An open-source AI tool no one was watching flagged a $292 million vulnerability in Kelp DAO 12 days ago
TechFlow Selected TechFlow Selected

An open-source AI tool no one was watching flagged a $292 million vulnerability in Kelp DAO 12 days ago
AI Agents can serve as an independent security layer for DeFi investors.
Author: Zengineer
Translation & Compilation: TechFlow
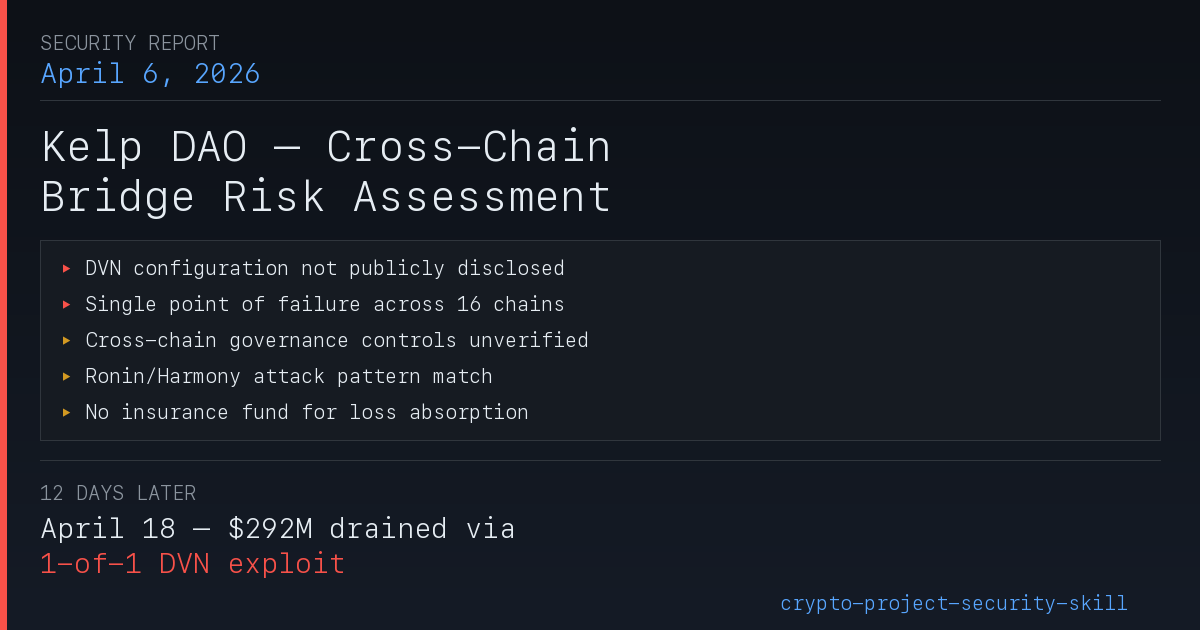
TechFlow Intro: On April 18, 2026, Kelp DAO suffered a $292 million exploit—the largest DeFi incident of 2026 to date. The vulnerability was not in the smart contract code, but in LayerZero’s cross-chain bridge configuration: a 1-of-1 validator node setup, where compromise of a single node enabled forgery of cross-chain messages. Twelve days earlier, on April 6, my open-source AI-powered auditing tool had already flagged this exact risk during a scan of Kelp. This article reconstructs the full attack timeline—and honestly reflects on three things the tool got wrong.
What Is Kelp DAO?
Kelp DAO is a liquid restaking protocol built atop EigenLayer. Its mechanism works as follows: users deposit ETH or liquid staking tokens (e.g., stETH, ETHx) into Kelp’s contracts, which then delegate those assets to EigenLayer’s operator nodes for restaking—simultaneously providing security to multiple AVSs (Actively Validated Services). In return, users receive rsETH as a receipt token. Unlike direct restaking on EigenLayer (where assets are locked), rsETH is liquid—it can be traded, used as collateral in lending protocols like Aave, and bridged across chains.
To enable this cross-chain liquidity, Kelp deployed rsETH across more than 16 chains using LayerZero’s OFT (Omnichain Fungible Token) standard. When rsETH is bridged from Ethereum to an L2, LayerZero’s DVN (Decentralized Verifier Network) validates whether the cross-chain message is legitimate. This bridge architecture lies at the heart of the subsequent incident.
Kelp was founded by Amitej Gajjala and Dheeraj Borra (previously co-founders of Stader Labs), launched in December 2023, peaked at $2.09 billion TVL, and employs a 6/8 multisig governance model with a 10-day timelock for contract upgrades. Its governance token, KERNEL, oversees Kelp’s three product lines: Kelp, Kernel, and Gain.
The Exploit
On April 18, 2026, attackers drained 116,500 rsETH—worth approximately $292 million—from Kelp DAO’s cross-chain bridge: the largest DeFi exploit of 2026 so far. The root cause was not a smart contract vulnerability, but a configuration flaw: a 1-of-1 DVN setup (i.e., only one validator node, requiring just one signature for message approval), enabling attackers to forge cross-chain messages after compromising that single node.
Twelve days earlier, on April 6, my open-source security auditing tool had already flagged this attack surface.
Let’s state it plainly: real people lost real money in this incident. Aave WETH depositors who had never interacted with rsETH saw their funds frozen; LPs across multiple protocols were forced to absorb losses they never agreed to bear. This article analyzes what happened—and what our tool detected—but the human cost matters more than any scorecard.
The full report is hosted on GitHub, with a commit timestamp verifiable by anyone. Below, we detail what our tool caught, what it missed, and what this means for DeFi security tooling.
46 Minutes That Shook DeFi
At 17:35 UTC on April 18, attackers compromised the isolated DVN validator node and coerced it into “approving” a forged cross-chain message. LayerZero’s Endpoint, seeing the DVN signature, forwarded the message via lzReceive to Kelp’s OFT contract—which minted 116,500 rsETH on Ethereum mainnet. The message claimed equivalent assets were locked on other chains as collateral. Those assets never existed.
What followed was a textbook DeFi money-laundering sequence:
- Deposit stolen rsETH as collateral into Aave V3, Compound V3, and Euler
- Borrow ~$236 million WETH against this unbacked collateral
- Aggregate ~74,000 ETH and withdraw via Tornado Cash
At 18:21—46 minutes later—Kelp’s emergency pause multisig froze the contracts. Two subsequent attempts by the attacker (each for 40,000 rsETH, ~$100 million) reverted entirely—this pause blocked an additional ~$200 million in losses.
Yet the fallout remained severe. Aave V3 absorbed ~$177 million in bad debt. The AAVE token plummeted 10.27%. ETH dropped 3%. WETH utilization on Aave spiked instantly to 100%, triggering frantic withdrawals. rsETH on over 20 L2s overnight became assets of highly questionable value.
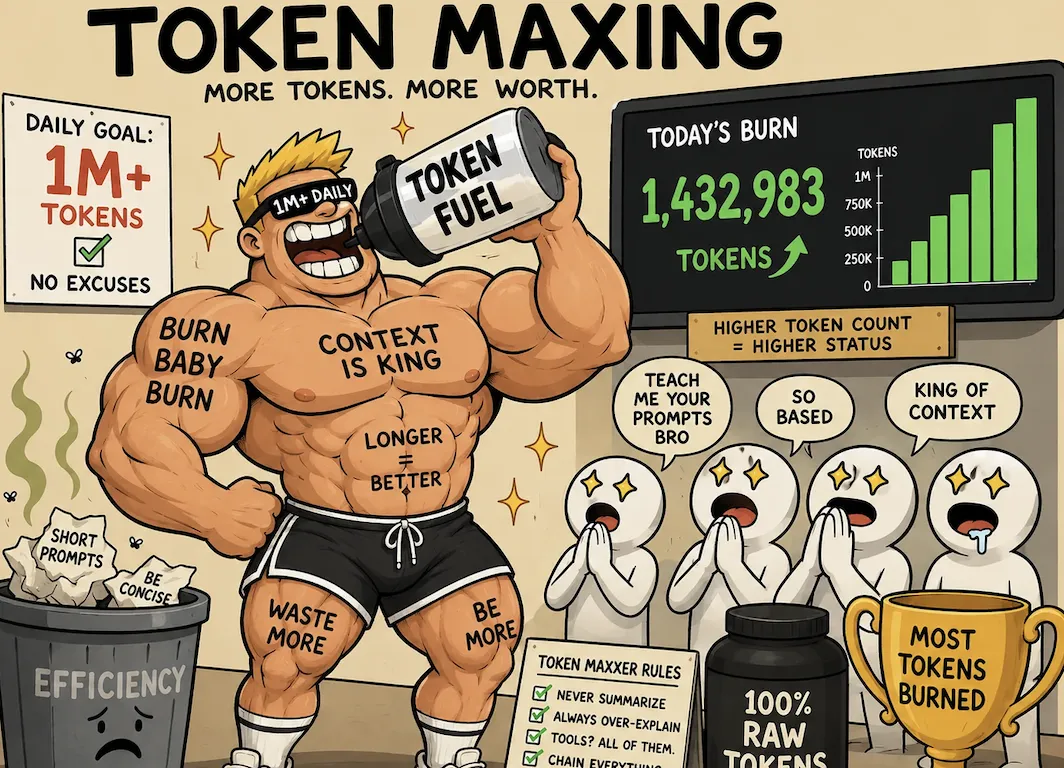
What the April 6 Report Caught
In early April—shortly after the $285 million Drift Protocol exploit on April 1—I developed an open-source Claude Code skill: crypto-project-security-skill. It’s an AI-assisted architectural risk assessment framework that evaluates DeFi protocols using public data (DeFiLlama, GoPlus, Safe API, on-chain verification). It is neither a code scanner nor a formal verification tool. The Drift incident clarified a critical insight: the greatest losses stem not from smart contract bugs—but from governance flaws, configuration oversights, and architectural blind spots—areas traditional code scanners simply cannot see. So I built a tool specifically designed to assess these layers: governance structure, oracle dependencies, economic mechanisms, and cross-chain architecture—comparing each protocol against patterns observed in major historical exploits (Drift, Euler, Ronin, Harmony, Mango).
On April 6, I ran a full audit on Kelp DAO. The full report is publicly available on GitHub, with an immutable commit timestamp.
The report assigned Kelp a composite risk score of 72/100 (Medium Risk). In hindsight, that rating was too lenient—the unresolved cross-chain information gaps should have lowered the score significantly. Yet even under a Medium Risk classification, the report explicitly highlighted the exact attack vector later exploited.
The screenshot below shows the original “Information Gaps” section of the report—the very DVN configuration issue that became the root cause of the $292 million loss:
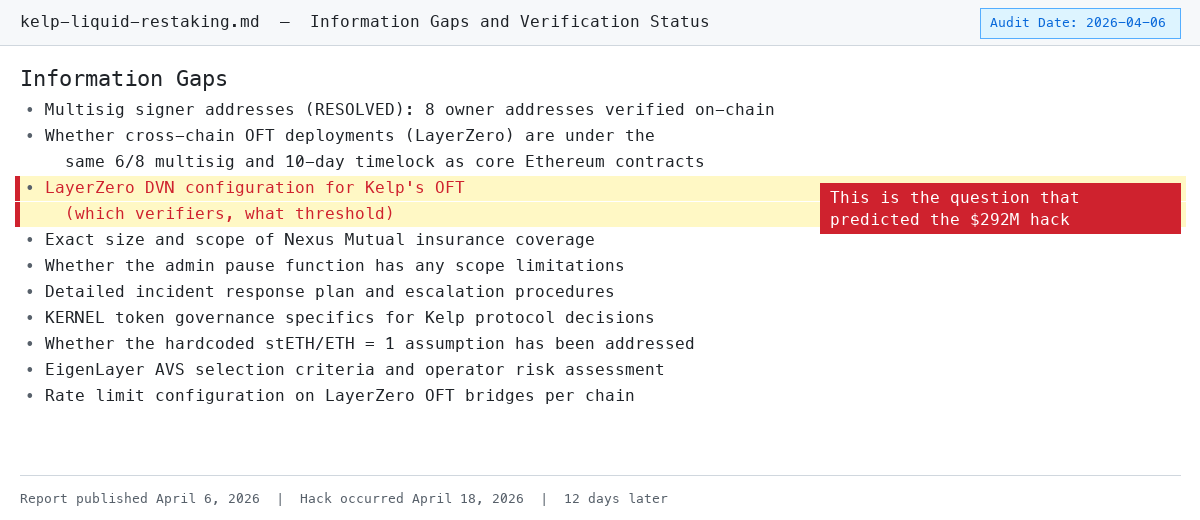
Caption: The “Information Gaps” section of the April 6 report directly named DVN configuration opacity
Below is a point-by-point comparison of what the report flagged—and how it was actually exploited.
Finding 1: DVN Configuration Opacity (Early Warning Signal)
Report Excerpt: “LayerZero DVN configuration (validator sets per chain, threshold requirements) is not publicly disclosed.”
What Actually Happened: Kelp ran a 1-of-1 DVN configuration—one node, one single point of failure. Attackers compromised that single node and forged cross-chain messages. Had the configuration been 2-of-3 (the industry’s minimum recommended threshold), attackers would have needed to breach multiple independent validators simultaneously.
A crucial clarification: this was Kelp’s decision—not LayerZero’s. LayerZero is infrastructure: it provides the DVN framework, and each protocol chooses its own configuration—number of validators (1-of-1, 2-of-3, 3-of-5…), which validators to use, and thresholds per chain. Kelp selected 1-of-1 when deploying its OFT bridge. LayerZero fully supports 2-of-3 or higher configurations—it was Kelp that chose not to enable them.
An analogy: AWS offers MFA (multi-factor authentication). If your account is compromised because you never enabled MFA, that’s your responsibility—not AWS’s. LayerZero provided the security mechanism; Kelp chose not to use it.
Our report couldn’t determine the exact DVN threshold (because Kelp never disclosed it), but we explicitly listed this opacity as an unresolved information gap and risk item. Refusal to disclose is itself a red flag.
Finding 2: Single Point of Failure Across 16 Chains (Direct Hit)
Report Excerpt: “A single-point failure in the LayerZero DVN could simultaneously impact rsETH across all 16 supported chains.”
What Actually Happened: The forged message targeted Ethereum mainnet directly, sending shockwaves across every chain where rsETH was deployed. LayerZero proactively paused all OFT bridges outbound from Ethereum. Holders of rsETH on over 20 L2s suddenly found themselves holding tokens whose backing was no longer verifiable.
This illustrates systemic risk inherent in multi-chain deployment: rsETH circulates across Arbitrum, Optimism, Base, Scroll, and other L2s—but all of its value derives from assets on Ethereum mainnet. Once the mainnet bridge was compromised, rsETH on every L2 instantly lost its guarantee—holders could neither redeem nor verify the value of their tokens. Lido’s earnETH (exposed to rsETH), Ethena’s LayerZero bridge—all were forced to pause. The blast radius extended far beyond Kelp itself.
Finding 3: Unverified Cross-Chain Governance Control (Related Issue)
Report Excerpt: “Governance control over LayerZero OFT configurations across chains remains unverified—specifically: whether such controls fall under the same 6/8 multisig and 10-day timelock governing core protocol upgrades, or are managed via separate admin keys.”
What Actually Happened: DVN configuration clearly fell outside strict core-protocol governance. Had bridge configuration changes also required approval by the 6/8 multisig plus 10-day timelock, a 1-of-1 DVN setting would have needed agreement from six of eight signers—a configuration unlikely to persist unnoticed.
This exposes a common governance blind spot: many protocols enforce rigorous multisig + timelock safeguards for core contract upgrades, yet leave operational-level changes—bridge configurations, oracle parameters, allowlist management—to a single admin key. Kelp’s core protocol governance is industry-leading (6/8 multisig + 10-day timelock), but those protections did not extend to its largest attack surface: the cross-chain bridge.
Finding 4: Alignment With Ronin/Harmony Attack Patterns (Direct Hit)
Report Excerpt: “The most relevant historical precedents involve bridge security. Kelp’s LayerZero deployment across 16 chains introduces operational complexity comparable to Ronin’s multi-chain architecture.”
What Actually Happened: The attack path nearly perfectly replicated the Ronin playbook—compromise bridge validators, forge messages, drain assets. Our tool’s attack-pattern matching module correctly identified this as the highest-risk attack vector by comparing protocol architecture against historical exploit categories—not by scanning code.
Context: In 2022, the Ronin bridge lost $625 million after 5 of its 9 validators were compromised; later that year, Harmony’s Horizon bridge lost $100 million after 2 of its 5 validators were breached. Kelp’s situation was more extreme—only one validator, reducing the attack threshold to its absolute minimum. Our tool flagged this risk precisely because it automatically compares protocol architecture against historical attack patterns—not because it scans code.
Finding 5: No Insurance Pool (Loss Amplifier)
Report Excerpt: “The protocol currently lacks a dedicated insurance pool or socialized loss-absorption mechanism to cover slashing events.”
What Actually Happened: With no insurance reserve, the entire $292 million loss was absorbed downstream by other protocols. Aave’s recovery reserve covered less than 30% of its $177 million bad debt. LPs—unrelated to Kelp’s bridge configuration decisions—bore the brunt of the impact.
Attackers deposited stolen rsETH as collateral into Aave V3, Compound V3, and Euler, then borrowed real WETH against it. Once rsETH was confirmed unbacked, those positions became “uncollateralizable” bad debt—collateral turned to paper, while borrowed WETH was already gone. WETH utilization on Aave spiked instantly to 100%, preventing ordinary users from withdrawing. If you were a WETH depositor on Aave—even if you’d never touched rsETH—your funds were affected. Kelp’s insurance partnership with Nexus Mutual covered only specific treasury products, not the core rsETH protocol exposure.
This was a failure on both sides. Kelp: a $1.3 billion TVL protocol with zero insurance pool, zero loss-absorption mechanism. When the bridge failed, there was no buffer to absorb damage. Aave: accepted rsETH as collateral without adequately assessing its cross-chain bridge configuration risk. Aave’s risk parameters (LTV, liquidation thresholds) were calibrated for normal price volatility—not for “bridge configuration breach causing collateral to vanish overnight,” a tail risk. Its recovery reserve couldn’t even cover 30% of the bad debt. Fundamentally, this was a risk-pricing failure: Aave treated rsETH as a normally volatile asset, though it carried binary tail risk tied to bridge failure. The failures compounded—Kelp lacked insurance to prevent bad collateral from entering the system; Aave lacked sufficiently granular risk modeling to limit exposure in such scenarios.
Where We Got It Wrong
Three things should have been done better:
Risk rating was too low. We rated cross-chain bridge risk as “Medium.” The report contained five unresolved information gaps—three directly tied to LayerZero bridge configuration—and matched Ronin/Harmony historical attack patterns. This should have warranted a “High” or “Critical” rating. Opacity itself should have been a stronger signal.
We failed to penetrate the configuration layer. The report repeatedly requested Kelp disclose its DVN threshold—but we couldn’t independently verify it. This is precisely the same structural blind spot identified in a post-mortem analysis by Cnyes.com: existing audit tools focus on code logic and miss configuration-layer risks. We flagged the problem—but didn’t answer it.
We didn’t check on-chain. DVN configuration is actually readable on-chain via LayerZero’s EndpointV2 contract. We could have queried the ULN302 registry to independently verify Kelp’s DVN threshold—rather than labeling it “not publicly disclosed.” Had we done so, we’d have seen the 1-of-1 configuration outright, eliminating the need for Kelp disclosure. This is the most concrete improvement direction for the tool: add on-chain DVN configuration verification to the cross-chain assessment step.
Findings weren’t specific or actionable enough. Stating “DVN configuration not disclosed” observes documentation absence—not predicting an exploit. Risks like oracle centralization, bridge dependency, and lack of insurance are widespread across most cross-chain DeFi protocols. Our tool flagged Kelp’s opacity—but also flagged similar patterns across dozens of protocols that weren’t attacked. Without publishing false-positive rates, claiming “we predicted it” is overstated. A more honest statement is: we asked some questions nobody else was asking—and one of them happened to land precisely on the critical load-bearing point.
On “Responsible Disclosure”
A fair question: If we flagged these risks on April 6, why didn’t we notify Kelp before the April 18 exploit?
We didn’t notify them. Reason: the report identified opacity—“DVN configuration not disclosed”—not a concrete, exploitable vulnerability. We didn’t know the configuration was 1-of-1; we only knew it wasn’t public. There was nothing specific enough to disclose. “Your bridge configuration lacks documentation” is a governance observation—not a bug bounty report.
Hindsight suggests we could have reached out privately to Kelp’s team and simply asked about their DVN threshold. That conversation might have exposed the 1-of-1 configuration and triggered remediation. We didn’t do it. Lesson learned: even if a finding seems too vague for formal disclosure, a private message asking a simple question is still worthwhile.
What This Means for DeFi Security
The Kelp exploit—like the Drift exploit 17 days earlier—was not a smart contract vulnerability. Slither, Mythril, or even GoPlus-style automated code scanners couldn’t detect it. The flaw resided in deployment configuration, governance gaps, and architectural decisions—layers above the code itself.
This is the core thesis of crypto-project-security-skill:
Protocol security is not just code security. A protocol can have flawless Solidity, five audits from top-tier firms, and a $250,000 bug bounty—and still lose $292 million due to a bridge validator configuration flaw.
The tool is open-sourced on GitHub—anyone can review its methodology, run it themselves, or improve it.
Timeline

Twelve days. The signal was there all along. The question is: how does the ecosystem build tools capable of spotting such signals before the next bridge collapses?
What You Can Do
If your assets reside in DeFi protocols with cross-chain bridges:
- Run your own audit. The tool is open-source. Don’t take our word for it—verify it yourself.
- Check bridge validator configuration. If a protocol refuses to disclose its DVN threshold, treat it as a red flag. Our report did exactly that—and it proved correct.
- Don’t assume code audits cover everything. Kelp underwent five or more code audits from reputable firms and platforms (Code4rena, SigmaPrime, MixBytes). Traditional code audits aren’t designed to catch configuration-layer risks like DVN threshold settings—that’s a different kind of analysis, not an audit firm’s failure.
- Evaluate insurance coverage. If a protocol lacks an insurance pool—and you’re an LP on a lending platform accepting its tokens as collateral—you’re implicitly underwriting it. This time, Aave WETH depositors learned that lesson the hard way.
The Bigger Picture: AI Agents as a Security Layer
This article discusses one tool and one exploit. But the underlying claim is broader: AI agents can serve as an independent security layer for DeFi investors.
Traditional crypto security has long followed this pattern: protocols hire audit firms, audit firms review code, audit firms publish reports. This model has blind spots—as the Kelp incident demonstrates. It focuses on code correctness, missing configuration, governance, and architectural risks.
Claude Code and tools like this offer an alternative path: anyone can use public data to run an AI-assisted risk assessment on any protocol—in minutes. You don’t need to pay $200,000 to an audit firm. You don’t need to read Solidity. You let the agent compare the protocol’s architecture against known attack patterns—and it surfaces the questions you should ask before depositing funds.
This won’t replace professional audits—but it lowers the barrier to first-line due diligence to a level accessible to everyone. An LP considering capital allocation into a new restaking protocol can now run audit defi <protocol> and receive a structured risk assessment covering governance, oracles, bridges, and economic mechanisms. For retail and mid-tier investors, this represents a tangible shift in self-protection capability.
Kelp’s report wasn’t perfect. It rated bridge risk as Medium instead of Critical. It failed to penetrate the configuration layer. But it asked the right questions—if Kelp’s team—or any LP—had taken those questions seriously at the time, the $292 million loss could have been avoided.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News