Cracking a Bitcoin Private Key in 9 Minutes? A Survival Guide for Blockchains Under Quantum Threat
TechFlow Selected TechFlow Selected

Cracking a Bitcoin Private Key in 9 Minutes? A Survival Guide for Blockchains Under Quantum Threat
Unveiling the Underlying Logic Behind Cracking Private Keys in 9 Minutes—and a Quantum-Resistant Self-Help Solution for 6.9 Million High-Risk Bitcoins
By Changan and the Biteye Content Team
TL;DR
A new paper from Google’s Quantum AI team reveals that a fault-tolerant quantum computer with 500,000 qubits could theoretically crack a Bitcoin private key in just nine minutes—posing a threat to approximately 6.9 million Bitcoins whose public keys have already been exposed on-chain. Although current technology remains 446 times short of this threshold—and such a machine is not expected before ~2029—this is no longer distant science fiction. The Bitcoin community is actively advancing quantum-resistant upgrade proposals, including BIP-360 and SPHINCS+. Ordinary users need not panic yet, but should verify their address format (avoid long-term use of Taproot addresses starting with bc1p), adopt a “one-address-per-transaction” habit, and stay attentive to wallet vendor updates.
March 31, 2026—a regular Monday—sent shockwaves through the crypto world.
Google’s Quantum AI team published a paper claiming quantum computers could crack Bitcoin private keys in just nine minutes—shorter than Bitcoin’s average block confirmation time of ten minutes.
Some dismissed it as alarmist; others said it remains decades away. But this warning came from Google.
Can quantum computers really break Bitcoin? Is the threat real—or exaggerated? What should ordinary users do? This article aims to clarify the issue.
I. What Exactly Does Google’s Paper Say?
The industry’s prior consensus held that cracking Bitcoin’s cryptography would require quantum computers with *millions* of qubits—an astronomically high number, leading most to assume this was still decades away. Google’s paper slashes that figure to under 500,000—cutting the estimate by roughly 20×.
The paper outlines a concrete attack scenario: When you broadcast a Bitcoin transaction, your public key is briefly exposed on the network while awaiting inclusion in a block—a window averaging ten minutes. According to Google’s estimates, a sufficiently powerful quantum computer could reverse-engineer your private key from that public key in ~9 minutes, then forge a higher-fee transaction to intercept your funds *before* your original transaction confirms—with an estimated success rate of ~41%.
Of course, the paper describes a fully error-corrected, fault-tolerant quantum computer. Google’s own Willow processor has only 105 physical qubits—446× fewer than the 500,000 required. So a quantum computer capable of breaking Bitcoin does not yet exist.
Google has set its own target for completing migration to post-quantum cryptography by 2029—a timeline that implicitly signals when they expect the threat to become practically relevant.
Yet if such a machine were ever built, cracking Bitcoin could prove far cheaper than many imagine.
II. How Do Quantum Computers Differ From Classical Computers?
Before assessing what this means, we must first answer a basic question: What *is* a quantum computer?
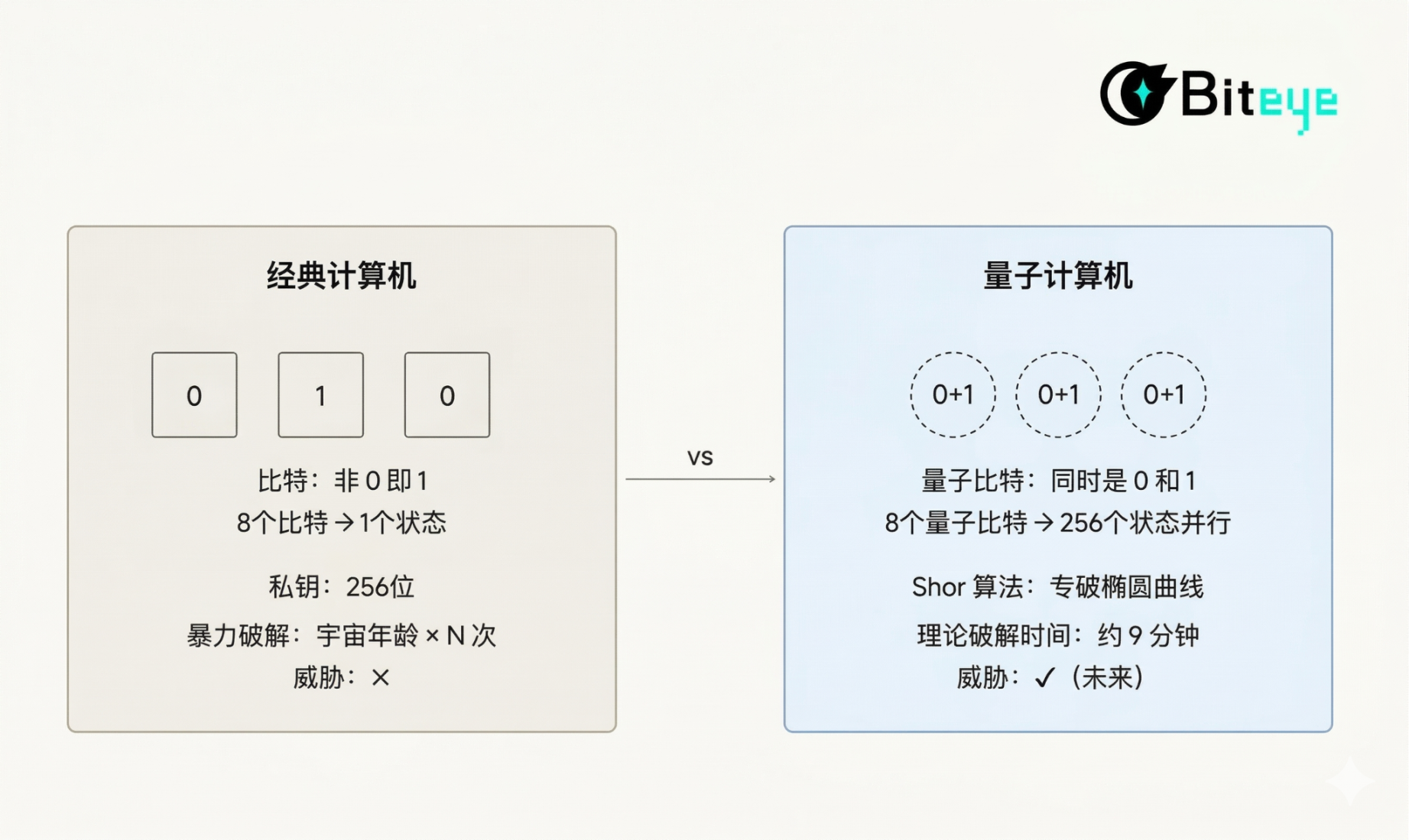
Classical computers process information using bits—each bit can be either 0 or 1.
All computation involves manipulating these 0s and 1s. A 256-bit private key implies 2²⁵⁶ possible combinations. Brute-forcing it with classical computing—even aggregating all global computational power—would take longer than the age of the universe. That’s why Bitcoin has remained secure for 15 years.
Quantum computers use *qubits*. Their magic lies in superposition: a qubit can be both 0 and 1 simultaneously. Eight qubits don’t represent just one state—they represent 256 states at once. As qubit count increases, parallel processing capability grows exponentially.
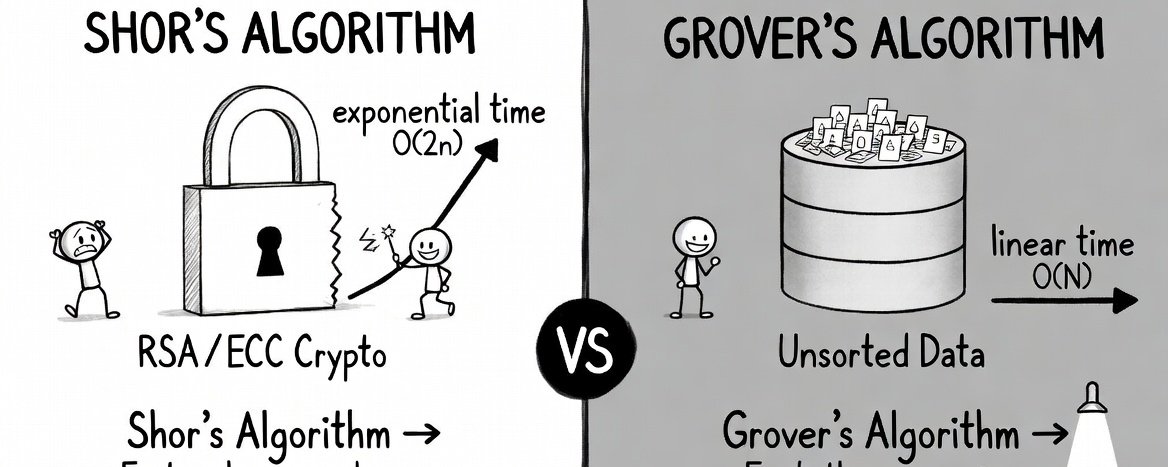
But mere parallelism alone isn’t enough to threaten Bitcoin. What truly endangers modern cryptography is Peter Shor’s 1994 algorithm—developed at MIT—which efficiently factors large integers and solves elliptic curve discrete logarithms—the very mathematical problems underpinning Bitcoin and Ethereum private-key security.
Analogy: A classical computer navigating a maze must try paths one by one. A quantum computer running Shor’s algorithm is like being handed an overhead map—you see the exit instantly.
Bitcoin uses ECDSA (Elliptic Curve Digital Signature Algorithm) over the secp256k1 curve. This system is impregnable to classical computers—but Shor’s algorithm is specifically engineered to dismantle elliptic curve mathematics.
III. How Exactly Could a Quantum Computer Steal Your Bitcoin?
Now that we understand quantum computing fundamentals, let’s examine how it threatens Bitcoin specifically.
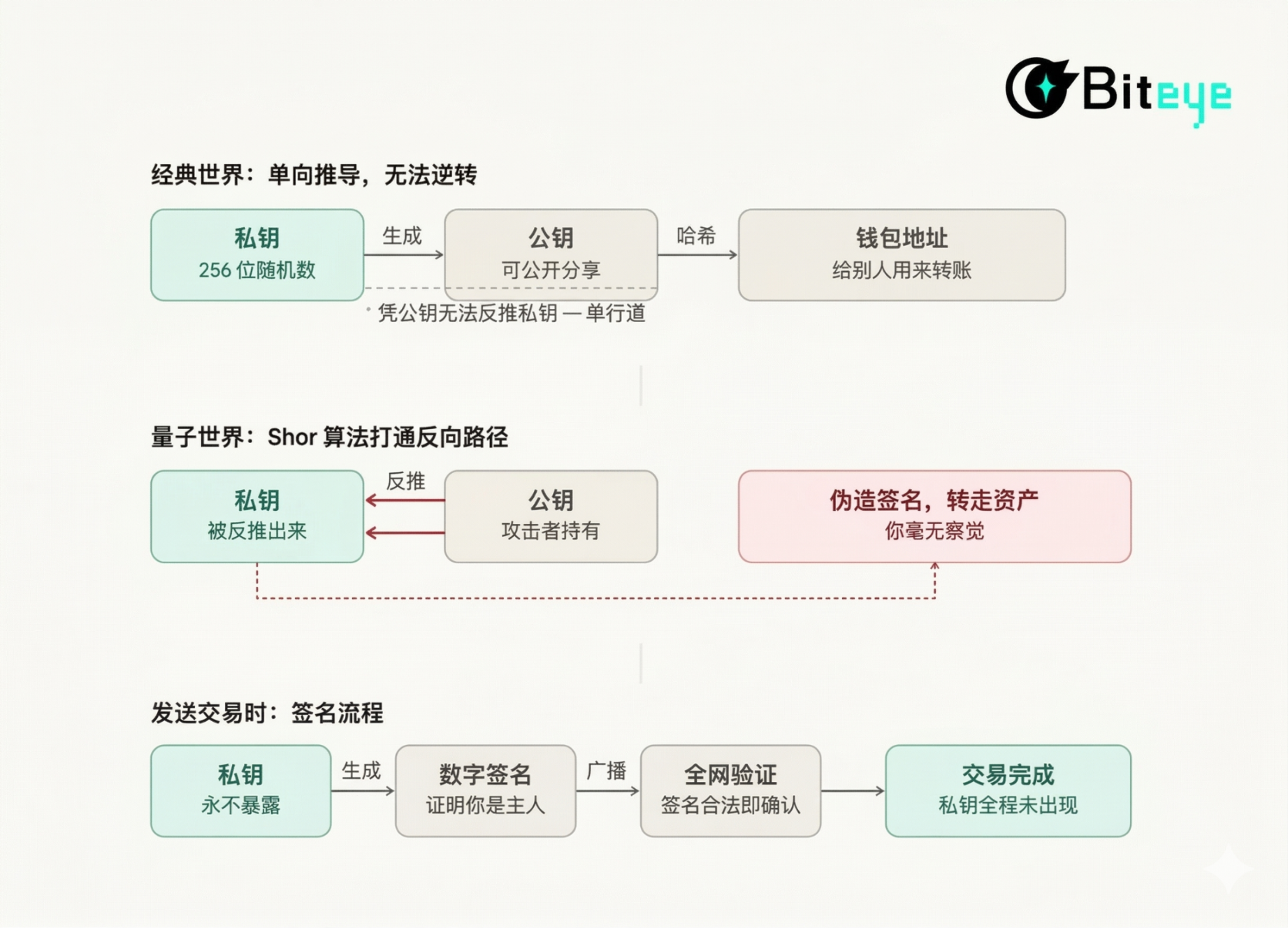
When creating a wallet, the system generates a private key—a random 256-bit number. The public key is derived from the private key, and the wallet address is derived from the public key. This chain flows unidirectionally: knowing the private key lets you compute the public key, but not vice versa.
When sending Bitcoin, your private key only signs a digital signature included with the transaction broadcast. The network verifies the signature and confirms the transaction.
Shor’s algorithm can theoretically break elliptic curve cryptography—the foundation of Bitcoin’s private-key security. Yet few took this seriously, because the computational power required is far beyond classical capabilities.
The problem is that quantum computing has genuinely progressed in recent years. Once sufficiently advanced, a quantum computer needs only your *public key* to deduce your private key, forge your signature, and drain your funds.
This raises a critical question: Has your public key already been exposed?
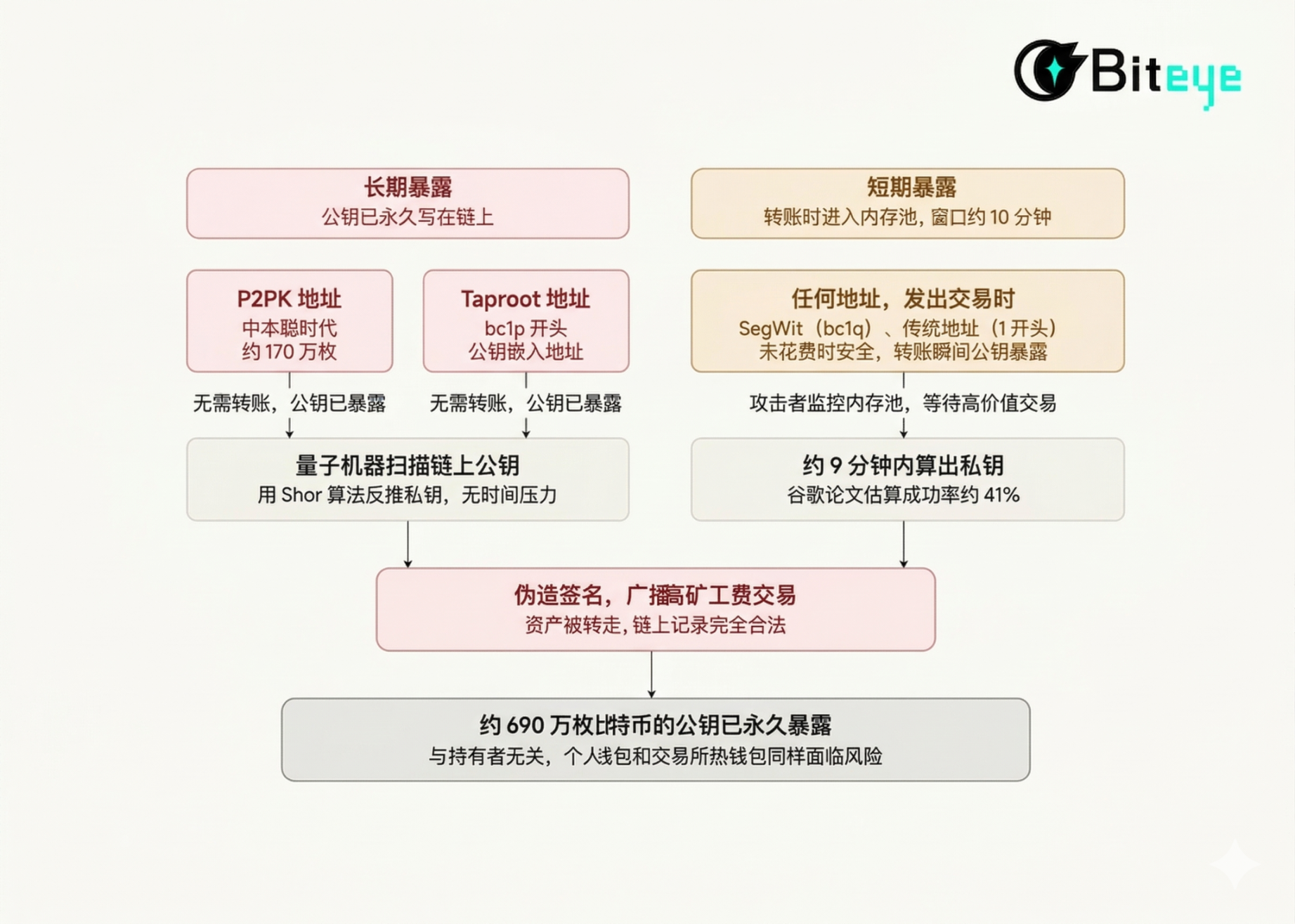
Public key exposure falls into two categories.
First, *permanent exposure*: The public key is permanently written onto the blockchain, accessible to quantum machines anytime. Two address types fall into this category:
- Legacy addresses used by Satoshi Nakamoto and early miners, where public keys were stored in plaintext;
- Addresses beginning with bc1p (Taproot). Though designed to improve privacy and efficiency, Taproot embeds the public key directly into the address—ironically making it *more* vulnerable to quantum threats.
Second, *temporary exposure*: With traditional address formats, the public key remains hidden behind a hash while unspent—unseen by outsiders. However, each time you broadcast a transaction, your public key enters the mempool and becomes visible to the entire network until confirmed in a block—typically a ~10-minute window.
In other words, no matter how cautiously you manage your funds, any transaction you’ve ever sent creates an attack window.
Currently, around 6.9 million Bitcoins have had their public keys permanently exposed on-chain. Whether held in personal wallets or exchange hot wallets, if the address belongs to a high-risk type—or if the address has ever sent a transaction—the public key has already leaked.
IV. What Is the Bitcoin Community Doing?
On the day Google’s paper dropped, CZ (@cz_binance) responded on X: “No need to panic—cryptocurrencies can upgrade to quantum-resistant algorithms. The threat is real, but the industry is capable of responding.”
Vitalik Buterin (@VitalikButerin) adopted a more cautious stance. He has warned about this risk for years and estimated a ~20% probability that a truly attack-capable quantum computer emerges before 2030.
Both agree the threat is real—only their assessments of urgency differ. In fact, Bitcoin developers had already been addressing this issue well before Google’s paper. Four approaches are now under serious discussion:

BIP-360 (Pay-to-Merkle-Root): Current Bitcoin addresses permanently record public keys on-chain. BIP-360 removes public keys entirely from the transaction structure, replacing them with Merkle roots instead. Without public keys to analyze, quantum attacks become impossible.
This proposal is already live on BTQ Technologies’ testnet, with over 50 miners participating and more than 200,000 blocks processed. However, it’s important to note: BIP-360 only protects newly minted coins. The ~1.7 million Bitcoins tied to legacy, publicly exposed addresses remain vulnerable.
SPHINCS+: Officially known as SLH-DSA, it’s a hash-based post-quantum signature scheme. Its logic is straightforward: since Shor’s algorithm targets elliptic curves, replace elliptic curves entirely—use hash functions for signing instead.
SPHINCS+ was standardized by NIST in August 2024. Its main drawback is signature size: today’s ECDSA signatures are just 64 bytes; SPHINCS+ signatures exceed 8 KB—over 100× larger—dramatically increasing transaction fees and block space requirements.
To address this, developers proposed optimizations like SHRIMPS and SHRINCS—aiming to shrink signature size without compromising security.
Commit/Reveal: Proposed by Lightning Network co-founder Tadge Dryja, this approach mitigates *temporary* exposure in the mempool. It splits transactions into two phases:
- Phase 1: Submit only a hash fingerprint—no transaction details—just a timestamp recorded on-chain;
- Phase 2: Broadcast the full transaction, revealing the public key only at this stage. Even if a quantum attacker intercepts the public key in Phase 2 and computes the private key, any forged transaction will be rejected—because it lacks the corresponding Phase 1 pre-commitment. The trade-off is an extra step per transaction and slightly higher cost.
The community views this as a transitional solution—deployable while more comprehensive quantum resistance is developed.
Hourglass V2: Proposed by developer Hunter Beast, this targets the ~1.7 million Bitcoins tied to legacy addresses with permanently exposed public keys. Its logic is pessimistic but pragmatic: since those public keys can never be hidden again, once quantum computers mature, those coins *will* eventually be stolen.
Rather than trying to prevent theft, Hourglass V2 proposes limiting withdrawals from such addresses to *one Bitcoin per block*—akin to banks imposing daily withdrawal caps during a bank run.
This proposal is highly controversial. Bitcoin’s core principle holds that no one—not even the protocol—should interfere with your coins. Even this limited restriction crosses a line for many.
This isn’t Bitcoin’s first major upgrade pressure point. The 2017 scaling debate lasted years and ultimately split the network into Bitcoin Cash. The 2021 Taproot upgrade took nearly four years from proposal to activation. Each time, the community endured prolonged debate, negotiation, and compromise before moving forward. Quantum resistance will almost certainly follow the same path.
V. What Should Ordinary Users Do Now?
So—what can ordinary users actually do?
The answer is simpler than you might think. Quantum computers cannot crack your Bitcoin today—but several practical steps can be taken right now.

Check Your Address Format
Open your wallet and check the prefix of your receiving address. Addresses beginning with bc1p are Taproot addresses—by design, their public keys are embedded directly into the address, making them high-risk for permanent exposure. If your funds sit in such addresses and have never moved, the current risk remains theoretical—but monitor BIP-360 developments closely.
Addresses beginning with bc1q (SegWit) or 1 (legacy P2PKH) keep their public keys protected by hashes while unspent—relatively safer. However, *any* transaction you send permanently exposes the public key on-chain.
Adopt Good Address Hygiene
Avoid repeatedly reusing the same address for receiving and sending. Every outgoing transaction exposes its public key—and reused addresses lose hash protection entirely. Most modern wallets automatically generate a new receiving address after each transaction; ensure this feature is enabled.
Monitor Wallet Software Updates
Hardware wallet vendors like Ledger and Trezor will play a crucial role in quantum resistance upgrades. Once BIP-360 or post-quantum signature schemes activate on mainnet, wallets must support new address formats and signing algorithms. For users, this may involve only a firmware update—or possibly migrating assets from old addresses to new ones. For now, ensure your wallet comes from a vendor with a proven track record of consistent updates, and stay informed.
Assets Held on Exchanges
Exchange-held assets require no user action—technical upgrades are handled by their engineering teams. Coinbase has already formed a Quantum Advisory Committee, and other major exchanges will likely follow under regulatory pressure. Assets held at reputable exchanges will experience quantum upgrades transparently.
VI. Final Thoughts
The claim that “quantum computers will break Bitcoin” has circulated for years—each time triggering skepticism, mockery, and inaction. Over time, it became widely assumed to be another “boy who cried wolf.”
This time, the warning comes from Google. Bitcoin developers are preparing response plans in earnest; Ethereum’s roadmap also includes quantum resilience initiatives. Yet until now, the issue remained purely theoretical—nobody can say for certain whether quantum computers will ever truly break Bitcoin’s cryptography.
Google says 2029. Others say decades. Some say never. Only time will tell.
Quantum computing progress has never been linear. The last major breakthrough arrived at an unexpected moment—and the next one might too.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News