The Real Threat of Quantum Computing to Bitcoin—99% of People Get It Wrong
TechFlow Selected TechFlow Selected
The Real Threat of Quantum Computing to Bitcoin—99% of People Get It Wrong
The truth is far more intriguing than panic—and far more worthy of caution than those dismissive denials.
Author: nvk
Translation: Saoirse, Foresight News
TL;DR
- Bitcoin does not use encryption—it uses digital signatures. The vast majority of articles get this wrong, and the distinction is critical.
- Quantum computers cannot break Bitcoin in nine minutes. That figure describes only a theoretical circuit; no such machine exists, and none will for at least a decade.
- Quantum mining is physically impossible. It would require more energy than the Sun emits in total.
- Bitcoin can absolutely be upgraded—indeed, it has been upgraded successfully before (SegWit, Taproot), and work is already underway (BIP-360). But the community needs to accelerate.
- The real motivation for upgrading isn’t quantum threat—it’s that classical mathematics has already broken countless cryptosystems, and secp256k1 is likely next. Quantum computers have yet to break any cryptosystem.
- There is one genuine risk: approximately 6.26 million BTC have exposed public keys. This isn’t cause for panic—but it *is* worth preparing for now.
Core Narrative
In one sentence, here’s everything I’ll explain below:
The quantum threat to Bitcoin is real—but distant; media coverage is largely sensationalized and inaccurate; and the greatest danger isn’t quantum computers themselves, but the self-satisfied complacency disguised as either panic or indifference.
Both those shouting “Bitcoin is doomed” and those saying “Nothing to worry about—don’t overreact” are wrong. Seeing clearly requires accepting two truths simultaneously:
- Bitcoin faces no imminent quantum threat—the actual timeline is likely far longer than clickbait headlines suggest.
- Yet the Bitcoin community must still prepare early, because the upgrade process itself takes years.
This isn’t a reason to panic—it’s a reason to act.
Below, I’ll clarify with data and logic.
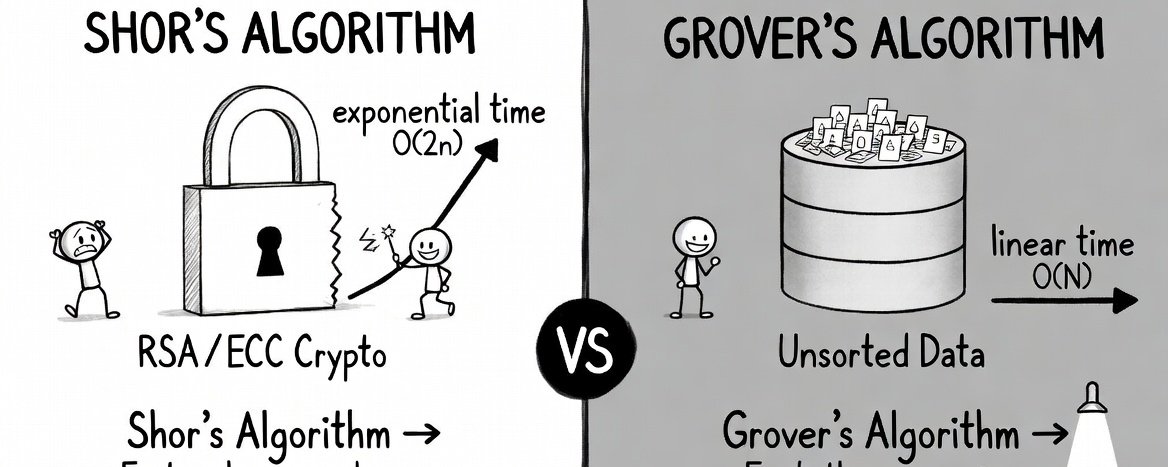
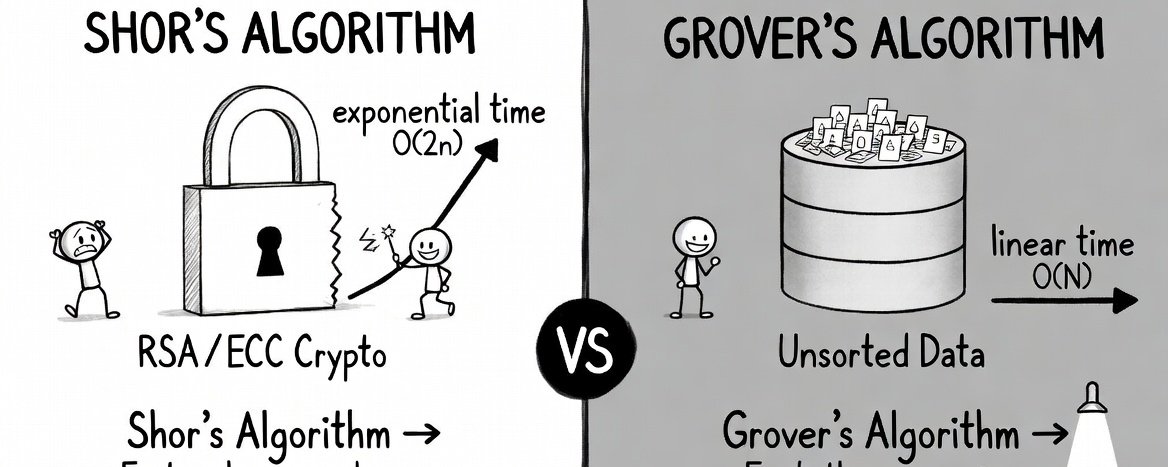
This diagram compares the two core quantum algorithms: Shor’s algorithm (left) is the “cryptographic killer” enabling exponential speedup for integer factorization and directly breaking RSA/ECC public-key cryptography; Grover’s algorithm (right) is a general-purpose quantum accelerator offering only quadratic speedup for unstructured search. Together they illustrate quantum computing’s disruptive potential—but both remain limited by error-corrected hardware, preventing large-scale deployment.
Media Playbook: Sensationalism Is the Real Risk
Every few months, the same cycle repeats:
- A quantum computing lab publishes a rigorous, highly qualified research paper.
- Tech media immediately rewrites it as: “Quantum Computer Breaks Bitcoin in 9 Minutes!”
- Crypto Twitter condenses it further: “Bitcoin is dead.”
- Your relatives and friends text you asking whether you should sell immediately.
- But the original paper never said any of that.
In March 2026, Google’s Quantum AI team published a paper showing that the number of physical qubits required to break Bitcoin’s elliptic curve cryptography could fall below 500,000—representing a 20× improvement over prior estimates. This is indeed significant research. Google was extremely cautious: it did not publish the actual attack circuit, only a zero-knowledge proof.
Yet the paper never claimed Bitcoin is currently breakable, that there is a concrete timeline, or that anyone should panic.
Headlines, however, proclaimed: “Breaks Bitcoin in 9 Minutes.”
CoinMarketCap once published an article titled “Will AI-Accelerated Quantum Computing Destroy Bitcoin in 2026?”, whose body text explicitly states the answer is almost certainly “no.” This is a classic pattern: alarming headlines drive traffic; careful, accurate explanations follow in the body. But 59% of shared links are never clicked—so for most people, the headline *is* the information.
As one observer put it aptly: “Markets price risk very quickly. You can’t steal something that zeroes out the moment it lands in your hands.” If quantum computers were truly about to upend everything, Google’s own stock—which relies on the same cryptographic primitives—would have crashed long ago. Yet Google’s share price remains stable.
Conclusion: The headline is the real rumor. The research itself is genuine and worth understanding—so let’s examine it carefully.
What Quantum Computers Actually Threaten—and What They Don’t
The Biggest Misconception: “Encryption”
Nearly every article about quantum computing and Bitcoin uses the word “encryption.” That’s incorrect—and the error skews the entire analysis.
Bitcoin does not protect assets via encryption, but via digital signatures (ECDSA, later Schnorr via Taproot). The blockchain itself is public: all transaction data is permanently visible to everyone. There is nothing to “decrypt.”
As Adam Back—creator of Hashcash and cited in the Bitcoin whitepaper—puts it: “Encryption means data is hidden and can be decrypted. Bitcoin’s security model is based on signatures, used to prove ownership without revealing private keys.”
This isn’t semantics. It means the quantum threat model of “harvest now, decrypt later”—the most urgent concern in other domains—barely applies to Bitcoin’s asset security. There’s no encrypted data to harvest; public keys are already publicly recorded on-chain.
Two Quantum Algorithms: One Is a Real Threat, the Other Is Not
- Shor’s algorithm (the real threat): Provides exponential speedup for the underlying mathematical problems behind digital signatures—allowing attackers to derive private keys from public keys and forge transaction signatures. This is what truly warrants concern.
- Grover’s algorithm (not a threat): Offers only quadratic speedup against hash functions like SHA-256. It sounds intimidating—until you do the math, revealing its practical irrelevance.
A 2025 paper, “Kardashev-Scale Quantum Computing and Bitcoin Mining,” calculates that quantum mining at Bitcoin’s current difficulty would require:
- Approximately 10²³ physical qubits (the global total today is ~1,500)
- Roughly 10²⁵ watts of power (the Sun’s total output is ~3.8 × 10²⁶ W)
Running a quantum computer to mine Bitcoin would consume energy equivalent to ~3% of the Sun’s total output. Humanity is currently only a Type 0.73 Kardashev civilization. To achieve such quantum mining, we’d need the energy capacity of a Type II civilization—one capable of harnessing an entire star’s energy. That is physically impossible for us today—and likely forever.
(Note: Kardashev scale definitions: Type I = full utilization of planetary energy [Earth]; Type II = full utilization of stellar energy [Sun])
By comparison: even under ideal design assumptions, a quantum miner achieves only ~13.8 GH/s; a standard Antminer S21 delivers 200 TH/s. Conventional ASIC miners are ~14,500× faster than quantum miners.
In short: quantum mining is fundamentally infeasible—not just now, but also in 50 years, or ever. Anyone claiming quantum computers can “break Bitcoin mining” is conflating entirely different algorithms.
Eight Common Claims—Seven and a Half Are Wrong
Claim 1: “The moment quantum computers arrive, all Bitcoin will be stolen overnight.”
Reality: Only Bitcoin with exposed public keys face security risk. Modern Bitcoin address formats (P2PKH, P2SH, SegWit) do *not* reveal public keys until you initiate a transaction. As long as you never reuse addresses and never send funds from an address, your public key remains off-chain.
Breakdown:
- Tier A (immediate risk): ~1.7 million BTC use legacy P2PK format—public keys fully exposed.
- Tier B (risk exists but is mitigable): ~5.2 million BTC reside in reused addresses and Taproot addresses—users can migrate to mitigate risk.
- Tier C (temporary exposure): Public keys are briefly exposed for ~10 minutes while transactions sit in the mempool awaiting confirmation.
Per Chaincode Labs’ estimate, roughly 6.26 million BTC face public-key exposure risk—about 30–35% of total supply. That’s substantial—but nowhere near “all Bitcoin.”
Claim 2: “Satoshi’s coins will be stolen, crashing the market to zero.”
Partially true, partially false: Satoshi’s ~1.1 million BTC use P2PK format, with fully exposed public keys—making them high-risk assets. However:
- Quantum computers capable of cracking these private keys simply don’t exist today.
- Nations first gaining access to early quantum technology will prioritize intelligence and military systems—not staging a “public Bitcoin heist spectacle” (per the Quantum Canary Research Group).
- Scaling from ~1,500 qubits today to hundreds of thousands will require multiple years of engineering breakthroughs—progress remains highly uncertain.
Claim 3: “Bitcoin cannot be upgraded—its pace is too slow and governance too chaotic.”
This claim is inaccurate—but not entirely baseless. Bitcoin has successfully completed several major upgrades:
- Segregated Witness (SegWit, 2015–2017): Highly contentious, nearly failed, and directly triggered the Bitcoin Cash fork—but ultimately succeeded.
- Taproot (2018–2021): Smooth rollout, taking ~3.5 years from proposal to mainnet activation.
The leading post-quantum proposal, BIP-360, entered the official Bitcoin BIP repository in early 2026. It introduces the bc1z address type and removes Taproot’s quantum-vulnerable key-path spending logic. The proposal remains in draft status, but Dilithium-based post-quantum signature instructions are already running on testnet.
Ethan Heilman, co-author of BIP-360, estimates the full upgrade cycle will take ~7 years: 2.5 years for development and review, 0.5 years for activation, and 4 years for ecosystem migration. He candidly admits: “This is only a rough estimate—nobody can give a precise timeline.”
Objective conclusion: Bitcoin *can* be upgraded, and the process has already begun—but it’s still in early stages and requires acceleration. Claiming “upgrades are impossible” is false; claiming “they’re already complete” is equally false.
Claim 4: “We only have 3–5 years left.”
Highly unlikely—but not something to dismiss outright. Expert timelines vary widely:
- Adam Back (Hashcash inventor, cited in Bitcoin whitepaper): 20–40 years
- Jensen Huang (NVIDIA CEO): Practical quantum computers still 15–30 years away
- Scott Aaronson (UT Austin quantum computing authority): Refuses to give a timeline, noting that breaking RSA may require “hundreds of billions of dollars” in investment
- Craig Gidney (Google Quantum AI): Only a 10% chance of achieving this before 2030; also believes current qubit requirements are unlikely to improve by another order of magnitude—the optimization curve may already be flattening
- Survey of 26 quantum-security experts: 28–49% probability of risk emergence within 10 years
- ARK Invest: “A long-term risk—not imminent”
Notably, Google’s Willow chip broke the quantum error-correction threshold at the end of 2024. This means each increase in error-correcting code distance reduces logical error rates by a fixed factor (2.14 for Willow). Such suppression improves exponentially—but real-world scaling depends entirely on hardware progress, which could be logarithmic, linear, or excruciatingly slow. Breaking the threshold proves scalability is *feasible*, not that it will be fast, easy, or inevitable.
Also, Google’s March 2026 paper did not disclose the actual attack circuit—only a zero-knowledge proof. Scott Aaronson has warned that future researchers may stop publishing resource estimates for breaking cryptosystems altogether. Thus, we may not detect the approach of a “quantum crisis day” well in advance.
Even so, building a fault-tolerant quantum computer with hundreds of thousands of qubits remains a monumental engineering challenge. Today’s most advanced quantum computers cannot factor numbers larger than ~13 bits—whereas breaking Bitcoin’s cryptography requires factoring ~1,300-bit numbers. That gap won’t close overnight—but the trend merits attention, not dismissal.
Claims 5–8: Quick Clarifications
“Quantum computing will destroy mining”
False. Energy demand approaches the Sun’s total output—see Section Two.
“Harvest now, decrypt later”
Does not apply to stealing assets (the blockchain is public by design); only marginally affects privacy—thus a secondary concern.
“Google says ‘9 minutes to break Bitcoin’”
Google refers to the theoretical runtime (~9 minutes) of a circuit on a non-existent 500,000-qubit machine. Google has explicitly cautioned against panic-driven interpretations and withheld attack circuit details.
“Post-quantum cryptography isn’t mature yet”
The U.S. National Institute of Standards and Technology (NIST) has standardized ML-KEM, ML-DSA, and SLH-DSA. The algorithms themselves are mature—the challenge lies in deploying them within Bitcoin, not inventing them from scratch.
Five Things I’m Truly Concerned About
A blanket debunking article loses credibility. Here are five issues that genuinely trouble me:
- Estimated qubit requirements for cryptanalysis continue to decline—though this trend may now be slowing. In 2012, breaking cryptosystems was estimated to require 1 billion qubits; by 2019, that dropped to 20 million; by 2025, it fell below 1 million. In early 2026, Oratomic claimed neutral-atom architecture could achieve this with just 10,000 physical qubits. But note: all nine authors of that study are Oratomic shareholders, and their assumed 101:1 physical-to-logical qubit ratio remains unverified (historical ratios are closer to 10,000:1). Also, the “9-minute” computation achievable on Google’s superconducting hardware would take 10²⁶⁴ days on neutral-atom hardware—two completely different devices with vastly divergent speeds. Gidney himself acknowledges the algorithmic optimization curve may have plateaued. Still, nobody knows when—or if—the inflection point between “required qubits” and “available qubits” will arrive. The most objective conclusion: extreme uncertainty remains.
- Public-key exposure is expanding—not shrinking. Bitcoin’s newest and most widely adopted address format, Taproot, reveals adjusted public keys on-chain—giving quantum attackers an infinite offline window to crack them. Ironically, Bitcoin’s most recent upgrade *reduced* its quantum resistance—a sobering paradox. And the issue extends beyond on-chain addresses: Lightning Network channels, hardware wallet connections, multisig schemes, and extended public key sharing services all inherently propagate public keys. In a world where cryptographically relevant quantum computers (CRQCs) exist, and the entire system is built around public-key sharing, “protecting public-key privacy” becomes unrealistic. BIP-360 is merely step one—not a comprehensive solution.
- Bitcoin’s governance is slow—but a time window remains. Since November 2021, Bitcoin’s base protocol has activated no soft forks for over four years, remaining effectively stagnant. Google plans to complete its own post-quantum migration by 2029, whereas Bitcoin’s most optimistic estimate points to 2033. Given that practical cryptanalytic quantum computers are likely still decades away (most credible forecasts place them in the 2040s—or possibly never), this is not an emergency—but complacency is dangerous. The earlier preparations begin, the more从容 the later stages will be.
- Satoshi’s Bitcoin represents an unsolvable game-theoretic dilemma. Roughly 1.1 million BTC sit in P2PK addresses; with no known holder of the corresponding private keys (or Satoshi having disappeared), these coins can never be moved. Whether left untouched, frozen, or destroyed—each option carries severe consequences. There is no perfect solution.
- The blockchain is a permanent, immutable target list. Every exposed public key is permanently and freely recorded. Governments and agencies can begin preparation now—waiting patiently for the right moment. Defense demands proactive, multi-party coordination; attack only requires patience.
These are real challenges—but there’s another side worth highlighting.
Why the Quantum Threat May Be Extremely Distant—or Never Arrive
Several serious physicists and mathematicians—not fringe thinkers—argue that fault-tolerant quantum computing at cryptanalytic scale may confront fundamental physical barriers, not just engineering hurdles:
- Leonid Levin (Boston University, co-formulator of NP-completeness): “Quantum amplitudes must be precise to hundreds of decimal places—but humanity has never discovered a single physical law that holds beyond ~12 decimal places.” If nature forbids precision beyond ~12 digits, quantum computing hits a hard physical ceiling.
- Michel Dyakonov (University of Montpellier, theoretical physicist): A 1,000-qubit system would require simultaneous control of ~10³⁰⁰ continuous parameters—far exceeding the total number of subatomic particles in the observable universe. His conclusion: “Impossible. Forever impossible.”
- Gil Kalai (Hebrew University, mathematician): Quantum noise exhibits unavoidable correlated effects that intensify with system complexity, making large-scale quantum error correction fundamentally unachievable. His conjecture has stood unrefuted for 20 years—though some experimental predictions have deviated, yielding mixed evidence.
- Tim Palmer (Oxford University, physicist): His “realistic quantum mechanics” model predicts a hard upper limit of ~1,000 qubits for quantum entanglement—far below the scale needed for cryptanalysis.
These aren’t marginal views. Empirical evidence also strongly supports this perspective: to date, practice shows that quantum computing capable of threatening cryptosystems is either far harder to realize in reality than theory suggests—or fundamentally impossible due to unknown laws of physics. The analogy to autonomous driving fits well: impressive demos, massive investment—but perpetually “five years away” for over a decade.
Most media operate on the default assumption that “quantum computers will inevitably break cryptography—just a matter of time.” That isn’t a conclusion drawn from evidence—it’s a mirage generated by hype cycles.
The Real Motivation for Upgrading Has Nothing to Do With Quantum
This is a rarely mentioned but critical fact (thanks to @reardencode for highlighting it):
- Cryptosystems broken by quantum computers to date: 0
- Cryptosystems broken by classical mathematical methods: countless
DES, MD5, SHA-1, RC4, SIKE, the Enigma machine—all fell to elegant mathematical analysis, not quantum hardware. SIKE was NIST’s final candidate for post-quantum cryptography—yet in 2022, a researcher broke it completely on a standard laptop in under an hour. Since the dawn of cryptography, classical cryptanalysis has continuously invalidated supposedly secure schemes.
Bitcoin’s secp256k1 elliptic curve could fail tomorrow—not due to quantum computers, but due to a single mathematical breakthrough in discrete logarithms. All it takes is one top-tier number theorist making progress on that problem. It hasn’t happened yet—but cryptography’s history is precisely the story of “proven secure” systems repeatedly being found vulnerable.
That’s the true reason Bitcoin should adopt alternative cryptographic primitives: not because quantum computers are coming—they may never arrive—but because relying on a single cryptographic assumption for a multi-trillion-dollar network is a risk that rigorous engineering must proactively mitigate.
Quantum-related hype, ironically, obscures this quieter but more immediate danger. The irony? Preparations for quantum threats (BIP-360, post-quantum signatures, hash-based alternatives) would equally defend against classical cryptanalysis. People are doing the right thing for the wrong reason—and that’s fine—as long as it gets implemented.
So What Should You Do?
If you hold Bitcoin:
- Don’t panic. The threat is real—but distant. You have ample time.
- Stop reusing addresses. Each reuse exposes your public key. Always use new addresses for receiving funds.
- Track BIP-360 developments. When post-quantum addresses launch, migrate your holdings promptly.
- For long-term holding, keep funds in addresses from which you’ve *never sent*—keeping your public key hidden.
- Don’t let headlines dictate your emotions. Read the original papers. They’re more interesting—and less frightening—than news reports.
If you’re a Bitcoin developer:
- BIP-360 needs more reviewers. Testnet is live—code urgently needs scrutiny.
- The 7-year upgrade timeline must be compressed. Every year delayed shrinks the safety buffer.
- Initiate governance discussions on legacy unspent transaction outputs (UTXOs). Satoshi’s Bitcoin won’t protect itself—the community must devise solutions.
If you just saw a sensational headline: Remember, 59% of shared links are never clicked. Headlines stir emotion; papers provoke thought. Go read the source.
Conclusion
The quantum threat to Bitcoin isn’t binary—it exists on a spectrum. At one extreme: “Bitcoin is doomed—sell everything now.” At the other: “Quantum computing is a scam—zero risk.” Both extremes are wrong.
Truth resides in the rational, actionable middle: Bitcoin faces clear engineering challenges—parameters are known, R&D is advancing, timelines are tight but manageable—*provided* the community maintains appropriate urgency.
The greatest danger isn’t quantum computers—it’s the oscillating media cycle between panic and apathy, which prevents rational engagement with a solvable problem.
Bitcoin survived the block-size debate, exchange hacks, regulatory shocks, and its creator’s disappearance. It can survive the quantum era—but only if the community begins steady, deliberate preparation *now*: no panic, no passivity—just the robust engineering mindset that made Bitcoin possible.
The house isn’t on fire—and may never catch fire from the direction everyone fears. But cryptographic assumptions are never permanent. The best time to reinforce Bitcoin’s cryptographic foundations is always *before* crisis—not after.
Bitcoin has always been built by people who prepare for threats that haven’t yet materialized. That’s not paranoia—it’s engineering.
References: This article draws on 66 research papers across two thematic wikis—covering quantum computing resource estimation, Bitcoin vulnerability analysis, debunking psychology, and content propagation mechanisms. Core sources include Google Quantum AI Lab (2026), “Quantum Mining at the Kardashev Scale” (2025), the BIP-360 proposal document, Berger & Milkmann (2012), the “2020 Debunking Handbook,” and insights from Tim Urban, Dan Lu, patio11, and other industry practitioners. Full wiki references are open for peer review.
Join TechFlow official community to stay tuned
Telegram:https://t.me/TechFlowDaily
X (Twitter):https://x.com/TechFlowPost
X (Twitter) EN:https://x.com/BlockFlow_News