TechFlow news: On March 13, Etherscan revealed that address-poisoning attacks on Ethereum have intensified significantly—especially following the Fusaka upgrade, which lowered transaction costs, leading to a notable surge in high-frequency attack activity.
A study covering July 2022 through June 2024 found approximately 17 million poisoning attempts occurred on Ethereum, affecting roughly 1.3 million users and resulting in confirmed losses of at least $79.3 million. The Fusaka upgrade, activated on December 3, 2025, reduced both transaction fees and attacker costs. Within 90 days post-upgrade, USDT dust-transfer volume surged from 4.2 million to 29.9 million transactions (+612%), while USDC dust transfers rose from 2.6 million to 14.9 million (+473%). Though the success rate per poisoning attempt is only about 0.01%, attackers achieve substantial returns via mass-batch sending—previously causing users to lose as much as $50 million.
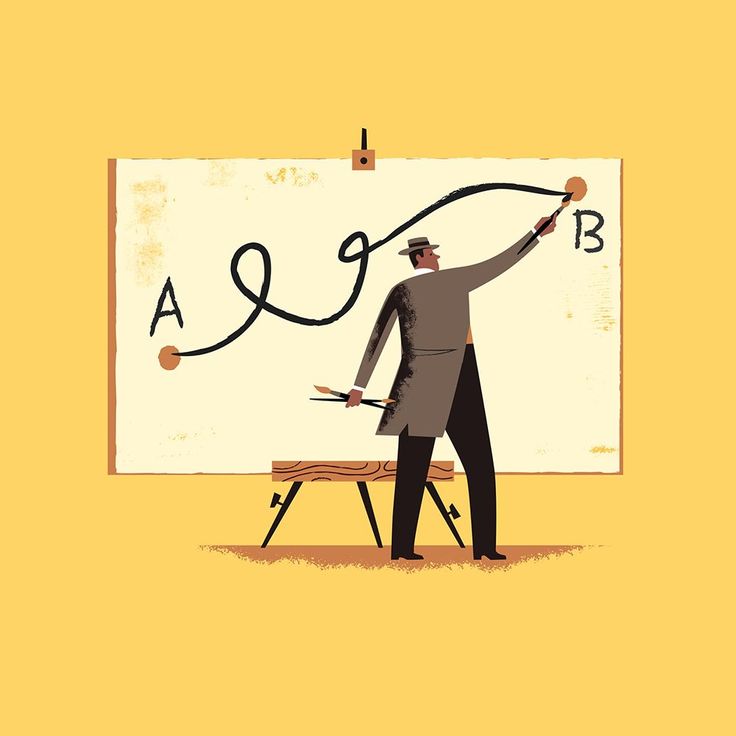
Address-poisoning attacks work by sending small-value transfers with spoofed addresses to target wallets, thereby embedding fake addresses into users’ transaction histories and tricking them into inadvertently copying the wrong address during their next transfer.