from CEXs to MPC-based nodes or self-custody wallets—posing greater challenges for decentralized wallet developers and driving technological maturity.
As long as an event doesn’t destroy the entire industry, it offers room for reflection and iteration—making us better prepared.
Bitizen: I’m Winson, founder of Bitizen Wallet—a next-generation Web3 wallet based on MPC technology, eliminating the need for private keys or seed phrases. What sets Bitizen apart is combining maximum security, full decentralization, and privacy protection with Web2-level ease of use. Simply put, it’s an innovative wallet with a Web3 core wrapped in a Web2 interface—the essential gateway for Web2 users entering Web3.
I believe the FTX fallout has two main implications:
- First, regaining user trust will become harder for centralized exchanges. This accelerates polarization—Binance-like giants grow larger. Personally, if I use a CEX, I’d likely stick to Binance. Others may struggle to survive.
- Second, this marks a turning point—the industry gradually shifts from centralization to decentralization. As wallet developers and security professionals, our responsibility grows heavier. Self-custody models place security responsibility on users, so wallet builders must balance usability and safety.
Before FTX, low-barrier wallets were trending—focused on improving usability for Web2 and Web3 users. Unfortunately, many achieved simplicity by compromising security.
Moderator: What are the current limitations of widely discussed Proof of Reserves (PoR) or Merkle Trees, and what better solutions exist?
PlatON: PoR is commonly used in traditional finance—like posting collateral to a central bank before issuing loans.
How can this be implemented technically? Vitalik Buterin proposed ideas like enabling distributed community verification of account balances to confirm total reserves. The fundamental issue lies in “client profiling”—how much money is in your account and what transactions occurred.
For financial institutions, this data must remain confidential. But for a decentralized, trustless ledger, transparency is ideal. Balancing usability, security, and privacy presents a great opportunity for experts to innovate.
Most people barely understand crypto—let alone PoR or Merkle Trees. There’s a need to educate users and break down knowledge barriers.
SlowMist: Currently, many CEXs use third-party PoR services. Some of these services only reflect reserve status at a single point in time (lacking real-time, continuous validation), and may not cover all tokens—especially when exchanges support numerous assets. Ideally, coverage should approach 100%.
Another concern: publicly listing reserve wallets could expose them to targeted attacks by hackers monitoring large holdings.
Currently, CEXs are adopting PoR to rebuild trust, but issues around timeliness, accuracy, and token coverage remain. The optimal level of PoR implementation will require ongoing adjustment and consensus within the market, community, and ecosystem.
Cobo: Fundamentally, PoR is an accounting reconciliation problem—matching user deposits against on-chain holdings. Merkle Trees help verify whether a user’s balance belongs to the system, but several critical gaps remain unresolved.
Here are key concerns:
- First, fake users. A Merkle Tree only proves a user exists within the tree, not that all entries represent real users. Exchanges could fabricate fake accounts and balances. These fake users won’t verify proofs, and others can’t validate authenticity without knowing actual user balances. This allows inflated reserve totals without genuine backing. Full ledger disclosure (e.g., publishing all addresses) could solve this, but financial confidentiality makes this impractical.
- Second, fake funds. Since PoR audits aren’t real-time, institutions can temporarily borrow funds to pass inspections. For instance, raising capital days before an audit, depositing it, then redeploying afterward. One solution: random, unpredictable audits—making manipulation difficult, though operationally challenging.
- Third, fake addresses. Even if institutions publish wallet addresses, there’s no way to confirm ownership. Some suggest requiring signatures, but a single signature isn’t enough—malicious actors could collude with external parties to sign. A better solution: use MPC + TSS. With secret sharing, a third-party auditor holds a key shard—insufficient alone to move funds—but capable of verifying the institution’s complete address set and real-time asset levels at any block height. This enables effective auditing. MPC-TSS custody is a product Cobo recently launched.
Safeheron: Our team open-sourced the Merkle Tree algorithm back in 2019 and applied it to ensure 100% reserve backing for a prior startup. To gain customer trust, we implemented fully transparent, daily snapshot-based PoR and encouraged the entire market to follow suit—though few did. Now, CZ advocates for PoR, and widespread adoption is underway; those who don’t comply may be perceived as suspicious.
Our method involved publishing all wallet addresses, covering every user, with daily snapshots—technically preventing fraud and boosting market confidence.
Benefits included rapid business growth. The downside: exposing wallets allowed adversaries to analyze positions, leverage ratios, and liquidation triggers—enabling targeted attacks. Jealous actors (including hackers) might target the platform, demanding extremely high security standards.
Despite deep collaboration with SlowMist and top-tier defenses, we always felt uneasy. In centralized architectures, hot wallets are always online, and private keys exist in plaintext. We wondered: is there a way to make private keys *never* appear, yet still function when needed?
How should users evaluate PoR and Merkle Trees?
- Check if the platform has historical baggage—has it ever stolen funds? If yes, their PoR claims warrant skepticism—perhaps they borrowed funds to meet audit requirements.
- Next, examine snapshot frequency. Monthly or biweekly intervals give platforms time to misuse funds between audits.
As more exchanges adopt PoR, the industry progresses. The best solution may mirror traditional finance: separating brokerage from custody. In crypto, this could mean regulated third parties hold user funds—exchanges wouldn’t control assets. Banks could play this role, though that reintroduces centralization, privacy risks, and loss of autonomy. Today’s centralized platforms already embody this model—users surrender privacy and control to central entities.
AlphaWallet: Many in Web3 treat USDC and USDT as income sources. But when proof of assets is required—say, applying to school—there’s no good way to demonstrate holdings. Traditionally, bank statements or savings certificates suffice.
From a personal view, average users shouldn’t need to understand complex tech—it’s too technical and costly to learn. They’ll care more about whether reputable security firms have certified the platform.
Bitizen: PoR and Merkle Trees serve as useful patches for current centralized custody models. I agree that decentralized exchanges and custody solutions represent the future. These native approaches are upgradable and potentially far superior to patchwork fixes like PoR—they can fundamentally prevent malicious behavior.
Moderator: Compare security pros and cons of various decentralized wallet solutions—what will dominate in the future? (Hot wallets, cold wallets, MPC wallets, smart contract wallets)
PlatON: Different users have different needs. Tech enthusiasts value innovation, others prioritize service quality, while some prefer centralized experiences.
Ideally, wallet infrastructure should be diverse—offering tailored options based on user experience levels.
SlowMist: Cold wallets suit advanced users—high entry barrier and cumbersome interactions, but highly secure. MPC wallets, smart contract wallets, and traditional decentralized wallets aim to simplify Web3 access and lower onboarding friction.
From a security standpoint, wallets are keys to the Web3 world. User interactions should strive for “what you see is what you sign.”
MPC and smart contract wallets technically eliminate single-point key risks—preventing loss or theft of private keys or seed phrases. For example, MPC allows refreshing key shards; smart contract wallets enable recovery/reset via social tools. These technologies aren’t mutually exclusive—smart contract wallets can incorporate MPC for key management.
Cobo: Strictly speaking, cold and hot wallets describe operational practices rather than distinct types—they’re methods of fund management.
Frequently used funds go into hot wallets for daily interaction; idle funds stay in offline cold storage. Institutions like exchanges commonly adopt this model. For individuals: safeguard your seed phrase, consider hardware wallets if possible, and strengthen security awareness—it goes a long way.
Smart contract wallets better suit institutional or high-net-worth users. They trade some convenience for enhanced security via multi-signature setups. Instead of a single point of failure (losing a private key = losing everything), you can set thresholds like 3-of-5 signatures—so losing one key doesn’t compromise funds.
But each transaction requires gathering multiple signatures—reducing convenience. As previously noted, there’s inherent tension between usability and security. Recently, Cobo launched Cobo Argus (https://argus.cobo.com/), built on Gnosis Safe, offering decentralized authorization and risk control. It allows certain low-risk operations to be delegated to single-signature addresses—streamlining multi-sig workflows while maintaining security.
Safeheron: Solutions vary by use case. Cold and hot wallets differ in how they protect private keys *after* generation. MPC fundamentally changes the paradigm—ensuring private keys never appear, using math and cryptography to manage them.
Private key generation: Using MPC protocols, the private key itself never exists. Instead, multiple parties engage in rounds of computation to generate cryptographic fragments—called key shards. These shards have no physical relation to the original private key. Mathematically, they collectively map to it, but the original key is never created centrally or distributed—it emerges from independent calculations by each party.
When using the private key: For actions like transfers or contract interactions, the key shards participate in multi-round communications. Only when all relevant shards are present can a valid signature be generated—functionally equivalent to one signed by the original private key. Thus, the key is usable—but never visible or exposed.
MPC wallets fall into two categories: To C and To B.
- To C: Platforms like Bitizen excel in secure UX—delivering keyless experiences including social recovery. As mass adoption grows, such wallets have a natural advantage over complex alternatives like smart contract wallets. Domestically, Bitizen and internationally, ZenGo stand out.
- To B: Companies like Safeheron and Fireblocks address enterprise security needs—managing assets across chains, exchanges, and banks in one system. Ensuring operators cannot freeze funds, supporting flexible multi-level approval workflows, and enabling auditable Web3 interactions—all critical for institutional users. This is our focus.
AlphaWallet: MPC wallets bridge the gap between mainstream users and Web3 adoption. Yet, veteran users accustomed to private keys may feel uneasy switching to keyless, seedless products—worried about losing access if the service shuts down.
So even though MPC is promising, different wallets fit different scenarios—just as people keep money in safes, bank cards, WeChat, or JD.
Bitizen: As a To C wallet solution provider, we’ve thoroughly researched existing wallet models. While we specialize in MPC, our vision extends beyond it.
Cold and hot wallets revolve around private key security—whether stored on connected devices. A wallet is an asset management tool; hackers target your private key or seed phrase. Their cheapest attack vector is usually online—so disconnecting eliminates most threats. Hence, hardware wallets are inherently safer than software ones.
However, with MPC and next-gen smart contract wallets emerging, hardware wallets may no longer be the safest option.
If we categorize by seed/private key dependency, traditional software and hardware wallets belong to the old generation. MPC-based solutions represent the new wave.
Hardware wallets protect private keys well—but say nothing about seed phrase security. From this angle, securing assets depends entirely on user diligence. If users lose their seed phrases, even hardware wallets offer no protection.
Considering both private keys and seed phrases, I believe next-gen solutions surpass hardware wallets in security—by fundamentally eliminating both. Being keyless and seedless is a deeper, more radical solution.
That said, achieving true security with MPC wallets introduces new design challenges—even after removing keys and seeds.
Many misunderstand Account Abstraction (AA). Some concepts are overhyped—especially since V神 champions it. His influence, combined with Ethereum maximalists who dismiss everything outside Ethereum, fuels blind faith in on-chain-only solutions. While aligned with decentralization ideals, this worldview may not serve everyday users’ practical needs.
Smart contract wallets don’t eliminate private keys—they remove seed phrases. Keys can still be managed via MPC. Controlling a smart contract wallet using MPC is entirely feasible—and our team is actively working on it.
I think ERC-4337 and similar smart contract wallets are overhyped. They have serious flaws.
First, gas costs. All wallet logic runs on-chain, meaning every action incurs gas fees. You wanted low barriers, but now every operation—including wallet creation—requires gas. Regular EOAs only pay gas for transactions; otherwise, none. But with smart contract wallets, even setup costs gas.
Though gas sponsorship models exist, they merely shift costs—to wallet developers or dApp providers. For users, this raises entry barriers instead of lowering them.
They only lower barriers in niche cases—e.g., paying gas with ERC-20 tokens during transfers.
Second, severe compatibility issues. Non-developers rarely grasp these problems. Smart contract wallets face enormous interoperability challenges ahead. We support innovation, but urge cooler, more nuanced perspectives.
Moderator: As Web3 builders—from wallet devs, app devs, security firms, and protocol layers—where are the biggest untapped security improvements?
PlatON: One area is risk control—commonly called anti-money laundering (AML), though perhaps more accurately described as pre-screening for links between user addresses and known hacker addresses. Traditional finance uses simulation and visual analytics for early warnings—UX improvements here are standard.
I’ll highlight two challenges: How will wallet security adapt to the quantum era? And how do we protect seed phrases for elderly or cognitively impaired users? MPC is a promising direction—it’s chain-agnostic and supports signing across multiple chains, unlike smart contract wallets which lack universality.
SlowMist: Much of our discussion centered on MPC. Most current MPC wallets are still early-stage—often using 2-of-2 threshold designs, where part of the key is managed by the project team to improve user experience. This requires mutual education between users and providers before truly robust MPC wallets emerge.
Personally, I look forward to user-controlled MPC wallets—fully decentralized, easy-to-use solutions where users manage their own shards. For those of us favoring decentralization, having full control over shards is ideal.
Cobo: The best way to secure seed phrases today is to not have them at all—using MPC solutions like Bitizen or multi-sig wallets.
Quantum computing may eventually break private keys, but this will likely unfold gradually. Meanwhile, blockchain will evolve—potentially yielding quantum-resistant cryptographic solutions along the way.
Safeheron: Security infrastructure is still nascent. The market lacks a comprehensive, proactive defense system covering multiple threat vectors—akin to Web2 antivirus software like 360.
MPC involves complex cryptography and mathematics—intimidating for most users. Innovation and disruption are needed to fuel the next narrative. We’re already planning decentralized, user-centric private key protection infrastructure.
AlphaWallet: I believe wallet security must meet three criteria: open-source code, third-party code audits, and white-hat penetration testing.
Future trends: MPC will play a vital role in next-gen wallet security. We need standardized portability—allowing users to migrate wallet accounts across apps, similar to how seed phrases work today. This enhances user confidence and freedom.
As app developers, we stress platform-specific optimizations. For example, many wallets prompt immediate seed backup after registration. But if the user switches apps mid-backup and someone else accesses the phone, is the seed still visible? Many wallets fail here—attention to detail matters.
Bitizen: For average users, focusing on security audits is sufficient—they don’t need to understand everything. Trust authoritative bodies like SlowMist—their audit reports offer reliable guidance.
Audits also reveal a team’s commitment to security—since audits cost money. Teams willing to invest signal stronger dedication—making their products more trustworthy.
I believe MPC needs wider adoption, standardization, and infrastructure-level integration—raising the entire industry’s security baseline. No wallet can prevent phishing—these are psychological attacks outside technical scope, akin to telecom fraud. Technology alone cannot fix this—only user education can.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News